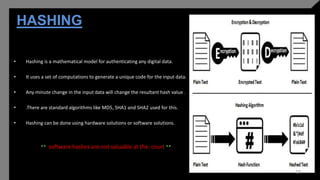
The document presents an overview of digital forensics, contrasting traditional and digital crimes and emphasizing the role of forensics in legal investigations. It details the processes involved in digital forensics, types of cyber attacks, and branches of the discipline, while highlighting tools and challenges faced in the field. The conclusion stresses the importance of digital forensics in addressing crimes related to digital devices and calls for ongoing research to keep up with technological advancements.