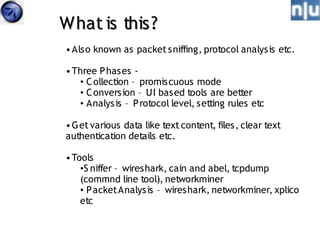
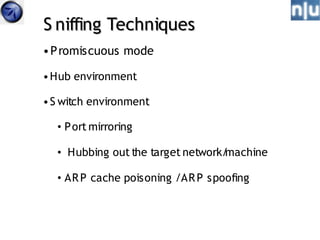
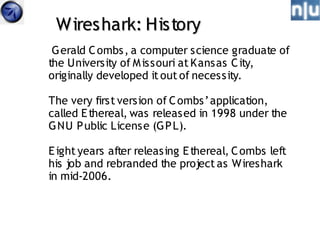
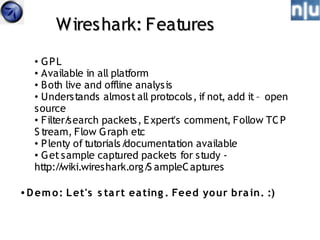
This document provides an overview of network sniffing and packet analysis using Wireshark. It discusses why sniffing is useful for understanding network activity, troubleshooting issues, and performing computer forensics. The document outlines topics like the basic techniques of sniffing, an introduction to Wireshark and its features, analyzing common network protocols, and examples of case studies sniffing could be used for. It emphasizes that patience is a prerequisite and encourages interactive discussion.