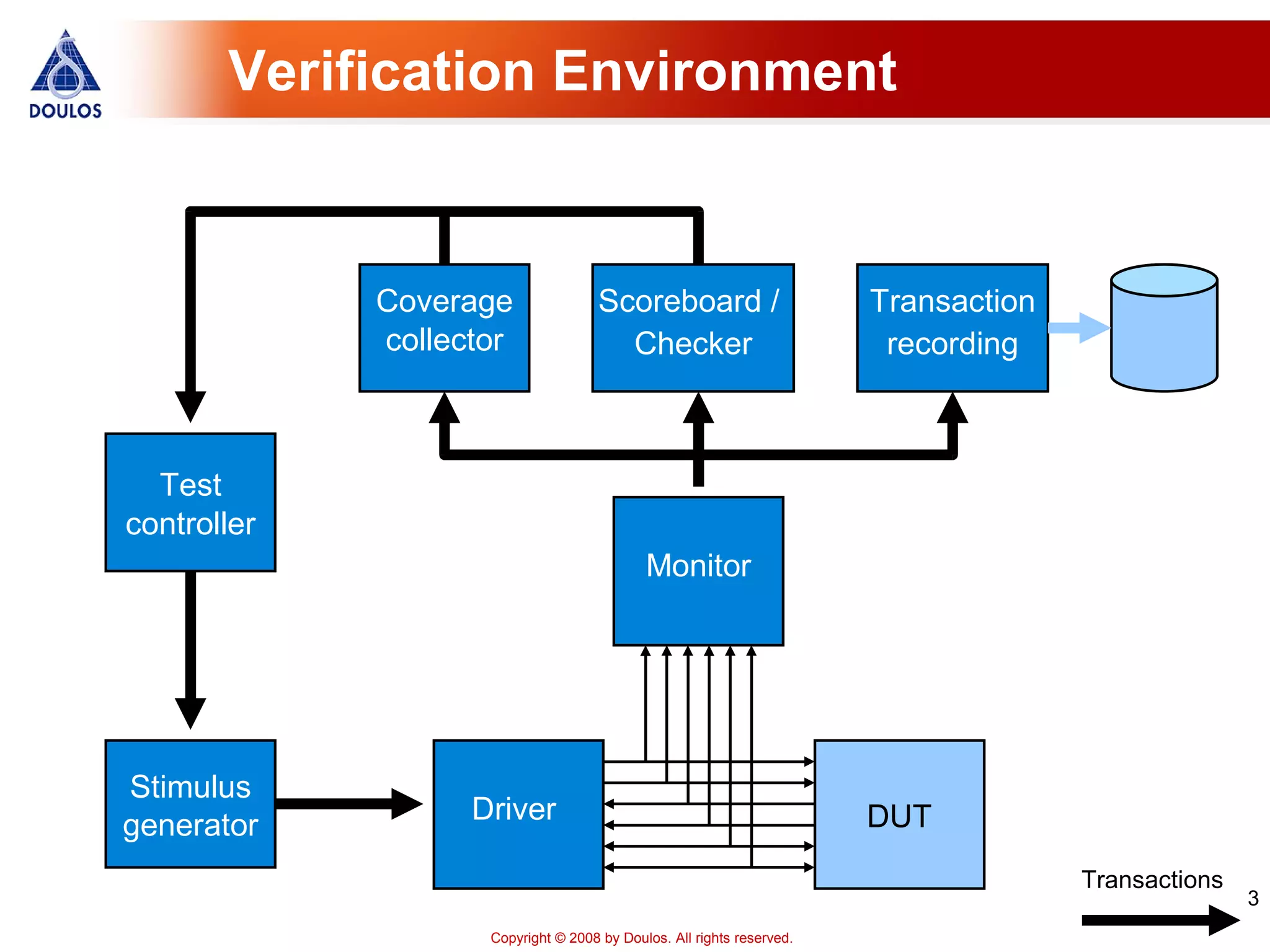
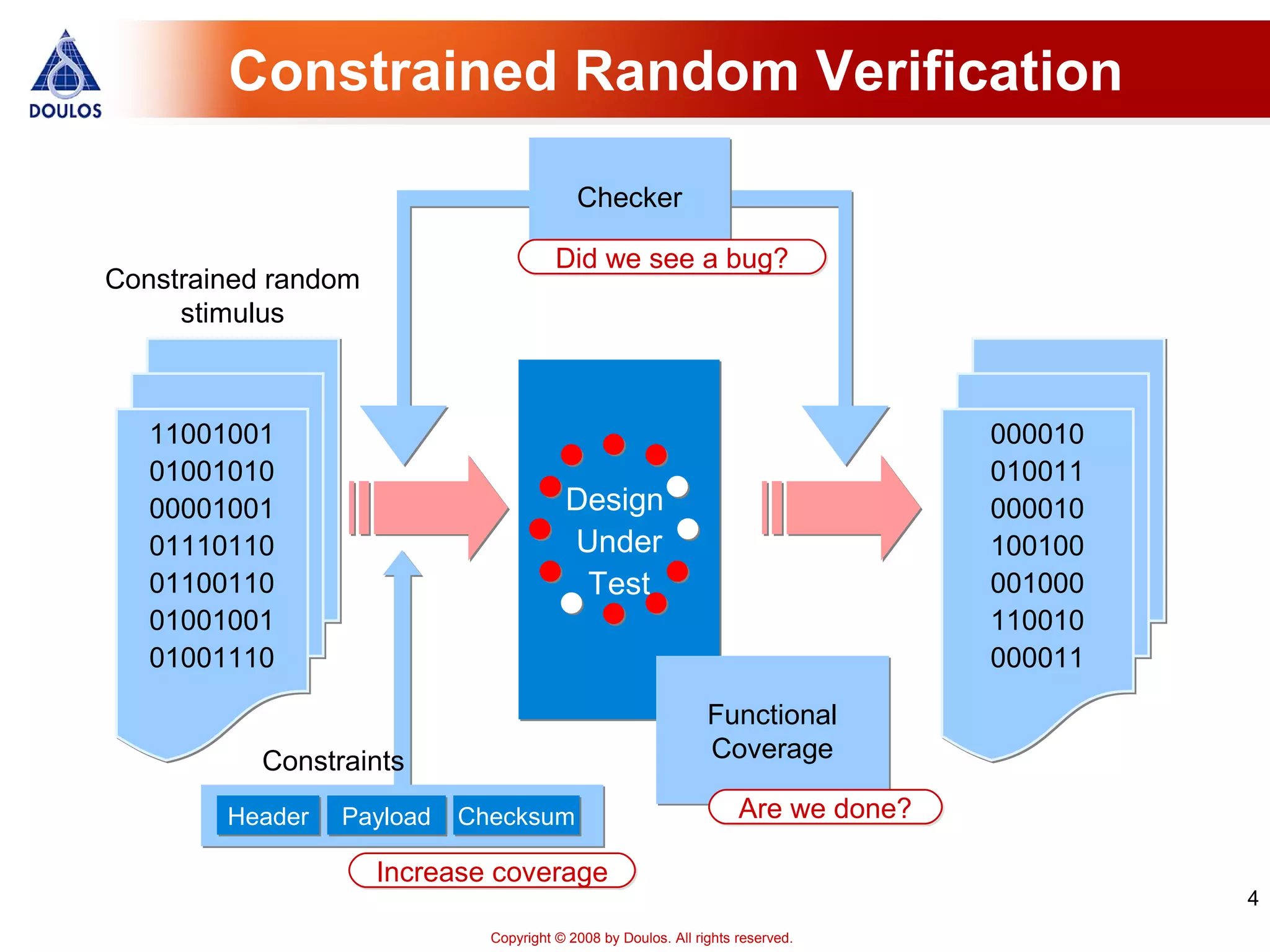
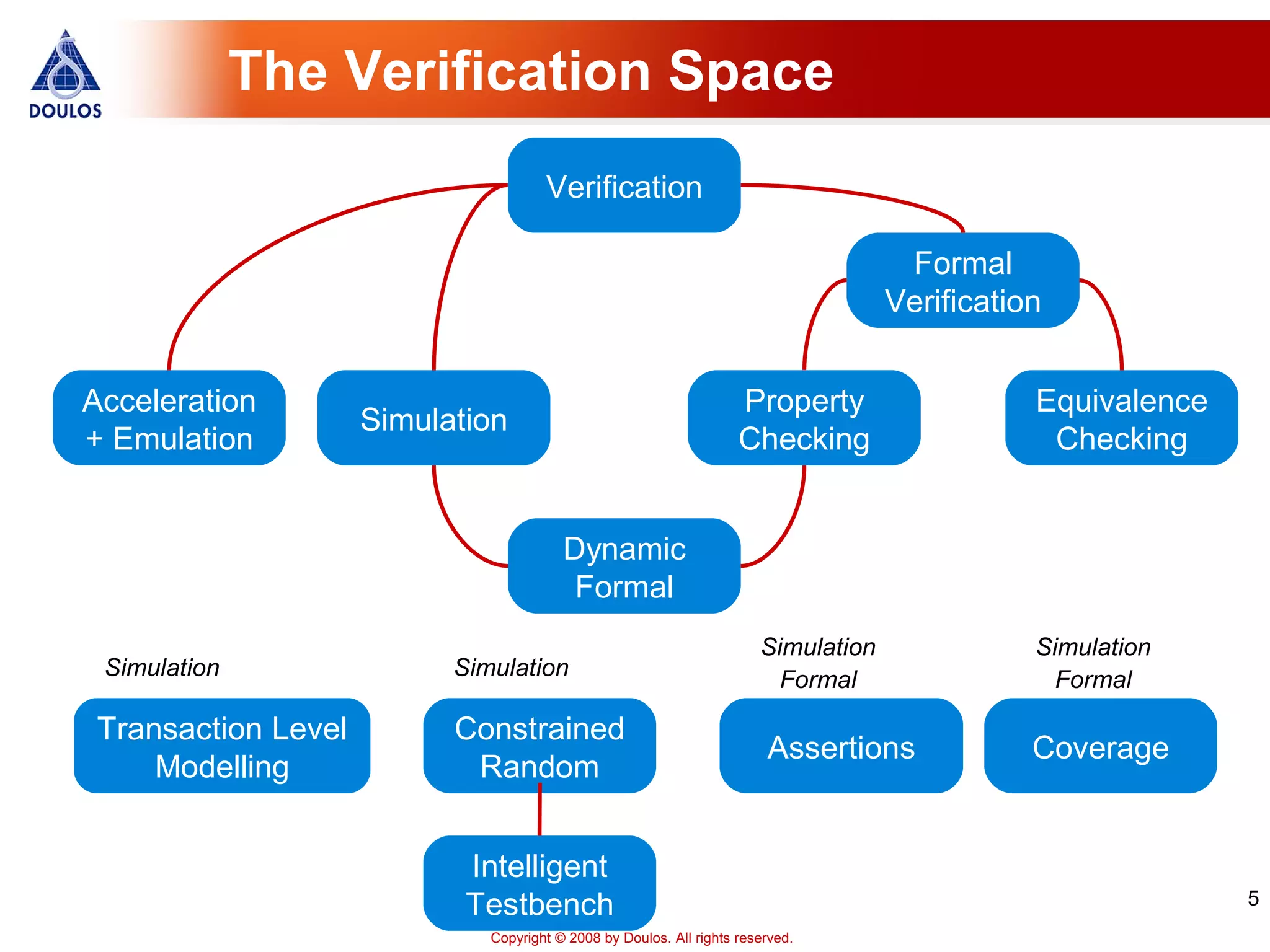
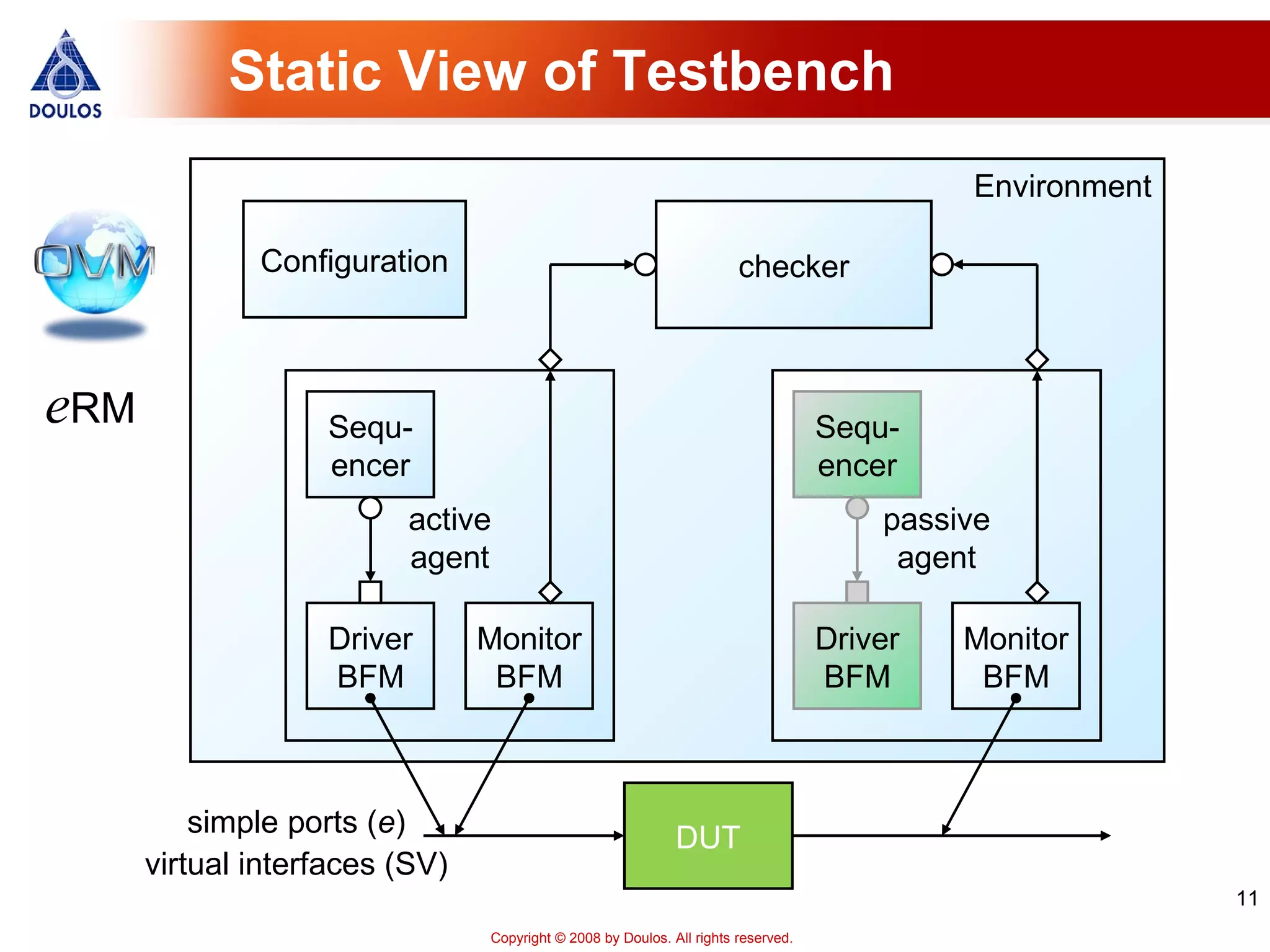
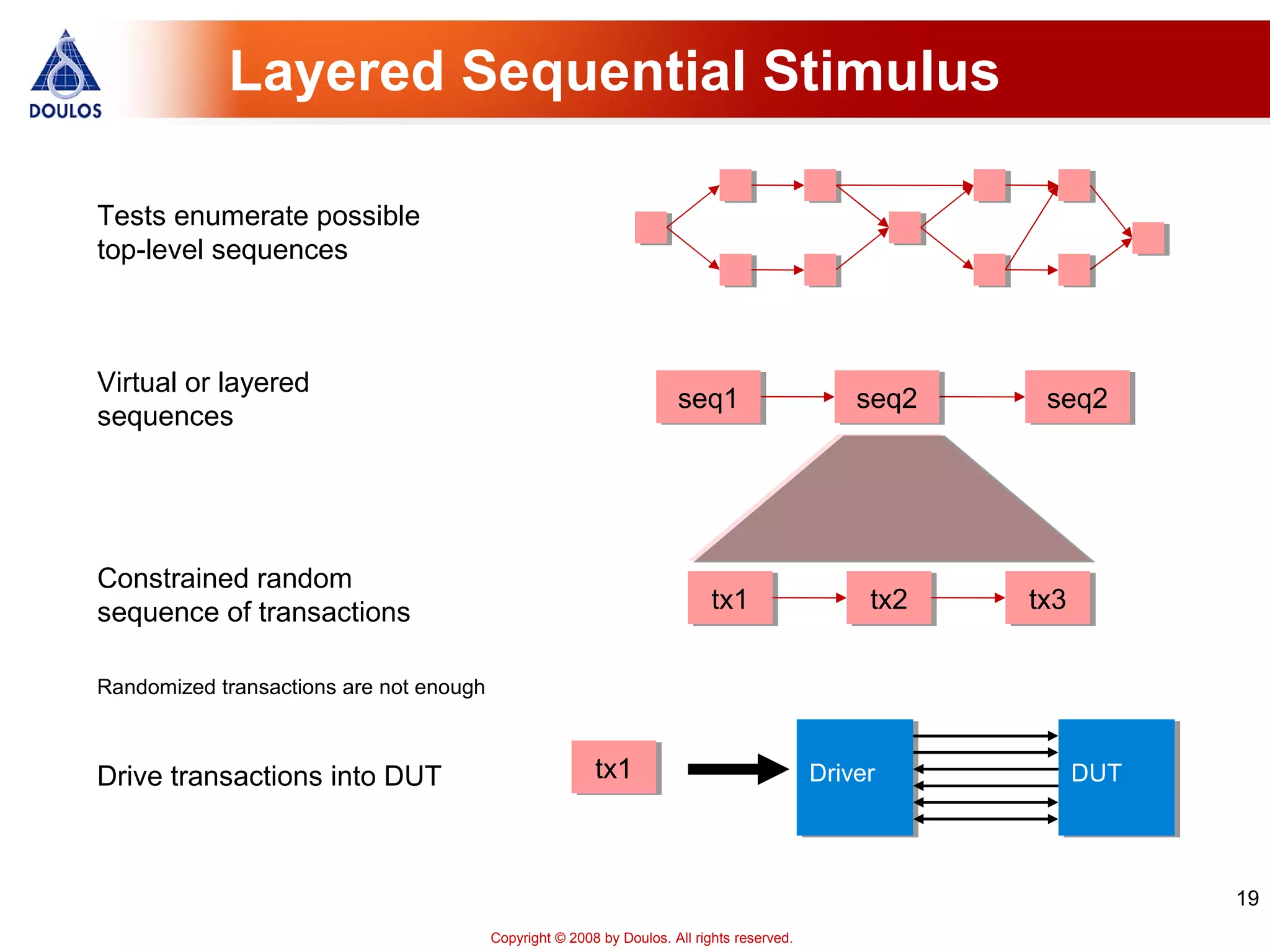
This document discusses verification methodologies like OVM, VMM, and eRM. It provides an overview of their key features such as constrained random stimulus, coverage-driven verification, and reusable verification environments. It also examines standards development efforts and looks at trends like growing adoption of verification IP and efforts to improve interoperability between methodologies.

![21
Copyright © 2008 by Doulos. All rights reserved.
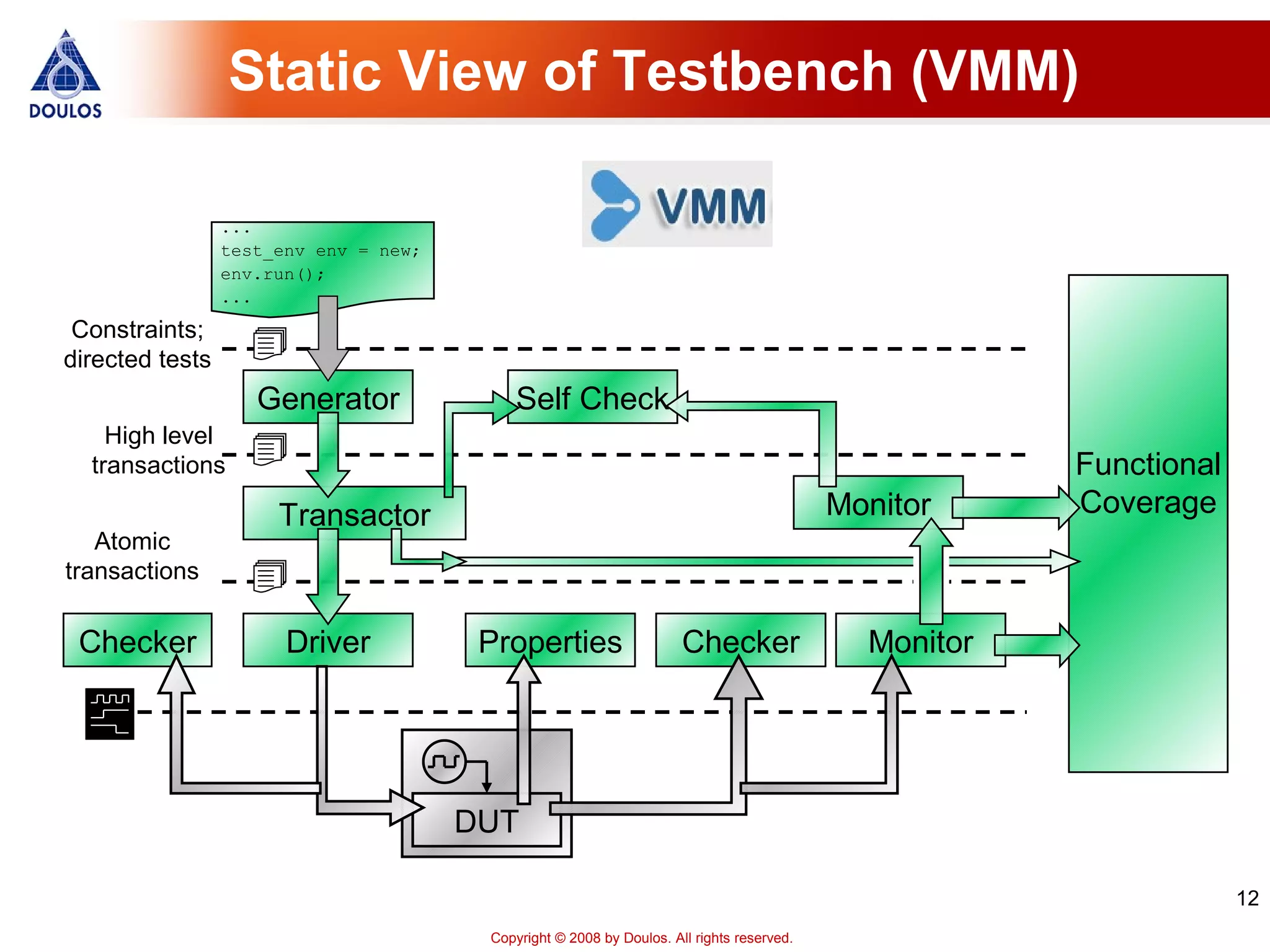
Scenario Generator (VMM)
Verification environment
Scenario generator
Downstream transactor
generator's output channel
atomic
scenario_set
burst[1]
[0]
RMW[2]
burst
items
select_scenario
select
copies of items](https://image.slidesharecdn.com/jonathanbromleydoulos-130422122710-phpapp02/75/The-Verification-Methodology-Landscape-21-2048.jpg)