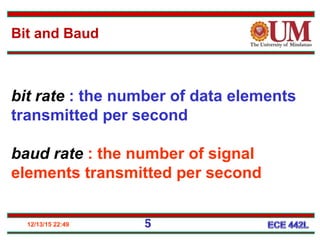
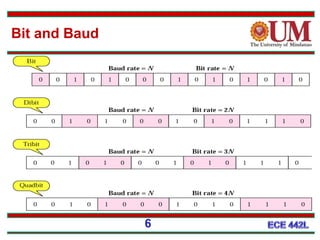
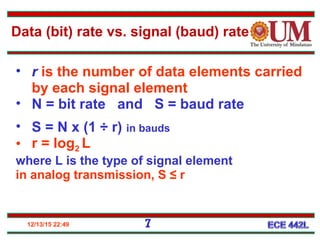
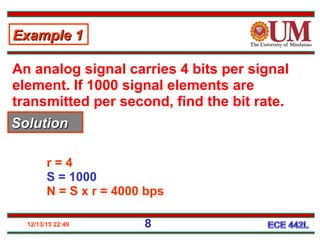
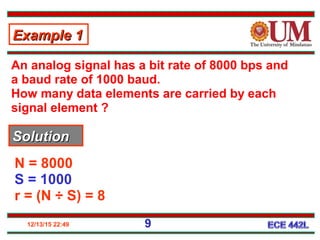
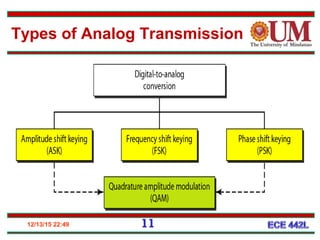
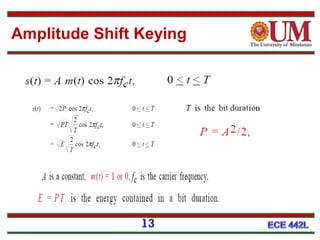
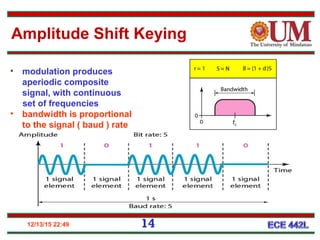
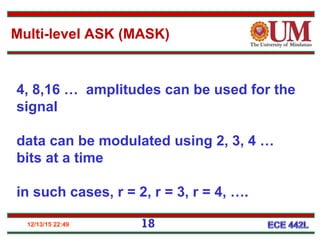
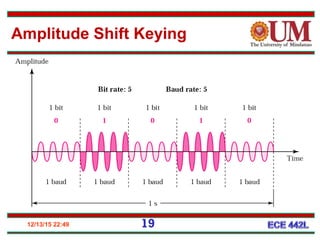
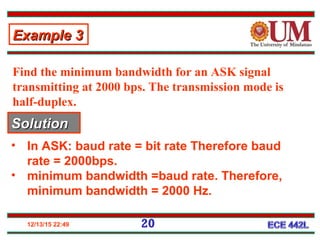
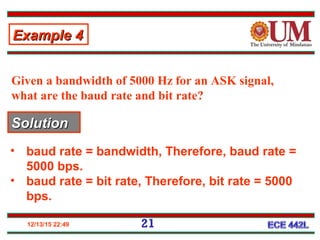
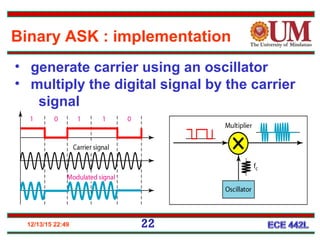
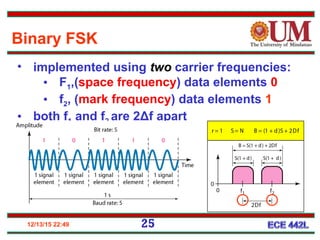
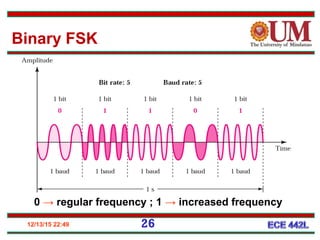
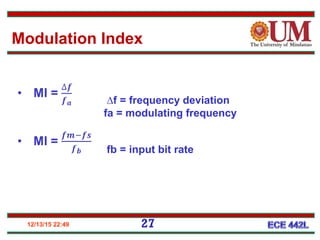
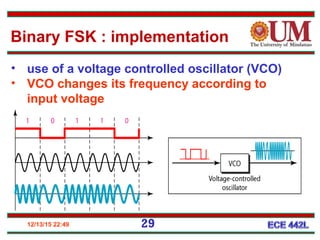
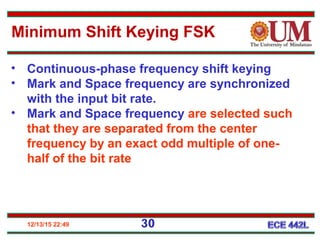
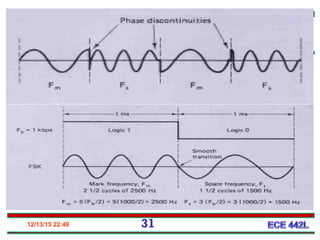
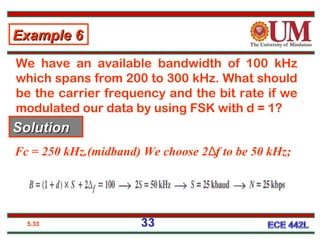
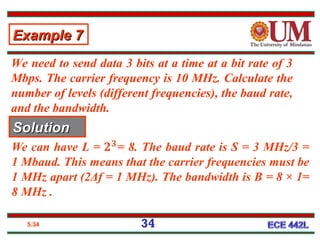
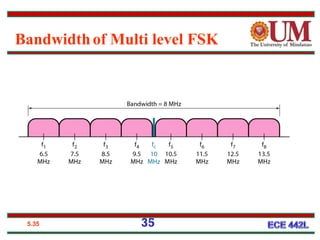
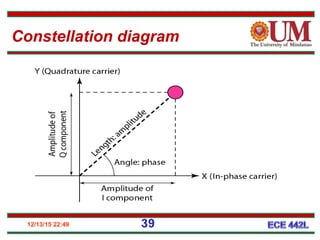
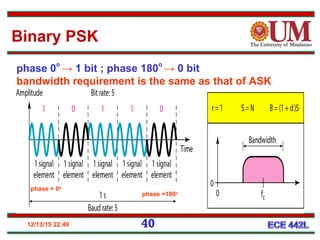
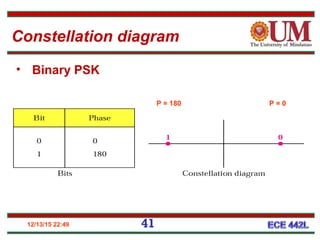
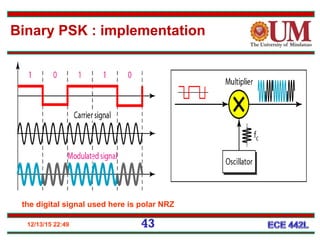
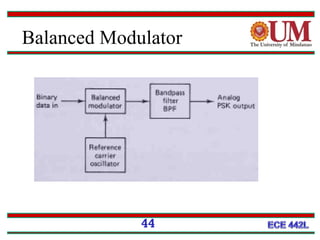
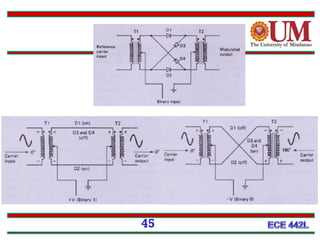
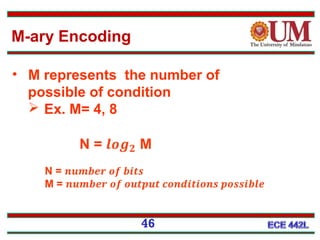
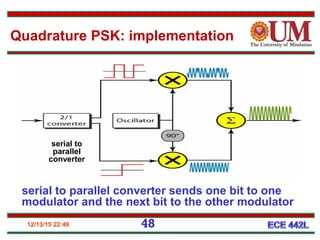
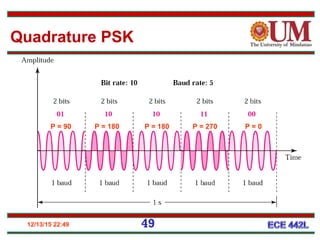
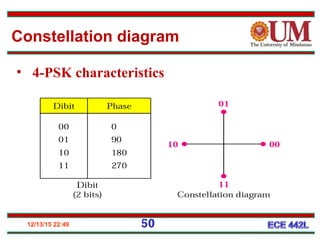
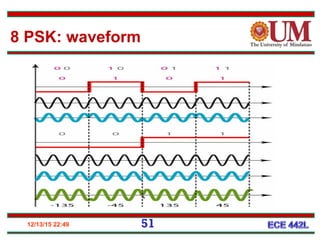
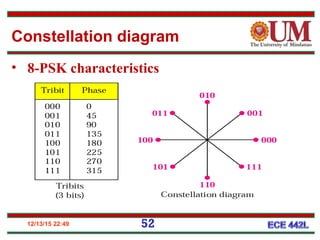
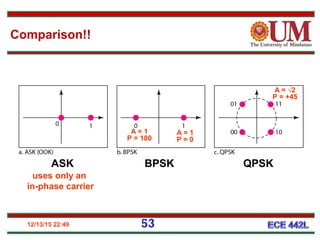
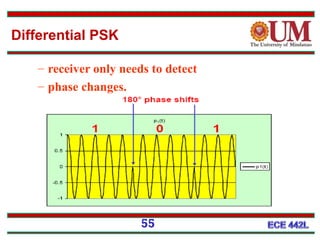
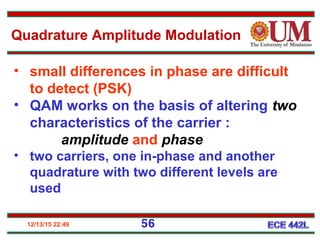
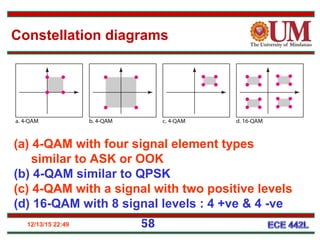
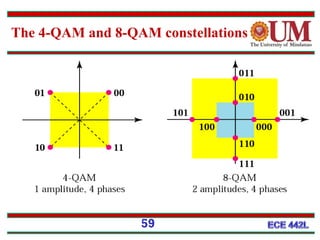
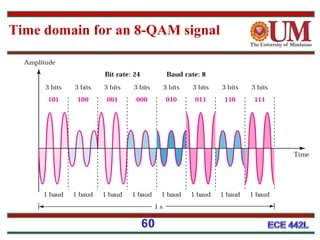
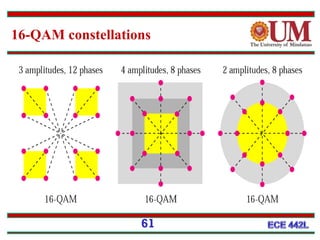
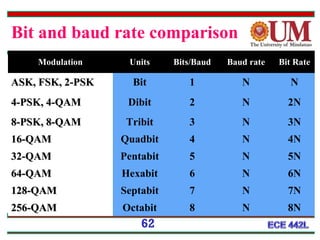
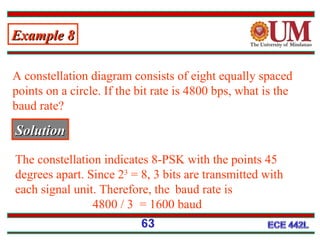
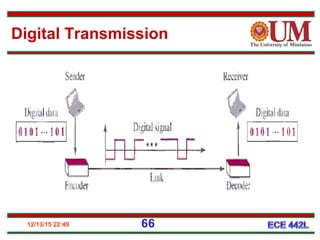
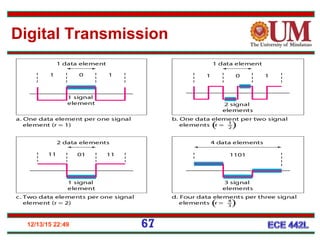
This document discusses various analog modulation techniques used for transmitting digital data over analog channels. It describes amplitude shift keying (ASK), frequency shift keying (FSK), and phase shift keying (PSK) in detail. It explains the concepts of bit rate, baud rate, modulation index, and provides examples of their calculation. It also introduces higher order modulation schemes like quadrature amplitude modulation (QAM) and provides constellation diagrams to illustrate various modulation techniques.