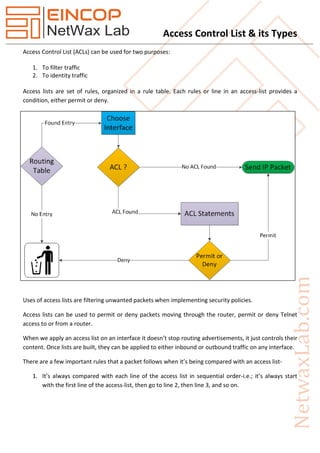
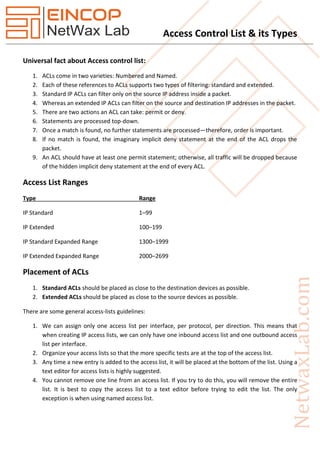
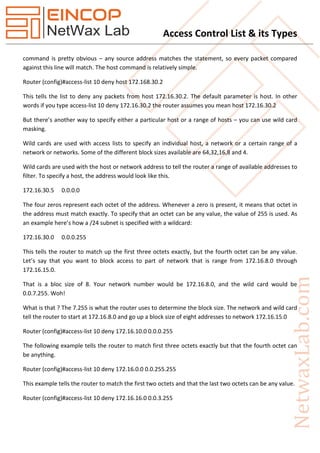
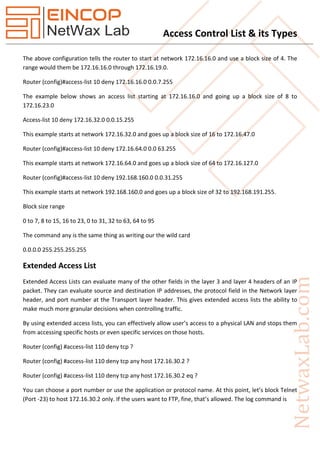
Access Control Lists (ACLs) are rules used to filter and identify traffic in networking by permitting or denying packets based on defined conditions. They come in two types: standard ACLs, which filter by source IP address, and extended ACLs, which can filter by both source and destination addresses and port numbers. Key operational rules include sequential processing of ACL lines, the importance of at least one permit statement, and the need to apply ACLs to specific interfaces for them to be effective.