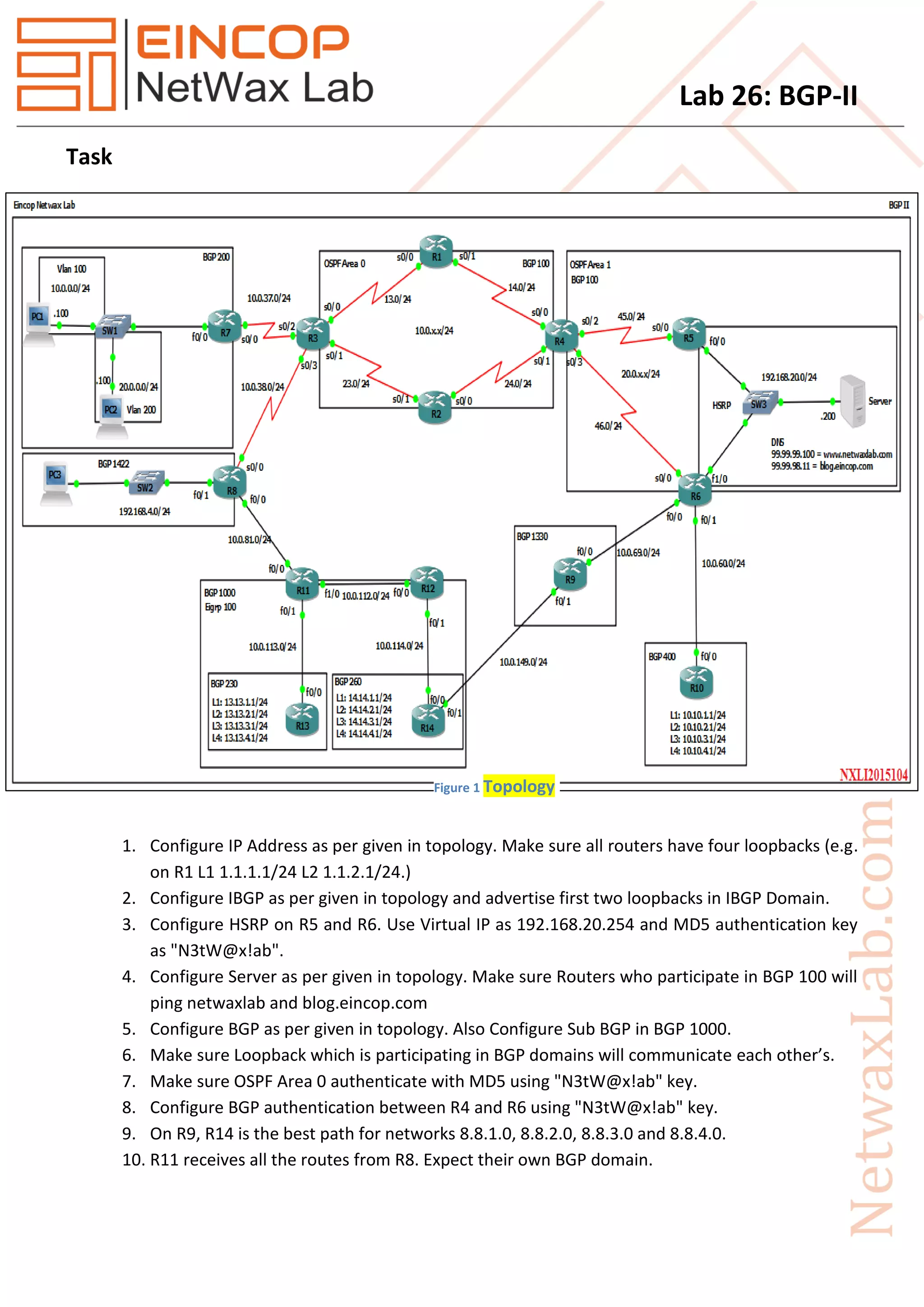
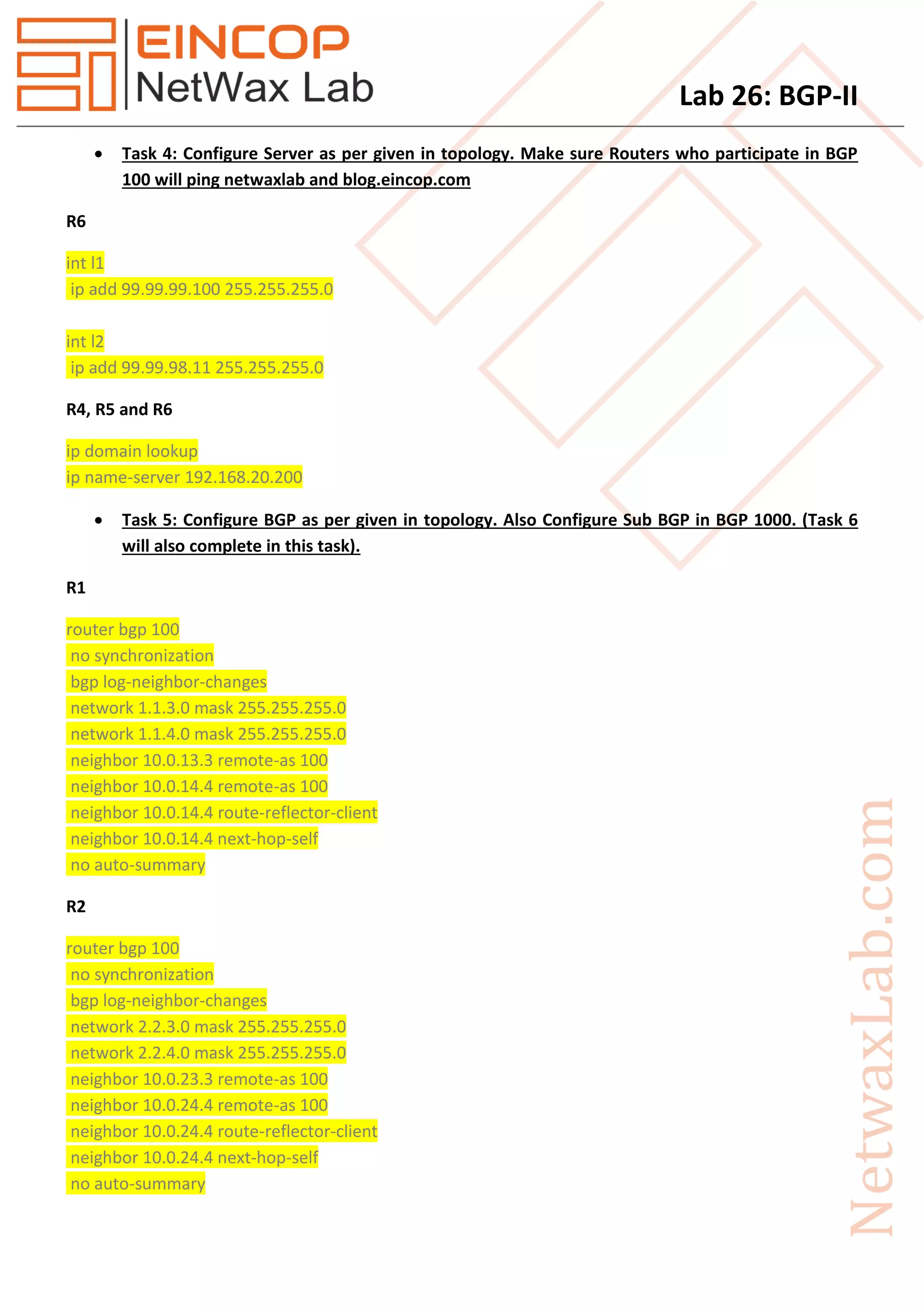
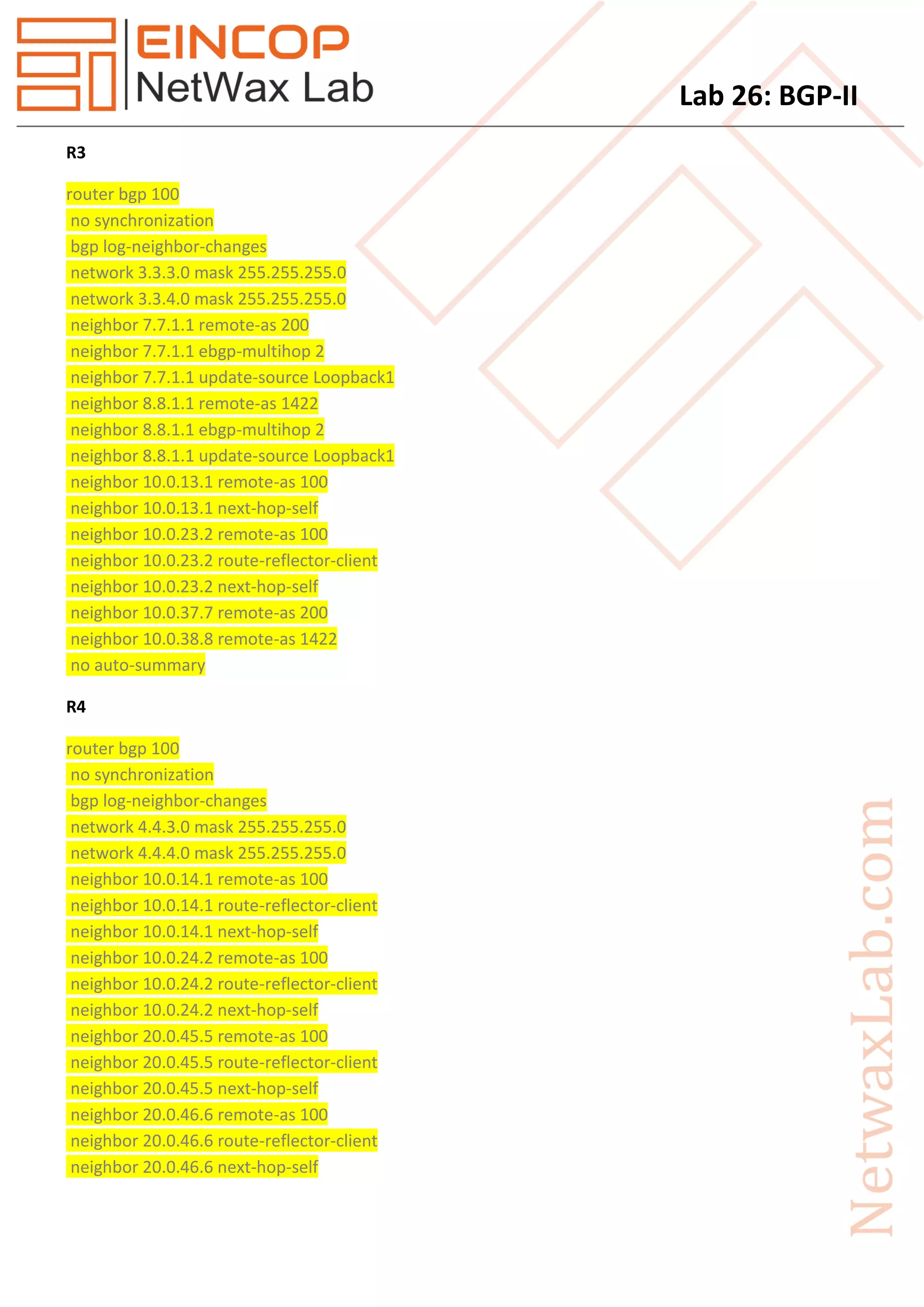
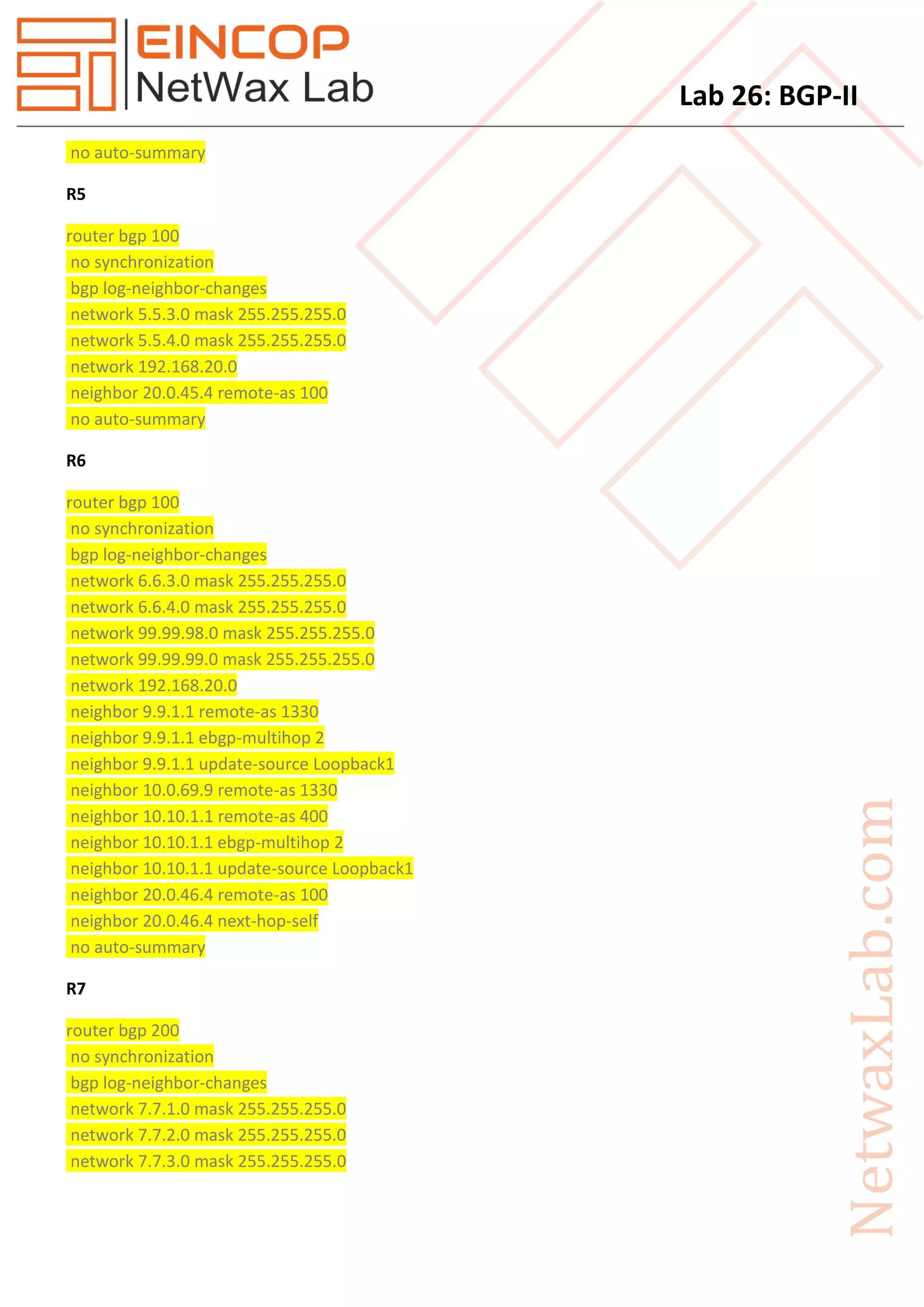
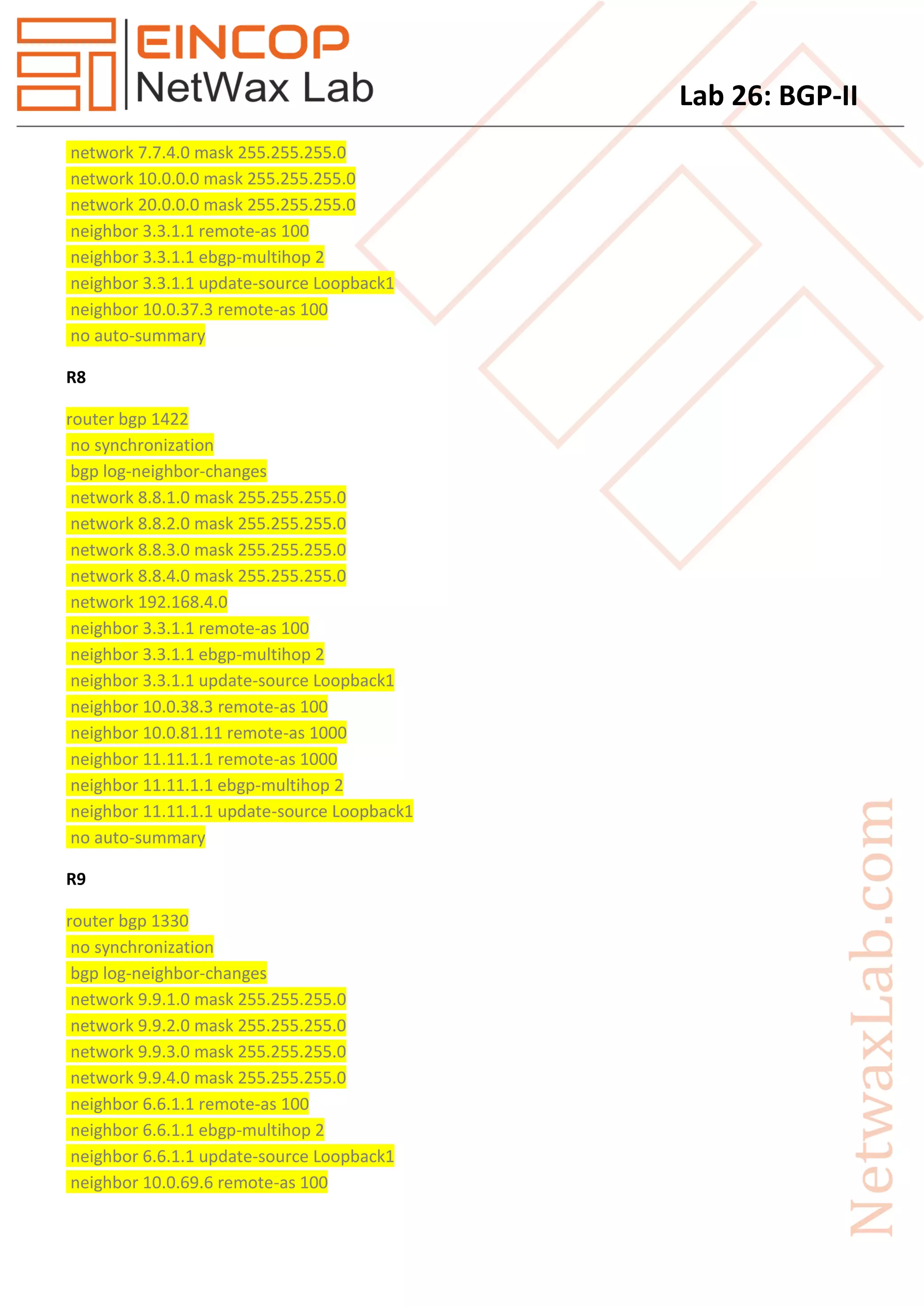
1. The document describes the configuration steps for a lab exercise involving BGP routing. It includes tasks to configure IP addresses, IBGP, HSRP, servers, and BGP routing on multiple routers as shown in the given topology diagram.
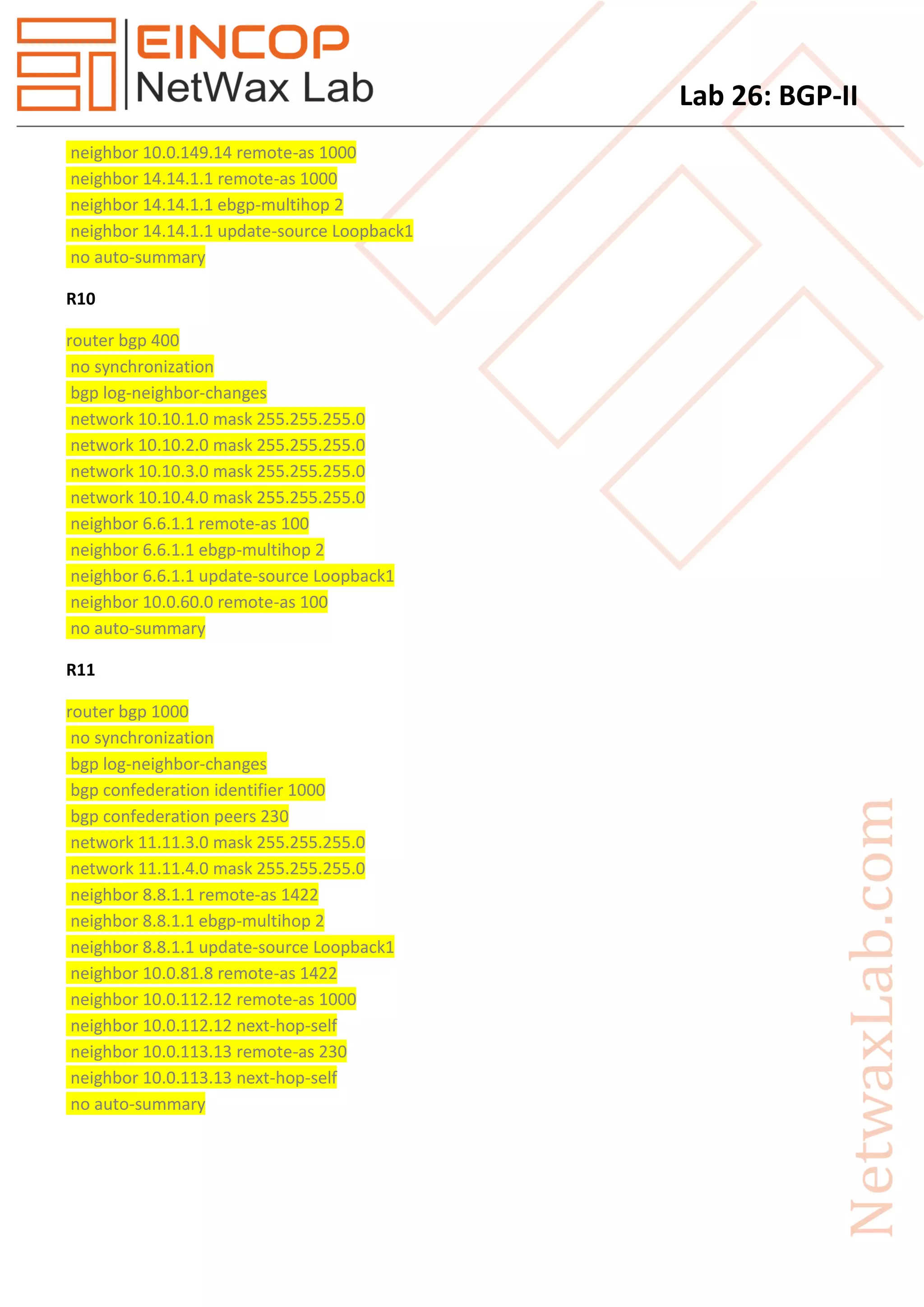
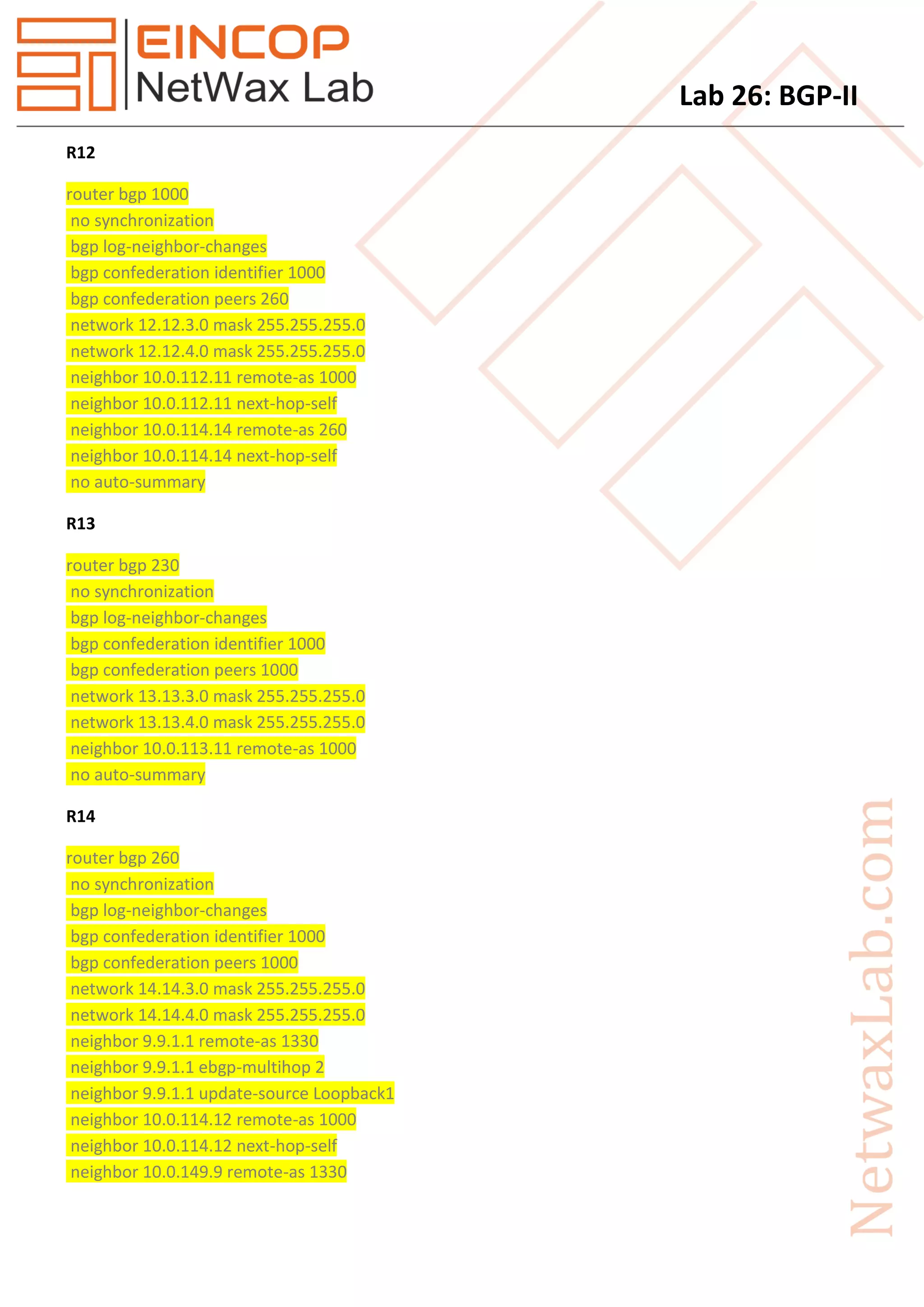
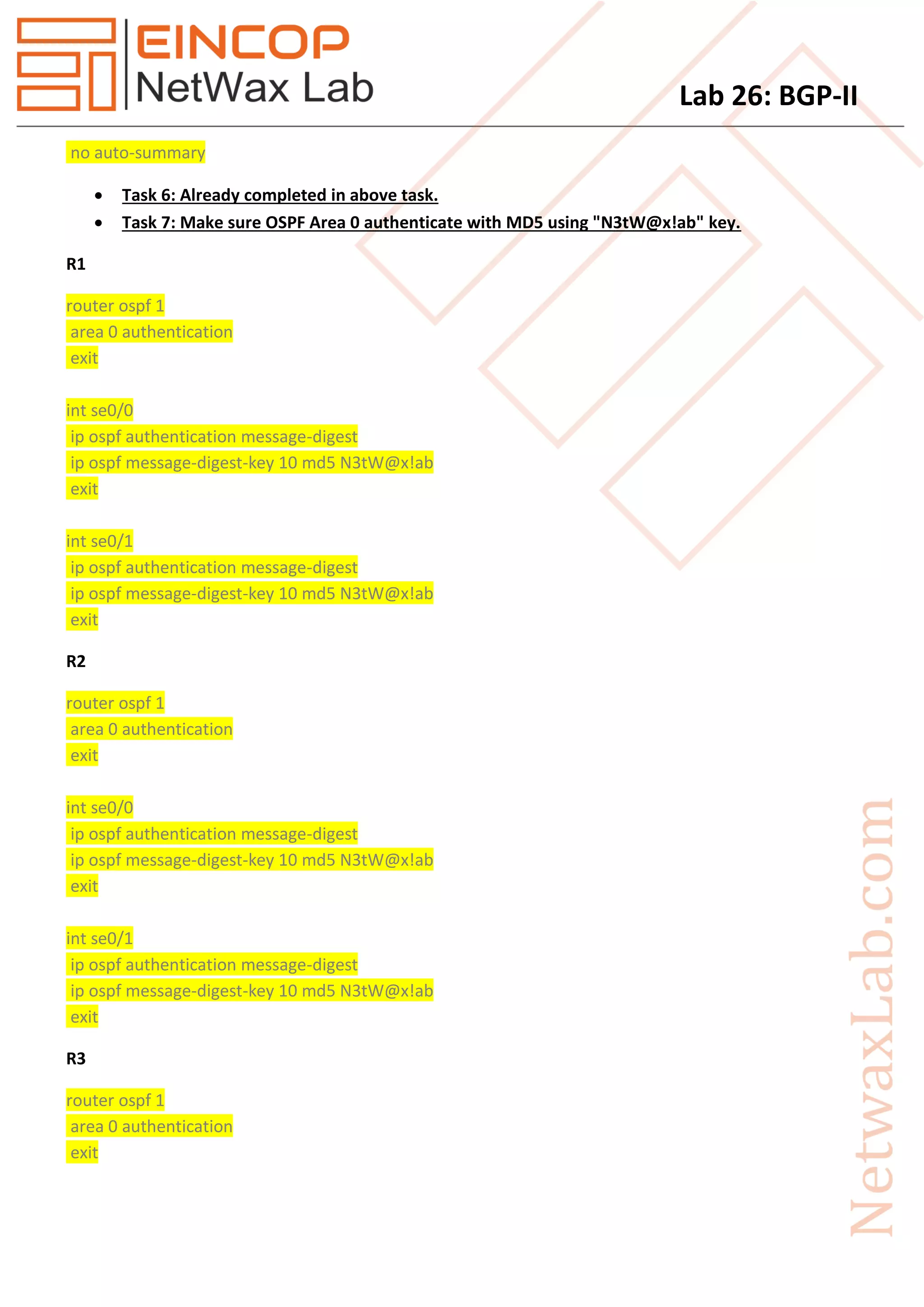
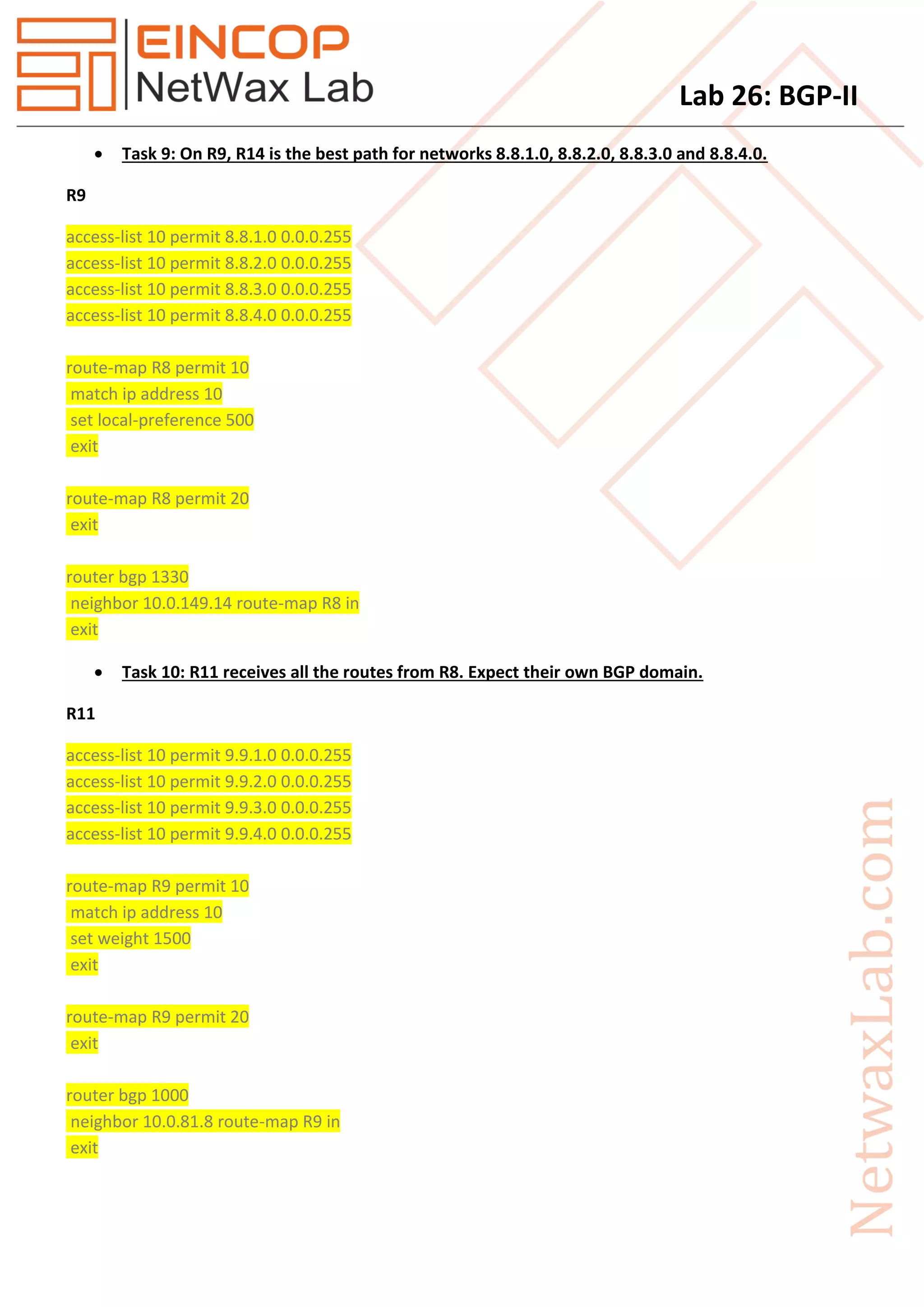
2. Key steps are to configure IBGP between routers R1-R4, HSRP between R5-R6, servers on R6, and BGP routing between all routers as specified in the tasks and topology, including IBGP, EBGP, route reflectors, and BGP confederations.
3. The goal is to verify connectivity between loopbacks and servers across the different BGP and IBGP domains as configured.