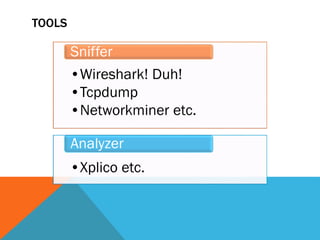
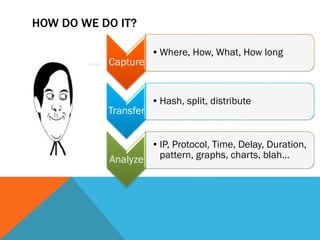
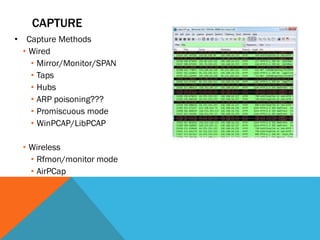
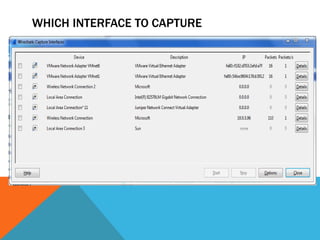
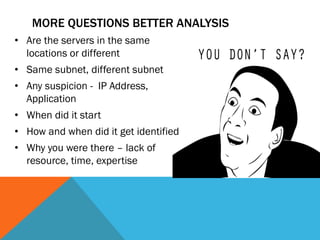
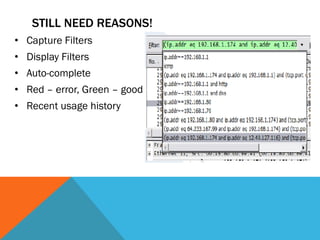
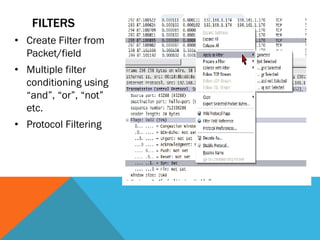
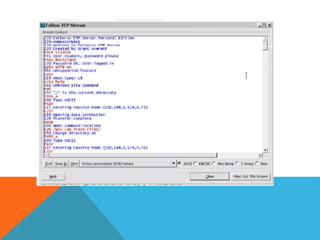
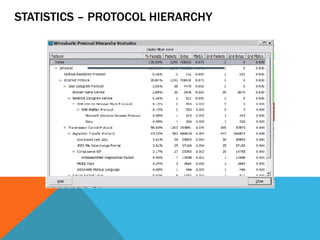
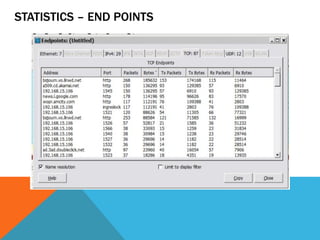
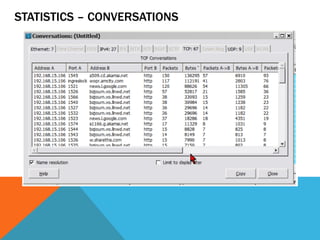
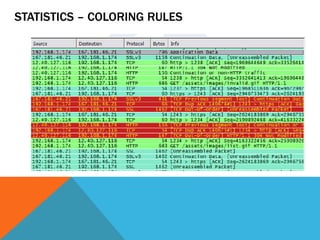
The document is a professional profile of Tamaghna Basu, a senior security engineer and developer specializing in web app security and network penetration testing. It outlines his qualifications, including various certifications, and experience in network forensics, mentioning tools like Wireshark and TCP Dump for packet analysis. The text emphasizes the intricate nature of network forensics and the importance of methodical analysis to uncover hidden data and suspicious activities.