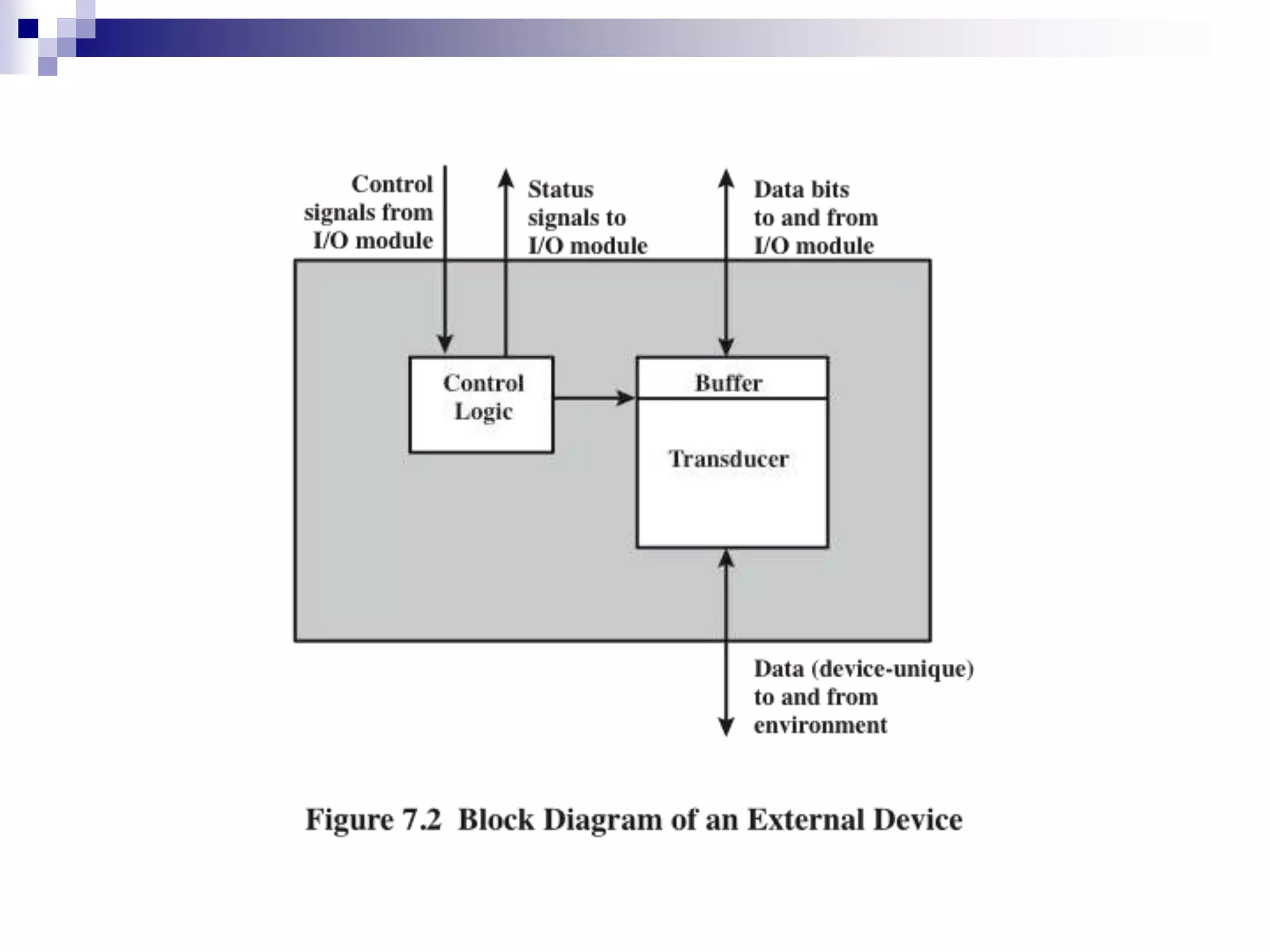
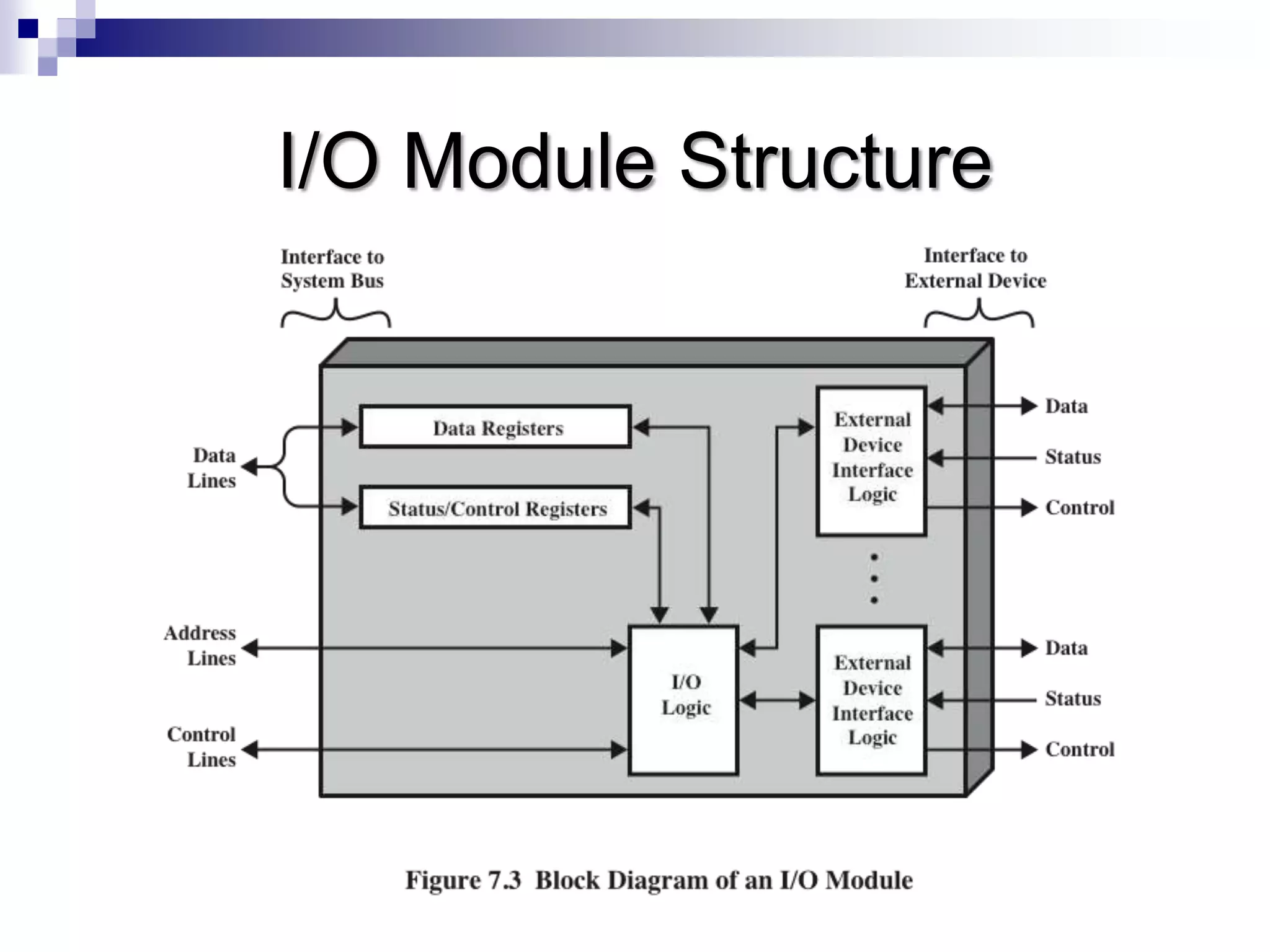
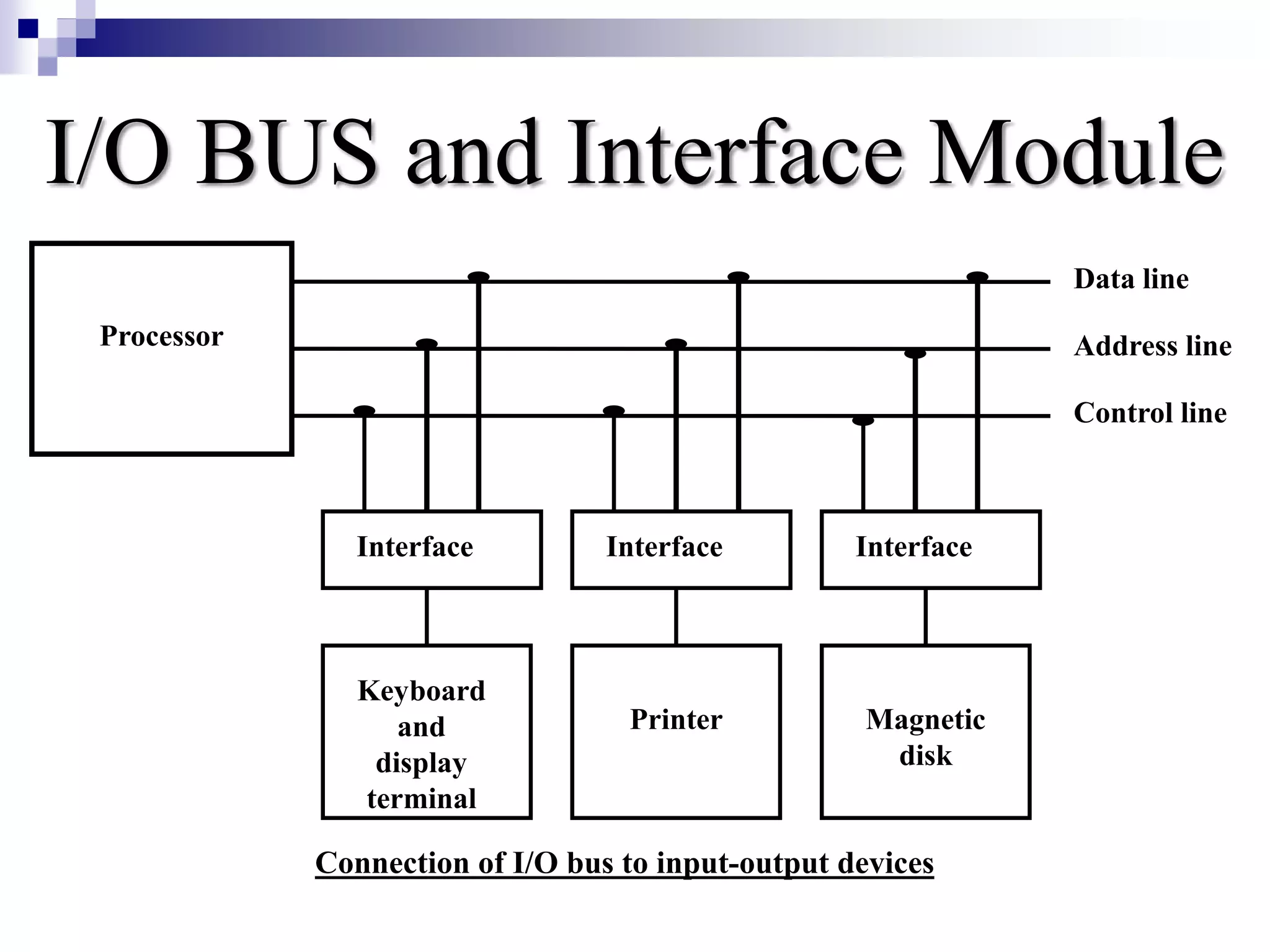
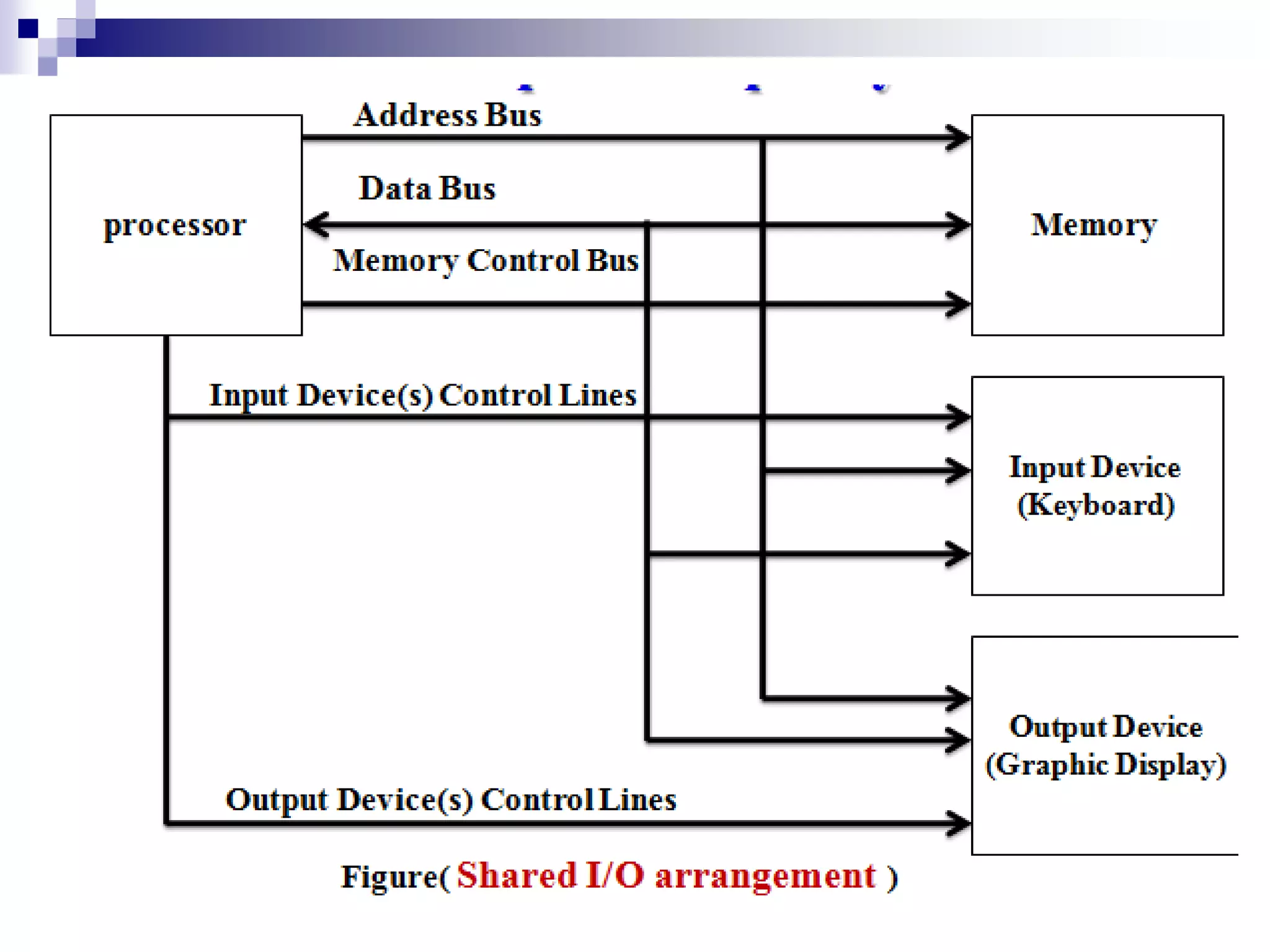
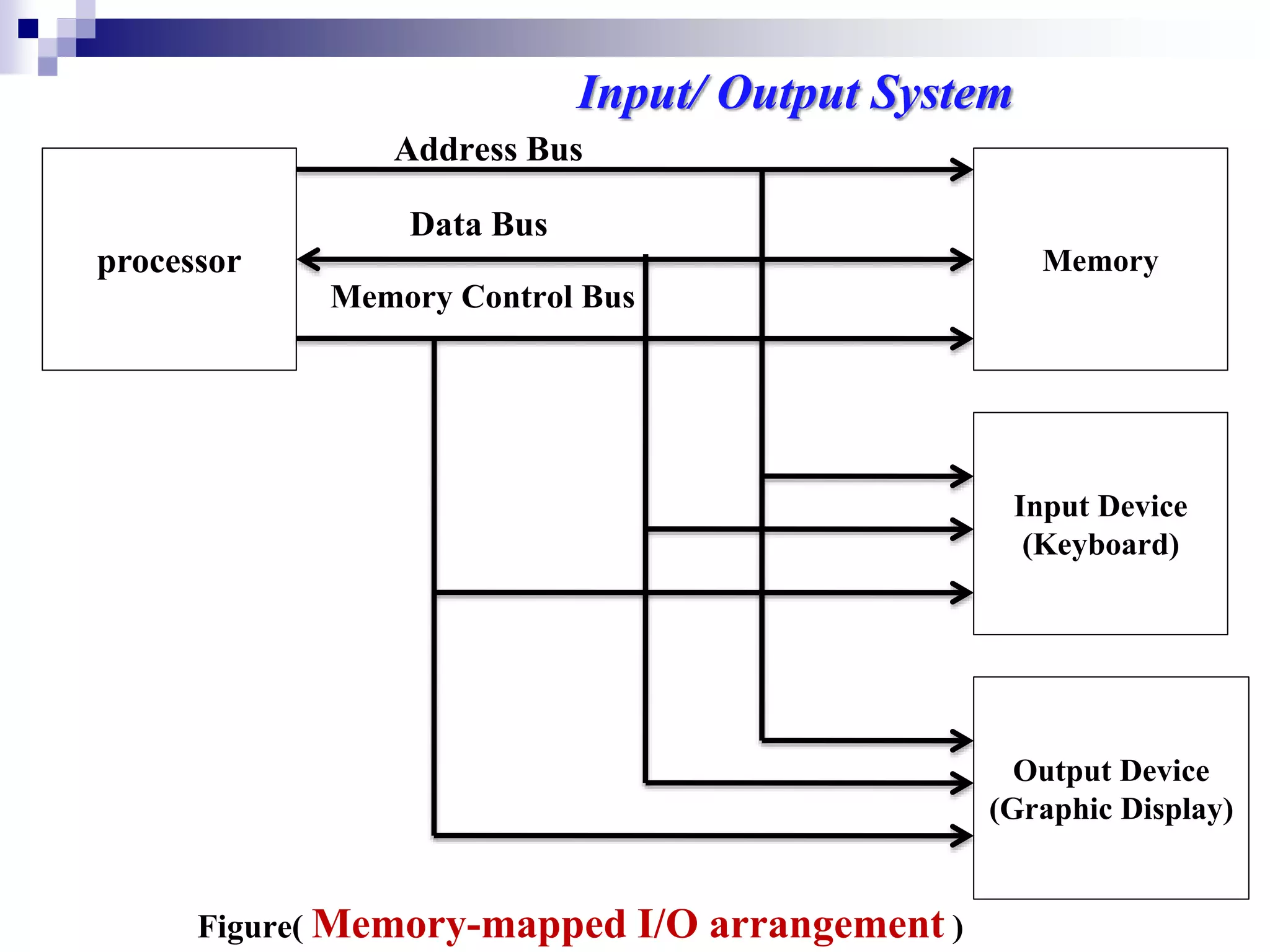
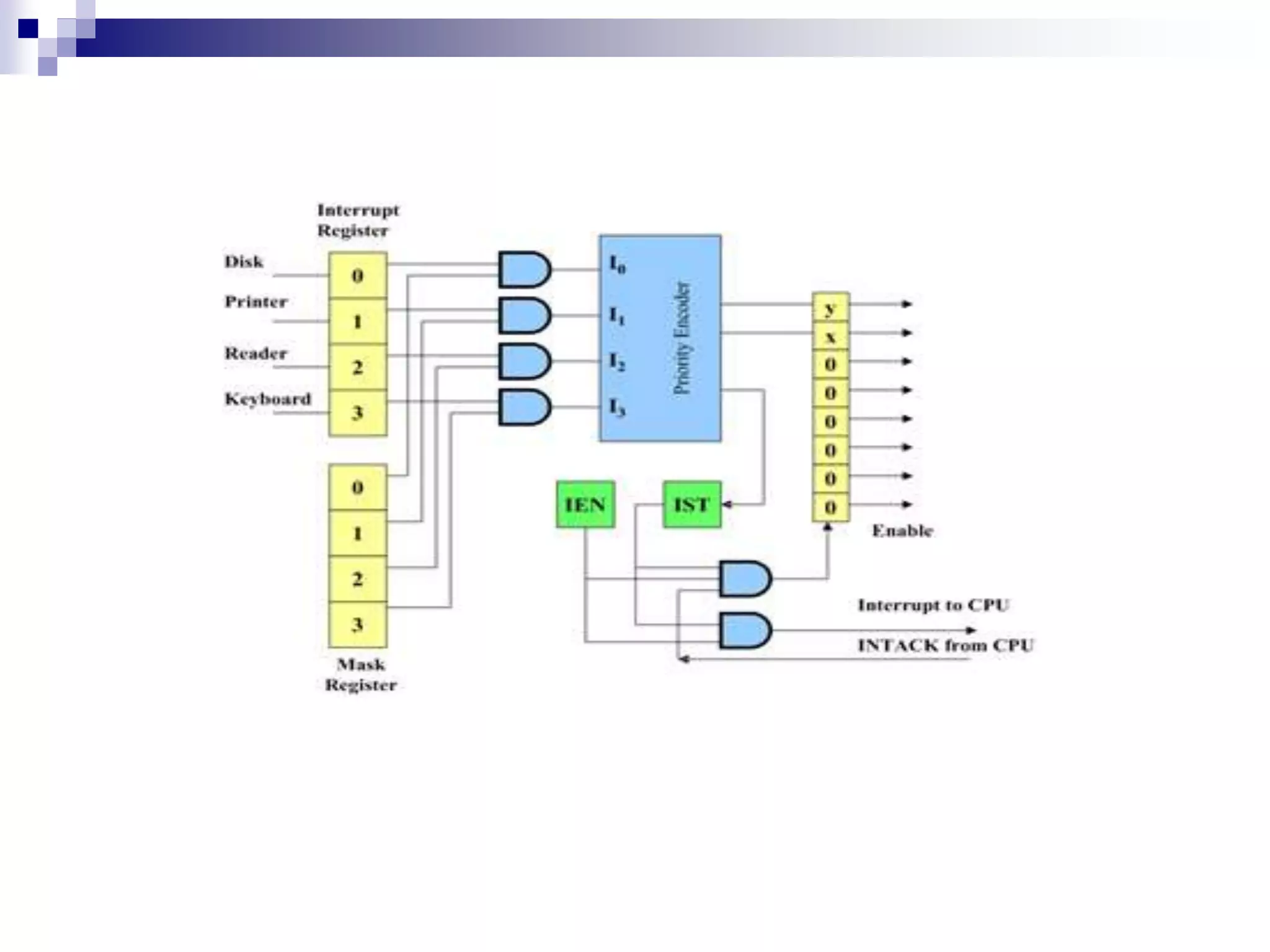
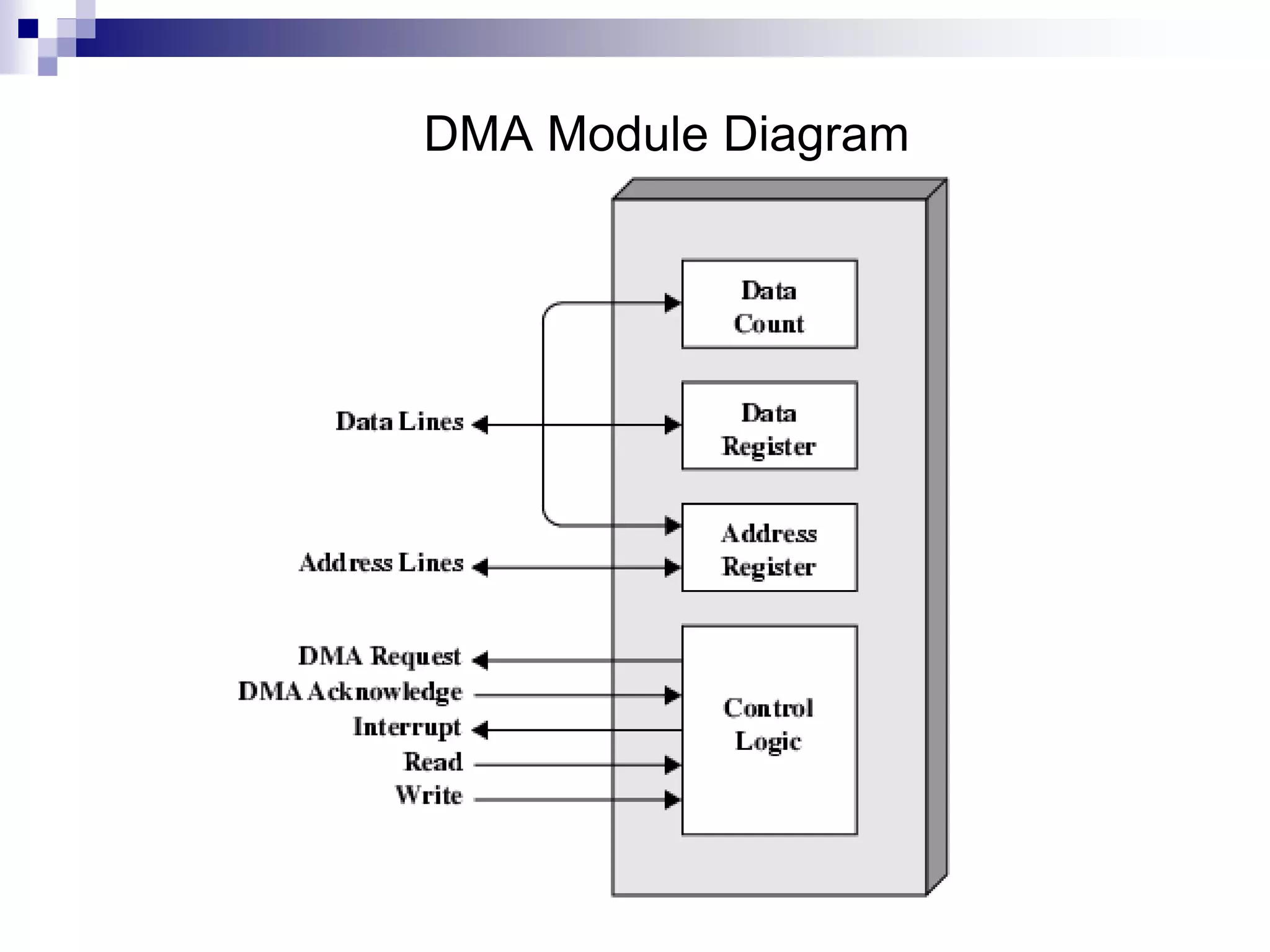
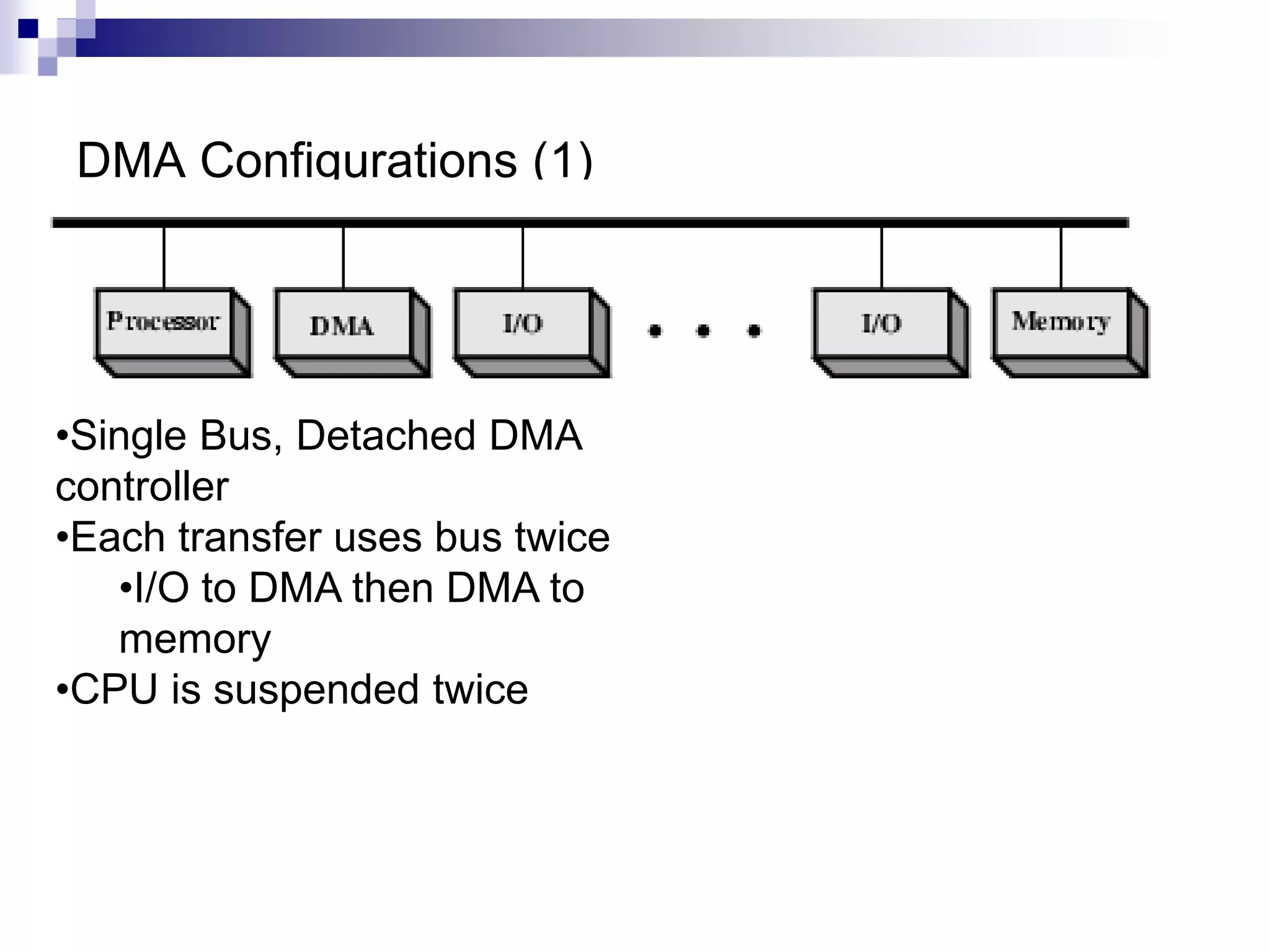
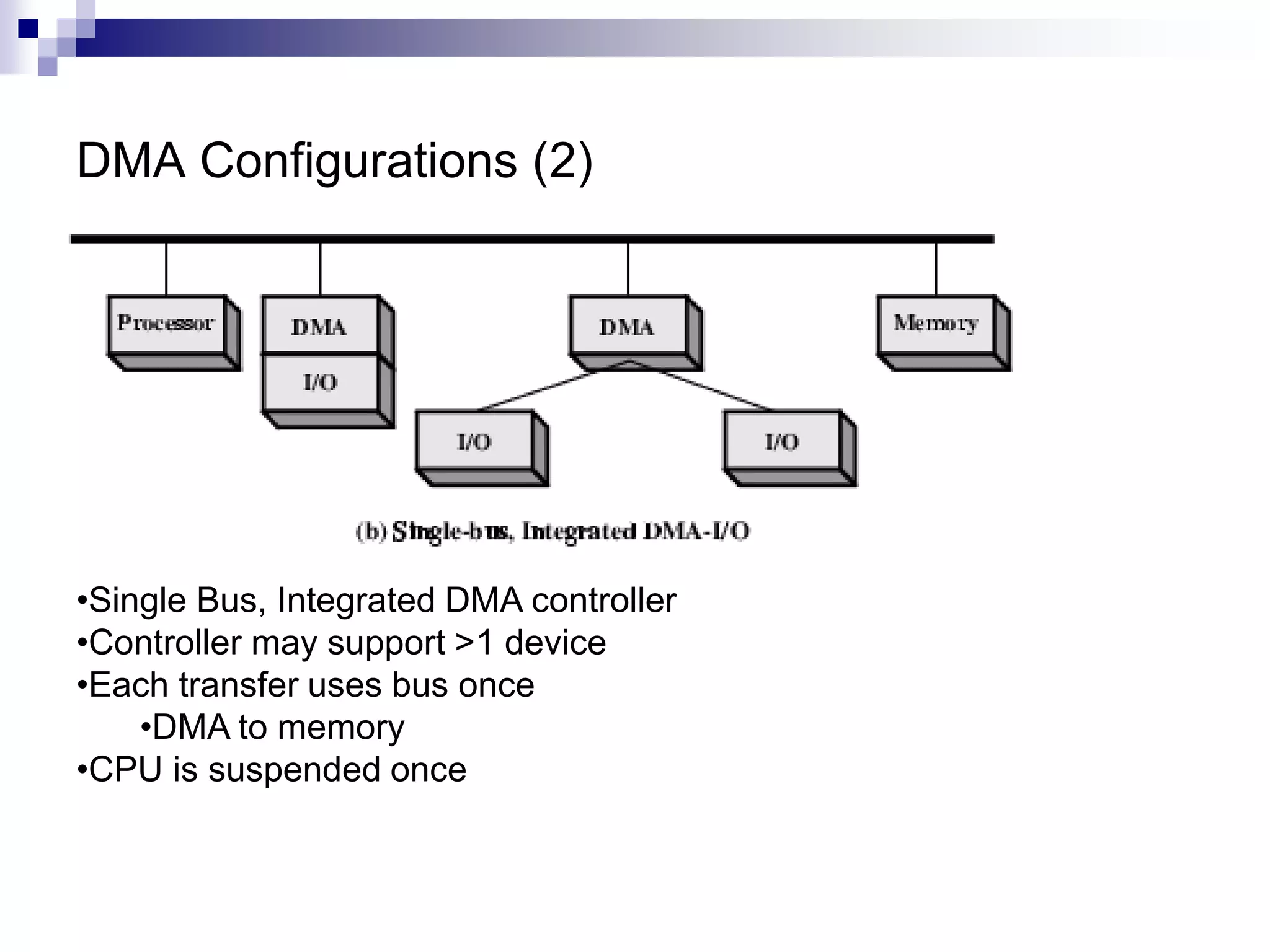
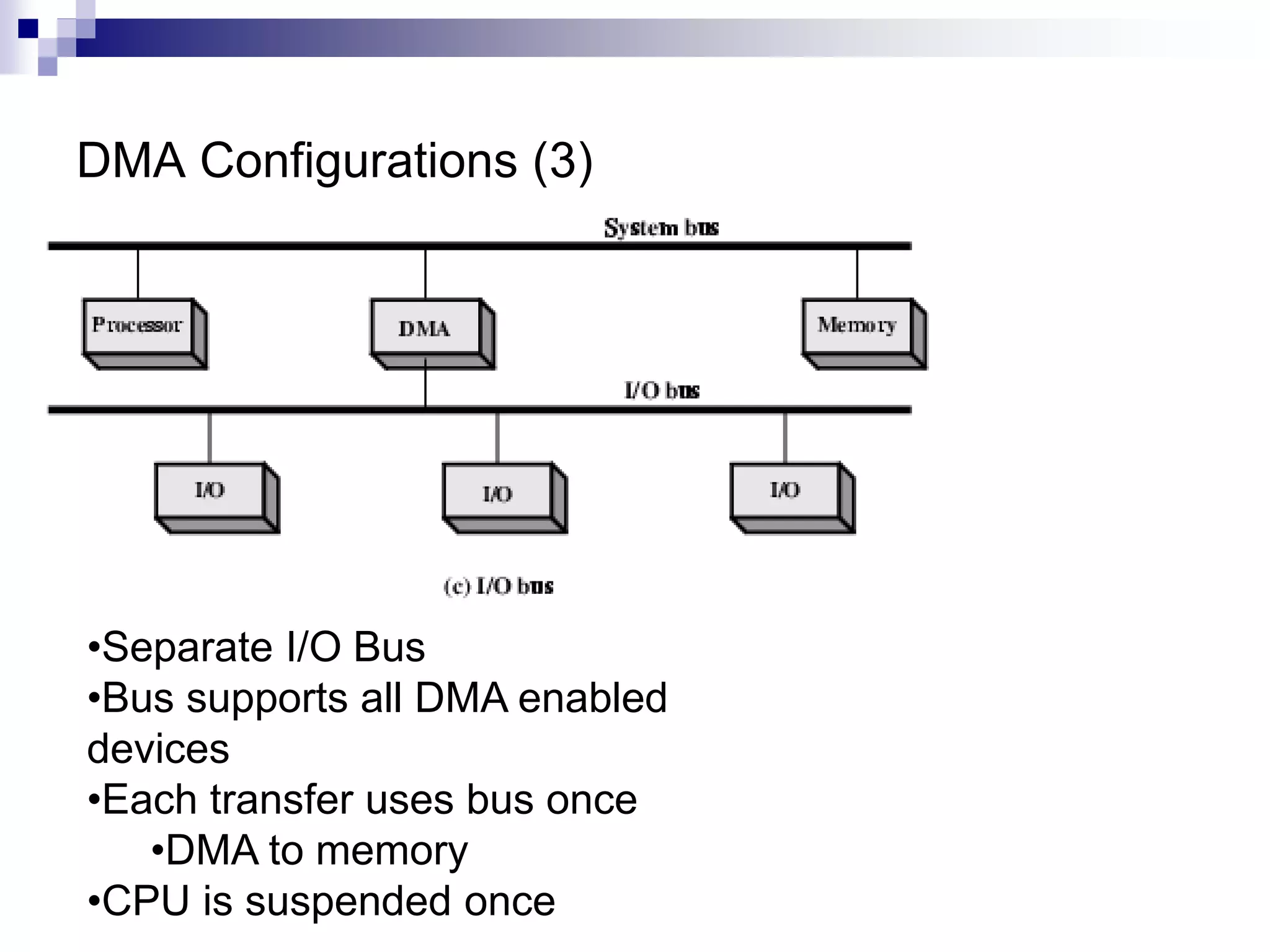
The document outlines the input/output organization of a computer, detailing components such as peripheral devices, interfaces, and methods of data transfer like programmed I/O and direct memory access (DMA). It describes the importance of I/O modules, including control, timing, and error detection functions, along with different I/O commands and configurations. Additionally, it discusses interrupt-driven I/O operations and the complexities involved in DMA to facilitate efficient communication between the CPU and peripherals.