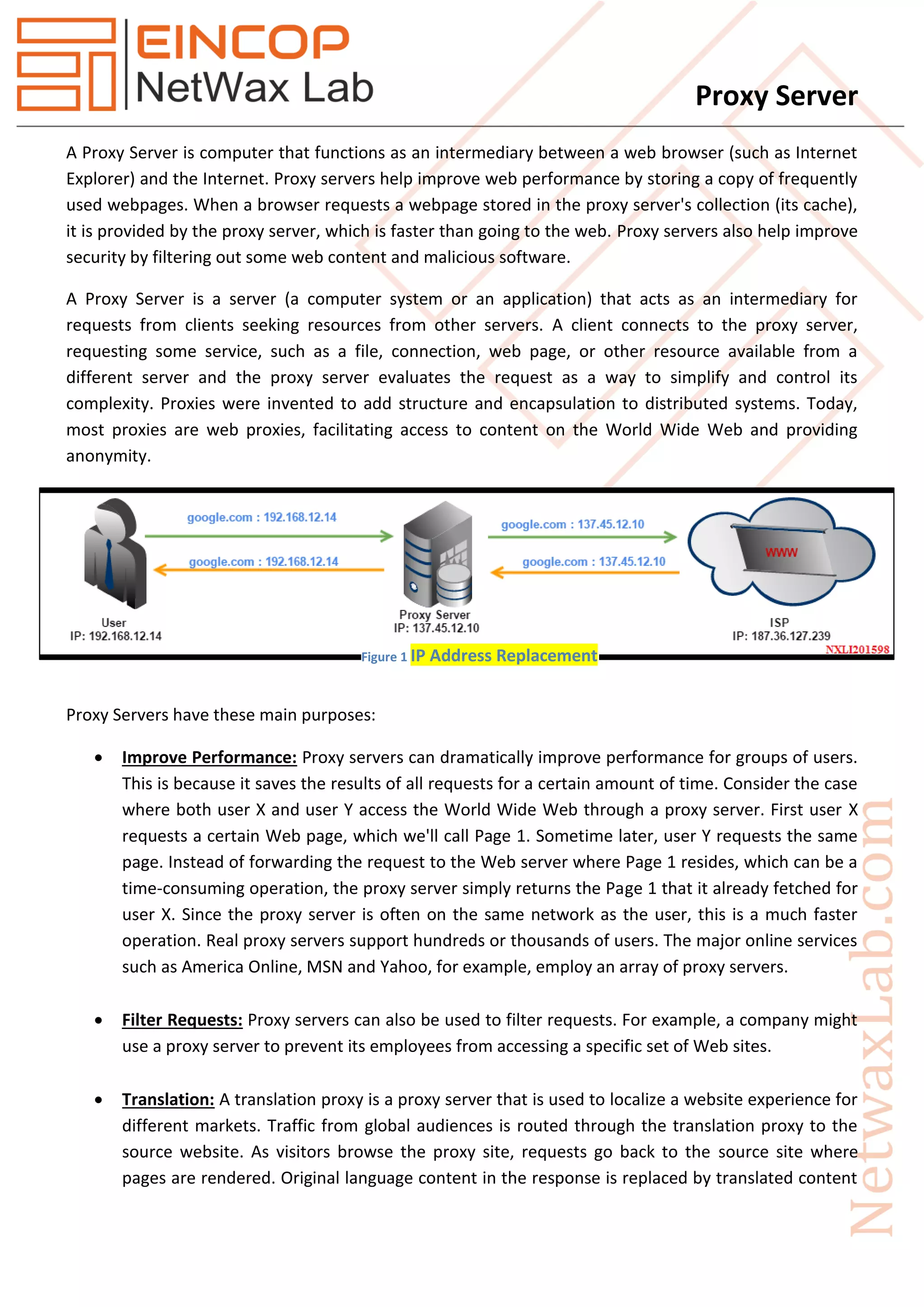
A proxy server acts as an intermediary between a web browser and the internet, enhancing web performance by caching frequently accessed pages and filtering out harmful content. It provides various functionalities, including request filtering, translation for localization, and anonymous browsing, while also maintaining network security. Different types of proxy servers, such as forward and reverse proxies, serve specific purposes, such as load balancing, caching, and SSL encryption for web servers.