Embed presentation
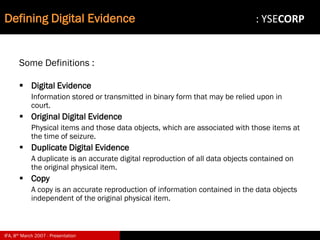
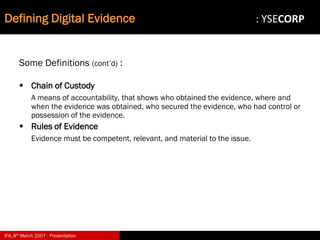
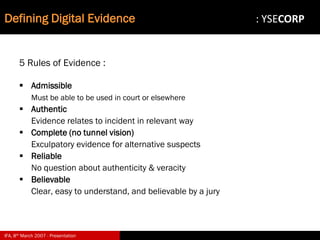
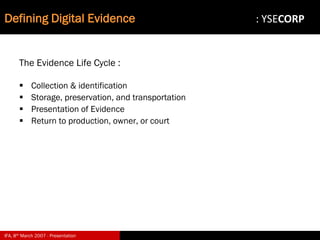
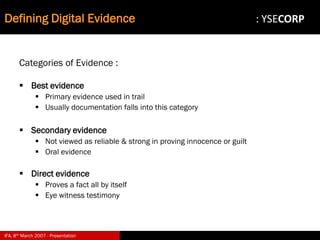
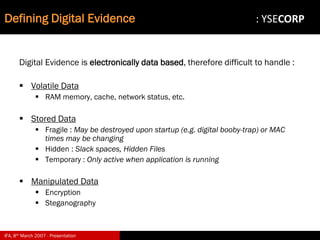
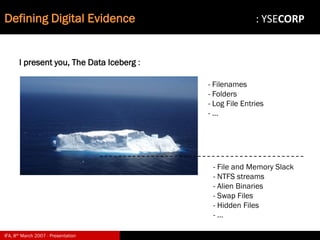
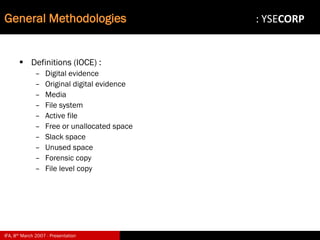
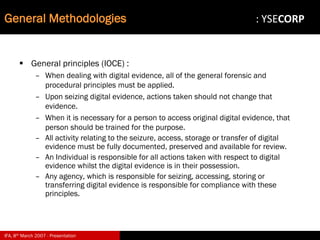
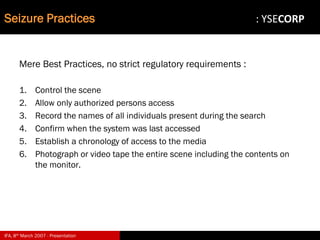
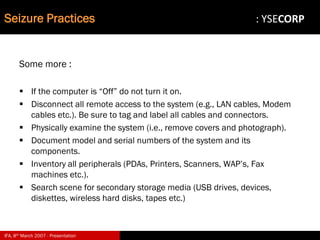
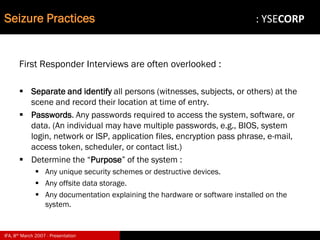
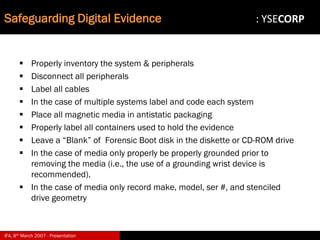
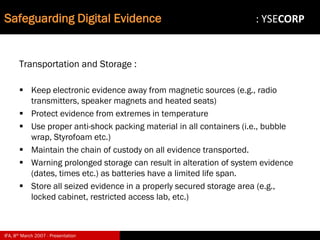
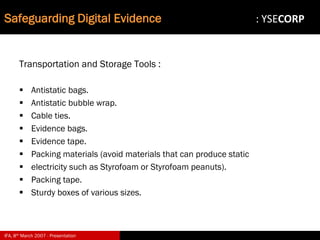

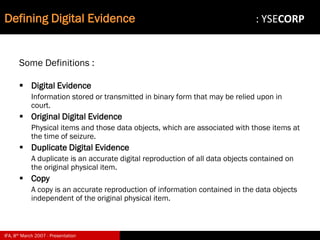
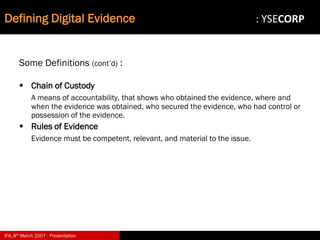
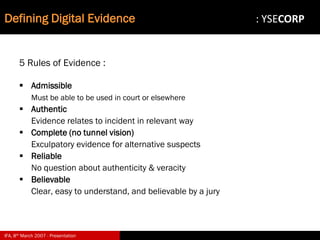
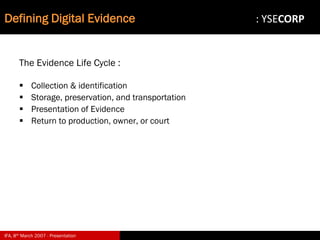
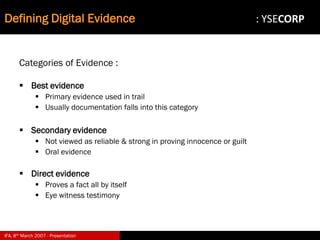
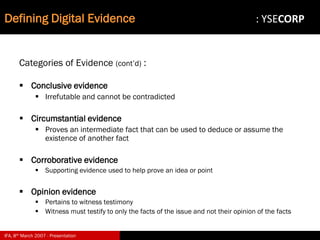
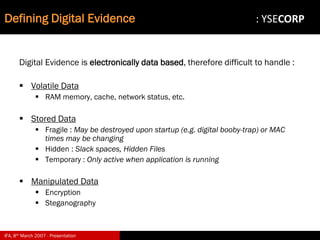
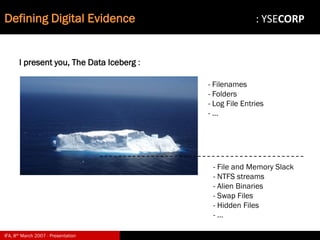
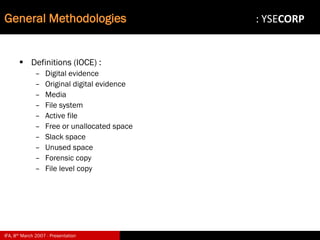
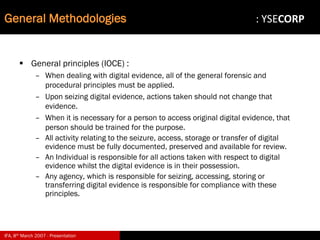
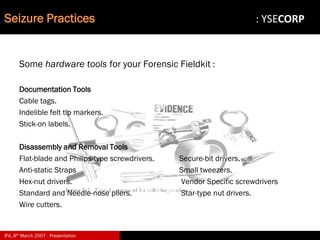
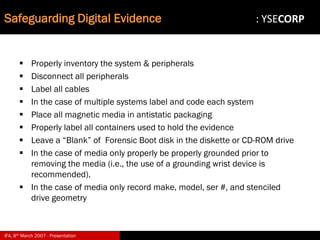
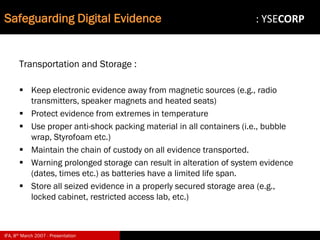
The document discusses digital evidence and its importance in investigations. It defines different types of digital evidence and outlines challenges and best practices for acquiring, handling, and preserving digital evidence. Specifically, it covers defining digital evidence, why it is important, challenges involved, general methodologies including seizure practices and safe acquisition methods, and safeguarding digital evidence. The presentation provides guidance to law enforcement on properly obtaining and securing digital evidence.