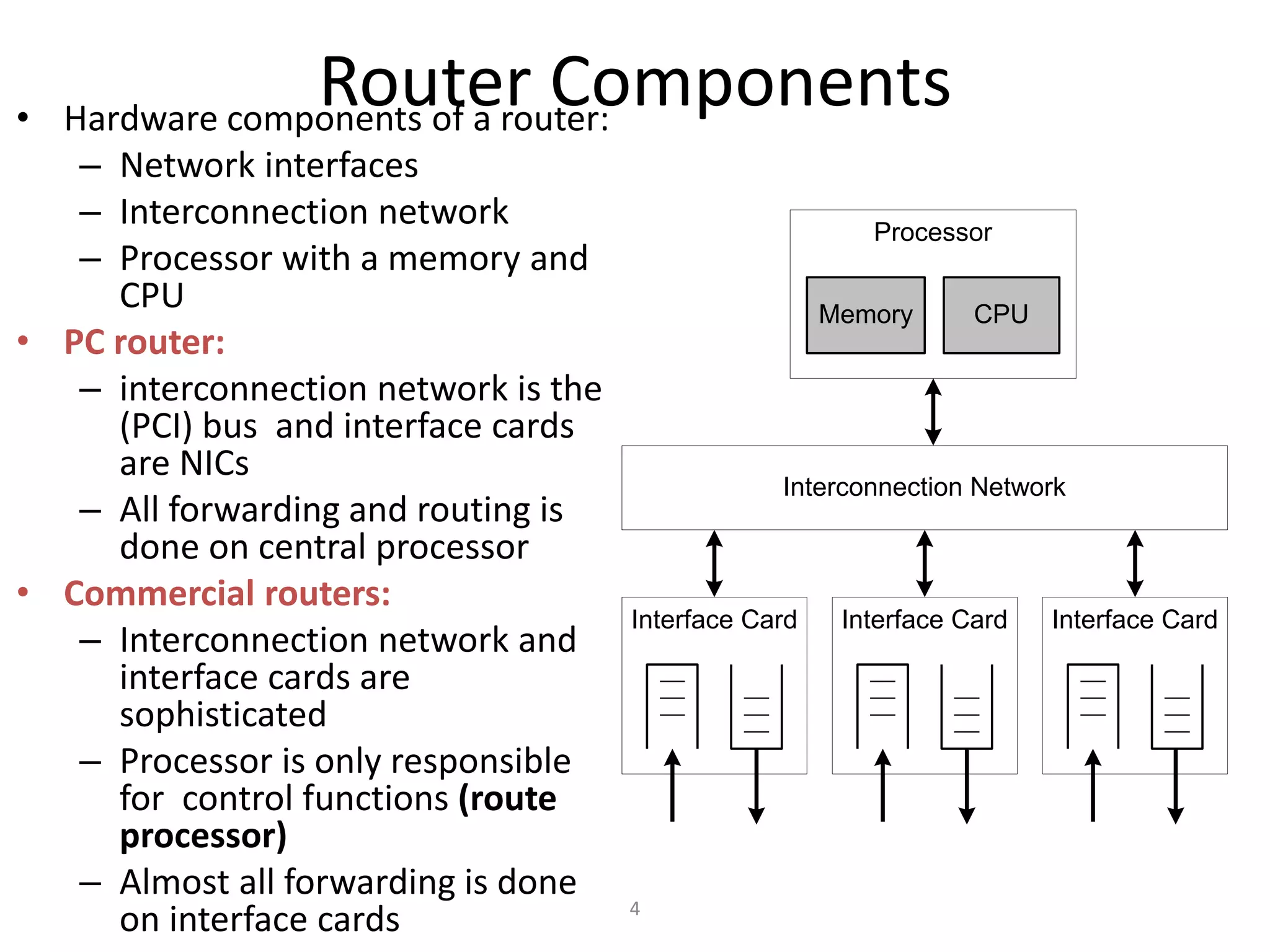
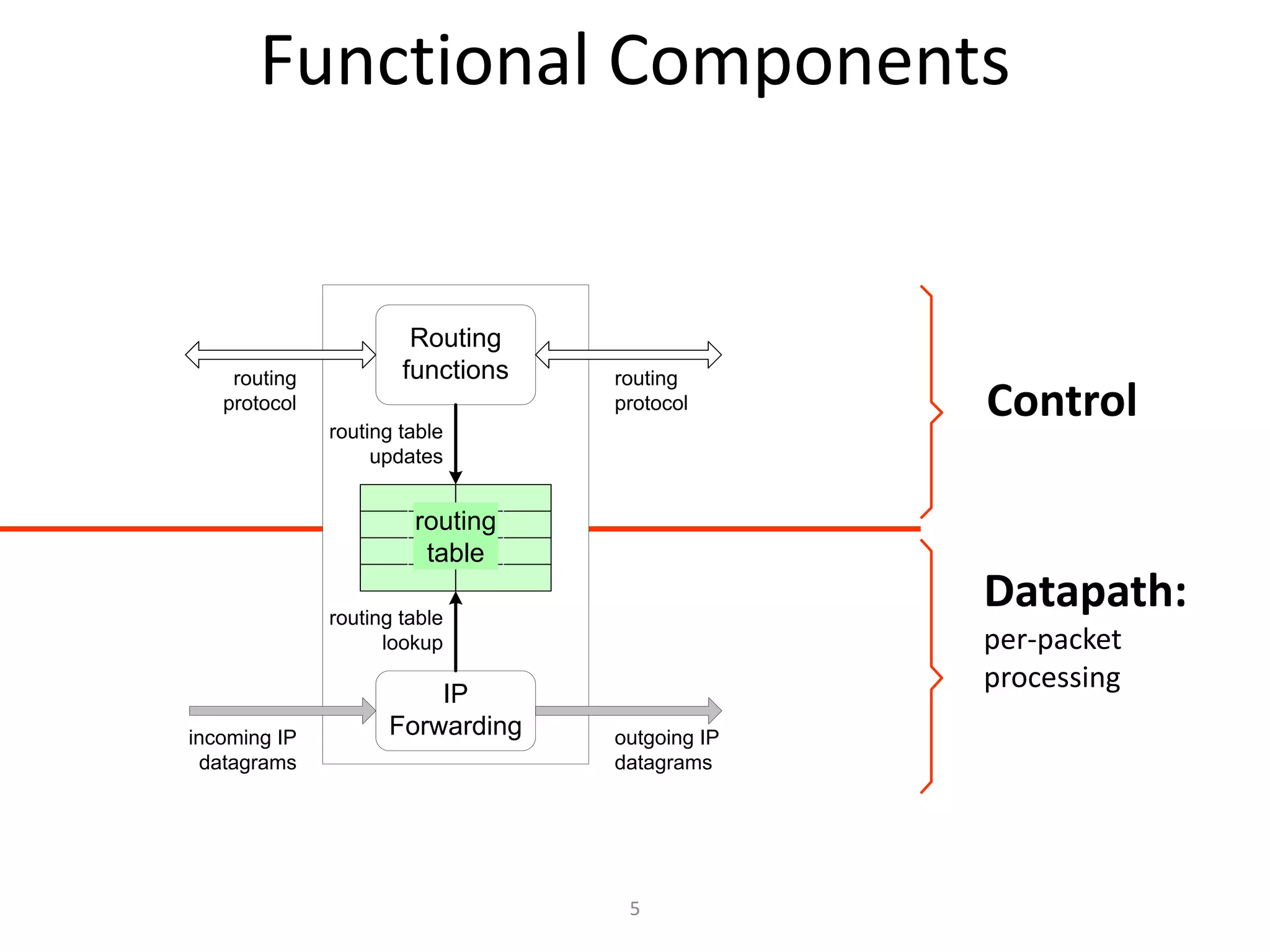
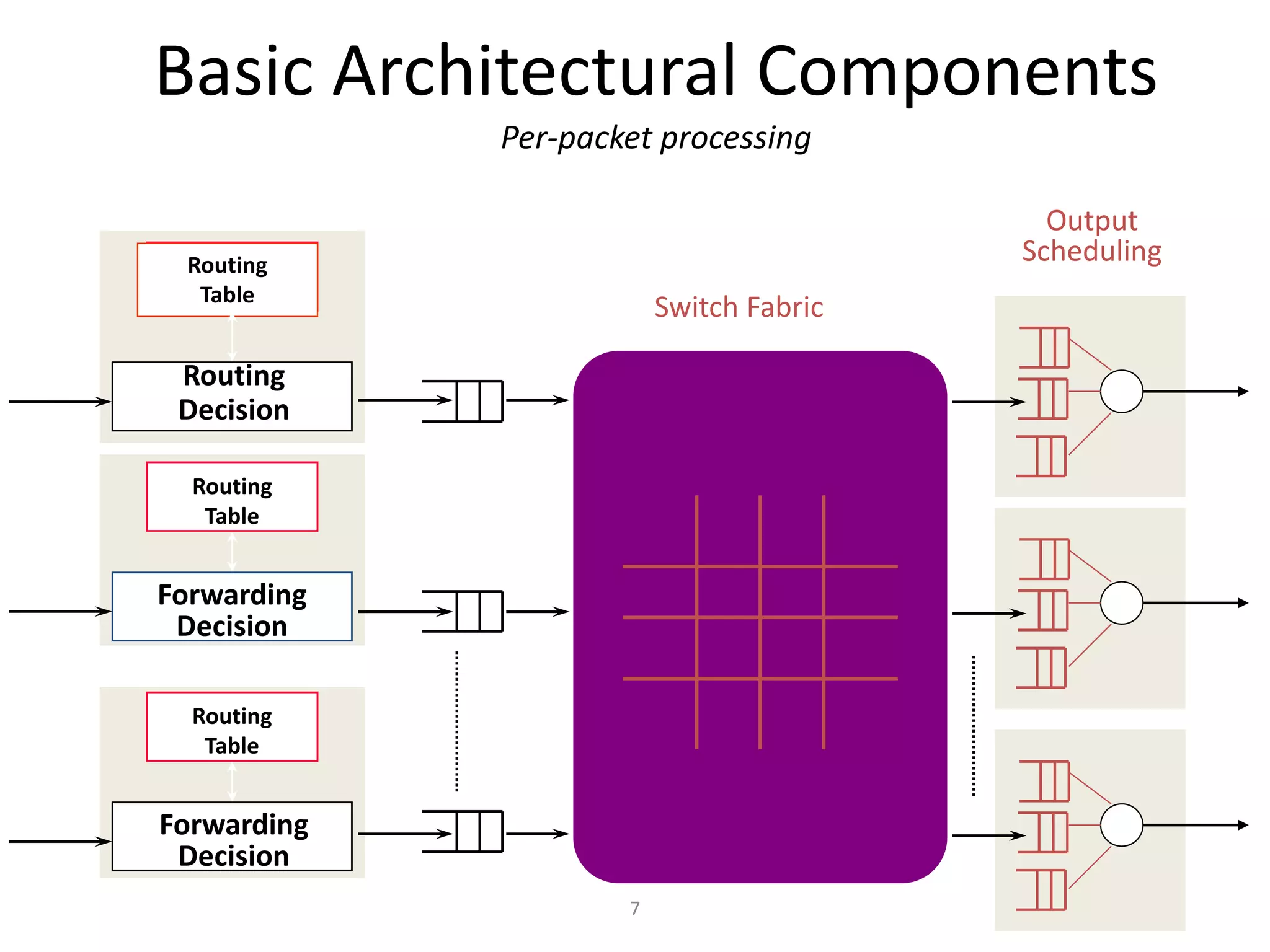
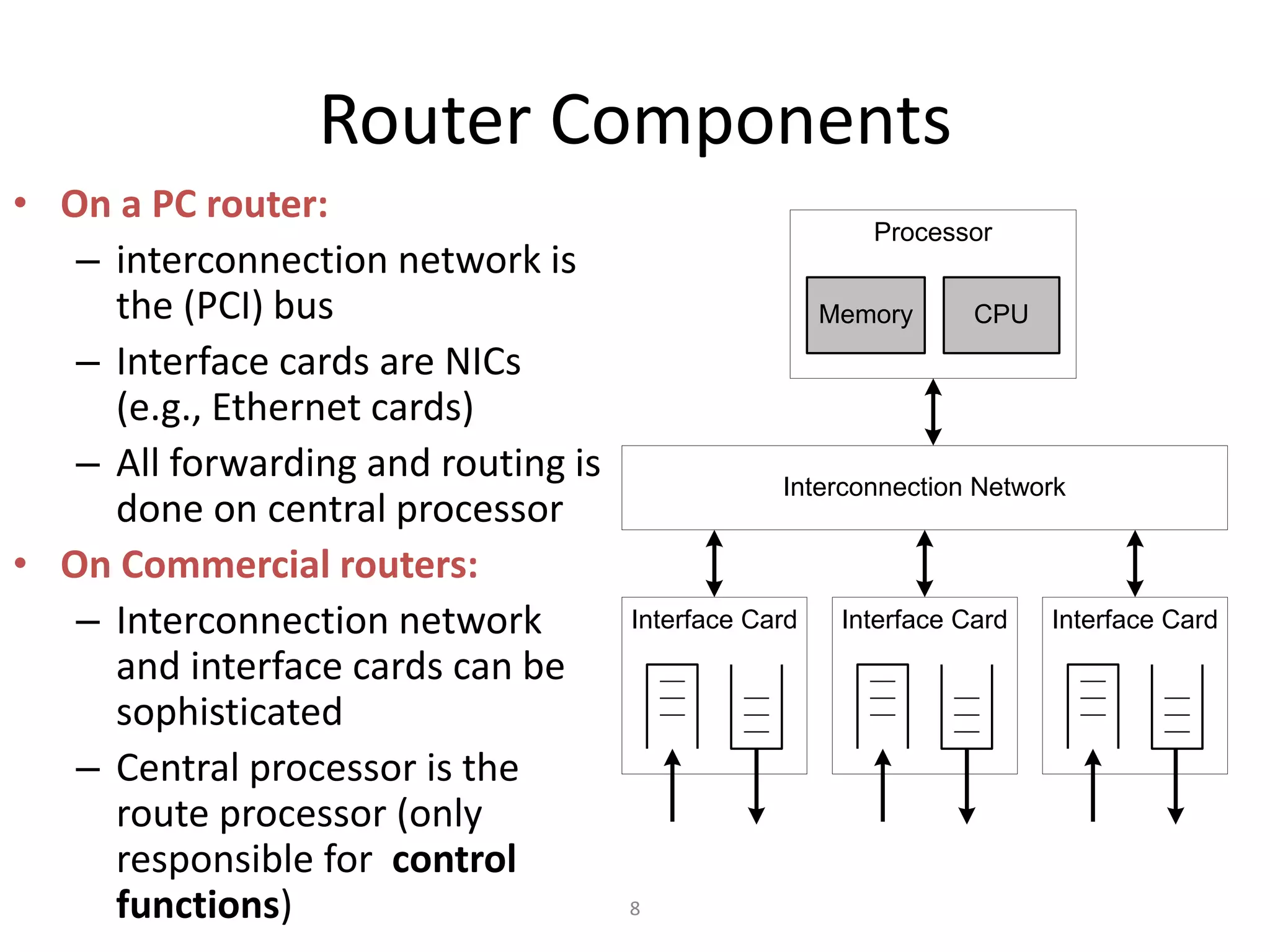
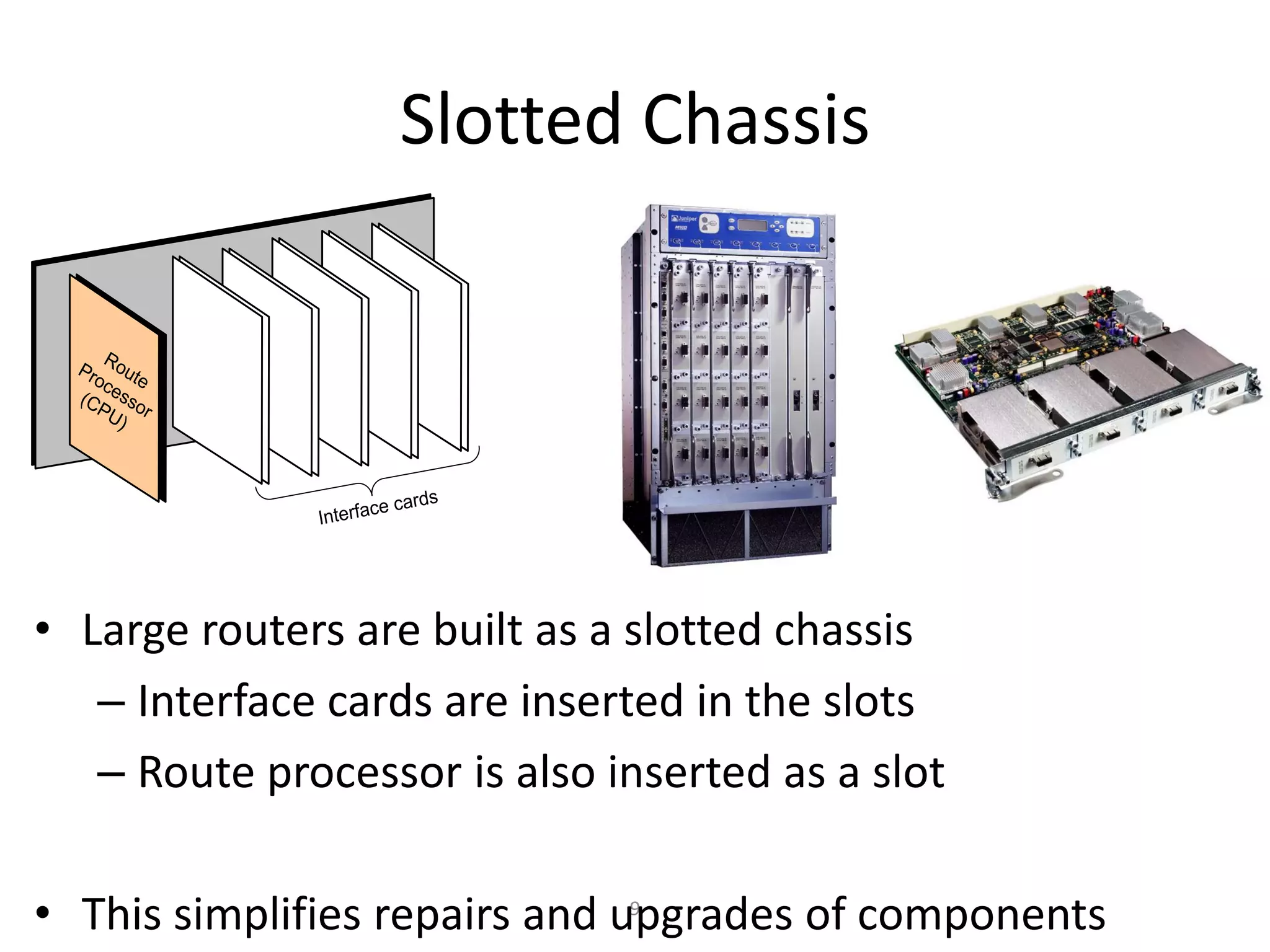
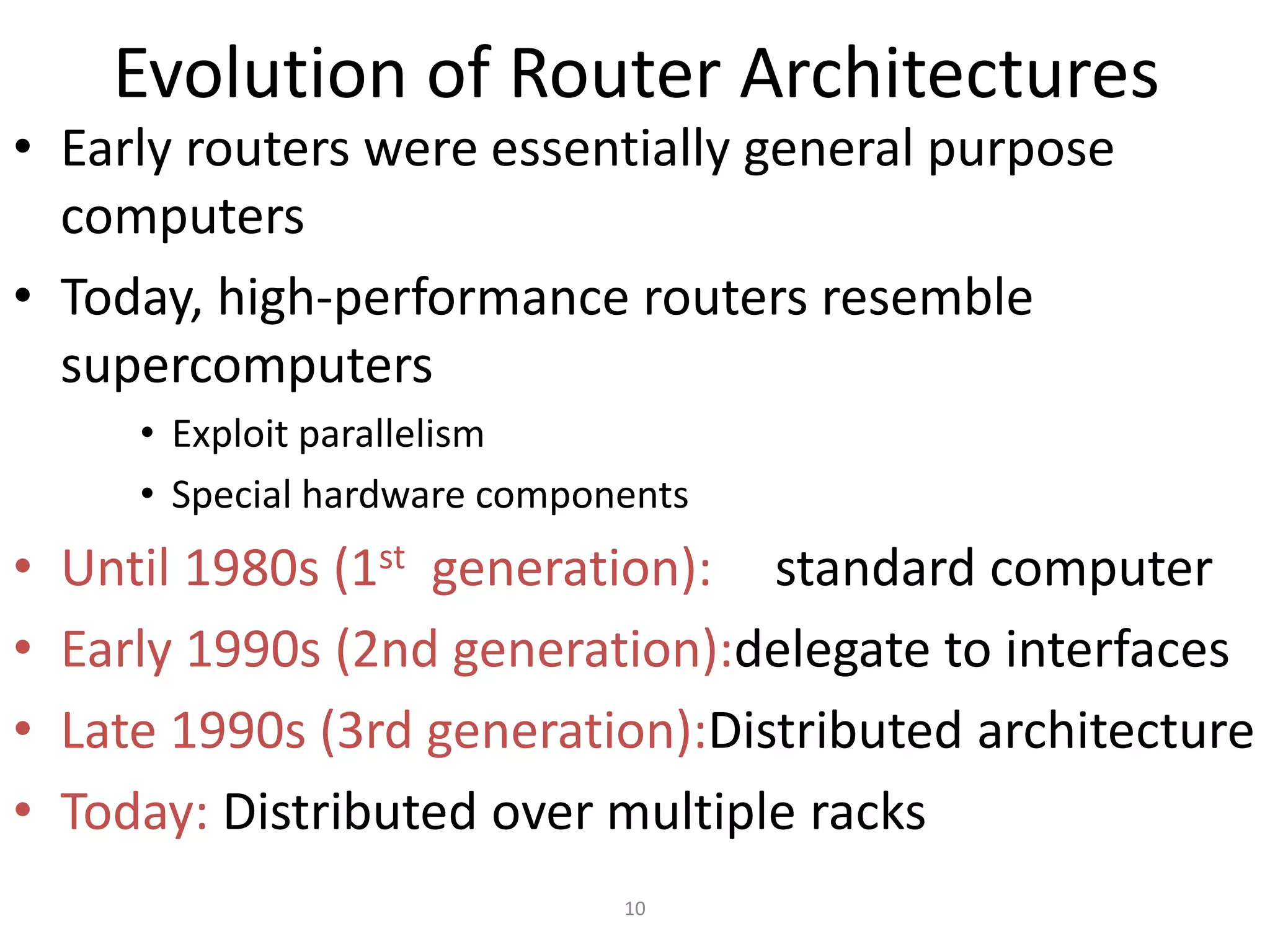
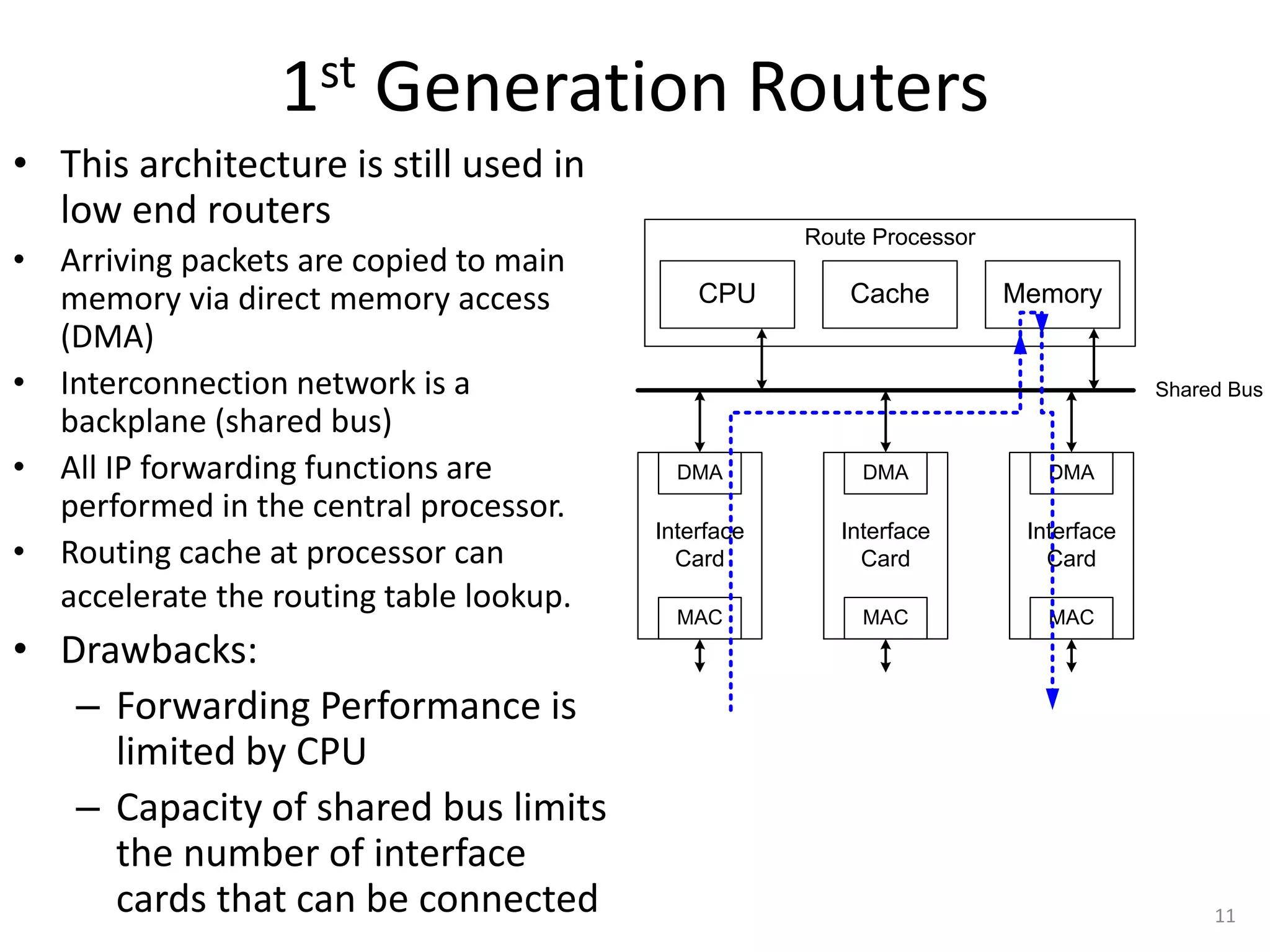
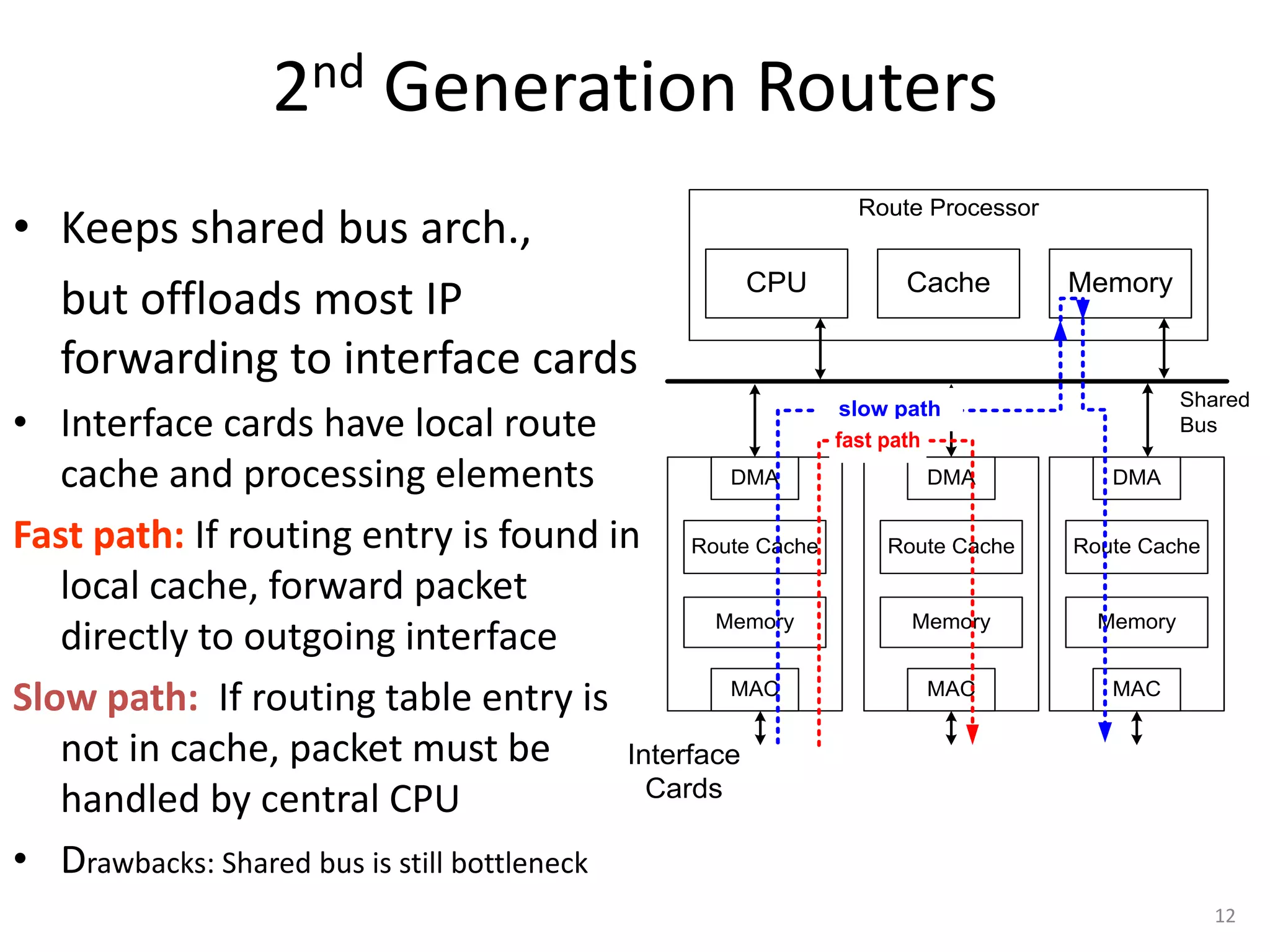
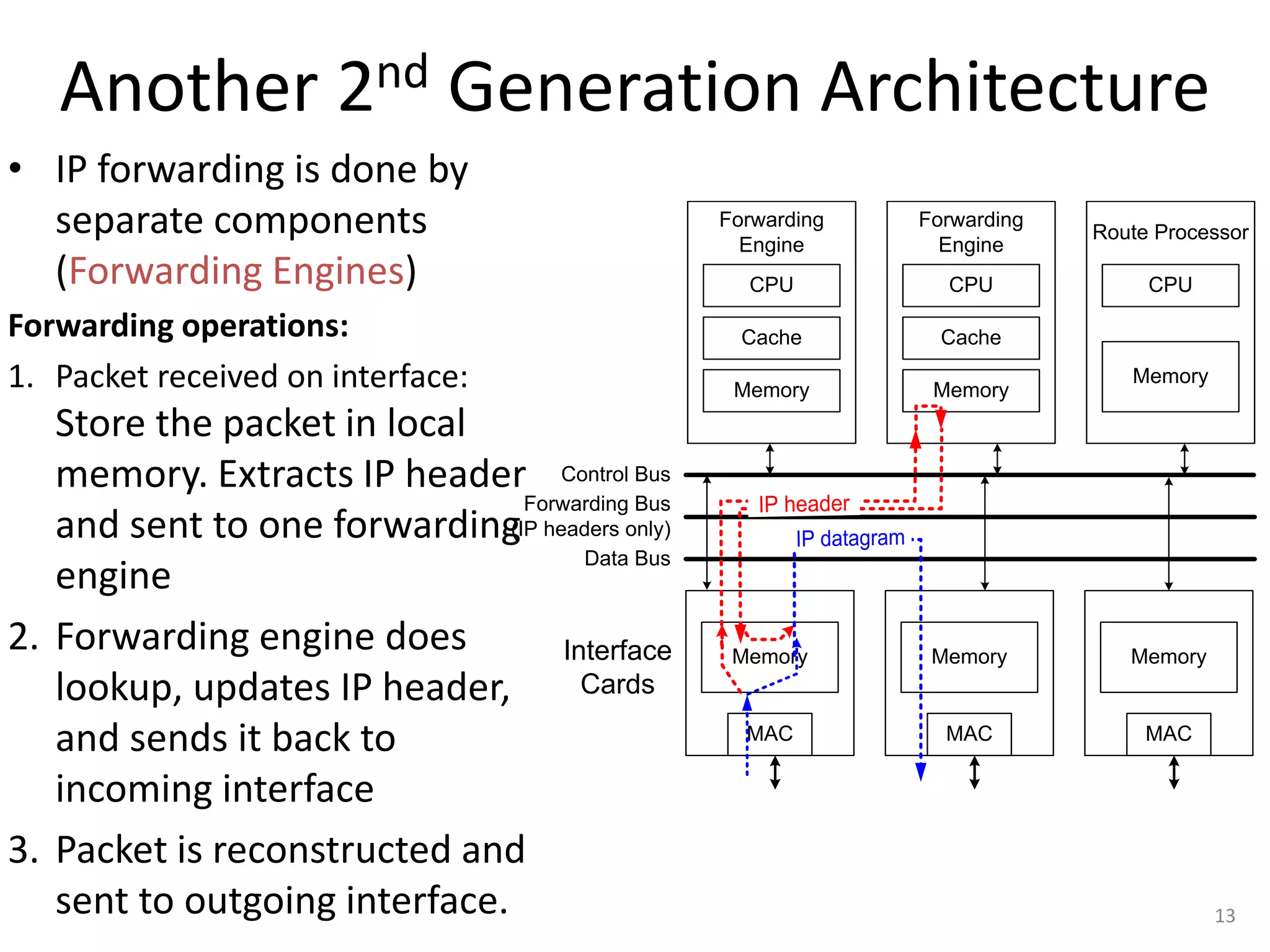
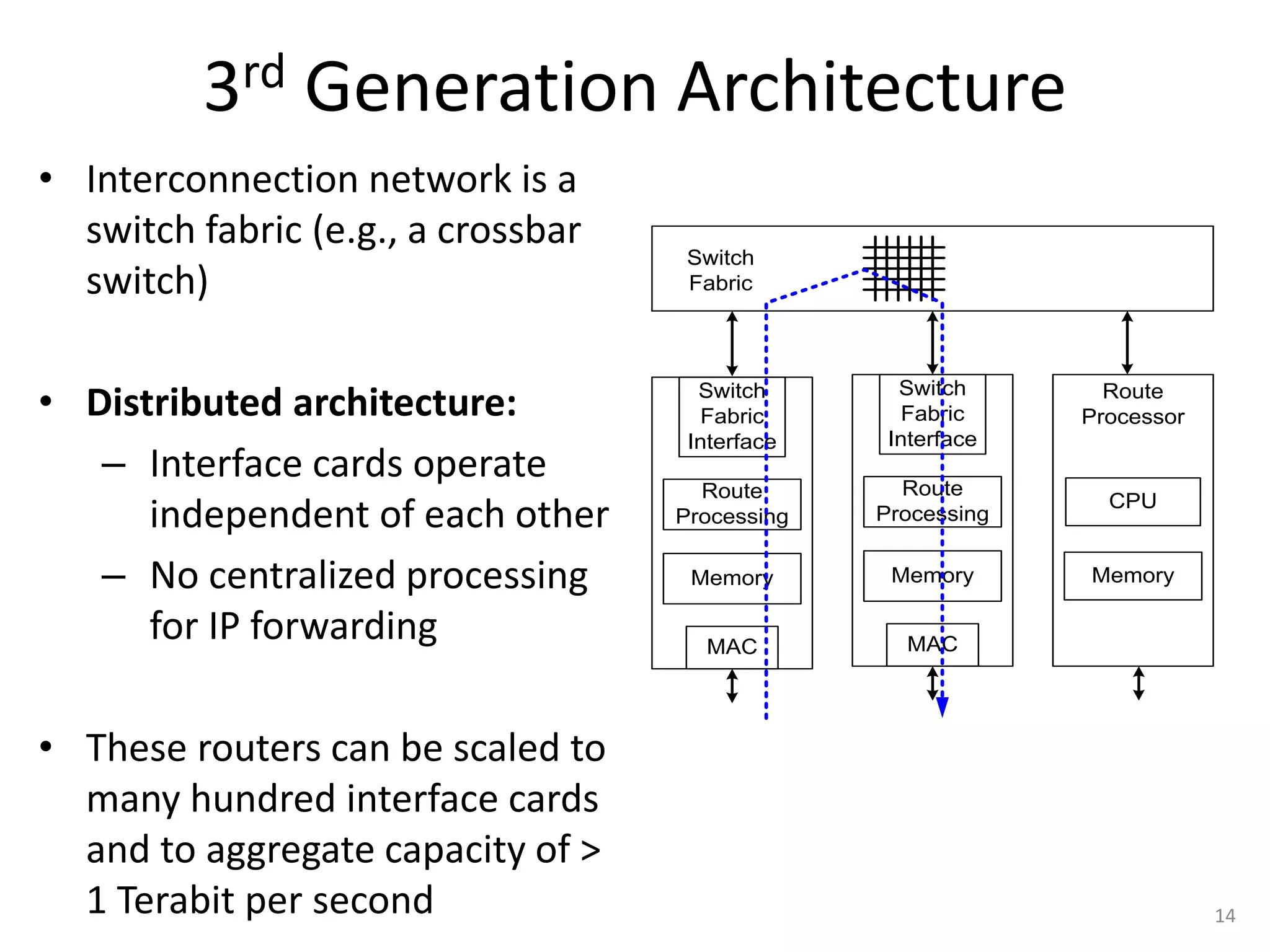
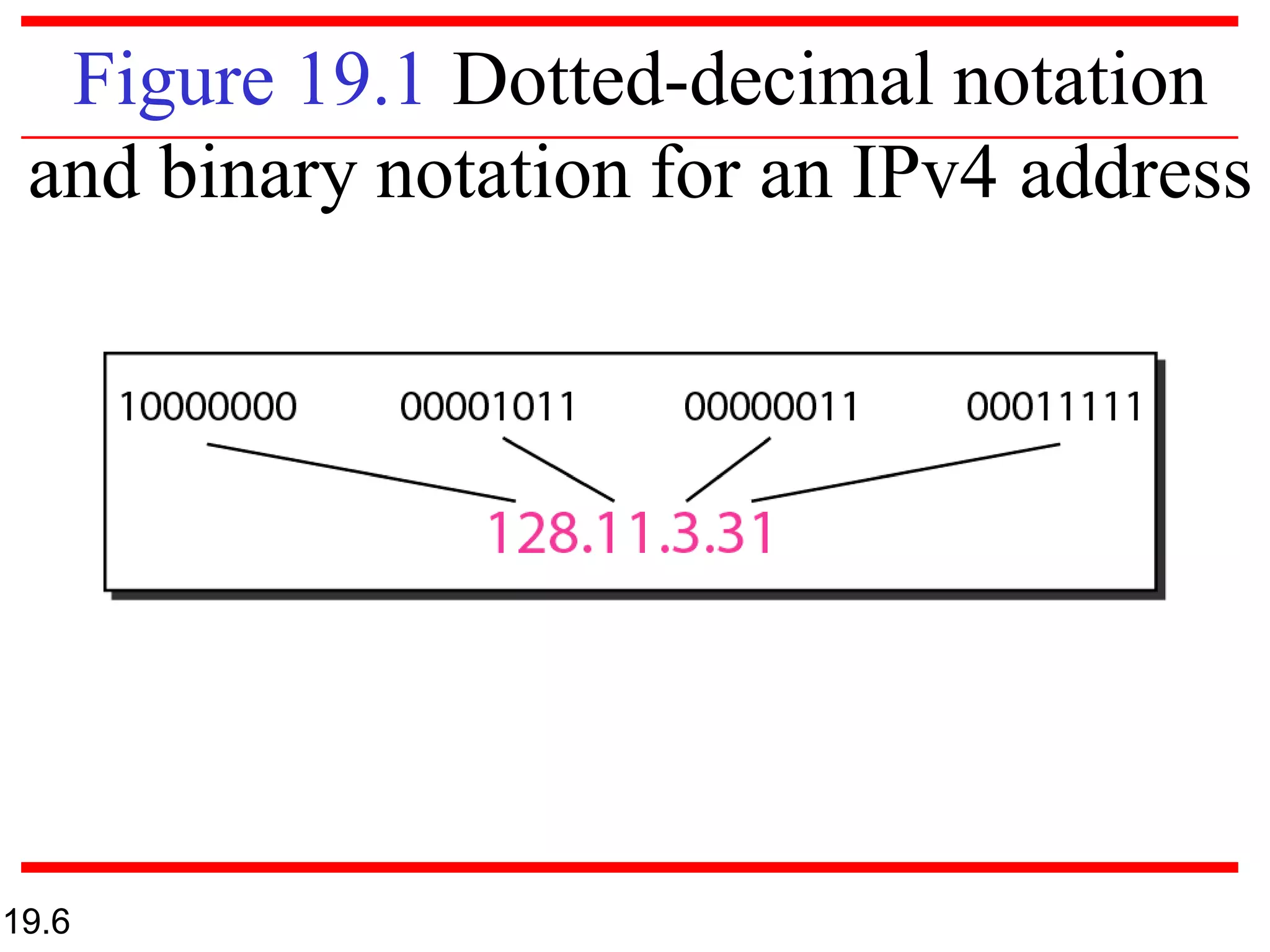
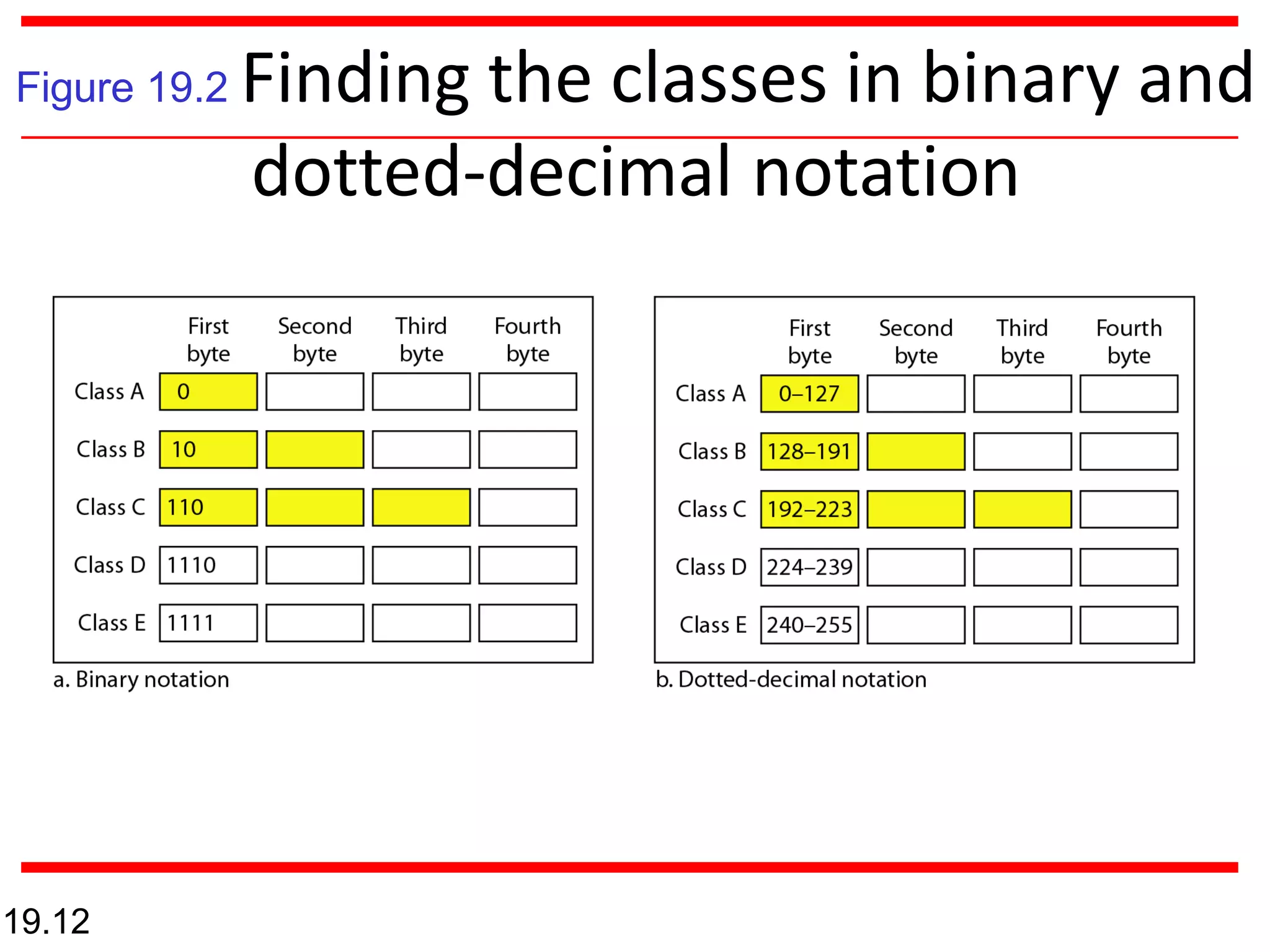
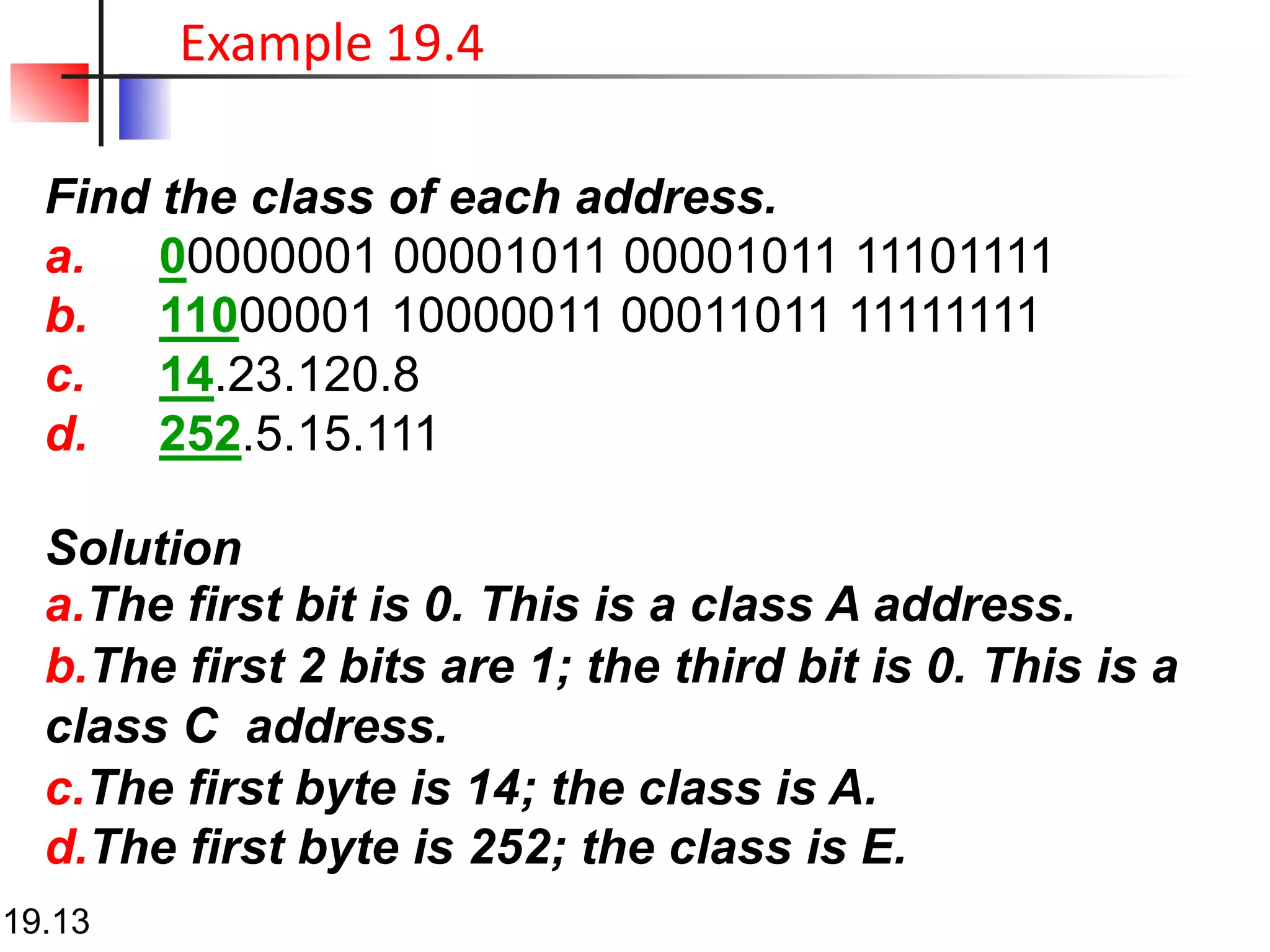
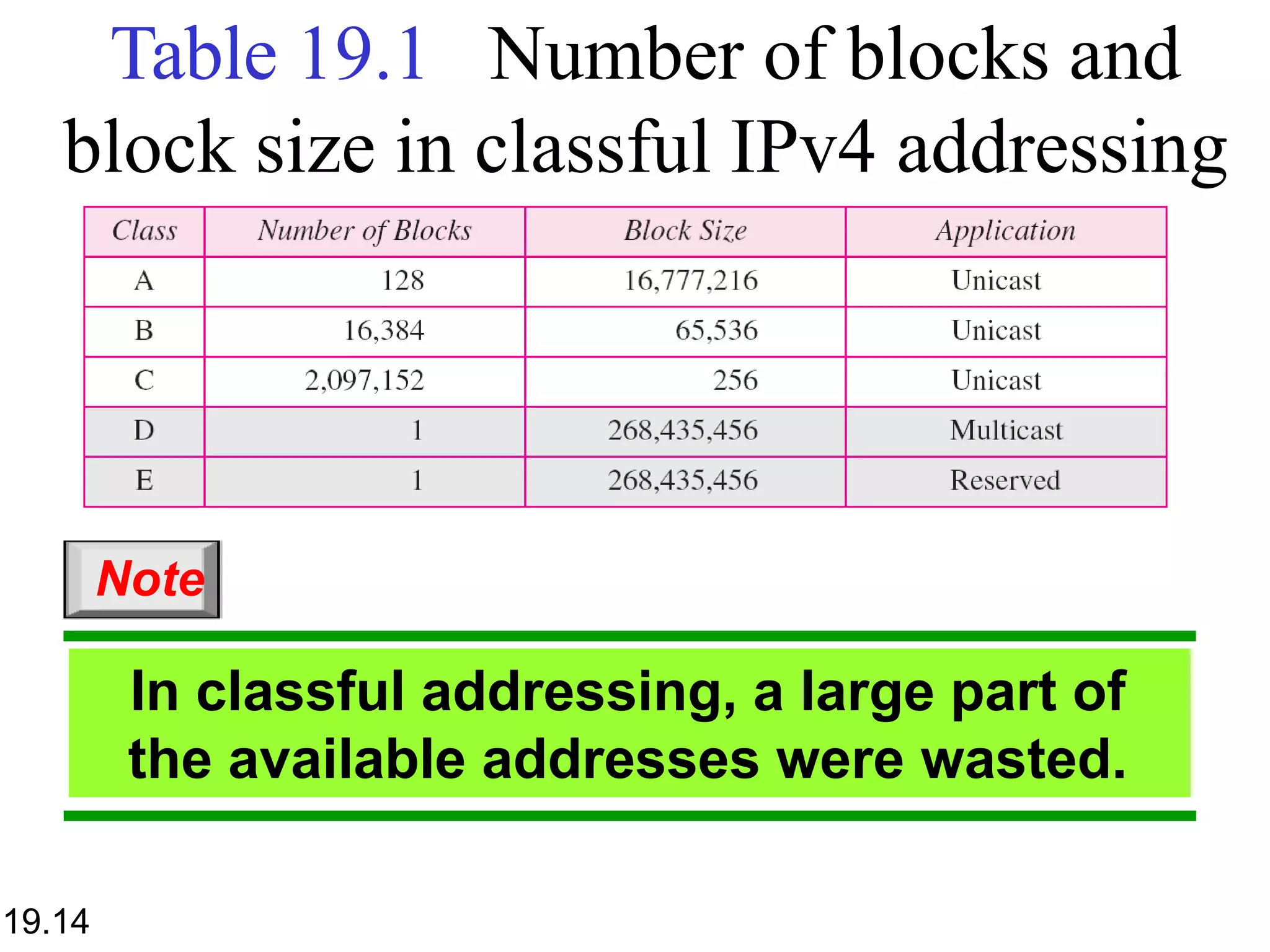
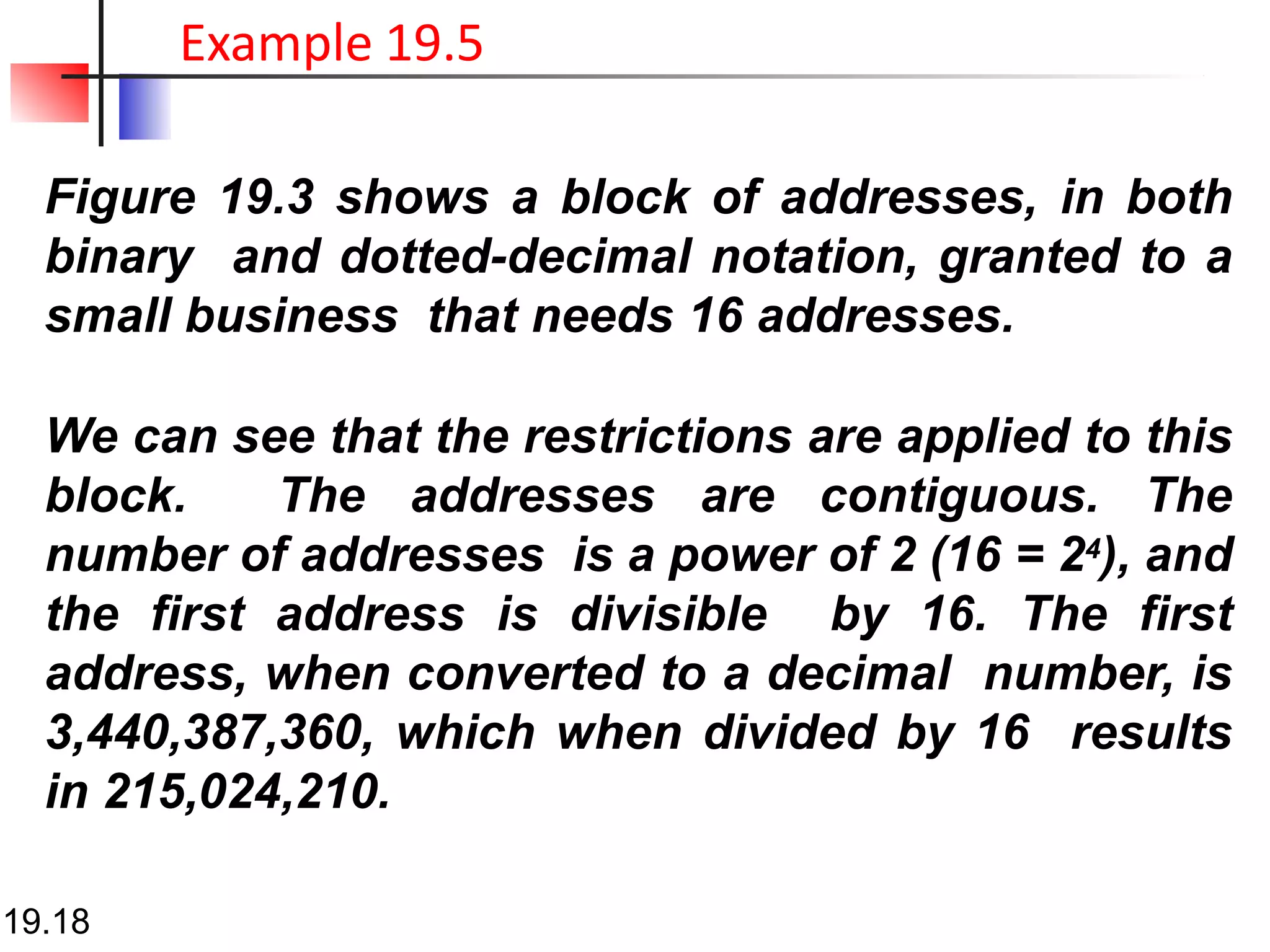
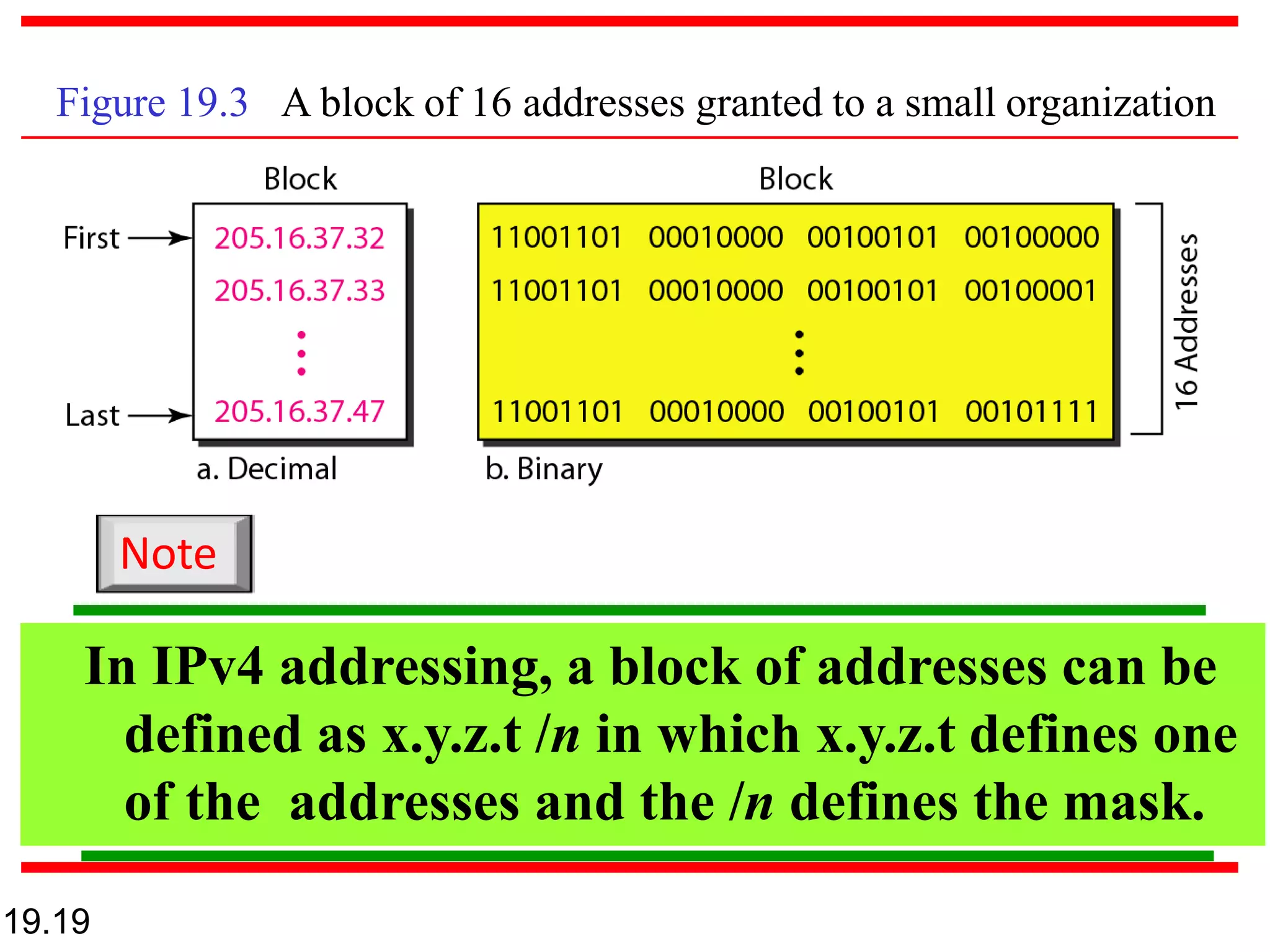
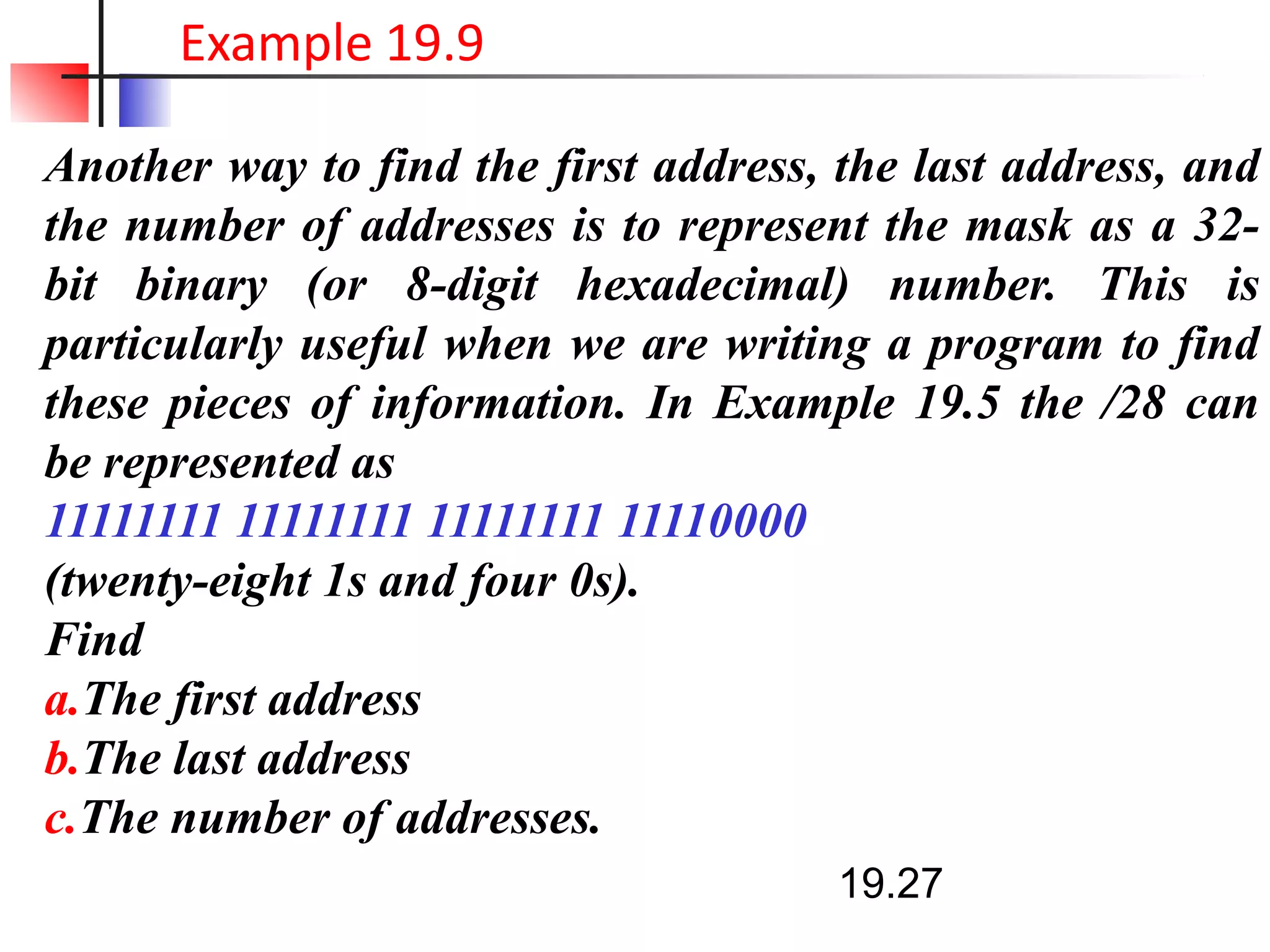
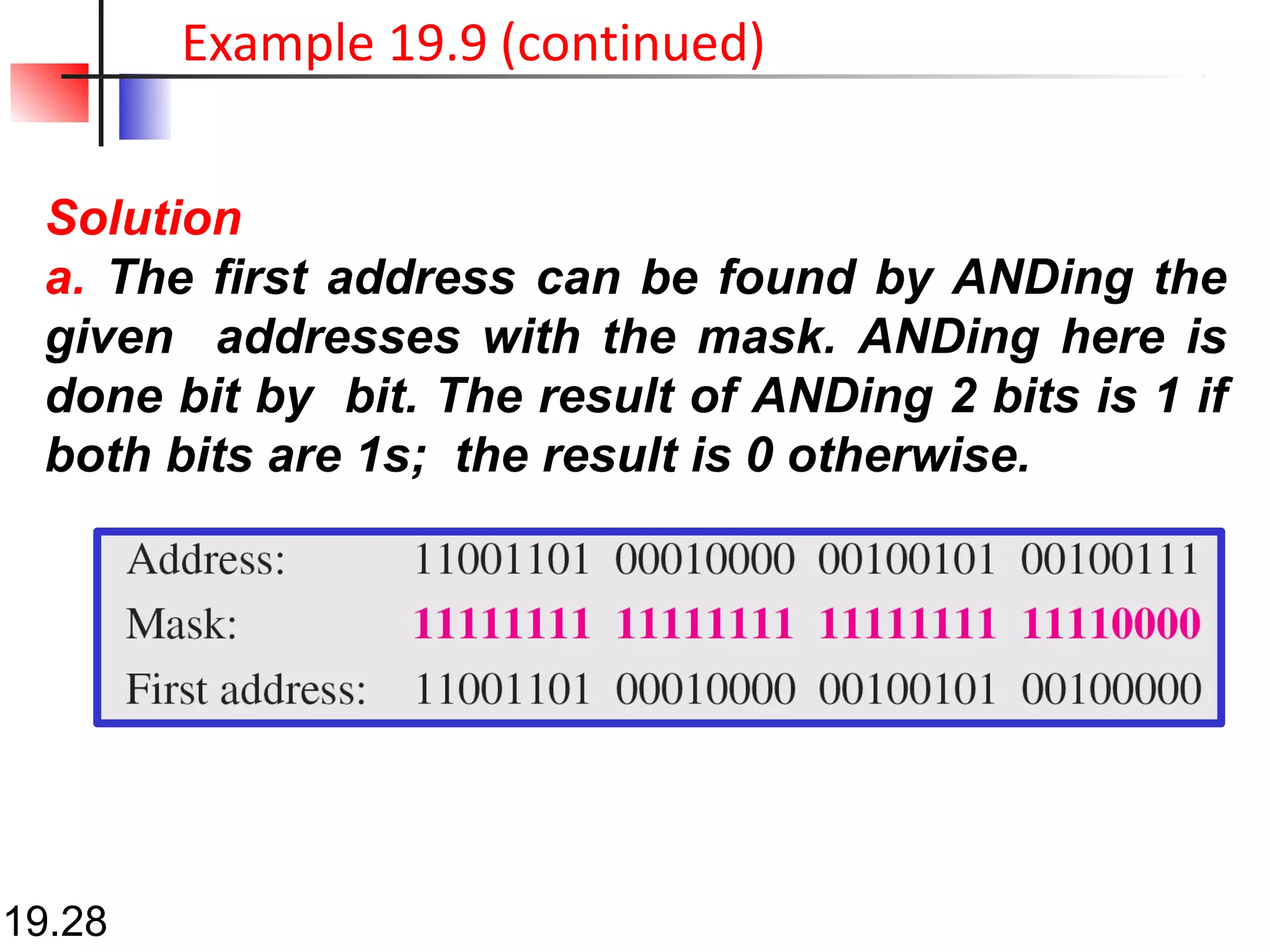
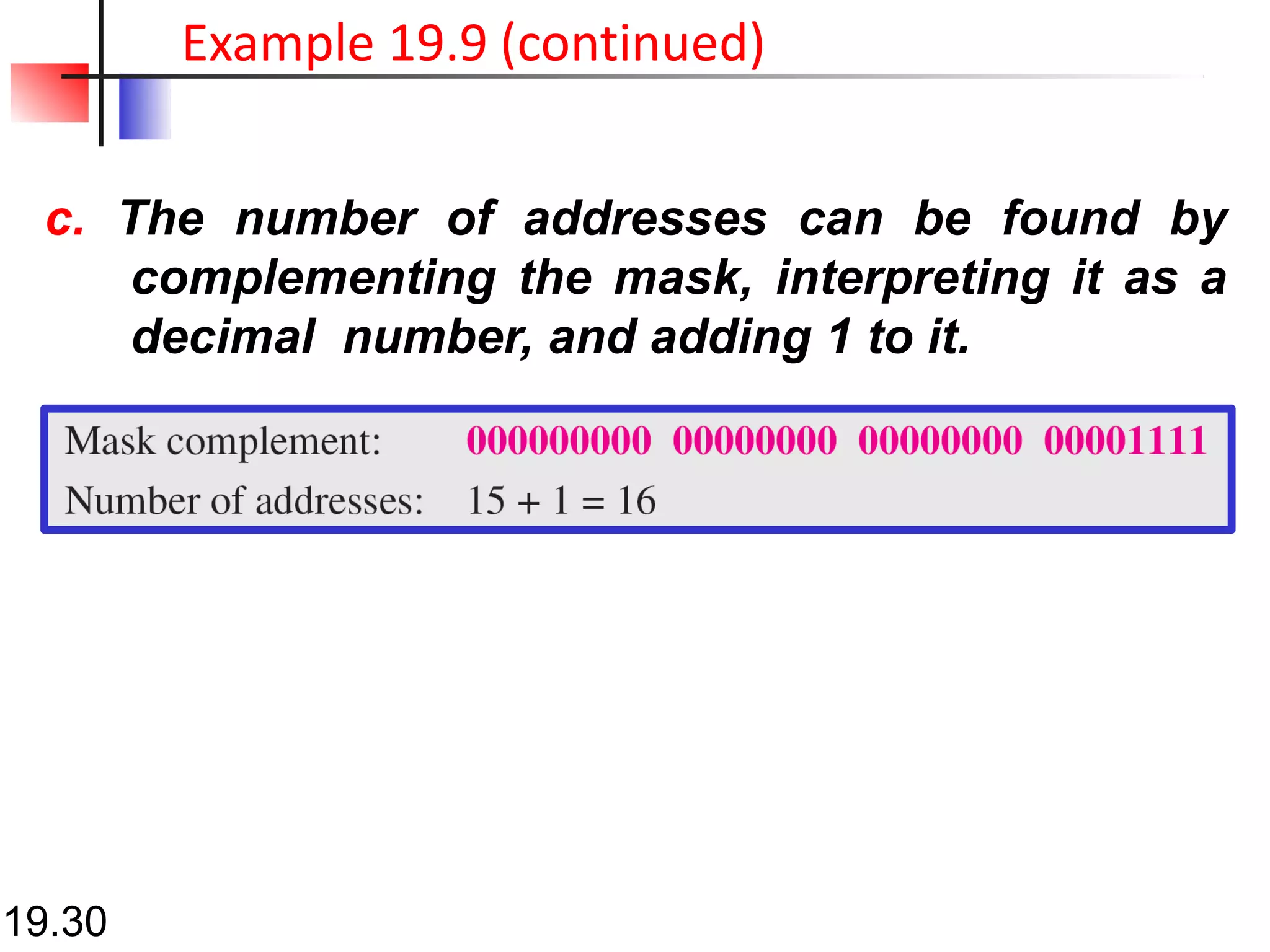
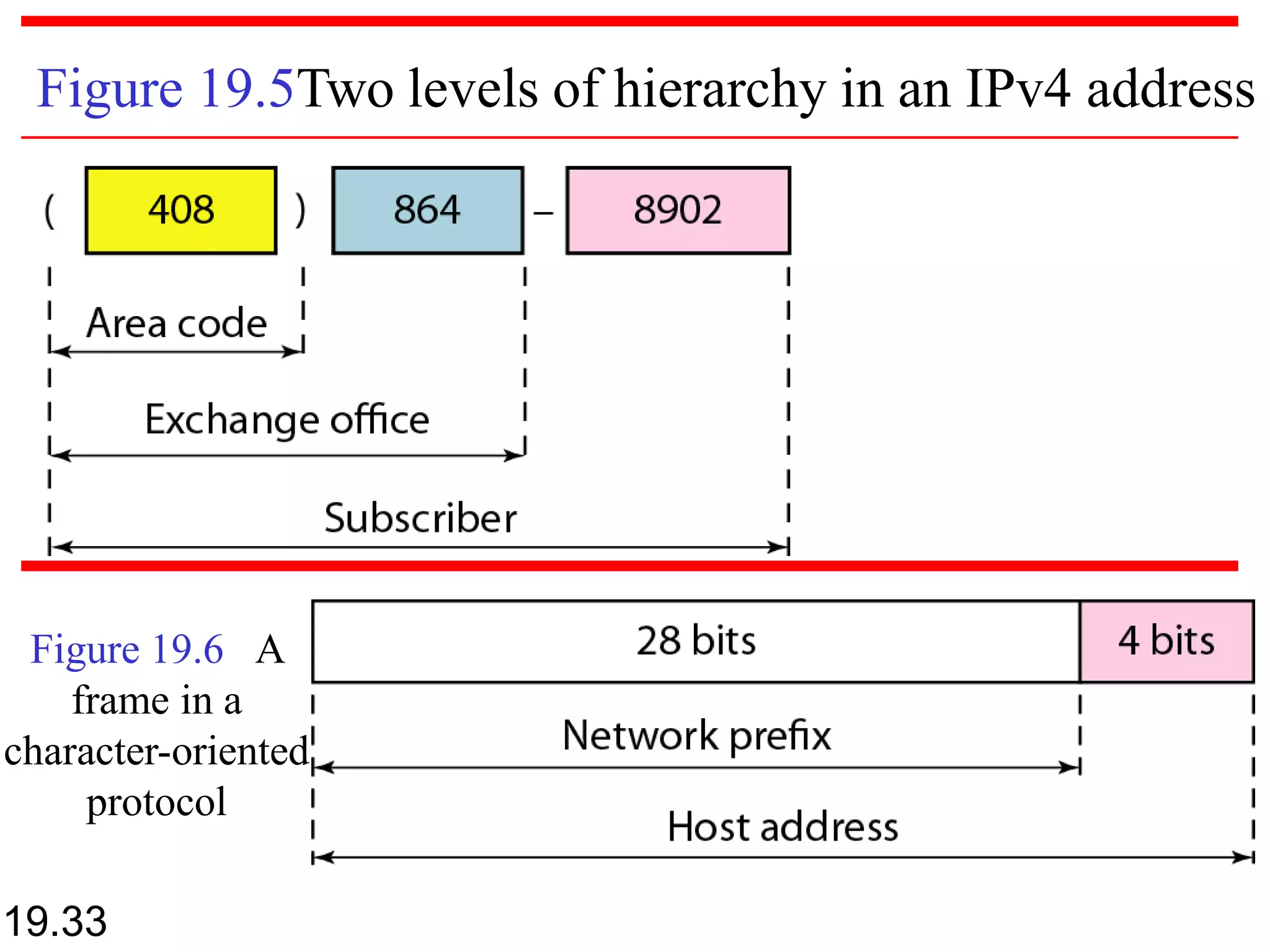
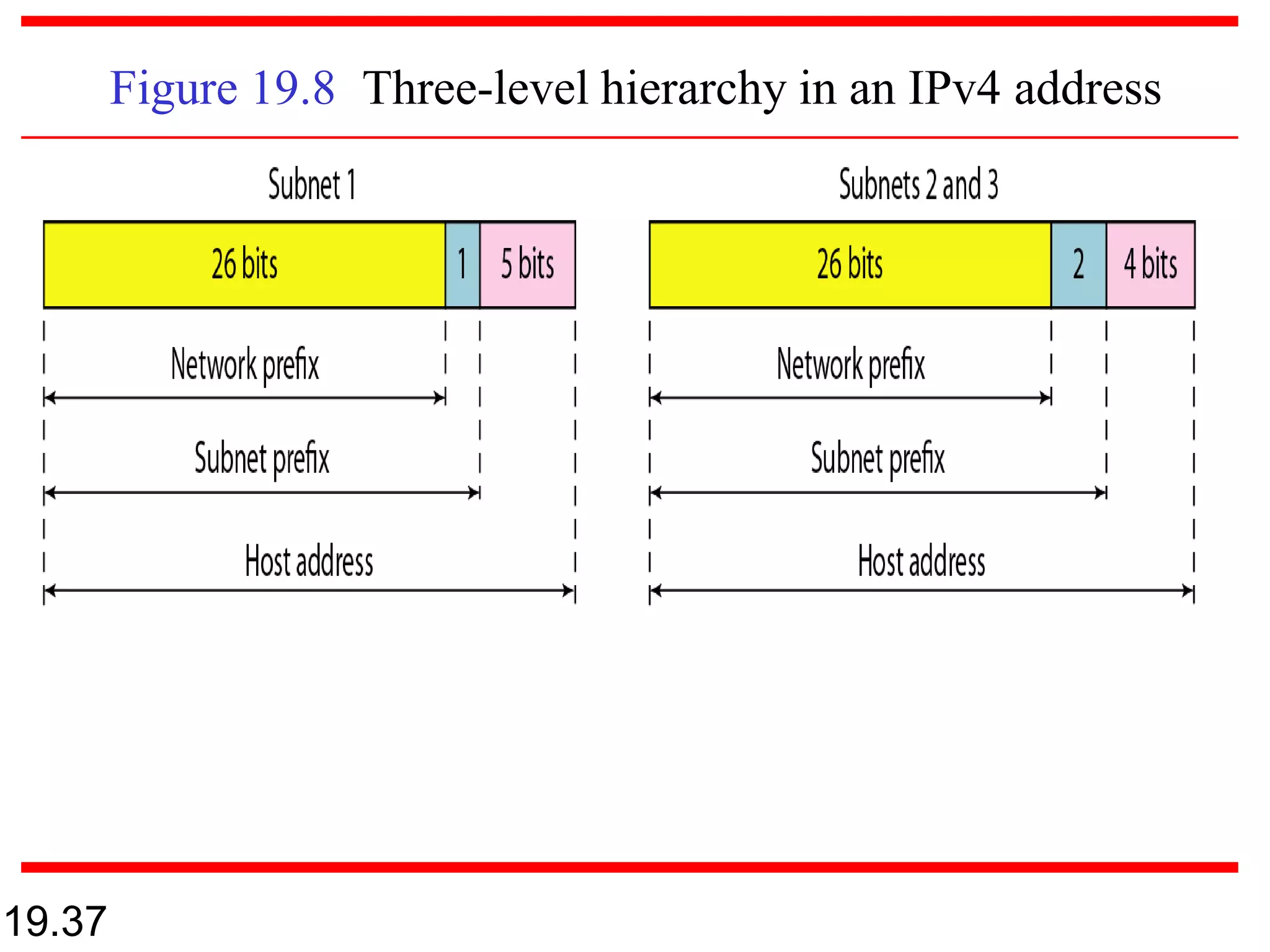
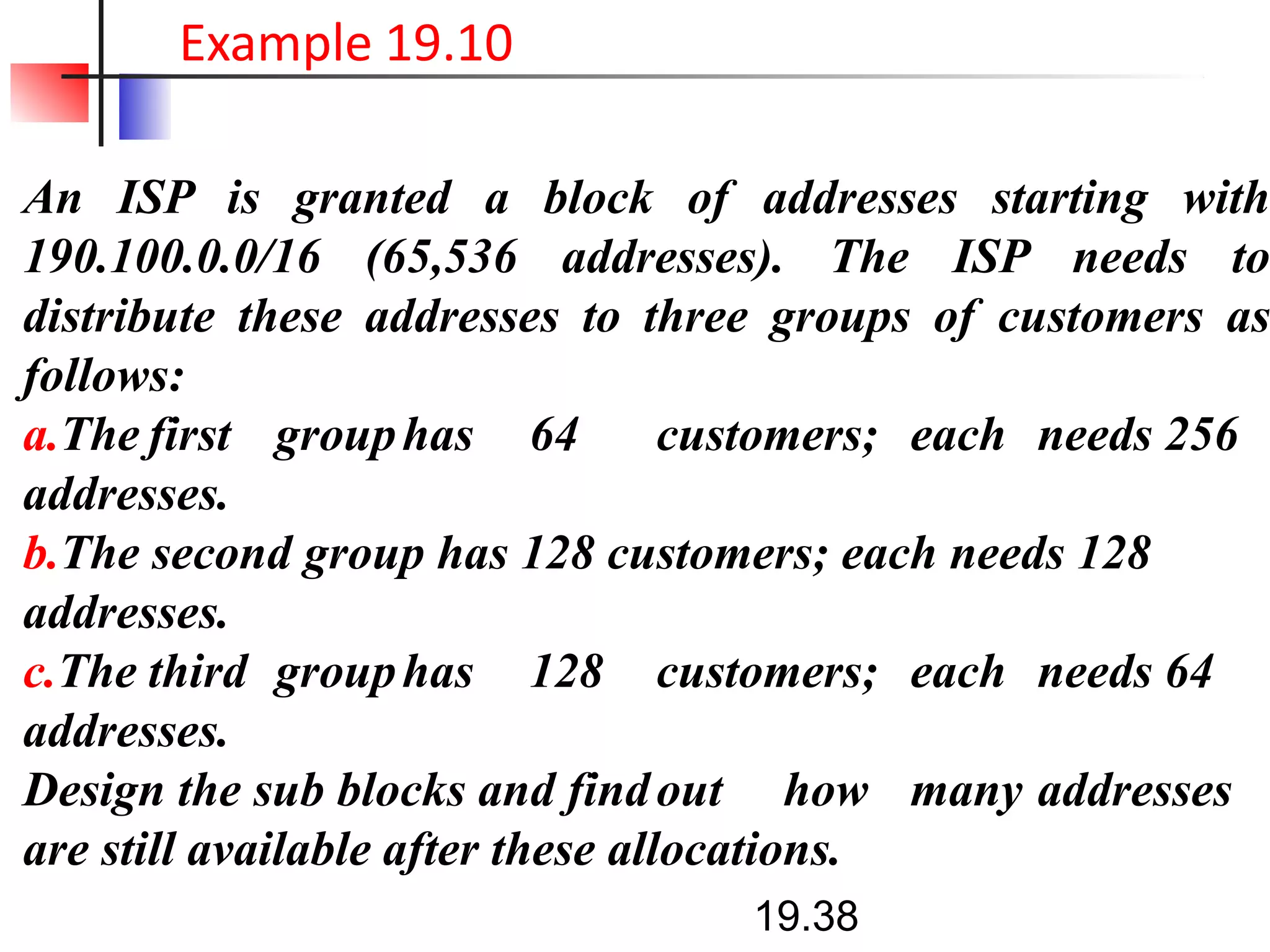
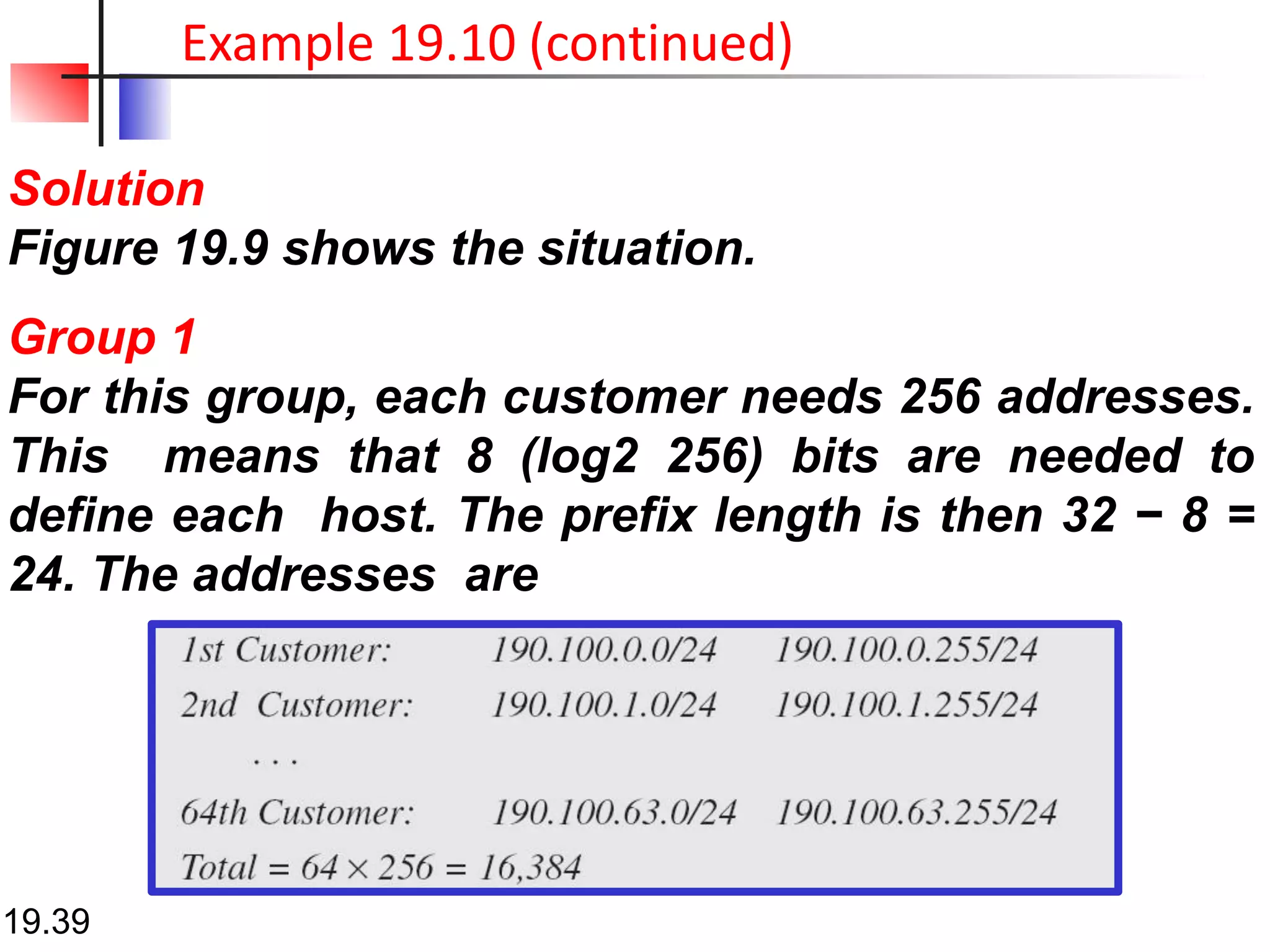
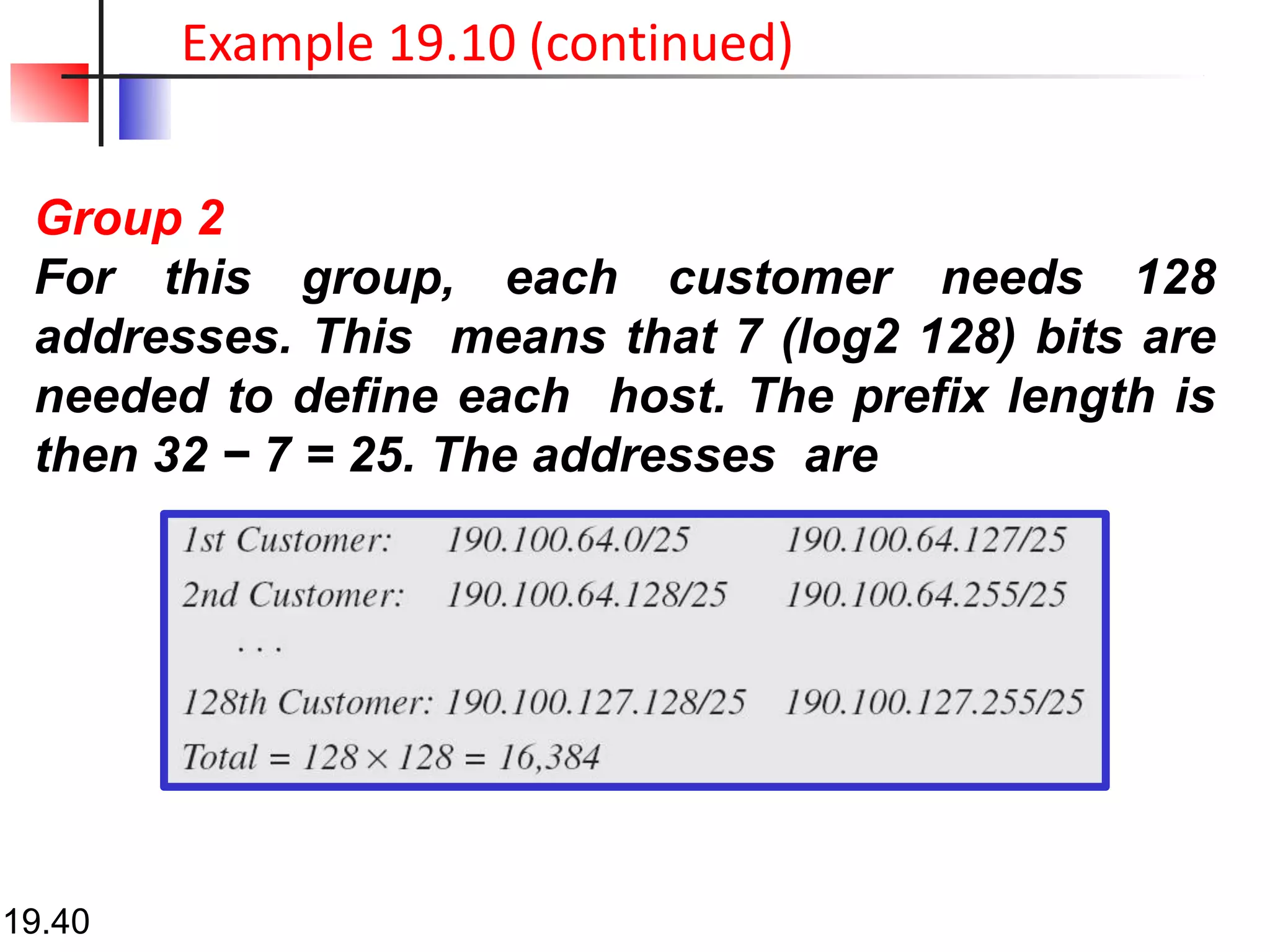
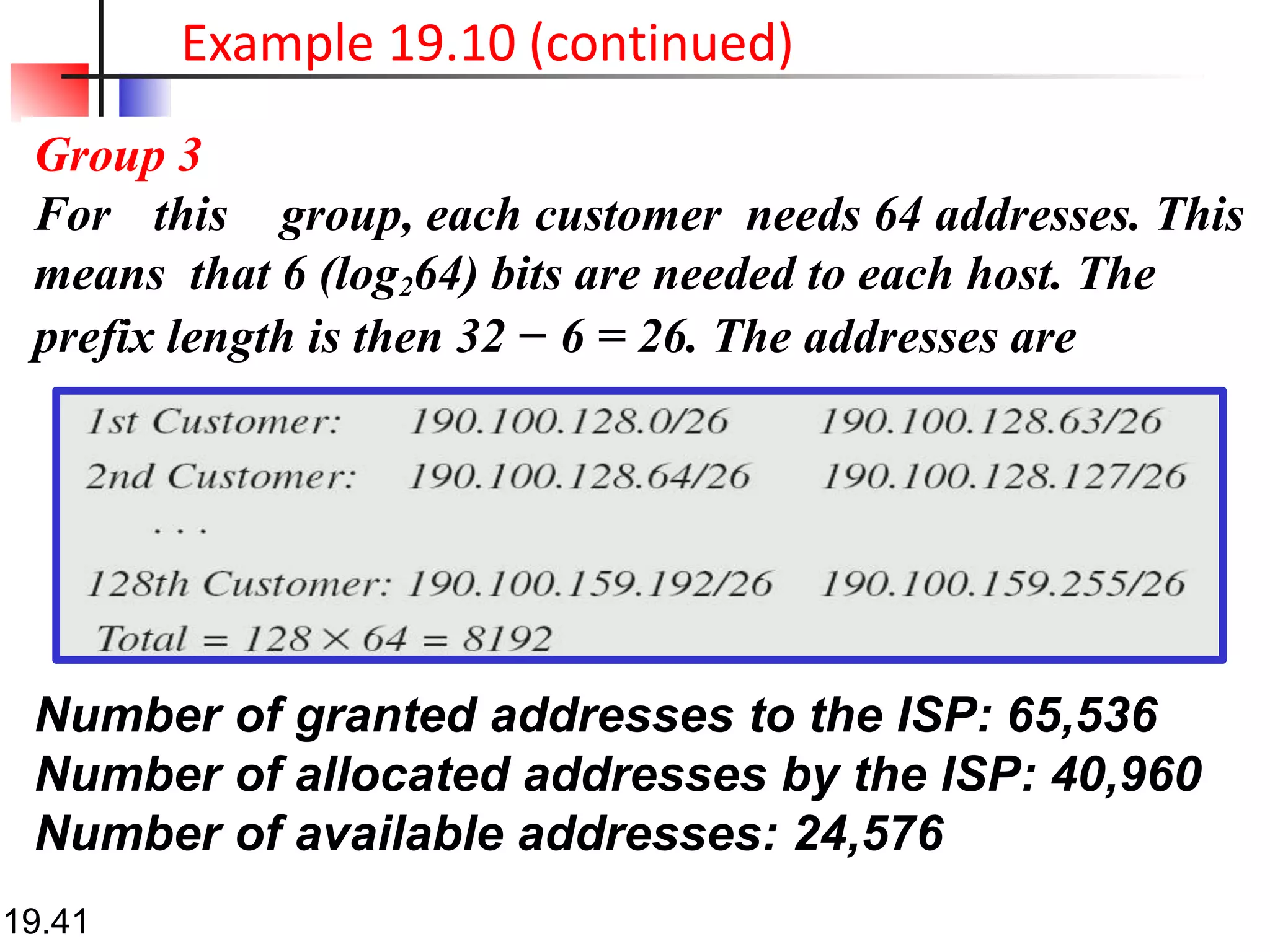
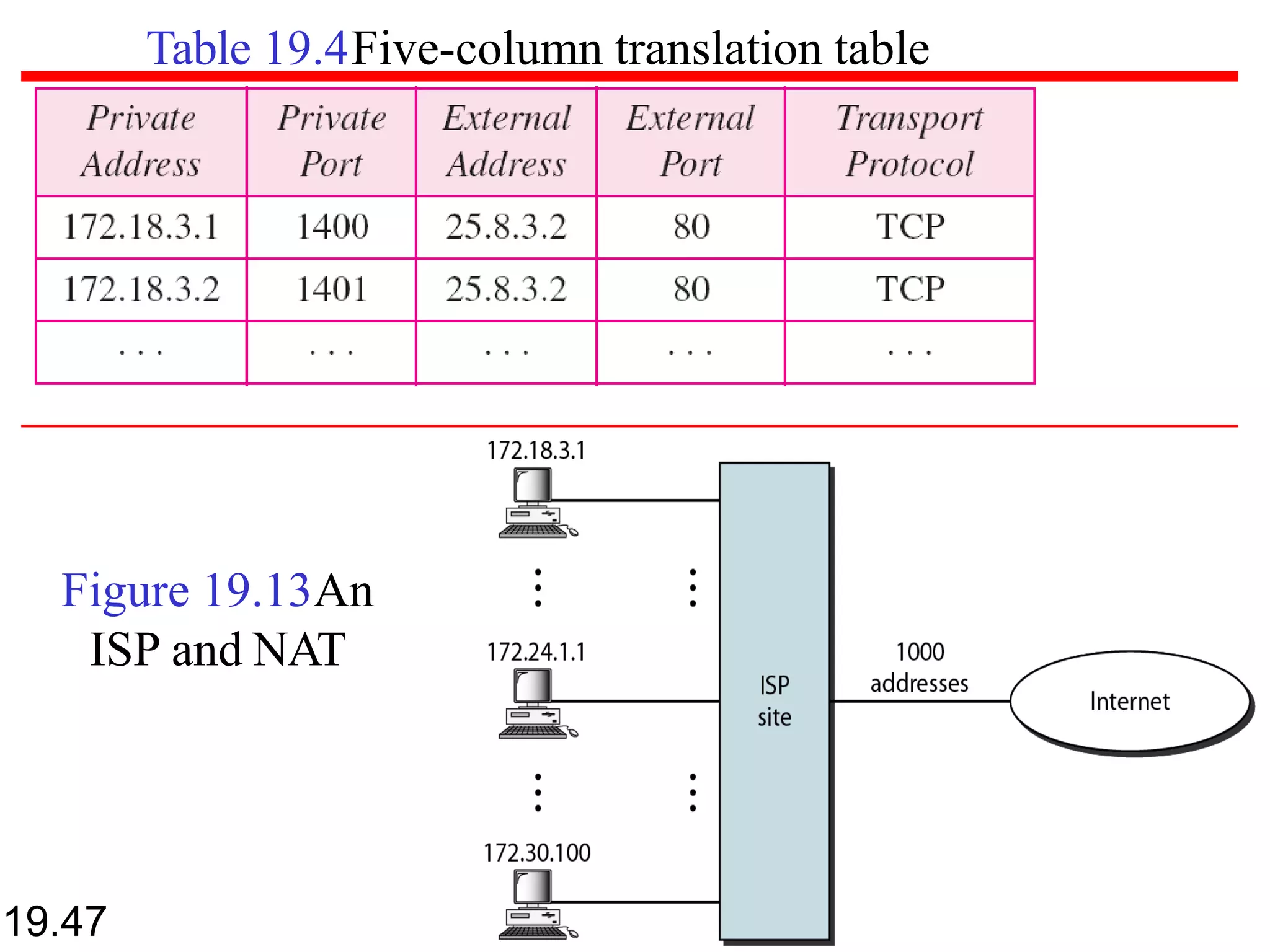
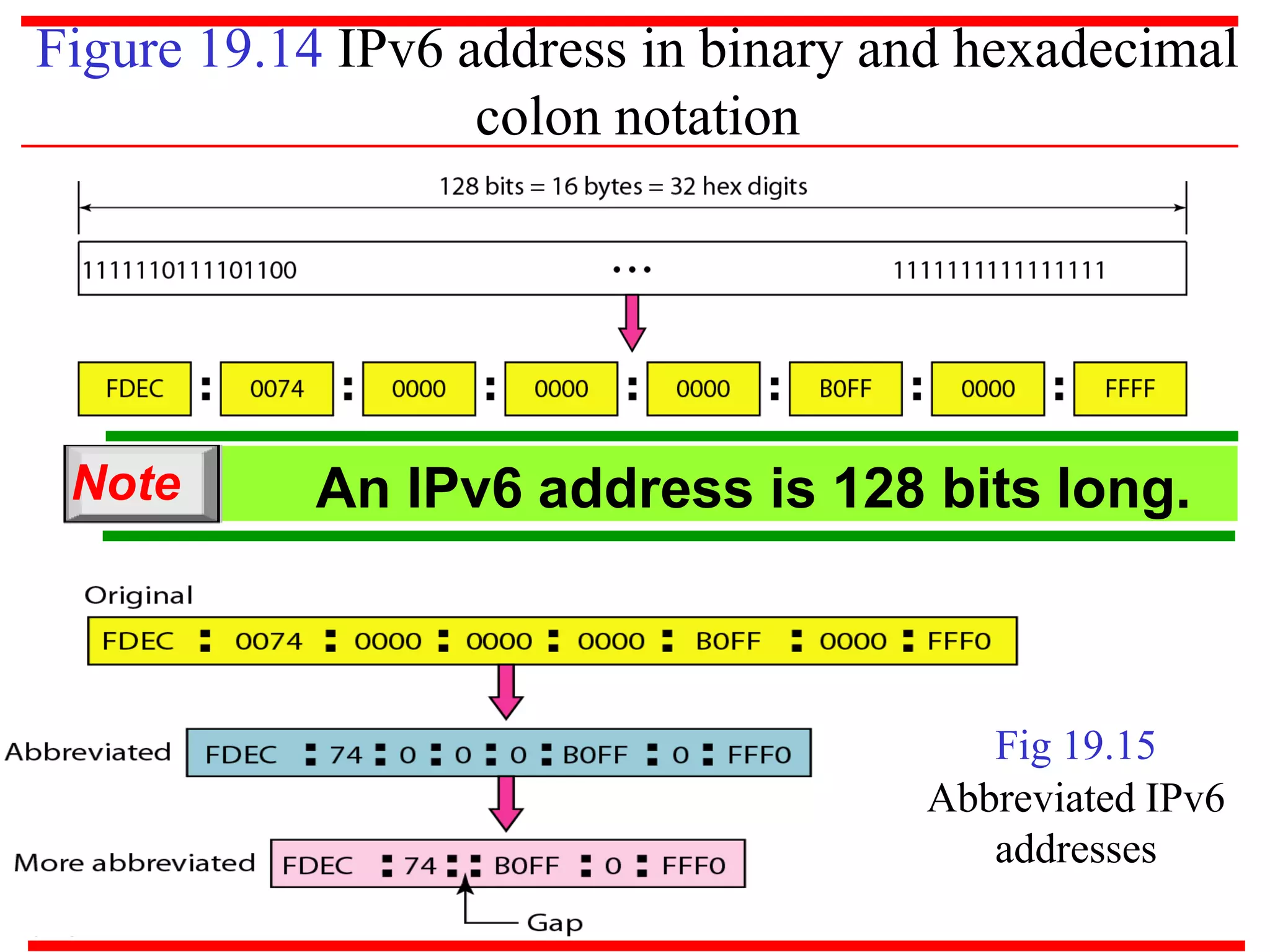
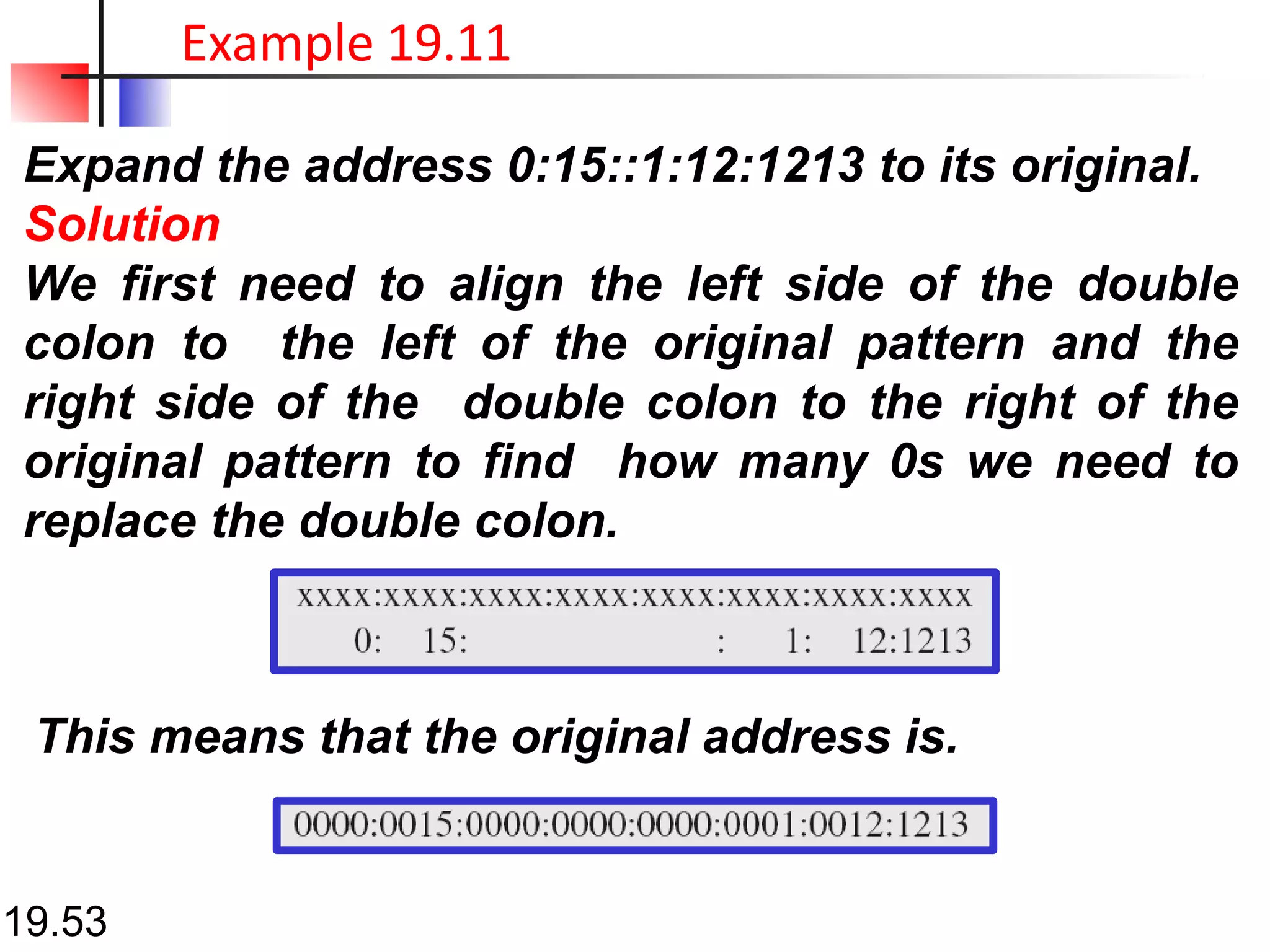
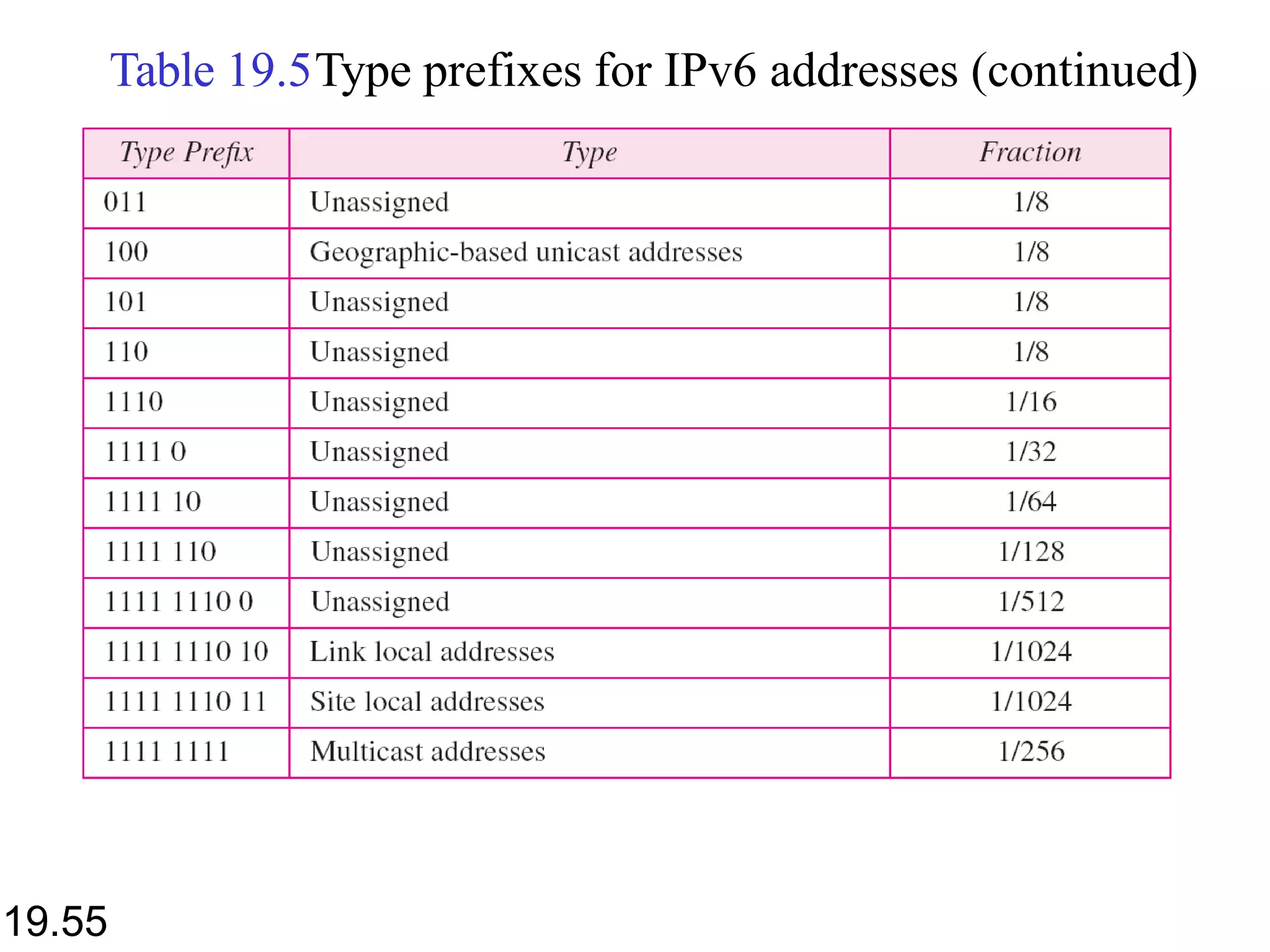
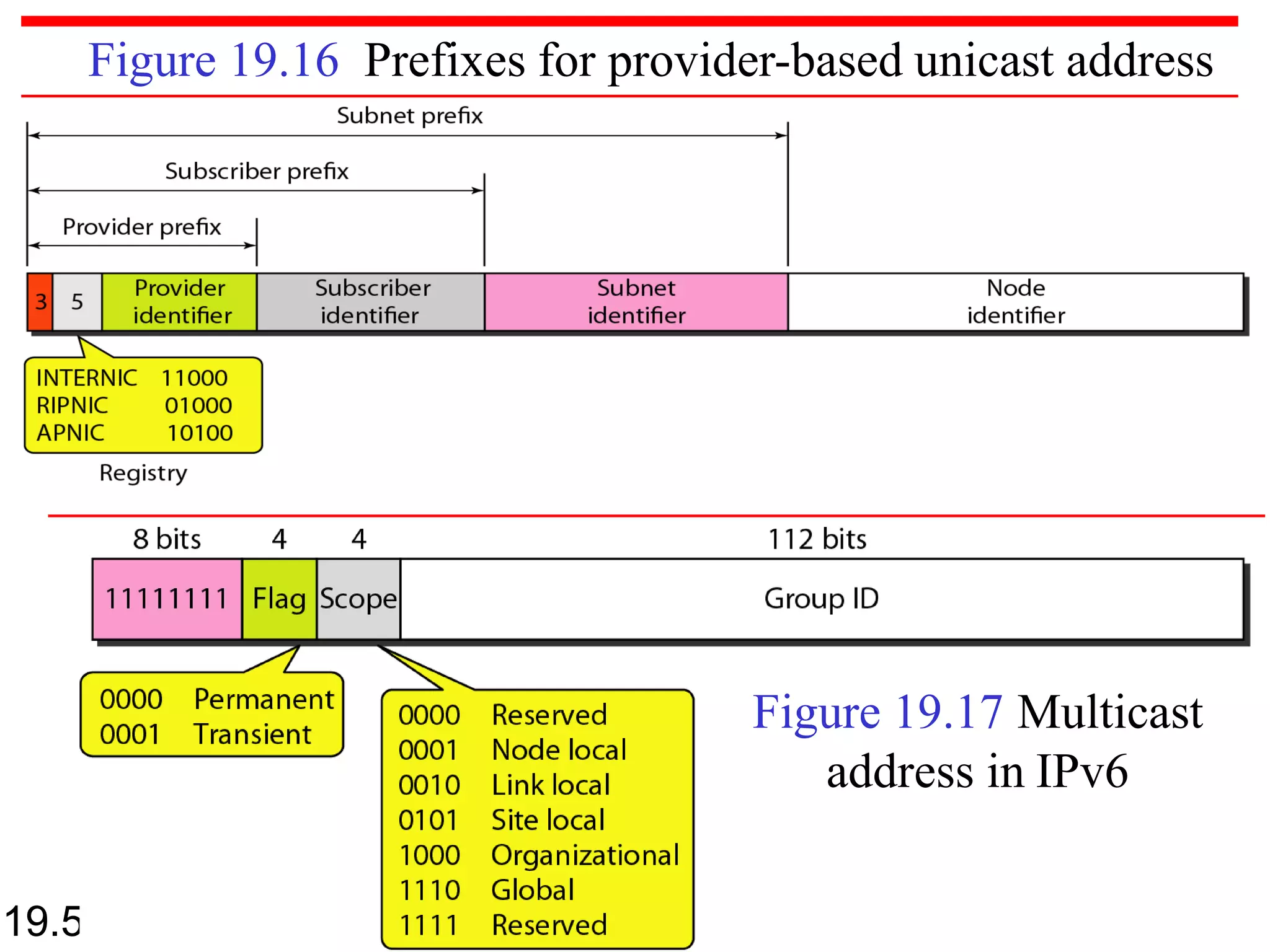
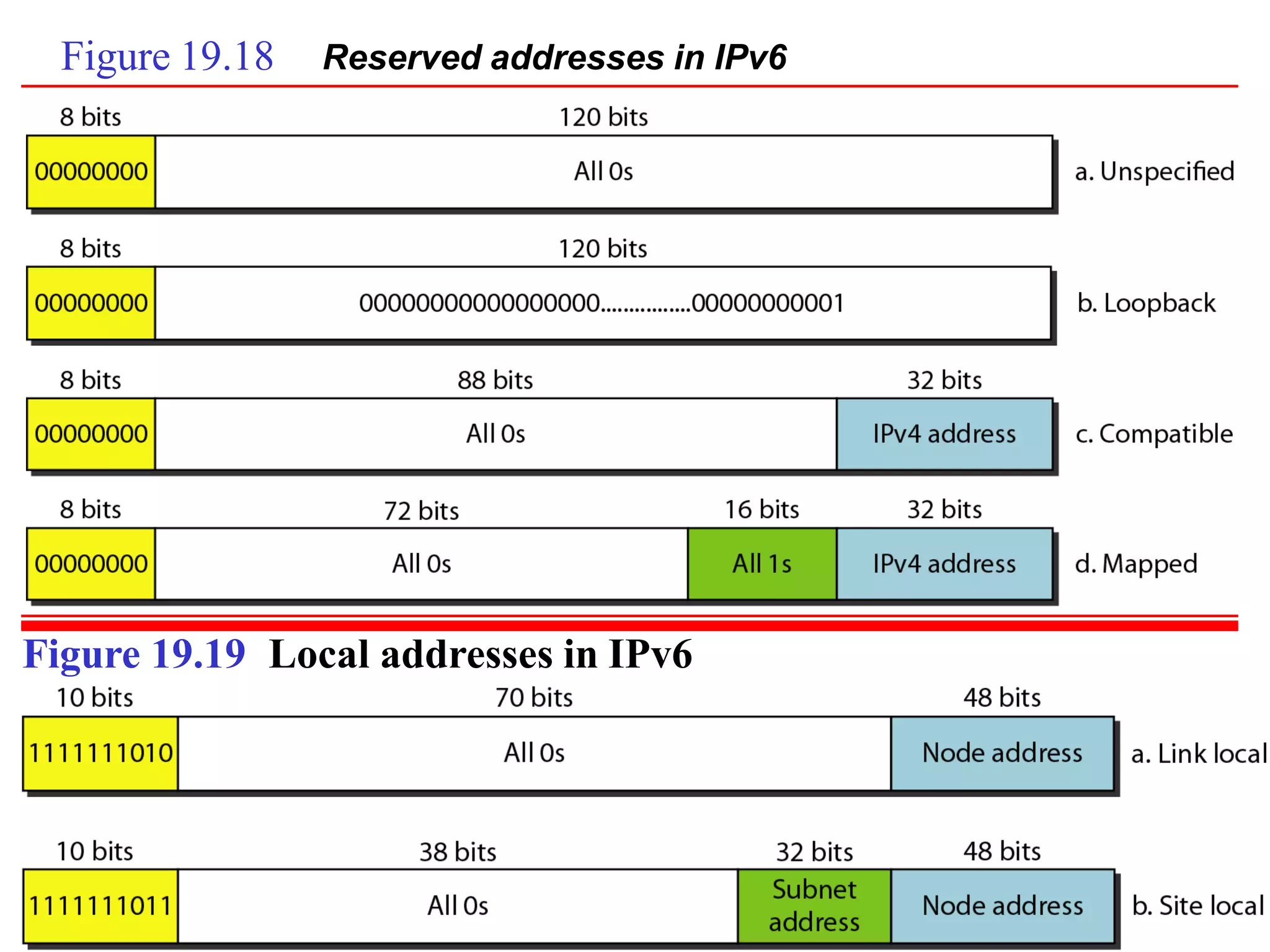
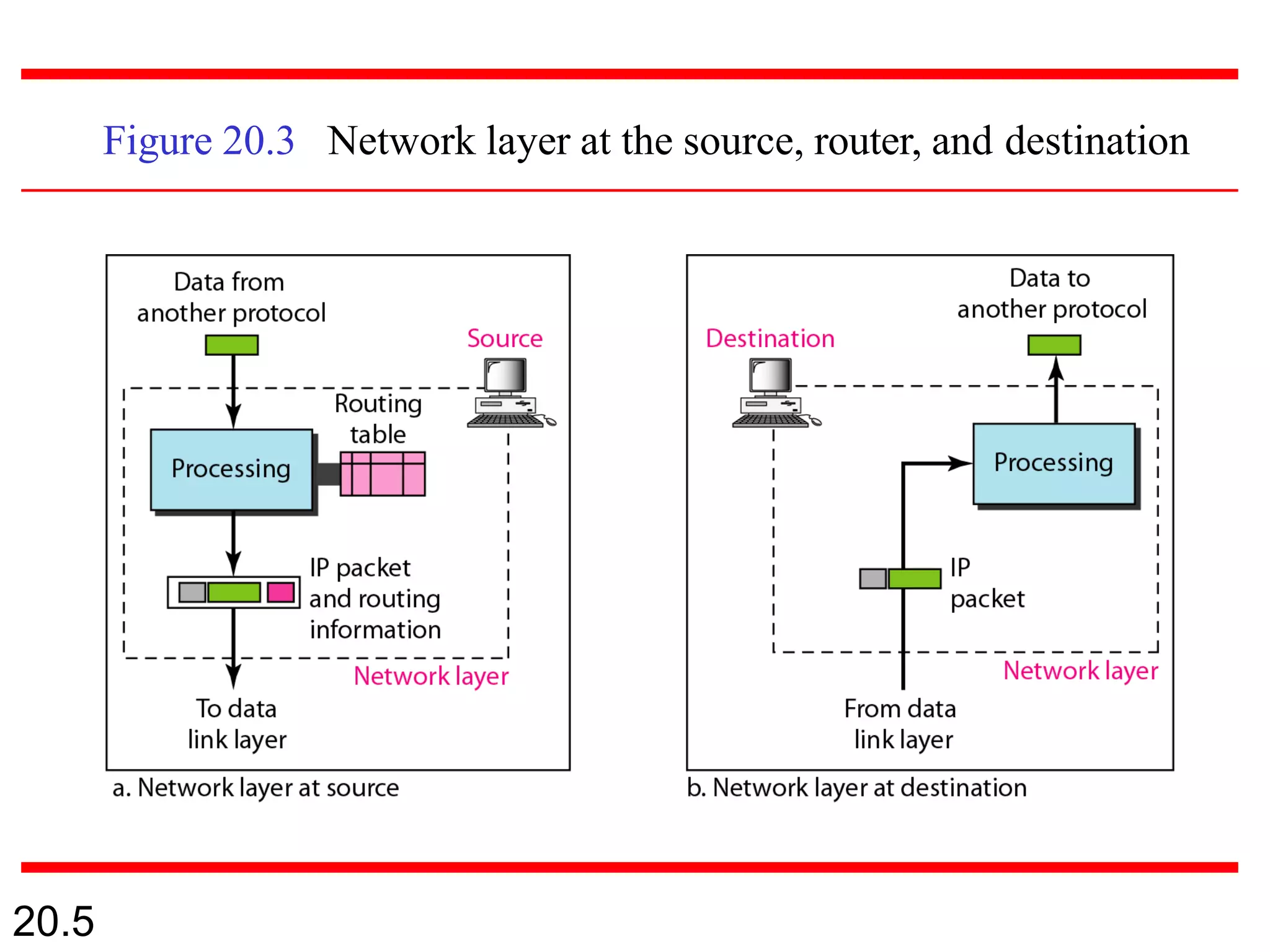
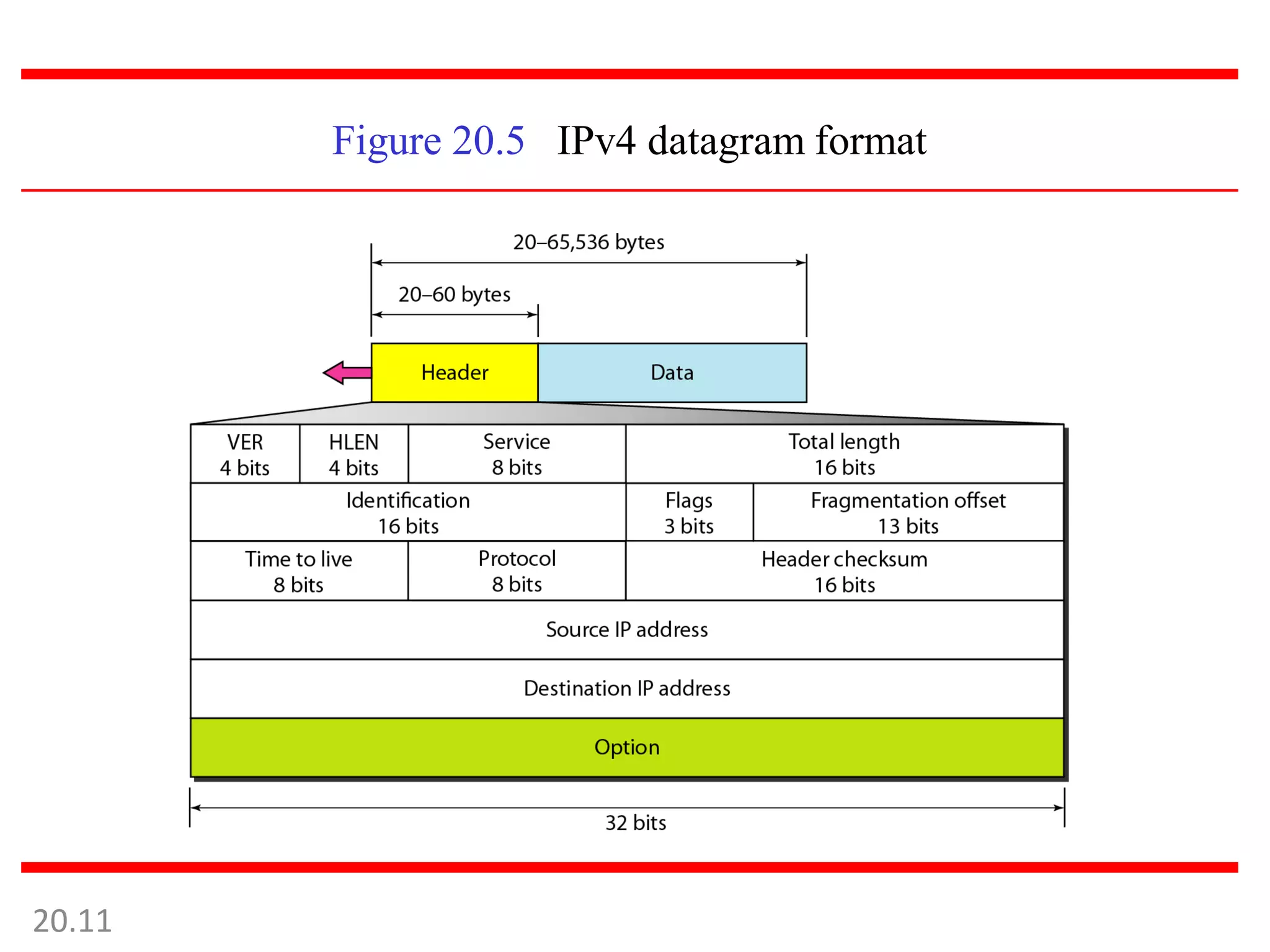
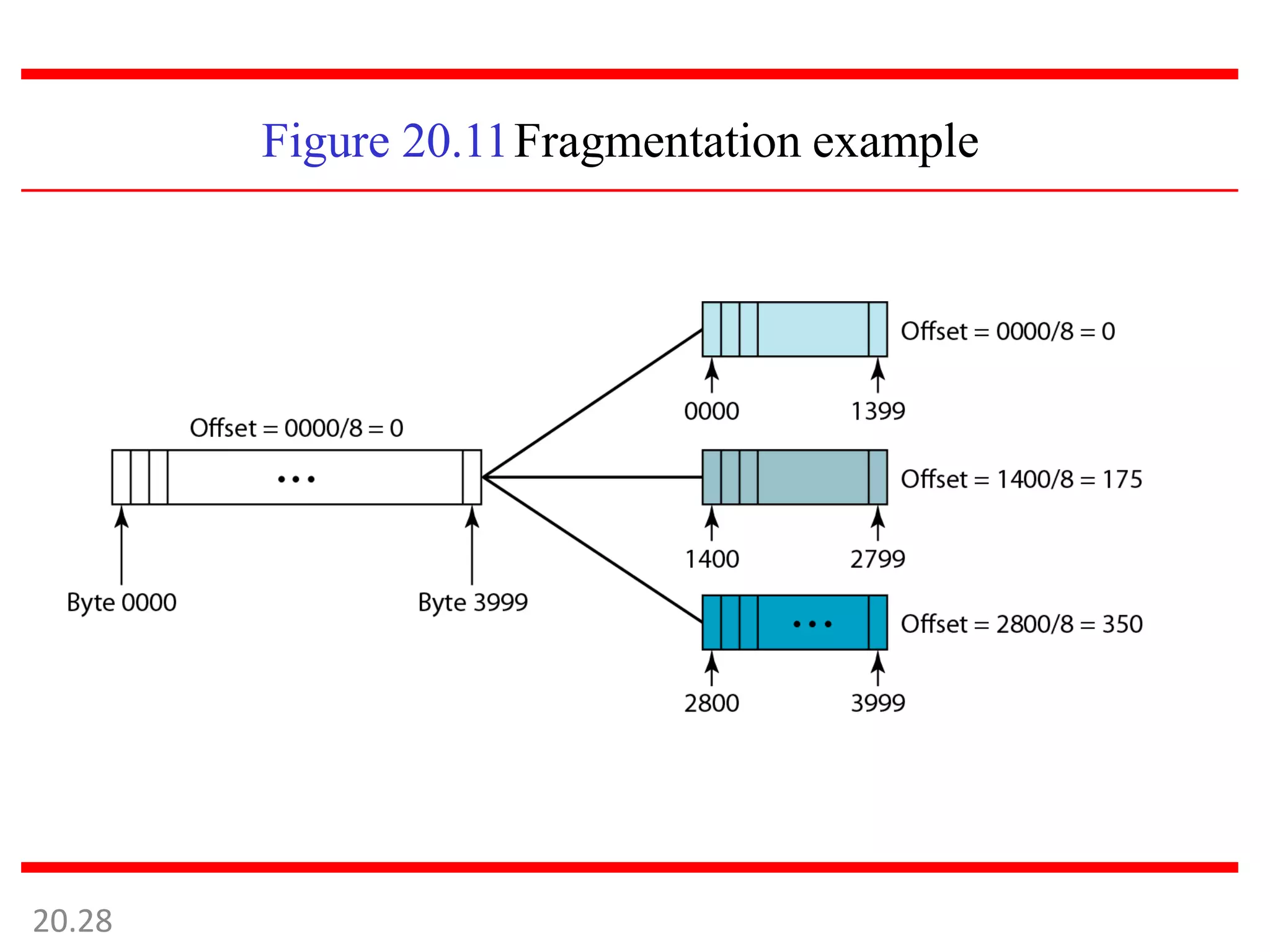
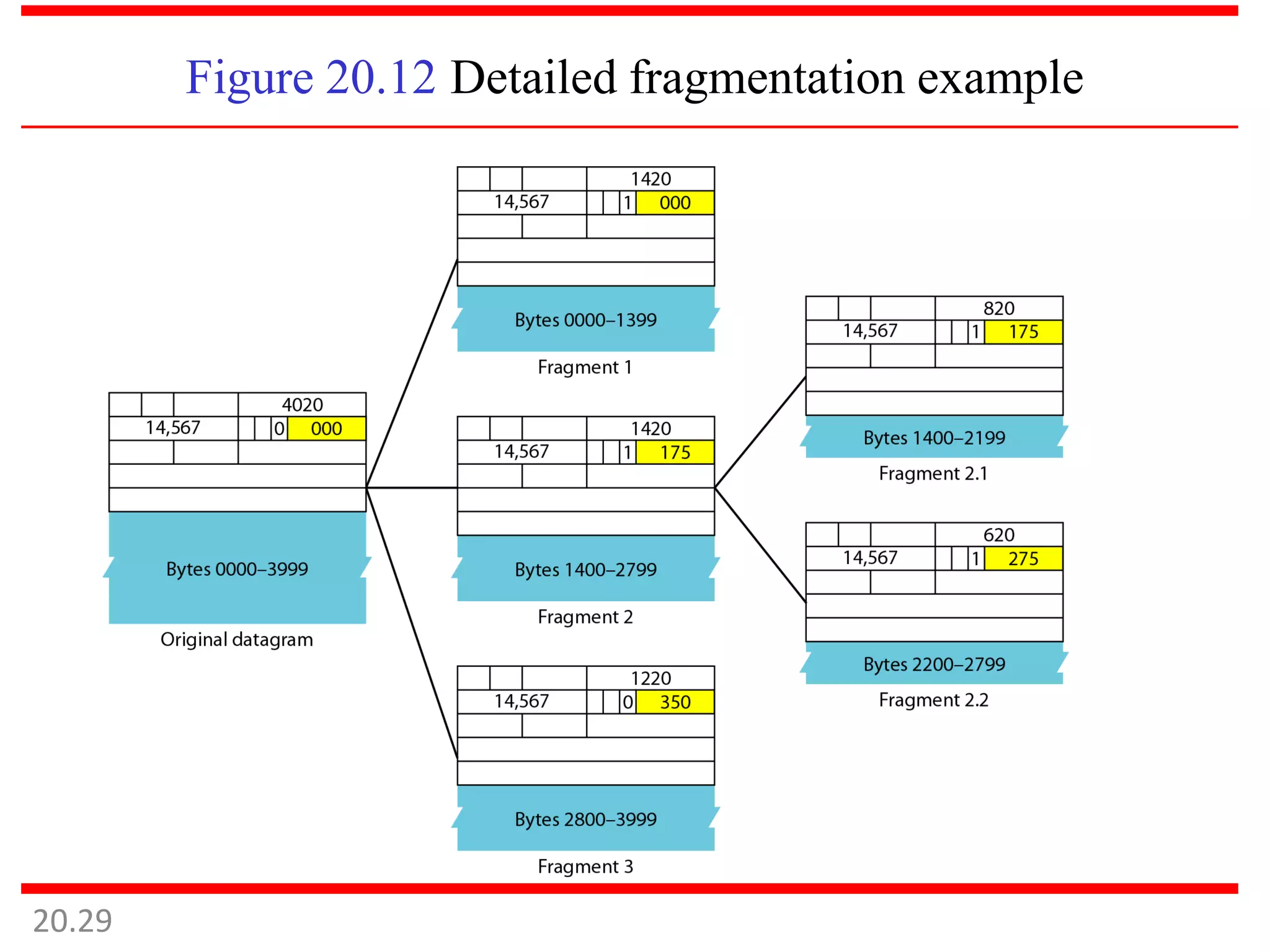
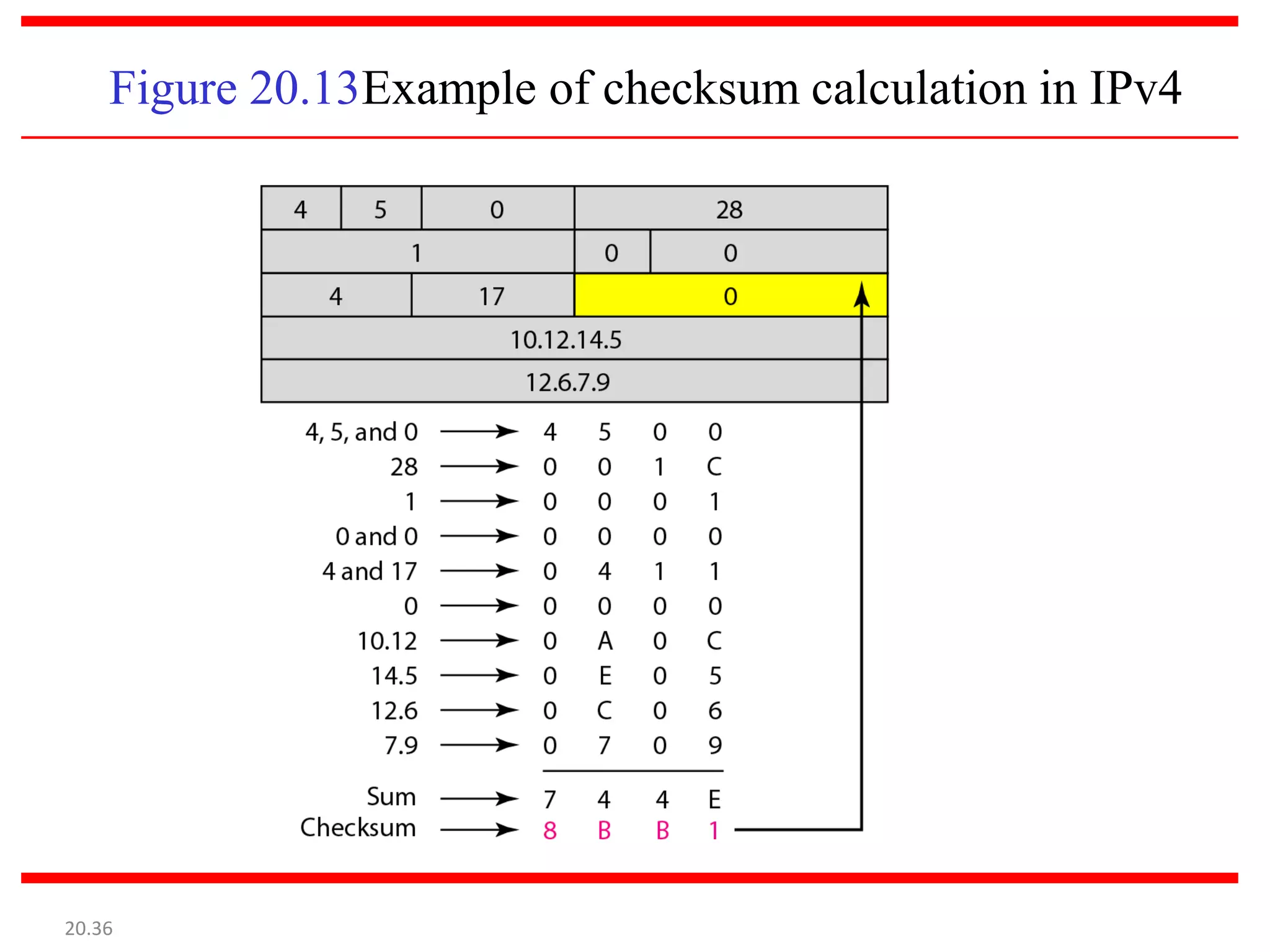
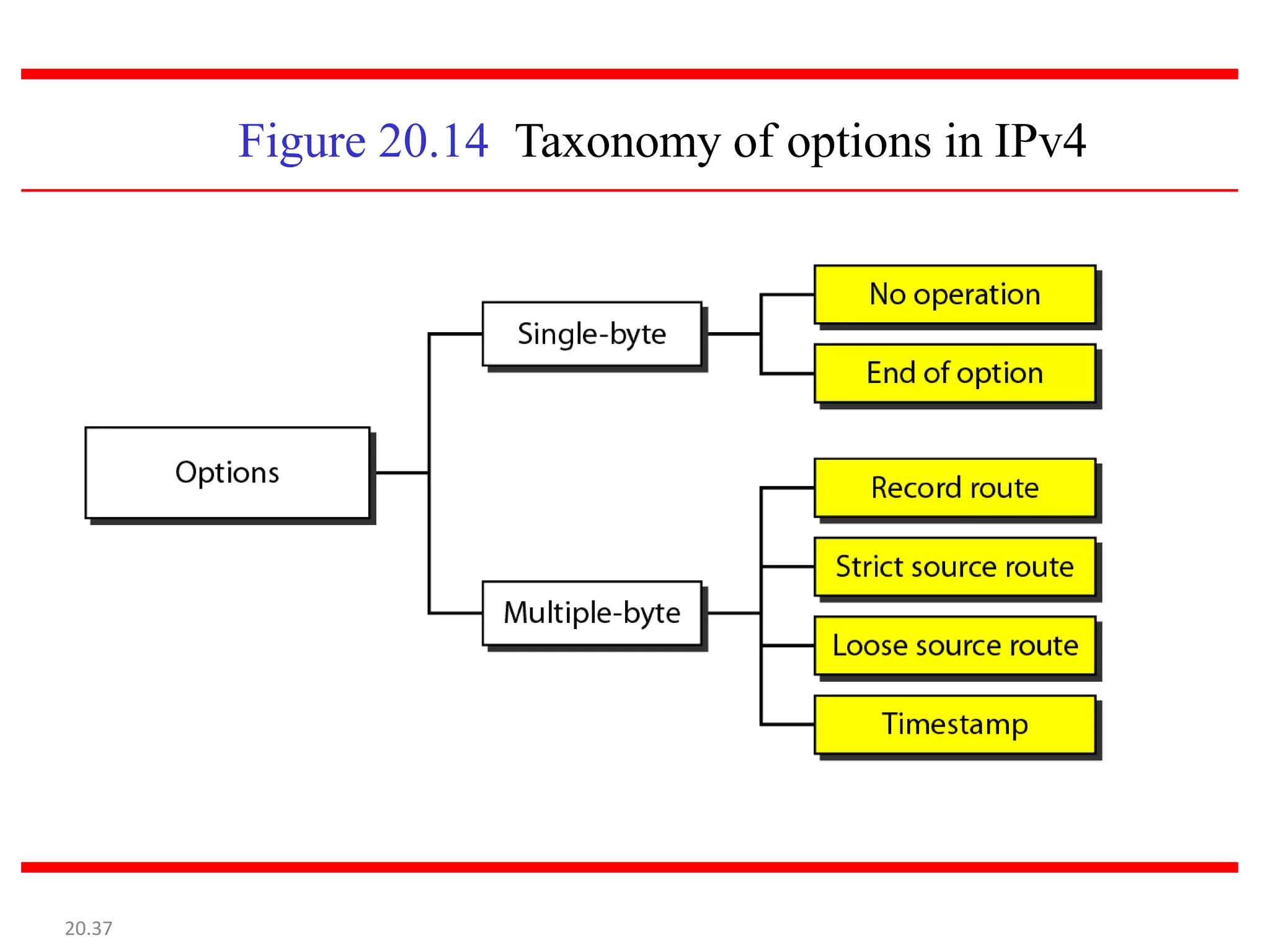
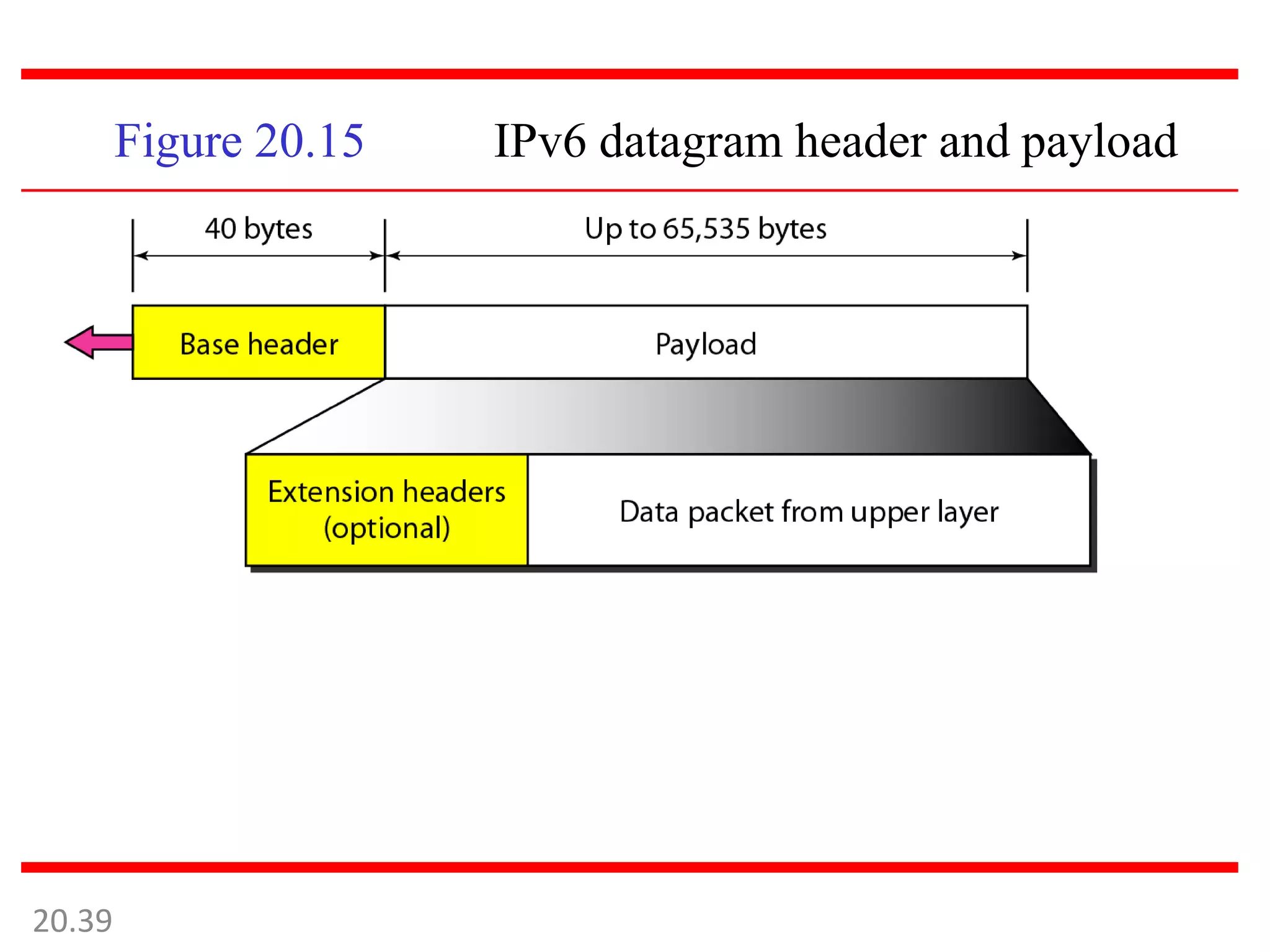
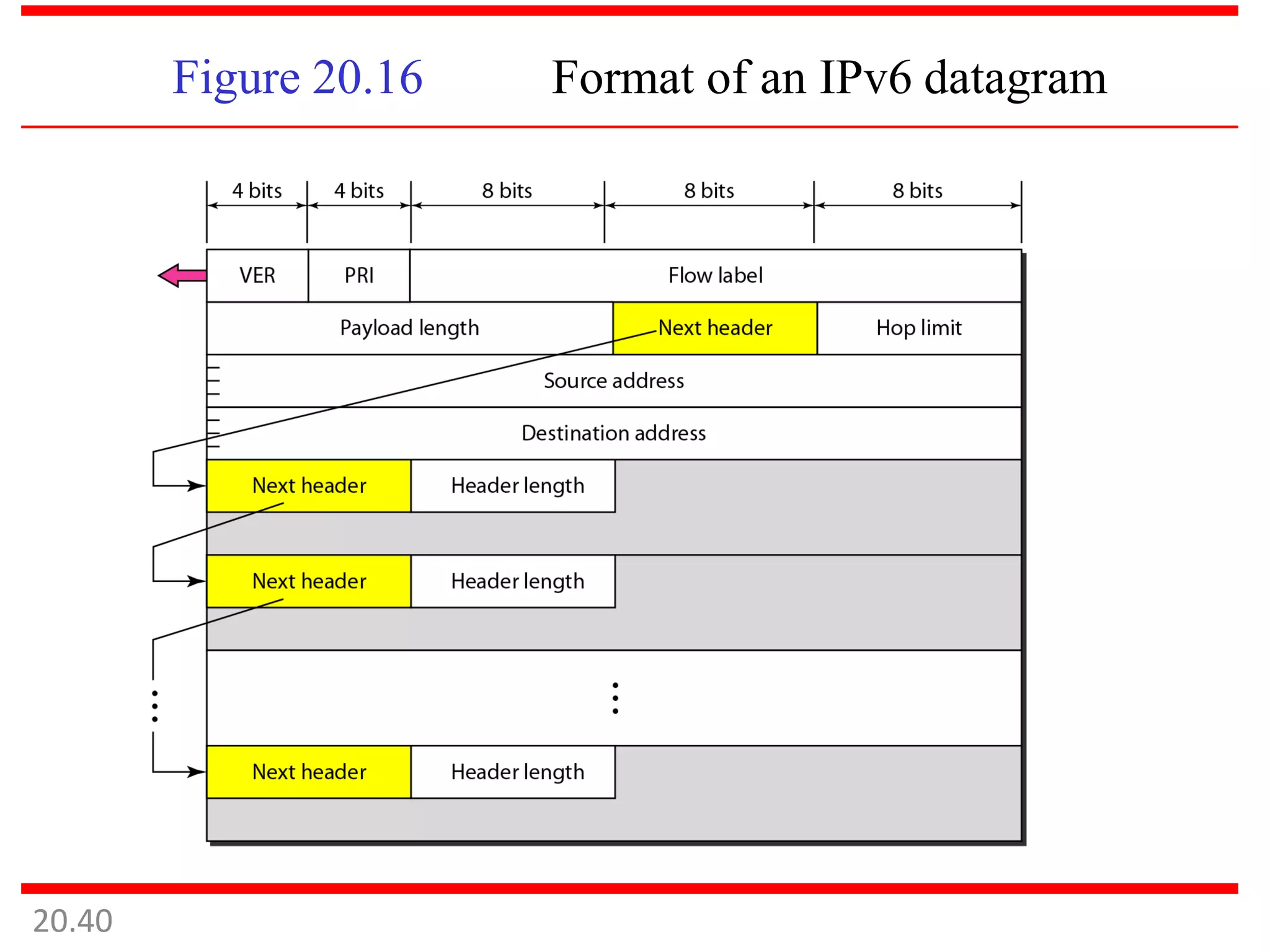
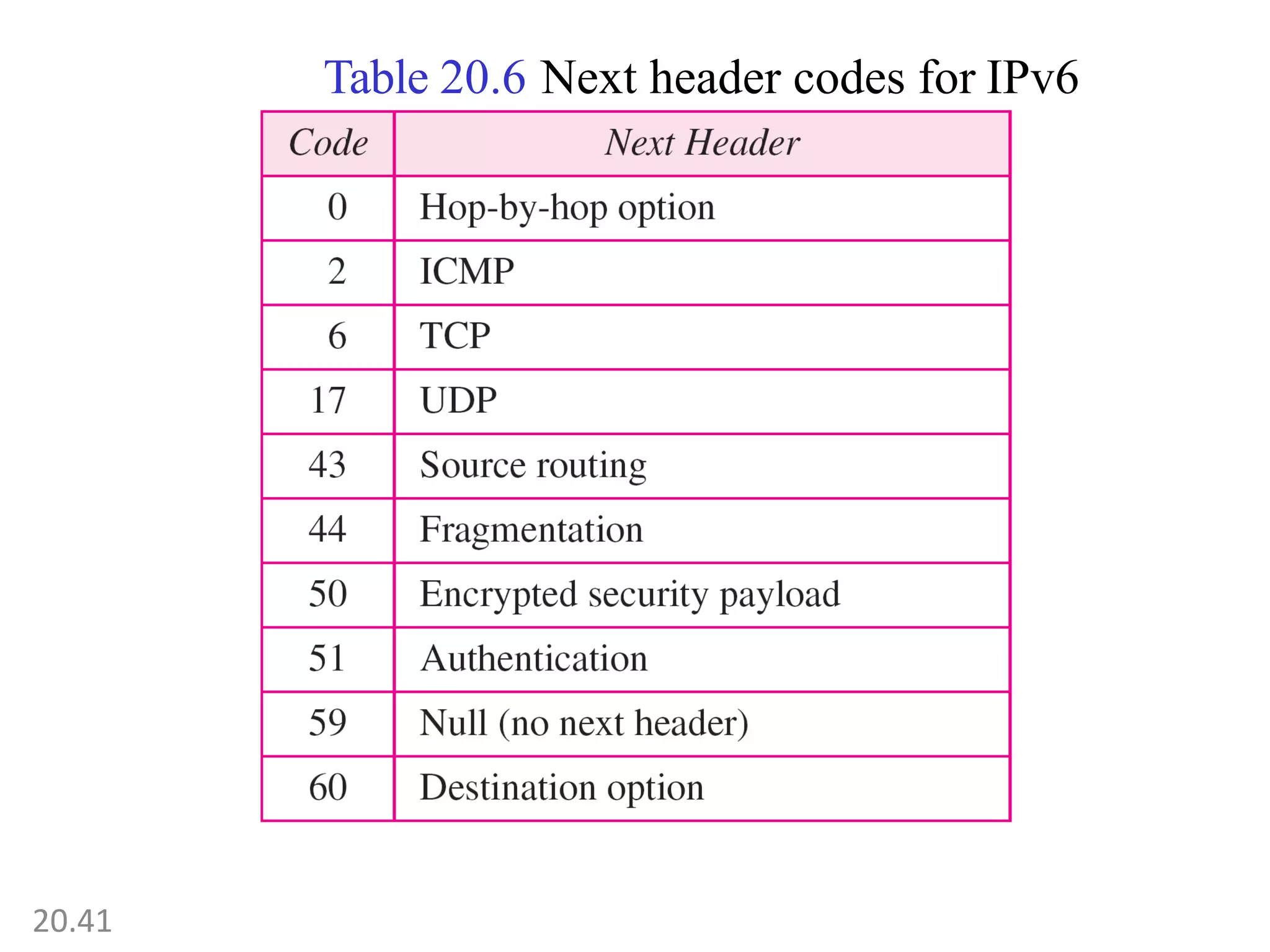
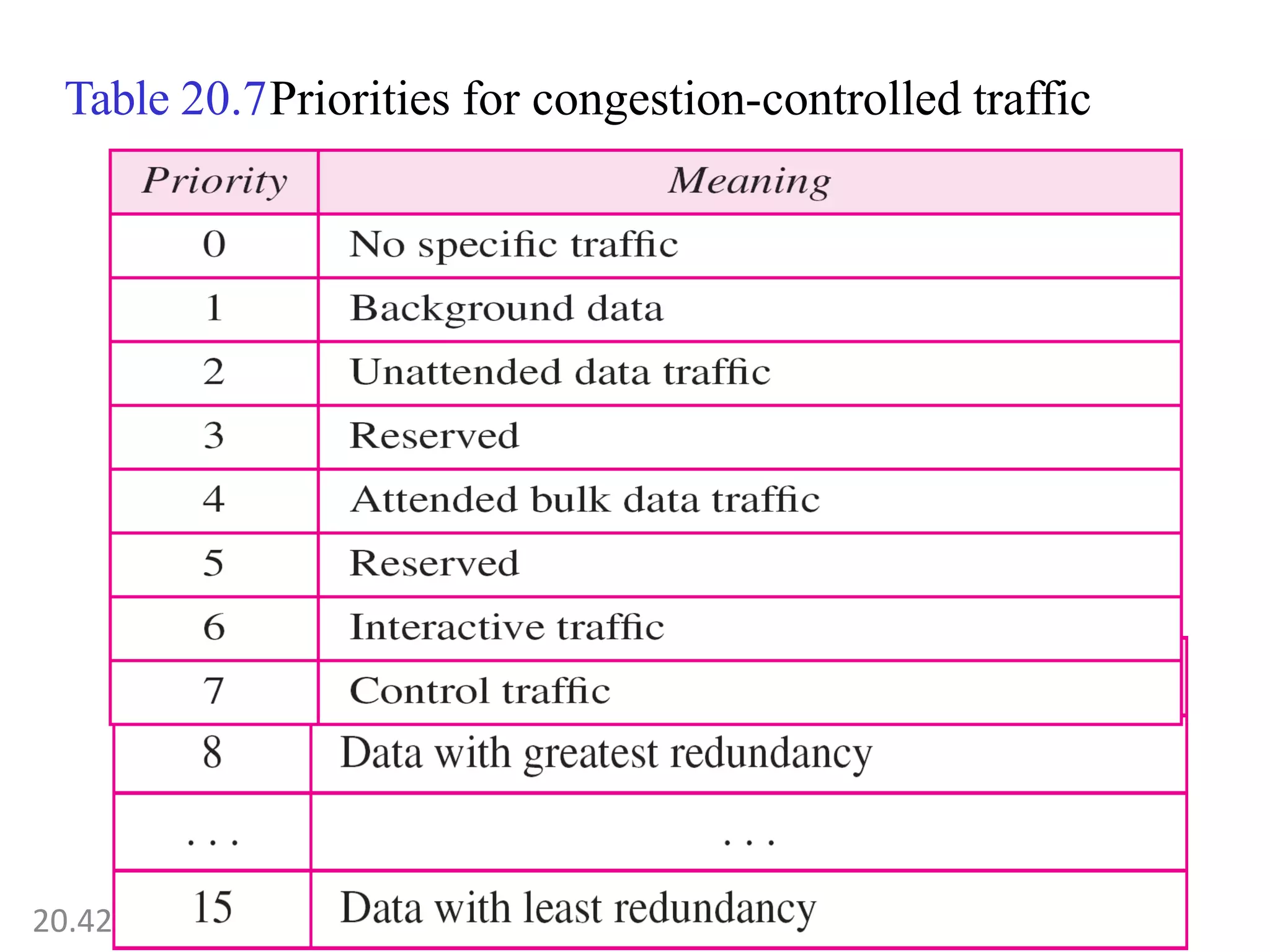
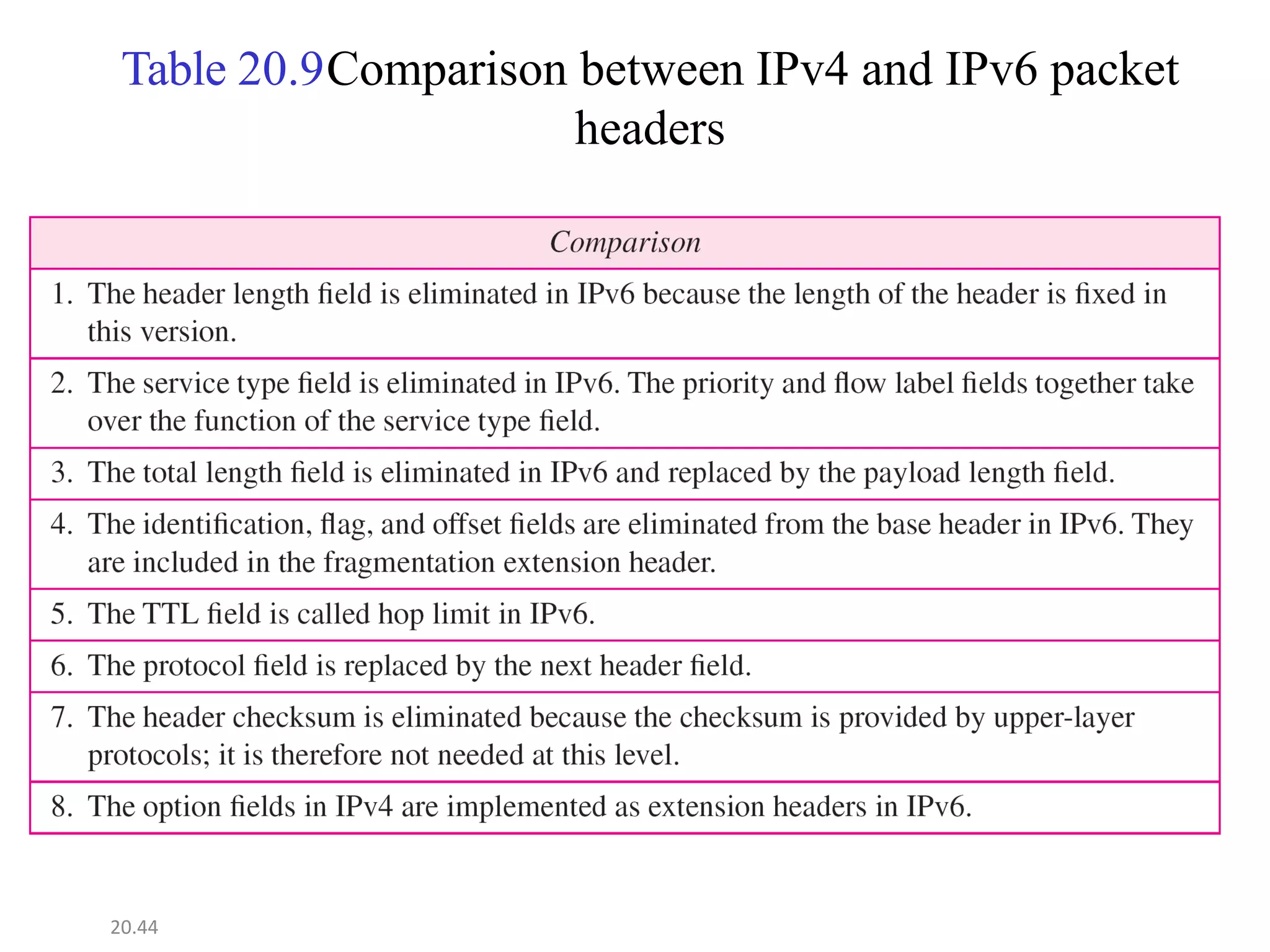
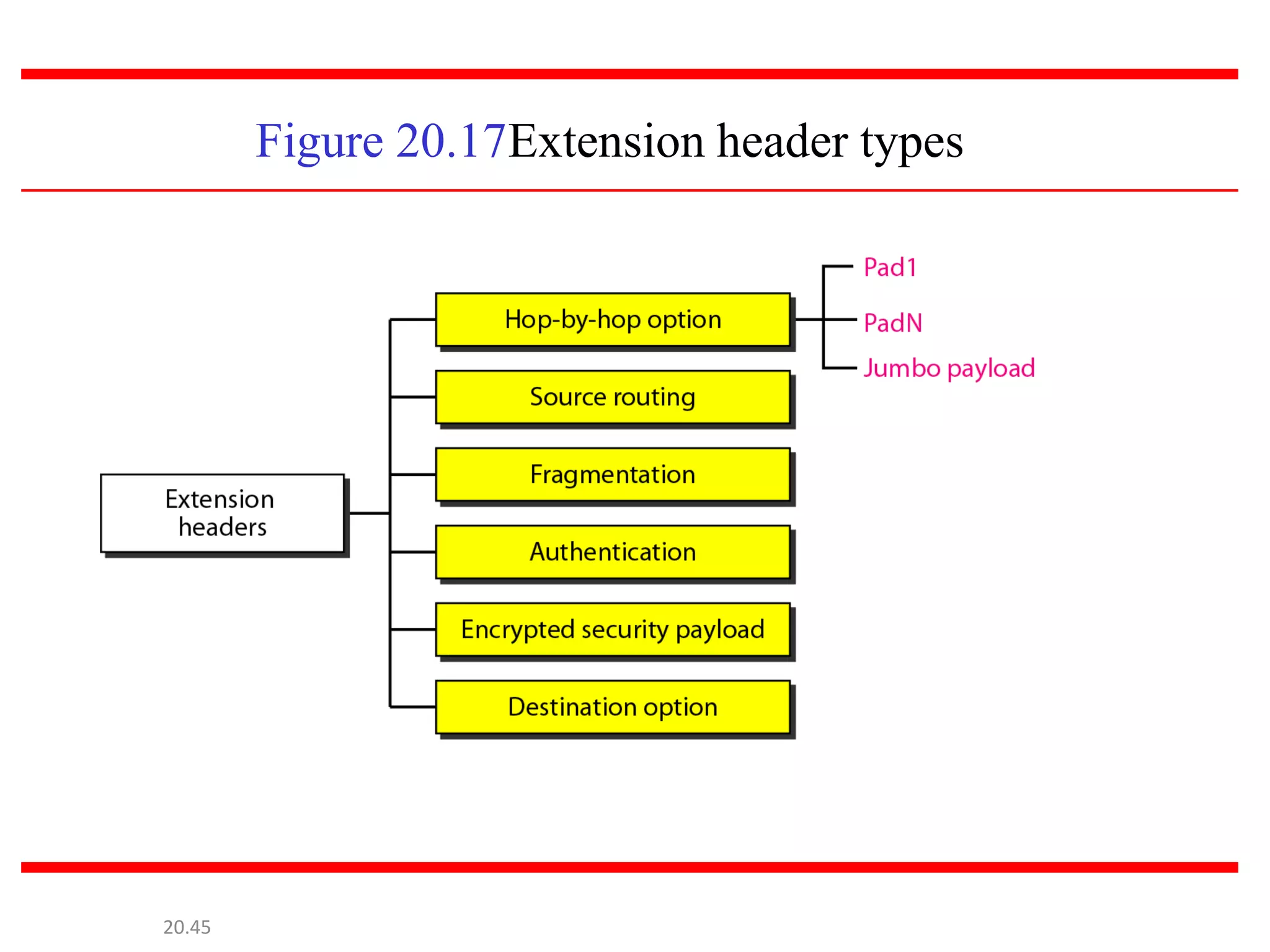
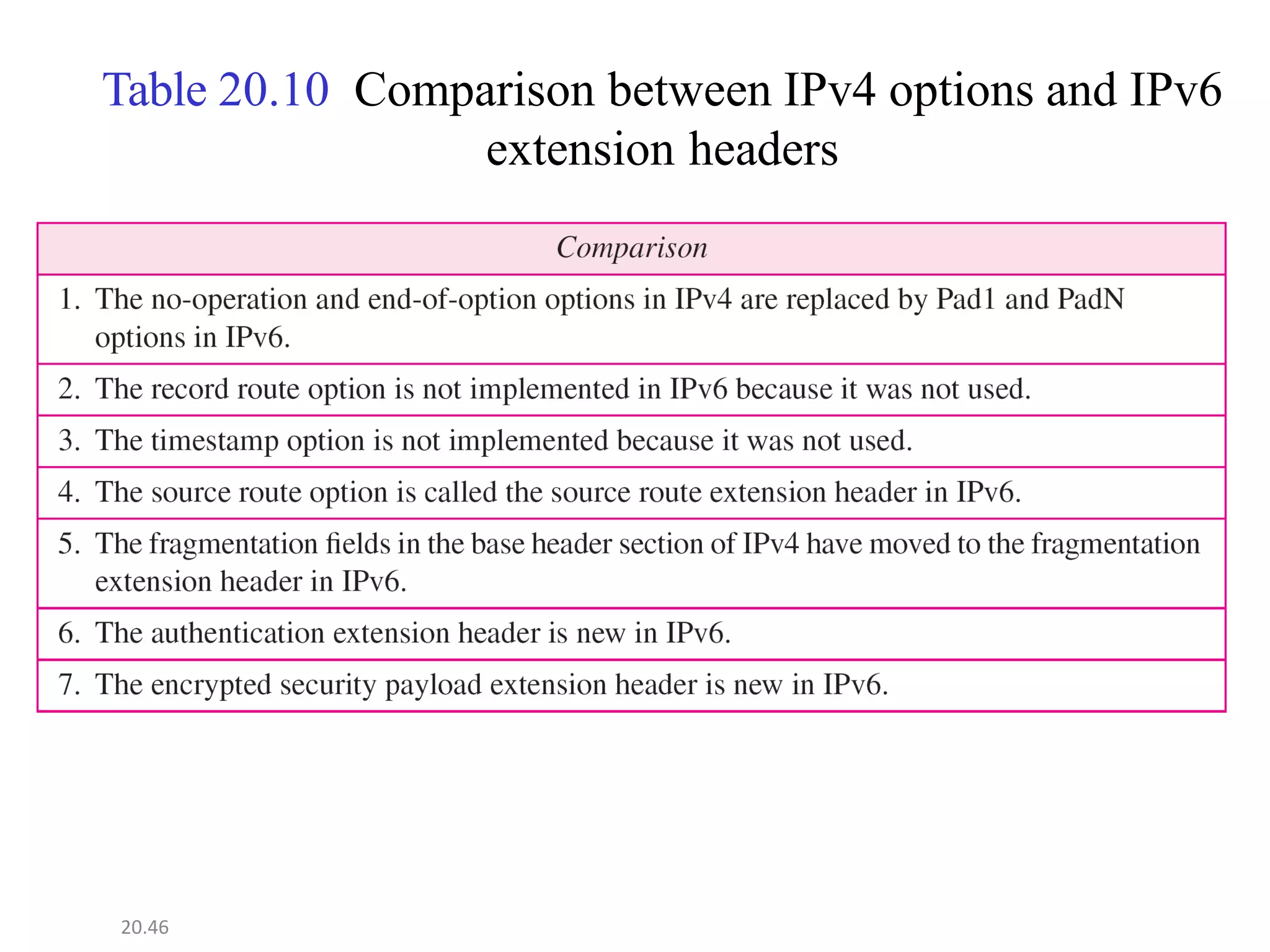
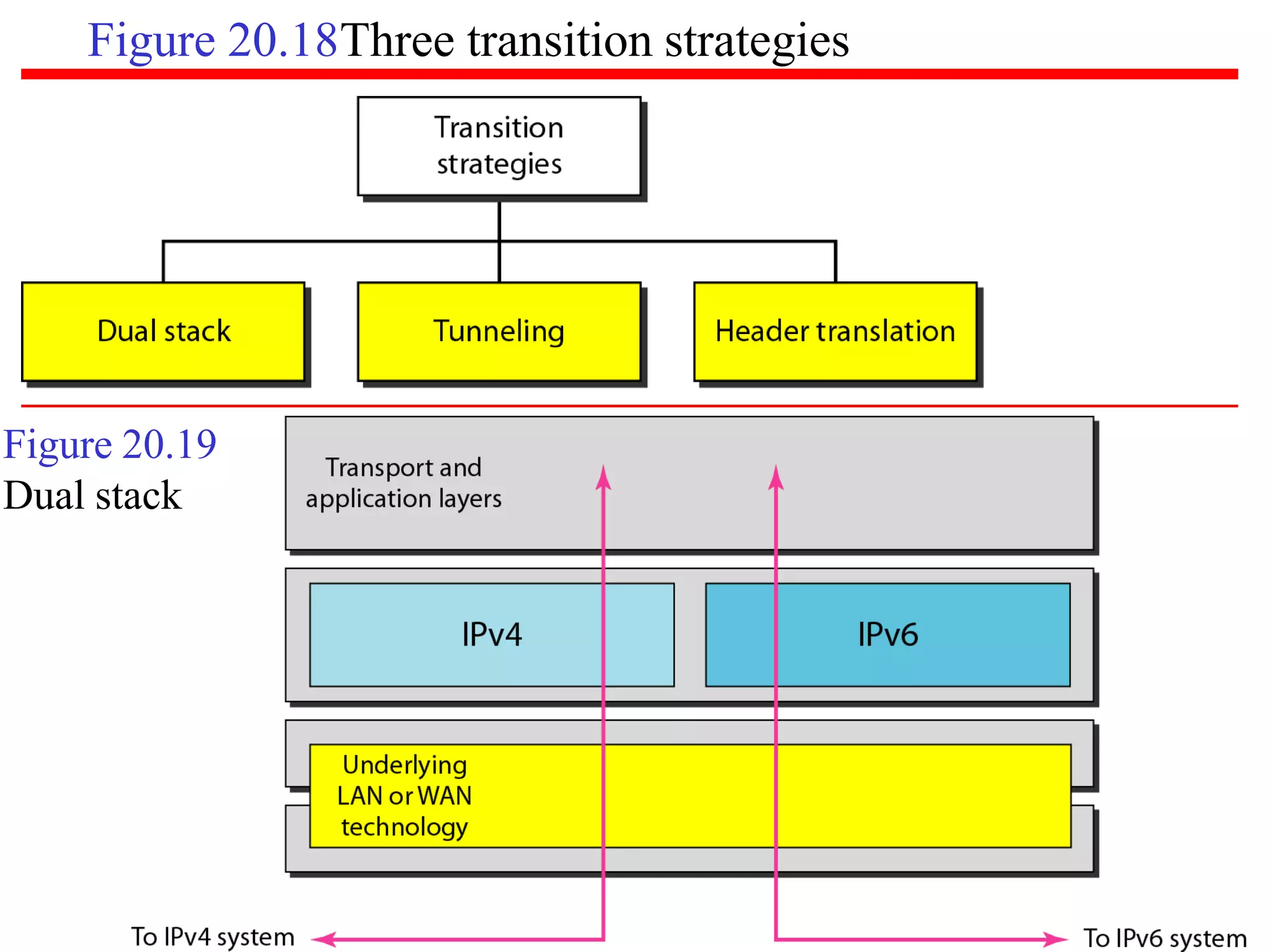
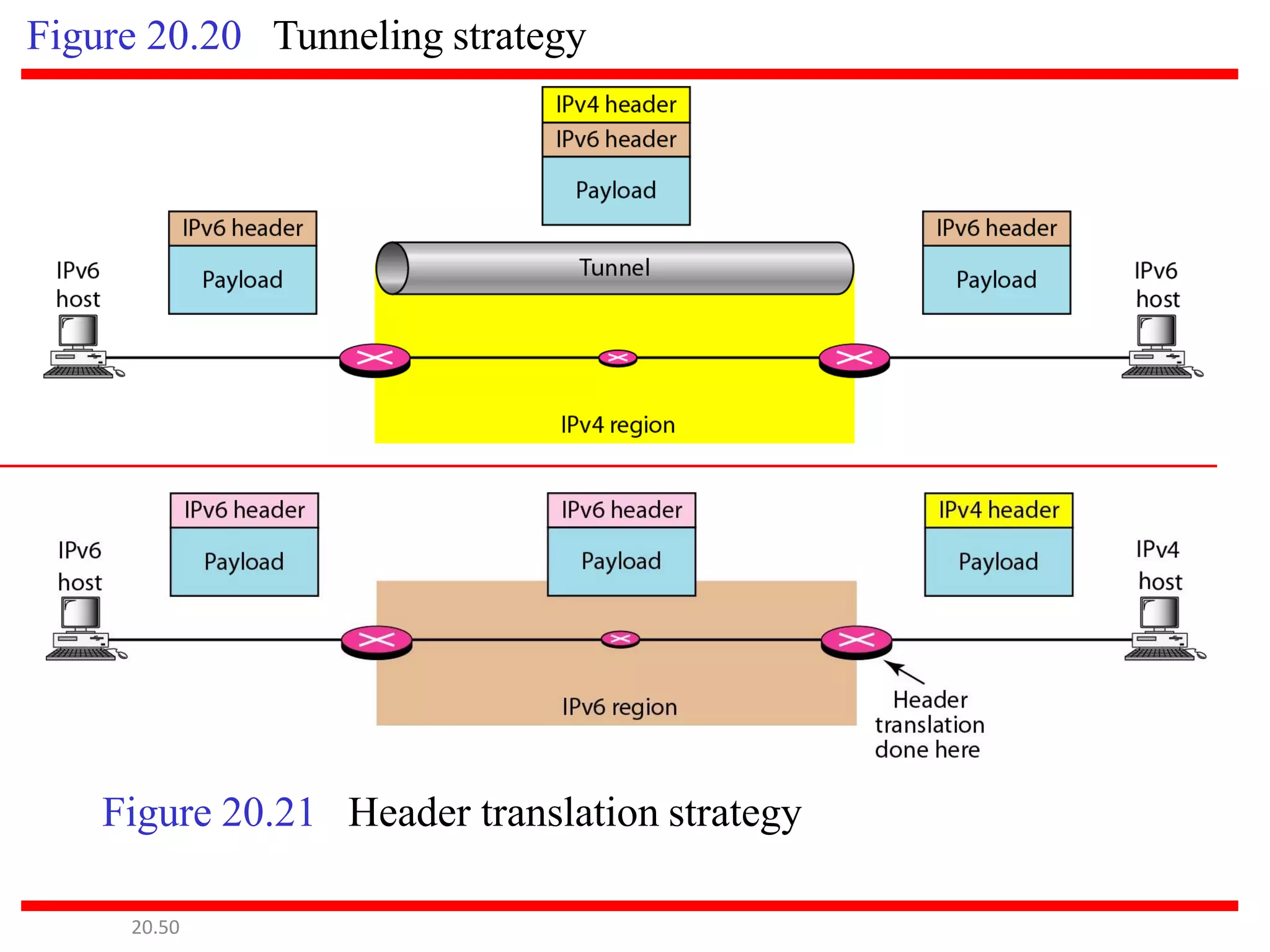
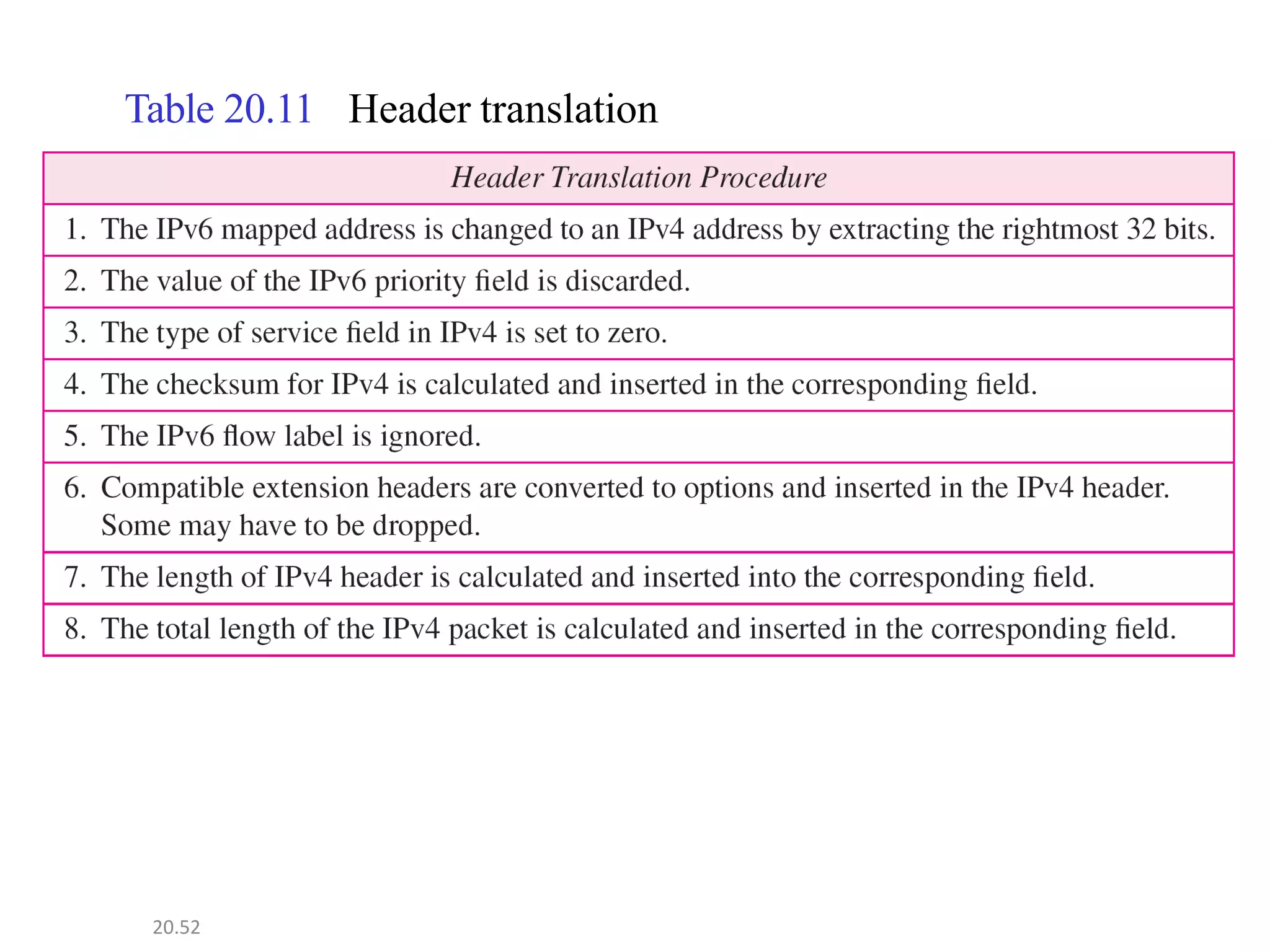
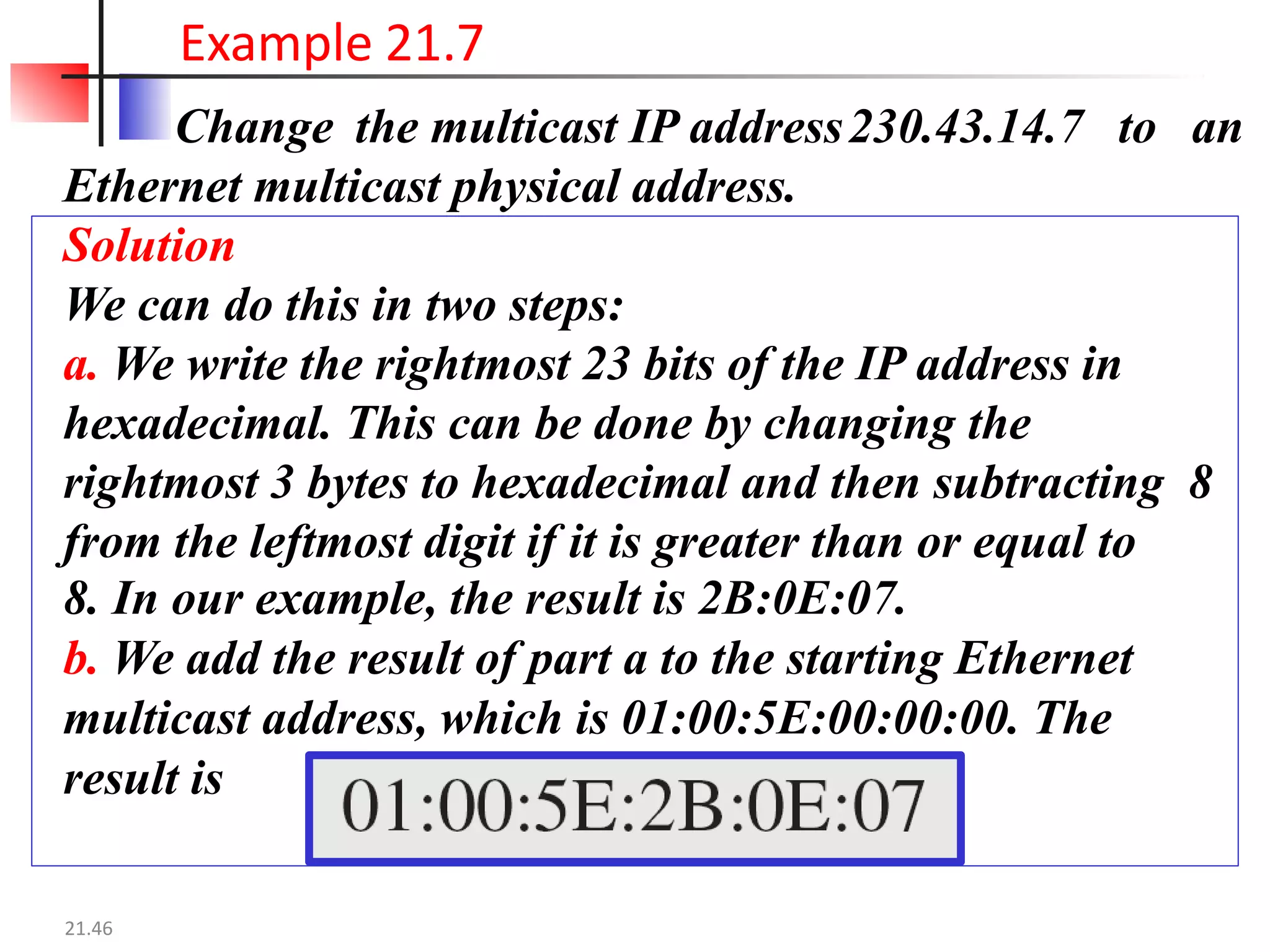
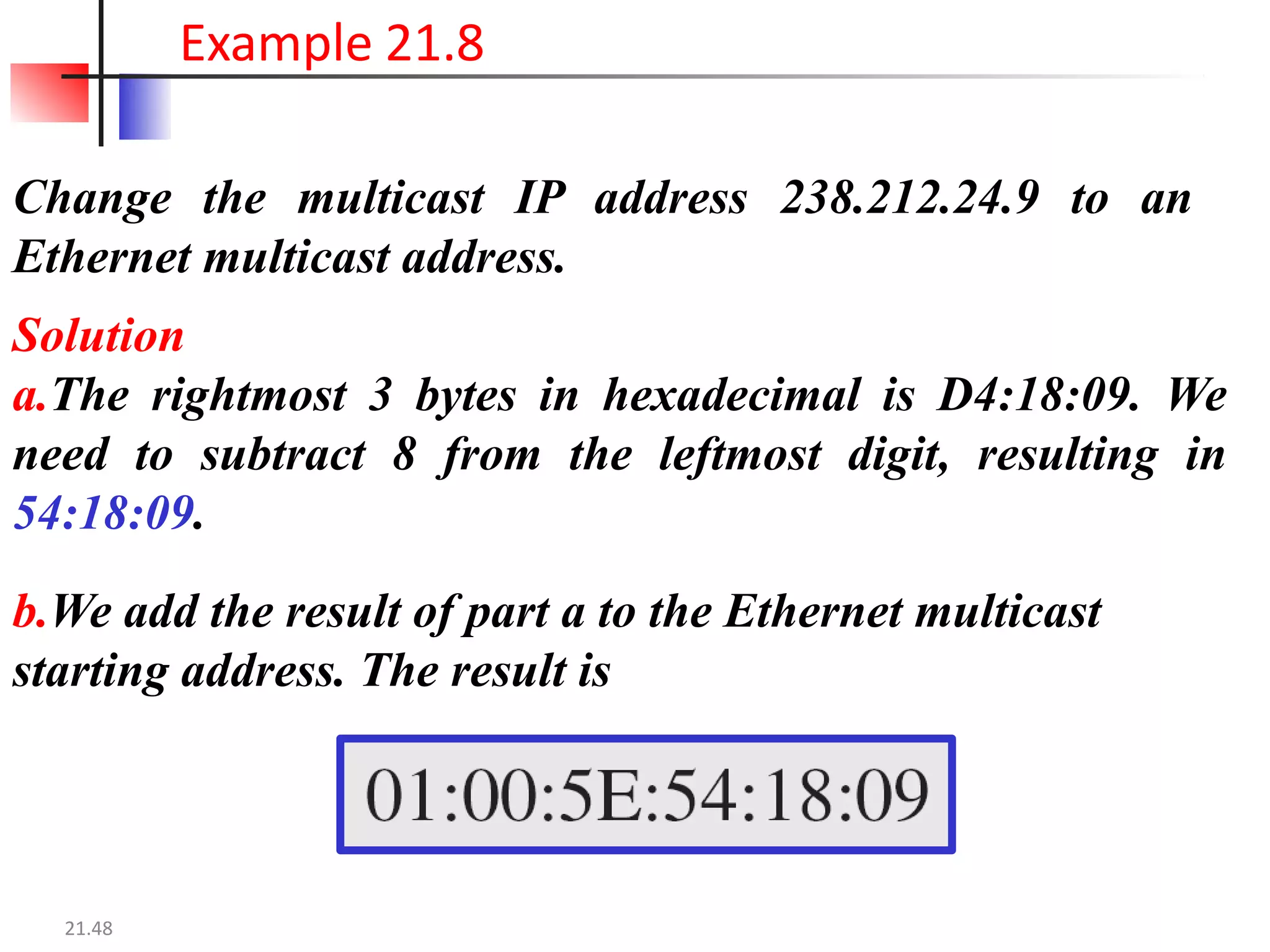
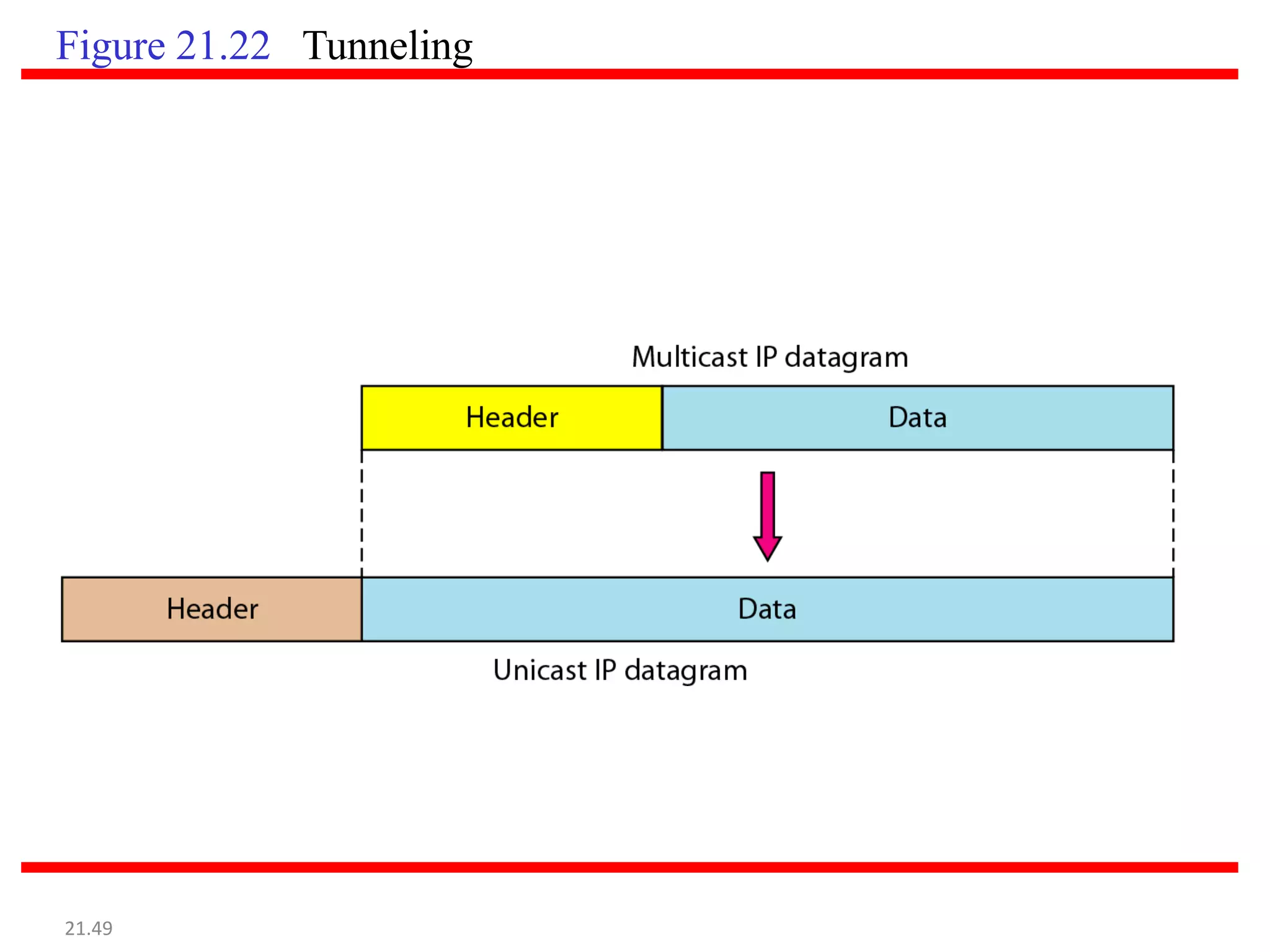
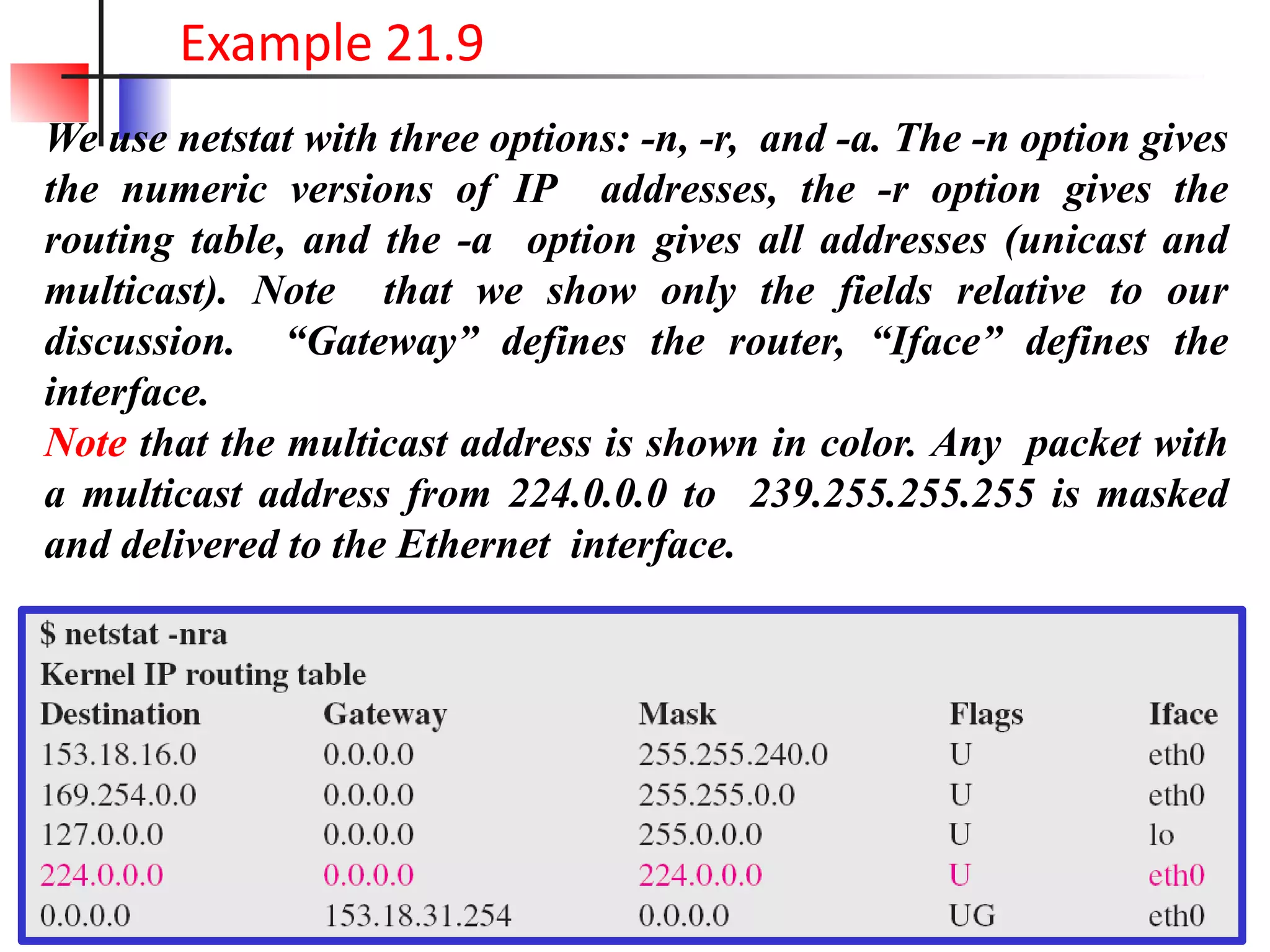
The document discusses the architecture of routers, detailing their components and evolution from early general-purpose computers to high-performance distributed systems in modern networks. It covers the intricacies of IPv4 and IPv6 addressing, highlighting the differences between classful and classless addressing, as well as the transition from IPv4 to IPv6 due to address depletion issues. Additionally, it emphasizes network layer operations essential for internetworking, including packet processing, routing decisions, and the role of Internet Protocol.