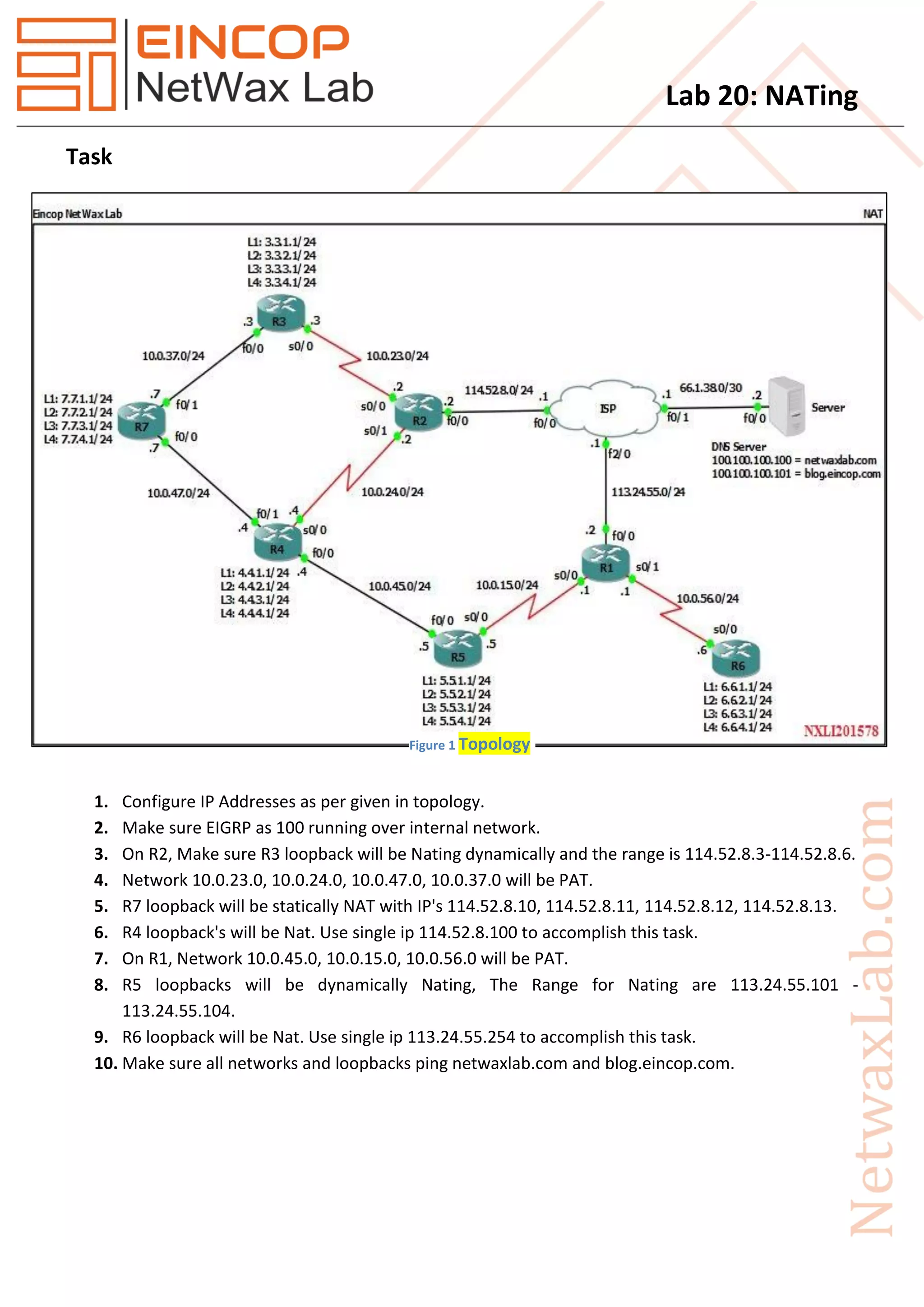
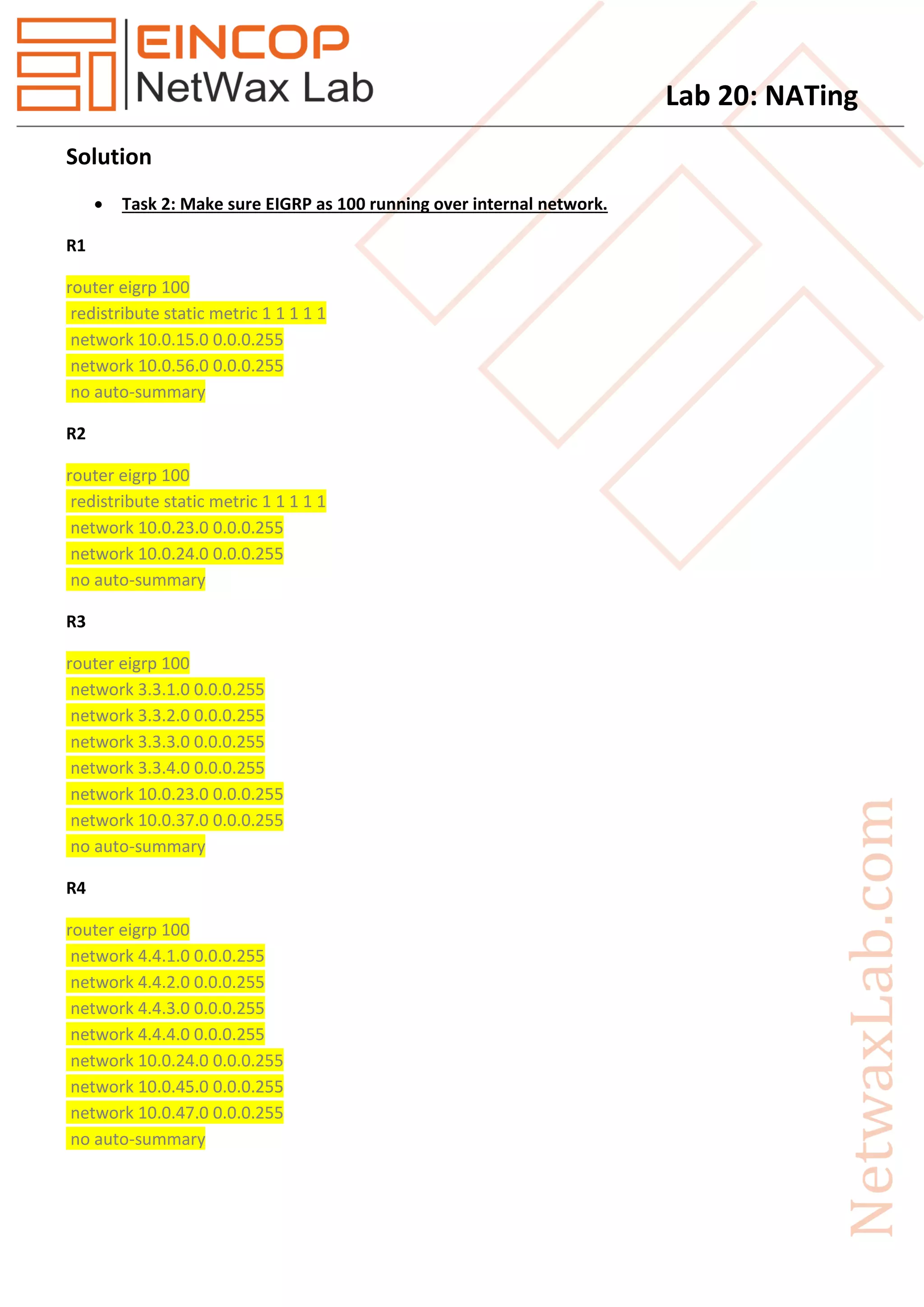
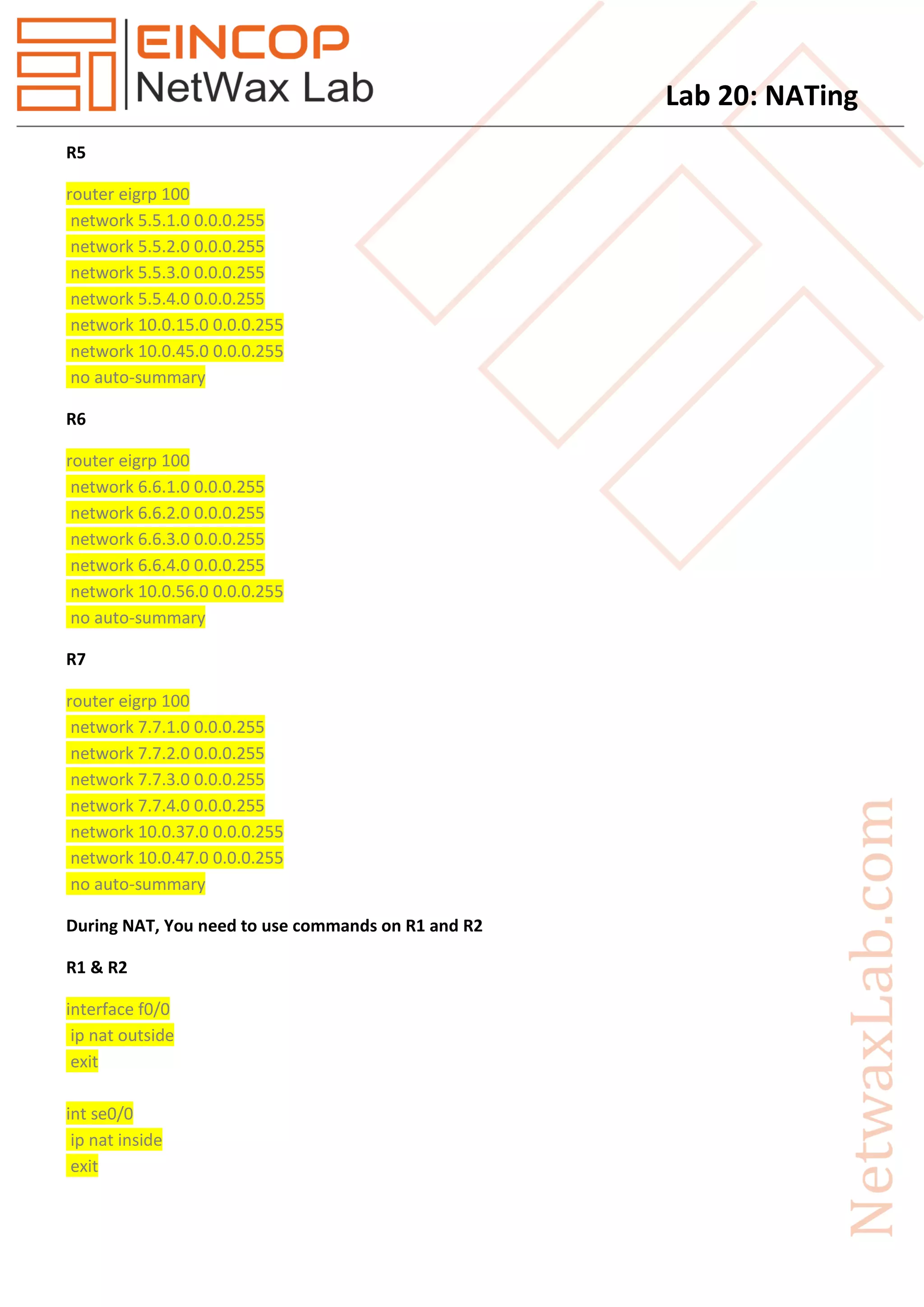
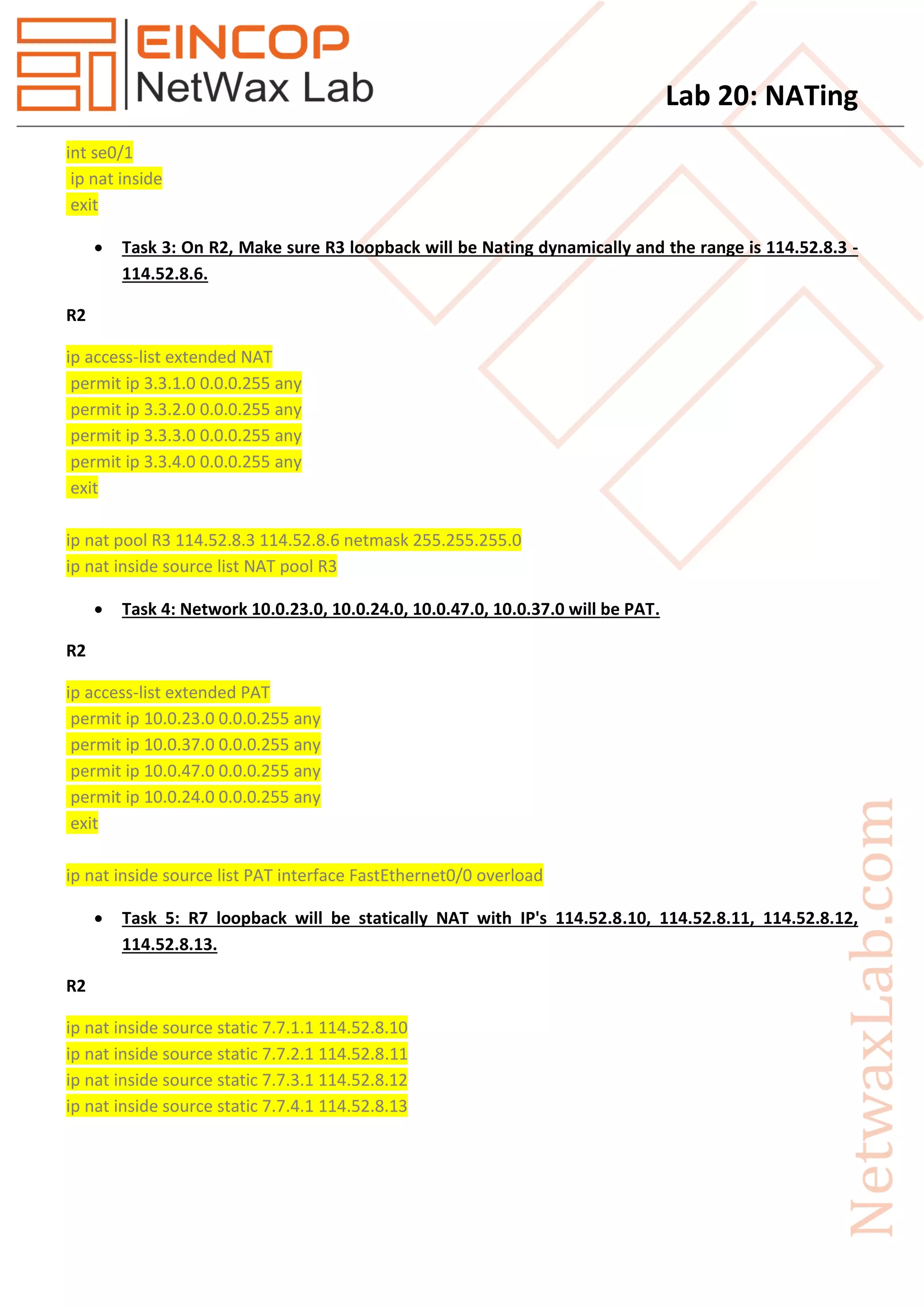
The document describes tasks to configure NAT on routers R1 and R2. This includes dynamically NATing internal networks and loopbacks to external IP ranges, PAT for some internal networks, and static NAT for R7's loopbacks. EIGRP is configured internally with redistribution. Access-lists are used to define the NAT source addresses and pools are used to map them to external IP ranges. Connectivity to external sites is tested with ping.