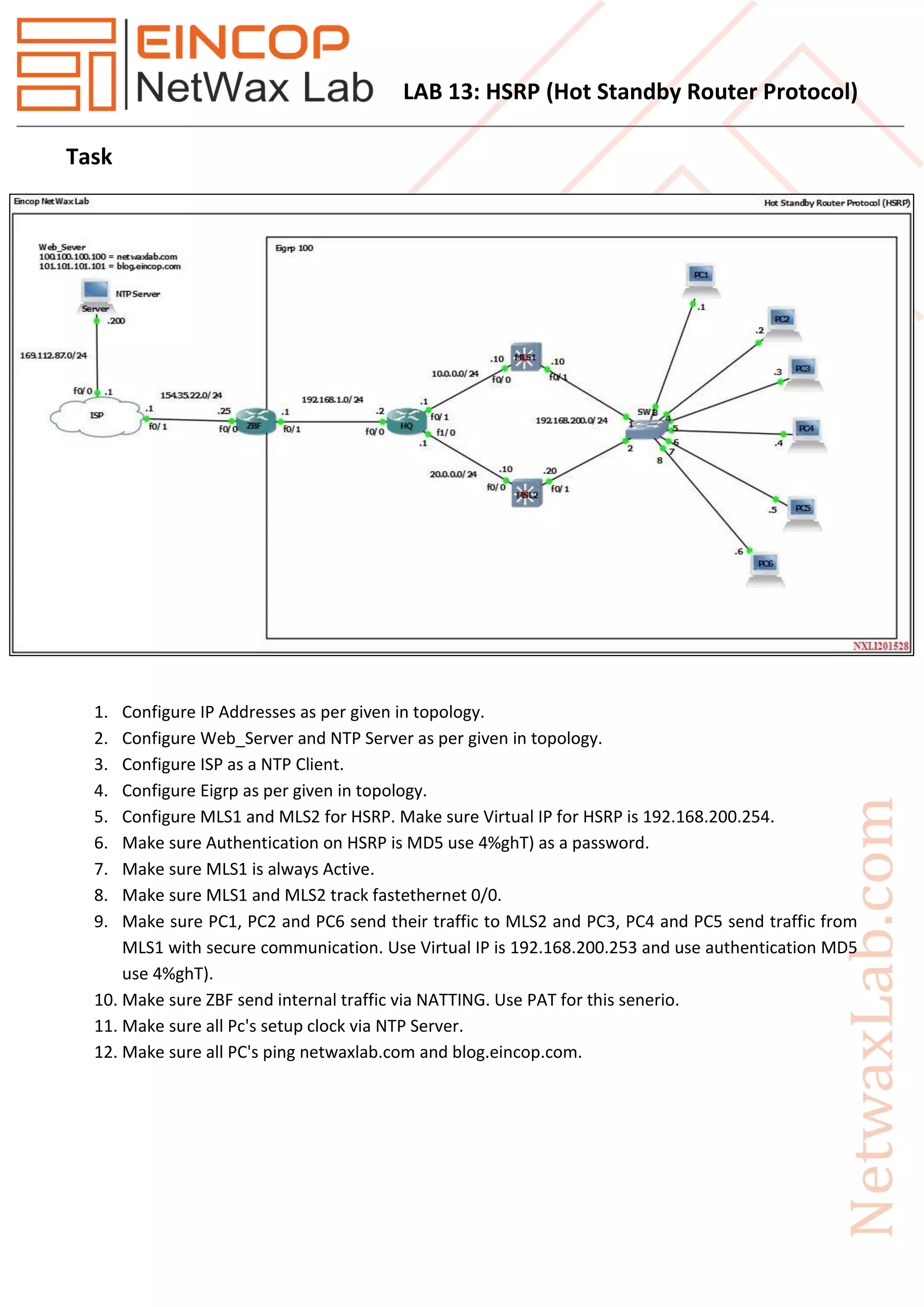
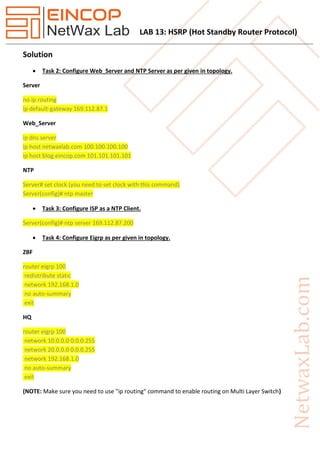
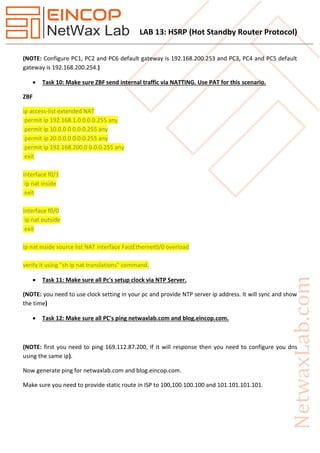
This document outlines the steps to configure HSRP (Hot Standby Router Protocol) on two multi-layer switches (MLS1 and MLS2) including: configuring IP addresses, EIGRP routing, web server and NTP server, setting MLS1 as the active router, tracking the state of interfaces, using HSRP for load balancing between the routers, and enabling NAT on the border router for internal traffic.