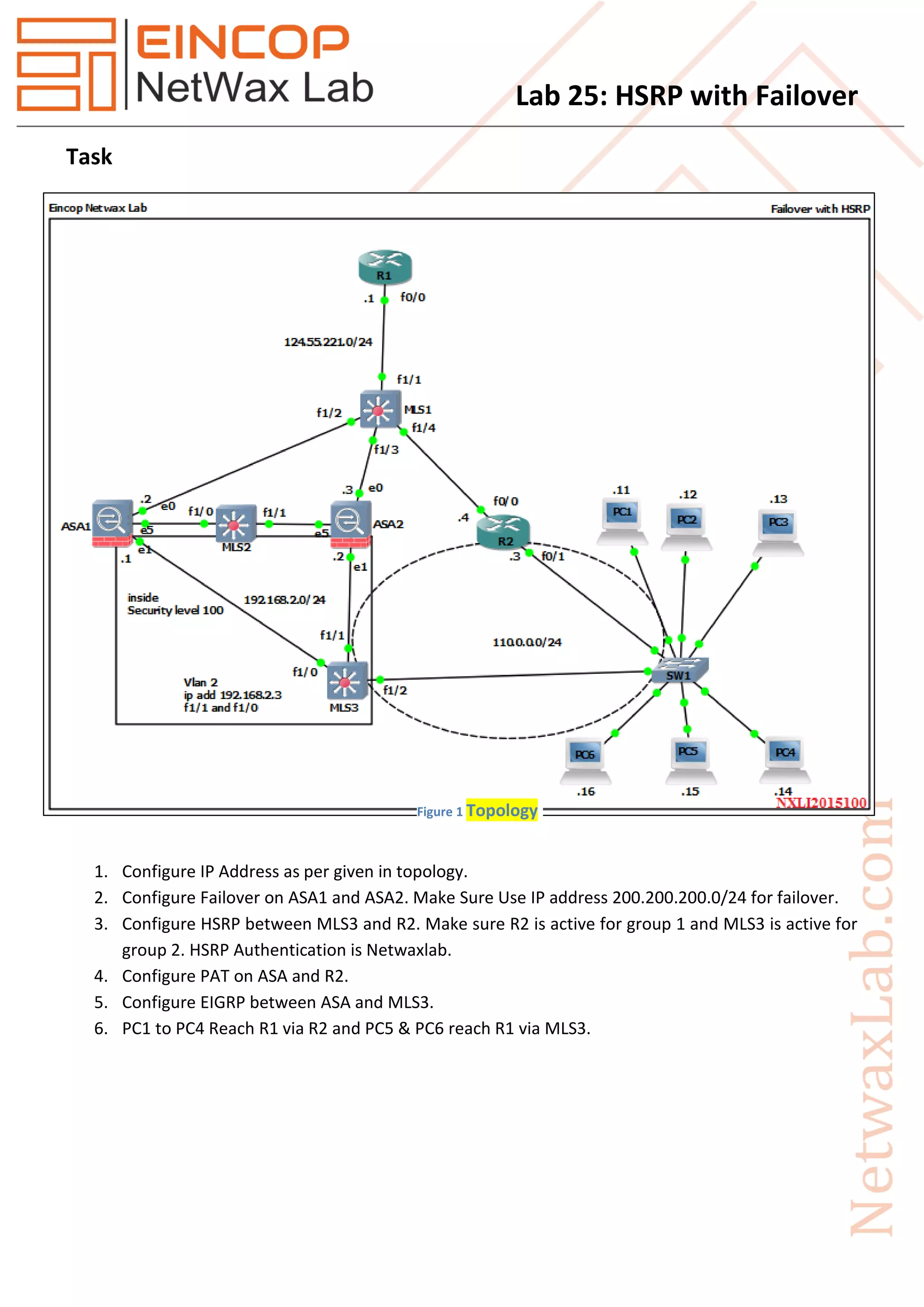
1. The document describes configuring high availability routing between two firewalls (ASA1 and ASA2) using failover, and between two routers (MLS3 and R2) using HSRP.
2. It provides configuration examples for failover on the ASAs, HSRP on MLS3 and R2, PAT on the ASA and R2, and EIGRP routing between the ASA and MLS3.
3. It also specifies default gateways for different PCs to reach R1 via the active HSRP router.