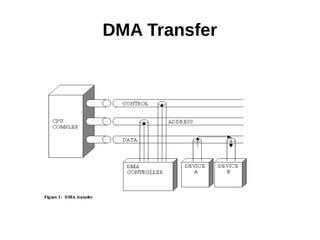
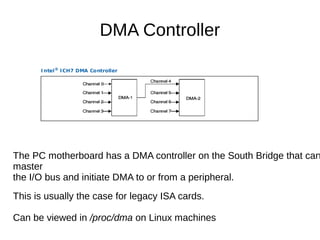
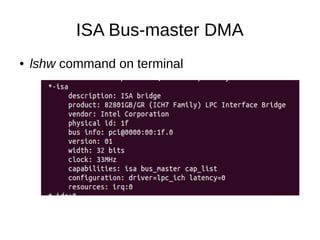
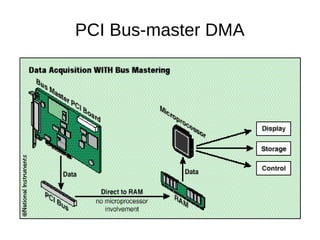
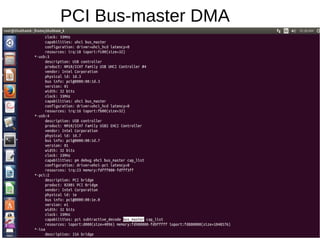
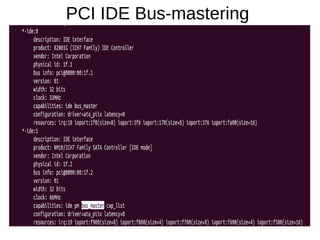
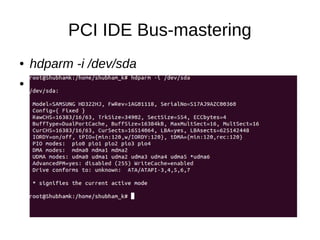
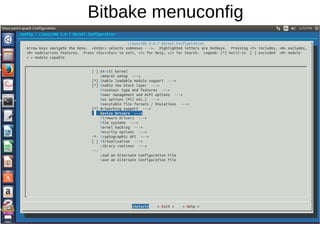
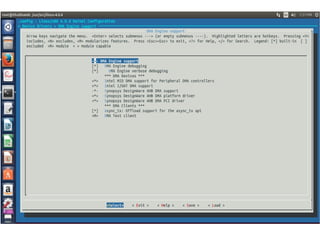
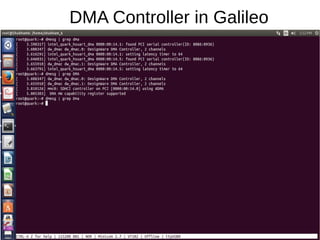
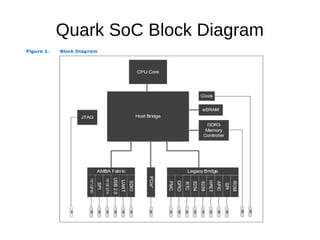
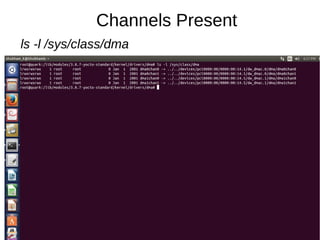
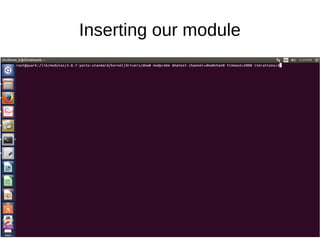
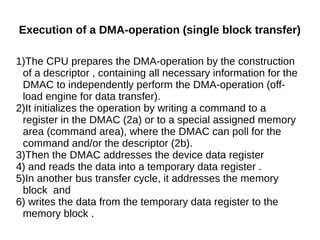
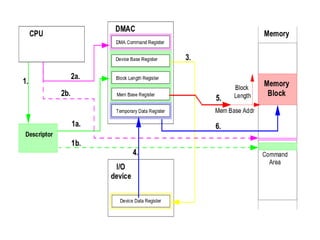
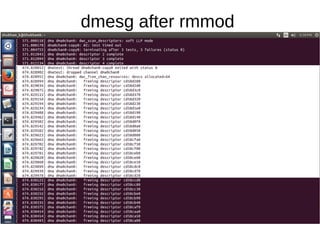
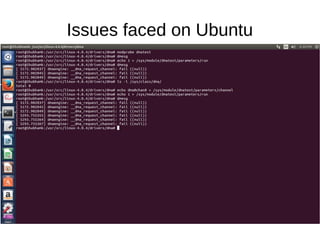
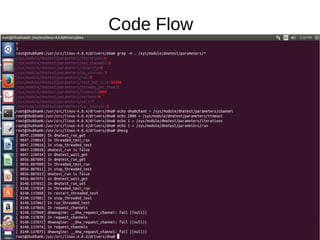
The document outlines various data transfer mechanisms used in computer-based data acquisition, focusing on polling, interrupts, and DMA (Direct Memory Access). It describes the functionality of DMA controllers on PC motherboards, detailing native and bus-master DMA types, as well as their implementations and performance implications. Additionally, it provides insights into the DMA operation code flow and references for further reading on related topics.