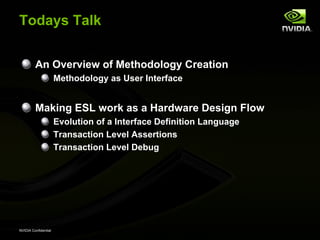
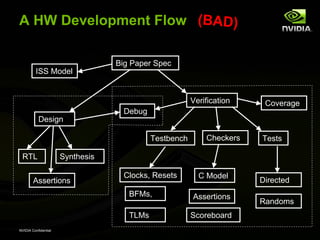
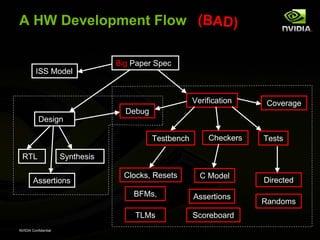
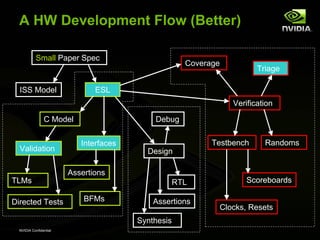
1. The document discusses methodologies for hardware verification and developing an efficient verification flow.
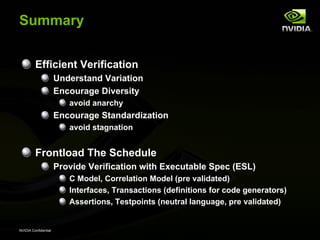
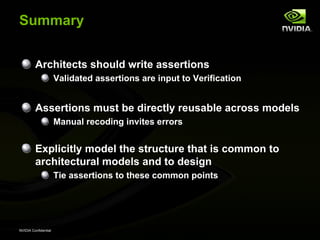
2. It recommends defining a conceptual framework for the flow to standardize some aspects while allowing for diversity and innovation.
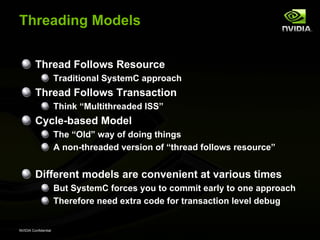
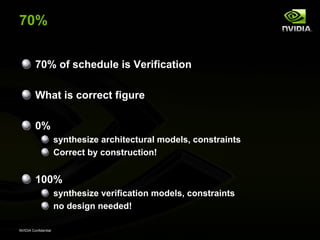
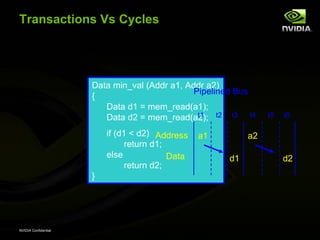
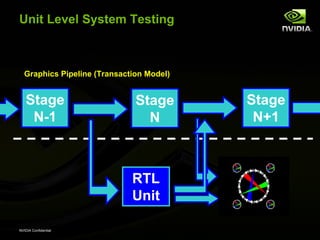
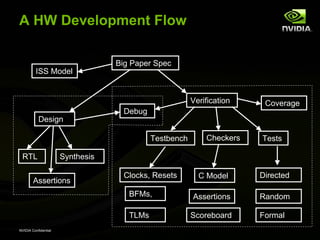
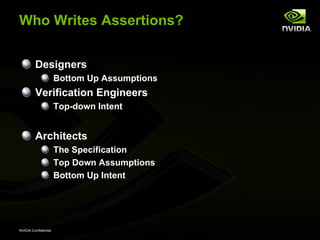
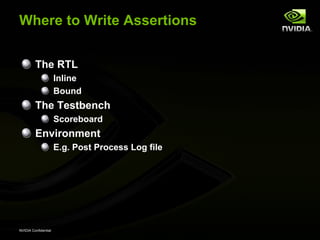
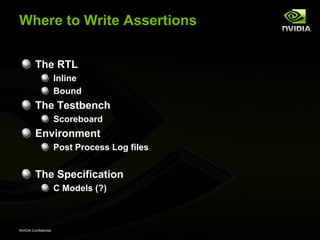
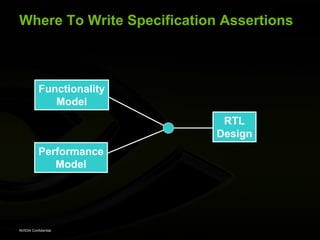
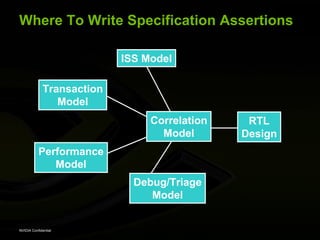
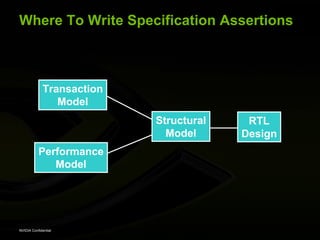
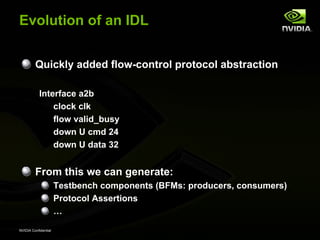
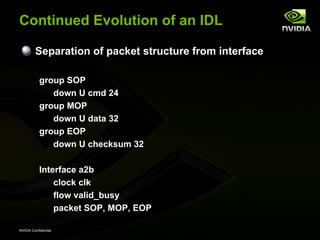
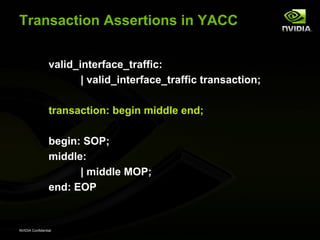
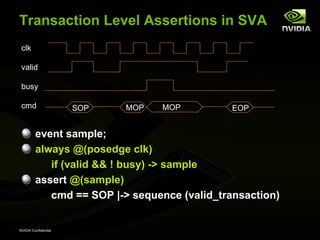
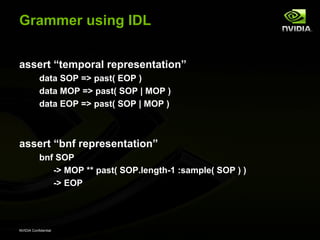
3. Using transaction level modeling and assertions in early stages like the specification model can help validation before the RTL design stage. Assertions can be written at different levels from the specification to the RTL and testbench.


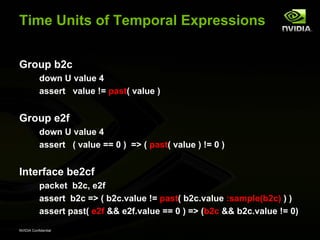
![Cycle Level Assertions in SVA
clk
cmd SOP MOP MOP EOP
sequence valid_trans;
(cmd==SOP)
(##1 cmd != SOP && cmd != EOP) [*0:$]
##1 cmd == EOP
endsequence
a_well_formed_transaction: assert @(posedge clk)
cmd == SOP |-> sequence (valid_trans)
NVIDIA Confidential](https://image.slidesharecdn.com/whippq32008sv-130424131024-phpapp02/85/Stop-Writing-Assertions-Efficient-Verification-Methodology-35-320.jpg)
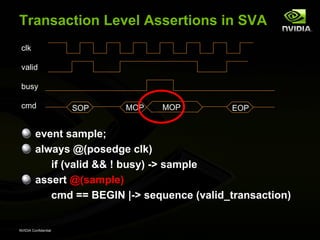
![Transaction Level Assertions in SVA
clk
valid
cmd SOP MOP MOP EOP
sequence valid_transaction;
(cmd==SOP)
(##1 cmd != SOP && cmd != EOP) [*0:$]
##1 cmd == EOP
endsequence
NVIDIA Confidential](https://image.slidesharecdn.com/whippq32008sv-130424131024-phpapp02/85/Stop-Writing-Assertions-Efficient-Verification-Methodology-36-320.jpg)
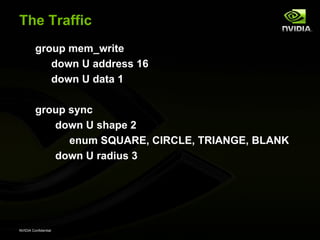
![Accumulate Memory State
group mem_write
down U address 16
down U data 1
assign mem[ x = 0 .. 15 ][ y = 0 .. 15 ]
= past( data :sample( address == {x,y} ))
NVIDIA Confidential](https://image.slidesharecdn.com/whippq32008sv-130424131024-phpapp02/85/Stop-Writing-Assertions-Efficient-Verification-Methodology-49-320.jpg)
![Add Predicates
group_more mem_write
assign is_circle[ r = 0..7 ] = “&&”(
[ x = -8 .. 7 ]
[ y = -8 .. 7 ]
mem[ x+8 ][ y+8 ] == ( x**2 + y**2 <= r**2 )
)
NVIDIA Confidential](https://image.slidesharecdn.com/whippq32008sv-130424131024-phpapp02/85/Stop-Writing-Assertions-Efficient-Verification-Methodology-50-320.jpg)
![Define the interface
interface render2memory
clock mem_clk
flow valid_busy
packet sync, mem_write
assert “correct sync shape”
sync && sync.shape == CIRCLE
=> past( mem_write.is_circle[ sync.radius ] )
NVIDIA Confidential](https://image.slidesharecdn.com/whippq32008sv-130424131024-phpapp02/85/Stop-Writing-Assertions-Efficient-Verification-Methodology-51-320.jpg)
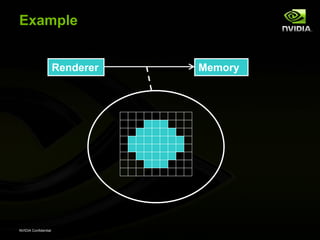
![Example
Renderer Memory
assert “correct sync shape”
sync && sync.shape == CIRCLE
=> past( mem_write.is_circle[ sync.radius ] )
NVIDIA Confidential](https://image.slidesharecdn.com/whippq32008sv-130424131024-phpapp02/85/Stop-Writing-Assertions-Efficient-Verification-Methodology-52-320.jpg)