Embed presentation
Download to read offline


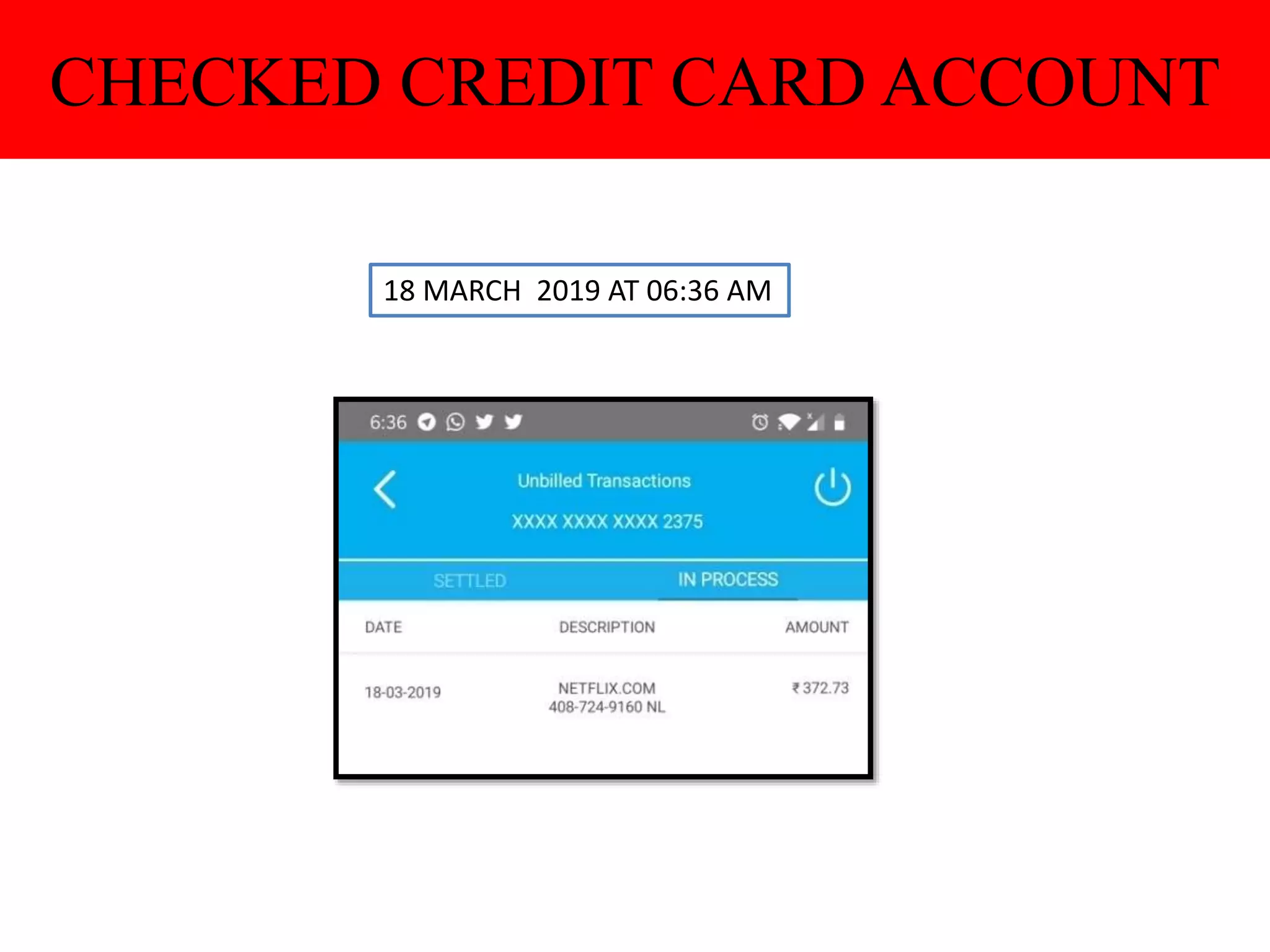



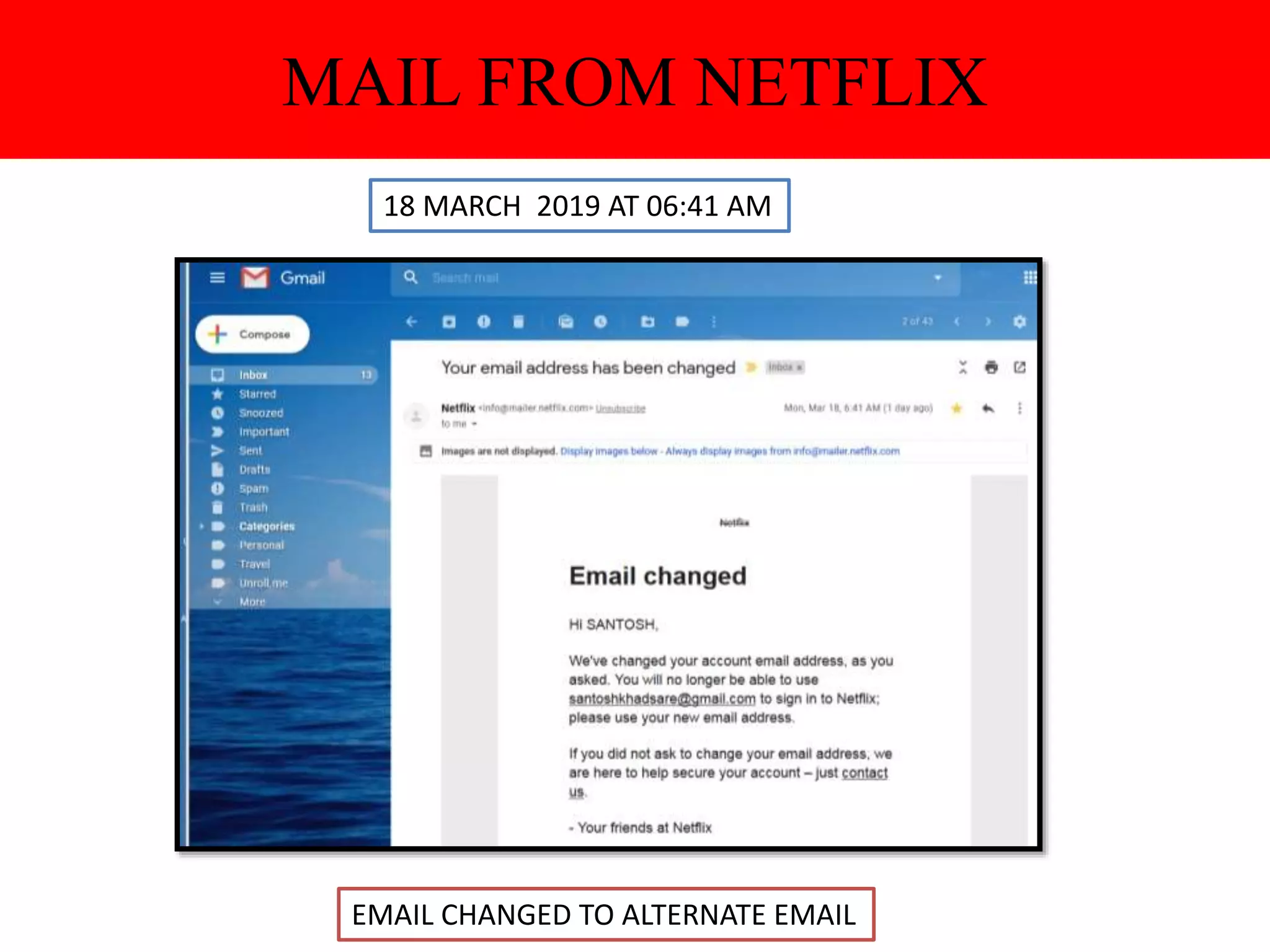



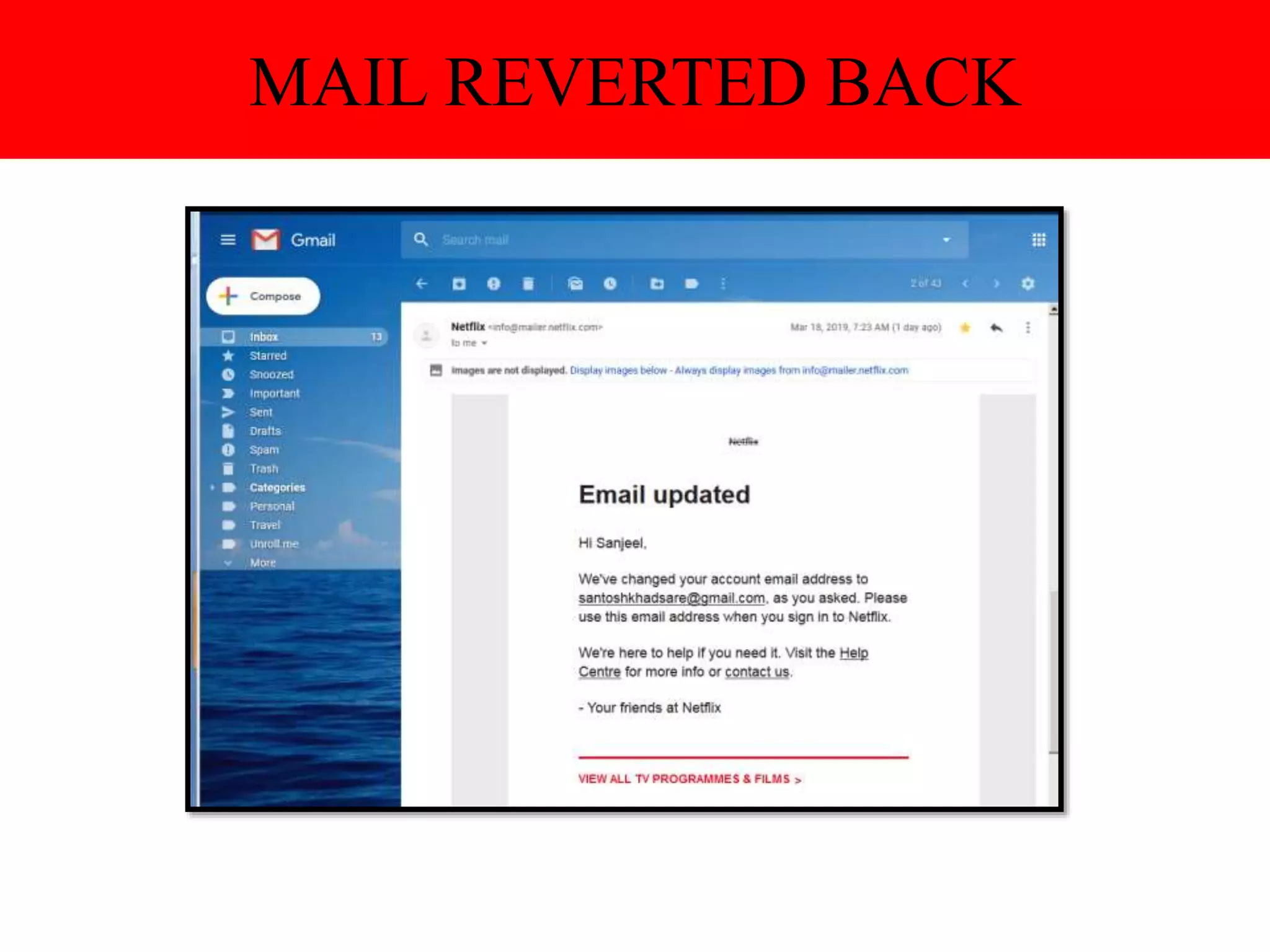



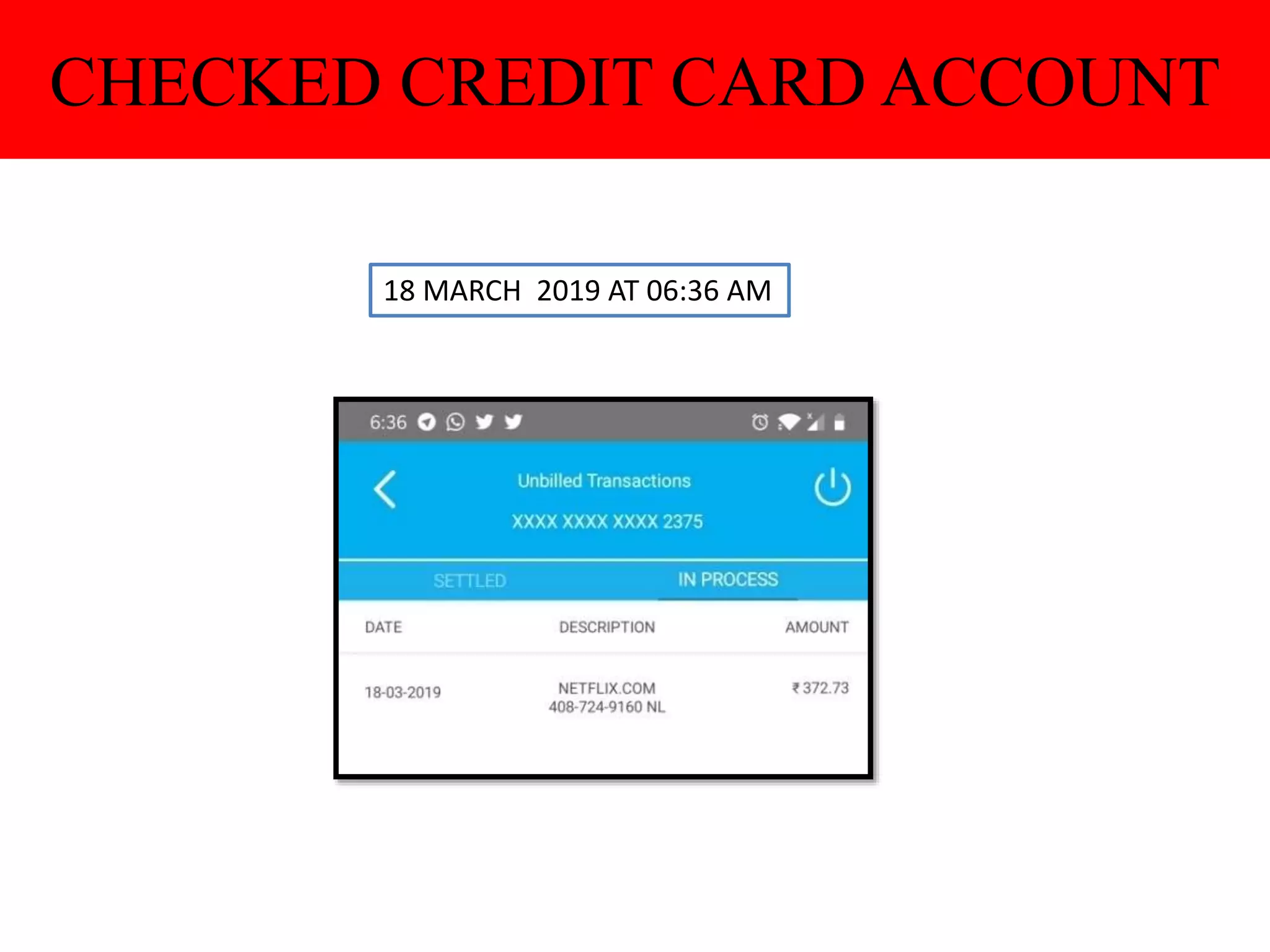
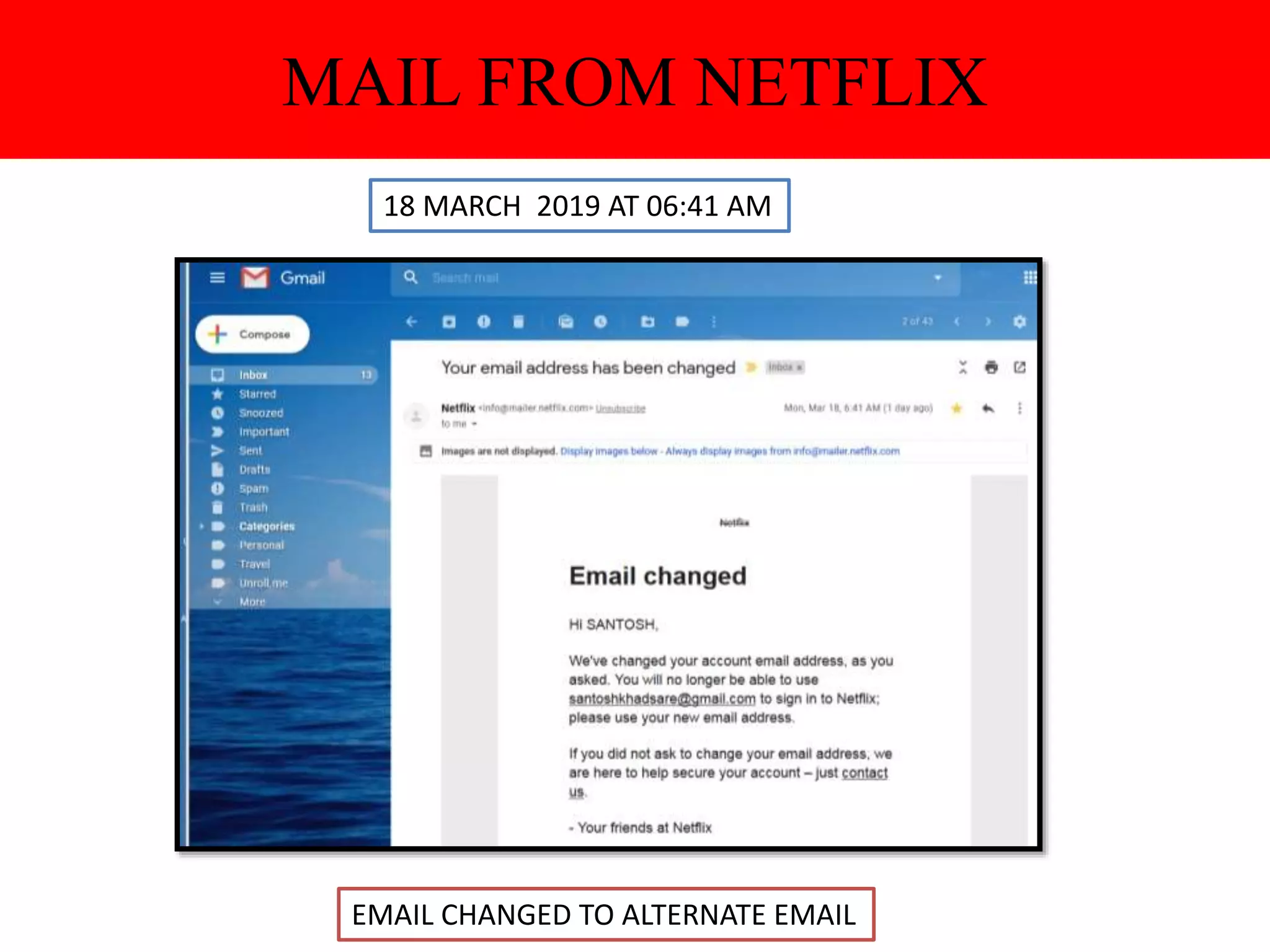
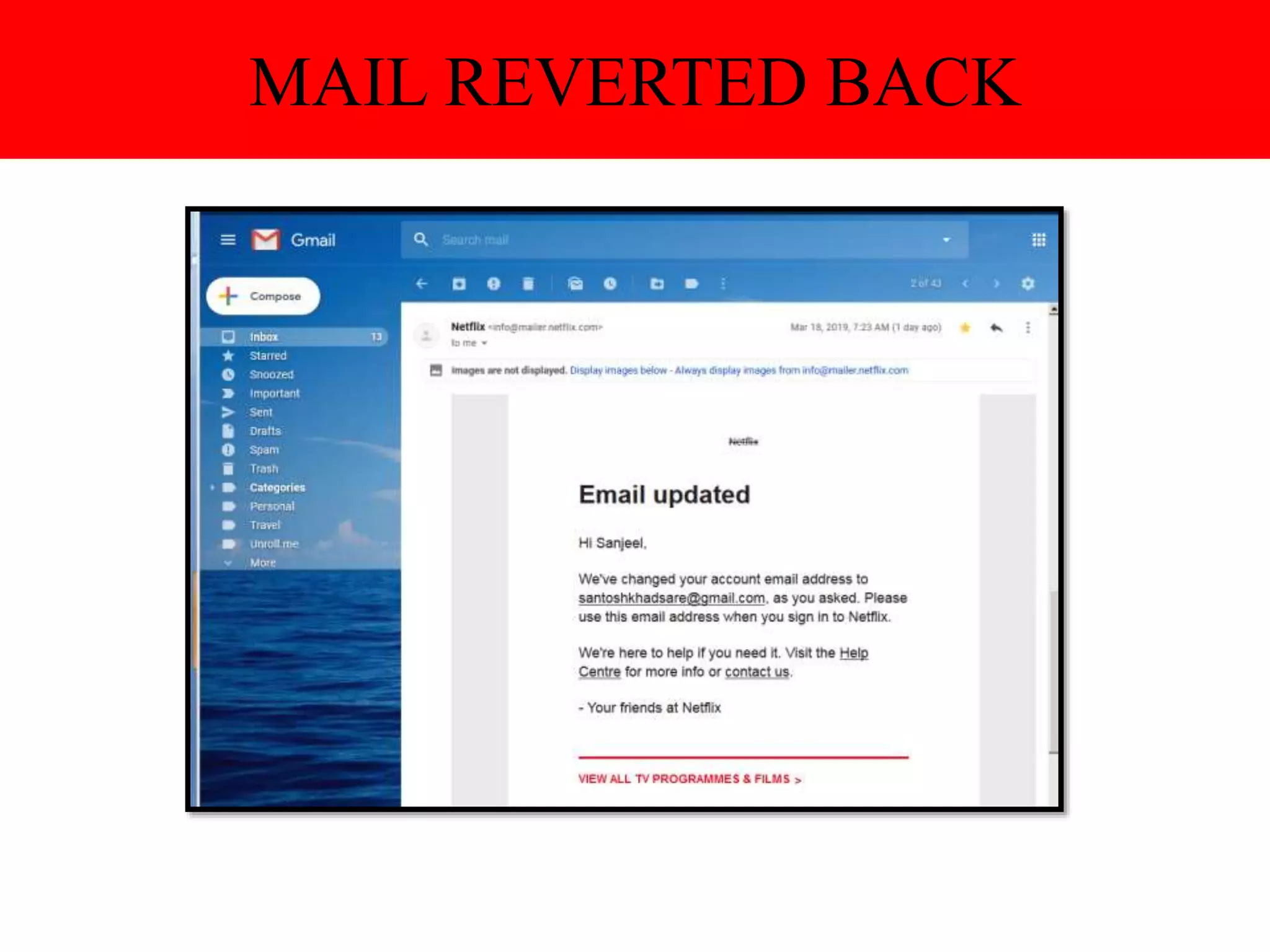
The document outlines a timeline of events on March 18, 2019, involving a victim who experienced credit card fraud related to their Netflix account. The victim received a suspicious email regarding membership renewal and noticed changes to their account, prompting attempts to reset the password and block their credit card. Ultimately, the victim contacted Netflix customer support to resolve the issue and sought a refund.