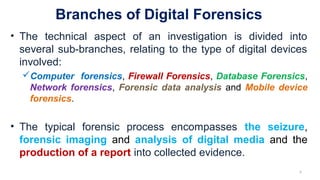
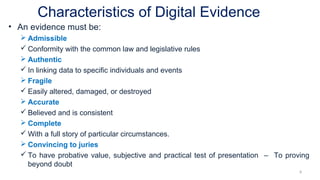
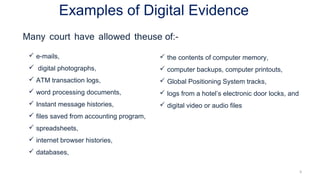
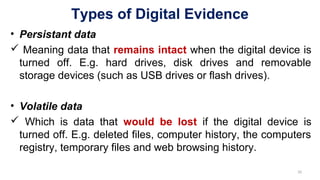
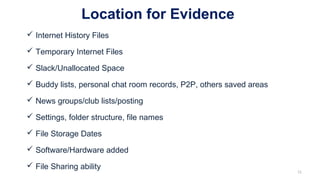
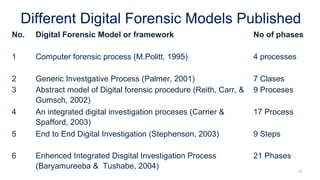
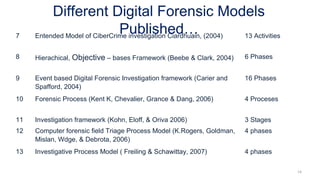
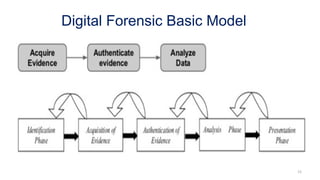
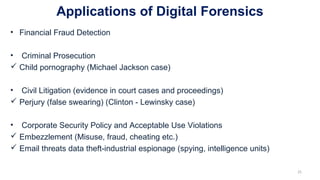
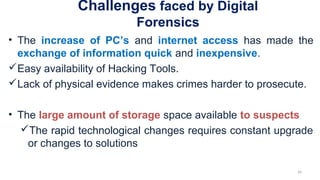
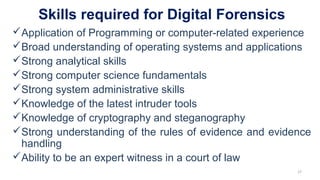
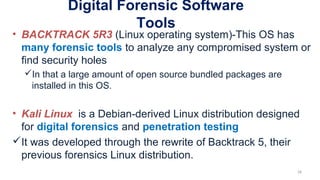
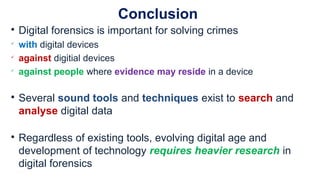
The document provides an overview of digital forensics, defining it as the preservation and analysis of digital evidence to support legal proceedings. Key topics include the digital forensic process, the types and characteristics of digital evidence, applications in crime-solving, and challenges faced in the field. It emphasizes the importance of skilled professionals and various software tools in conducting effective digital forensic investigations.