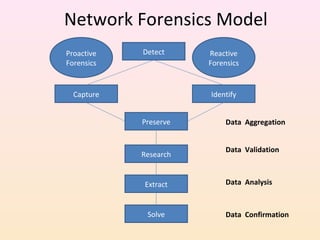
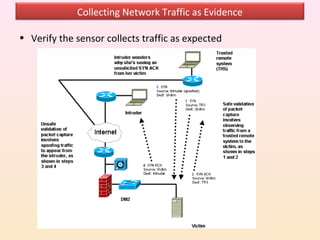
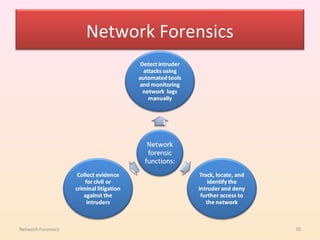
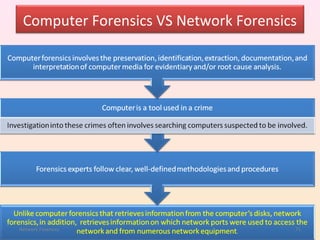
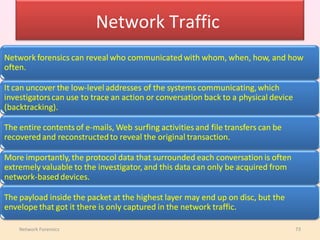
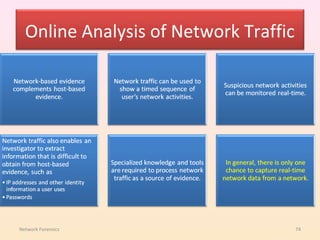
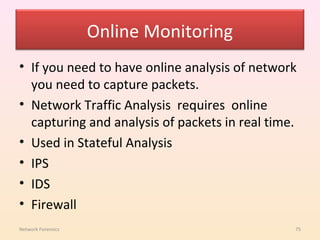
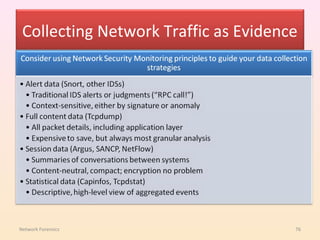
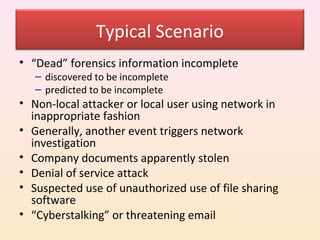
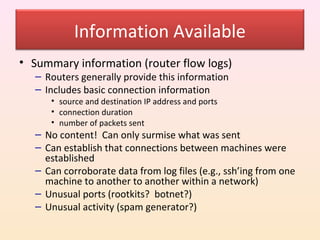
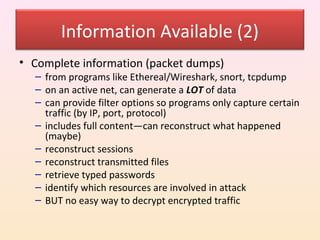
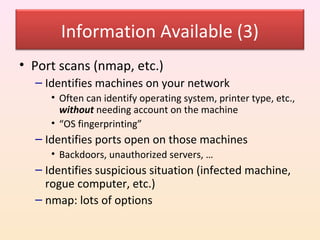
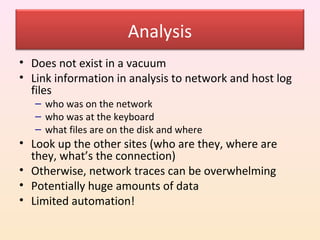
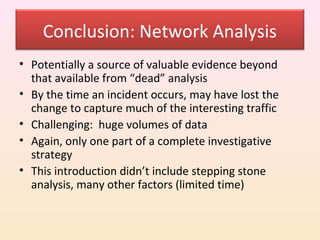
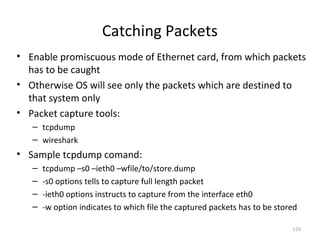
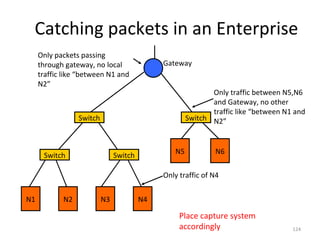
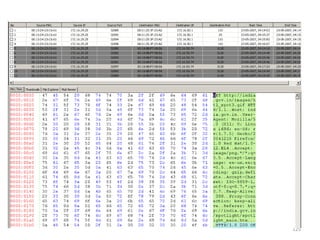
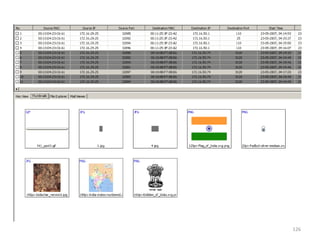
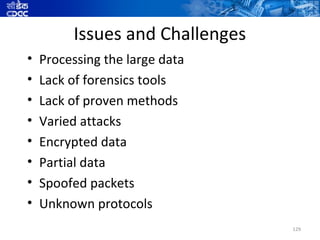
Network forensics is the capture, recording, and analysis of network events and traffic in order to discover the source of security attacks or other problem incidents. It involves systematically capturing and analyzing network traffic and events to trace and prove a network security incident. Network forensics provides crucial network-based evidence that can be used to successfully prosecute criminals. It is a difficult process that depends on maintaining high-quality network information.