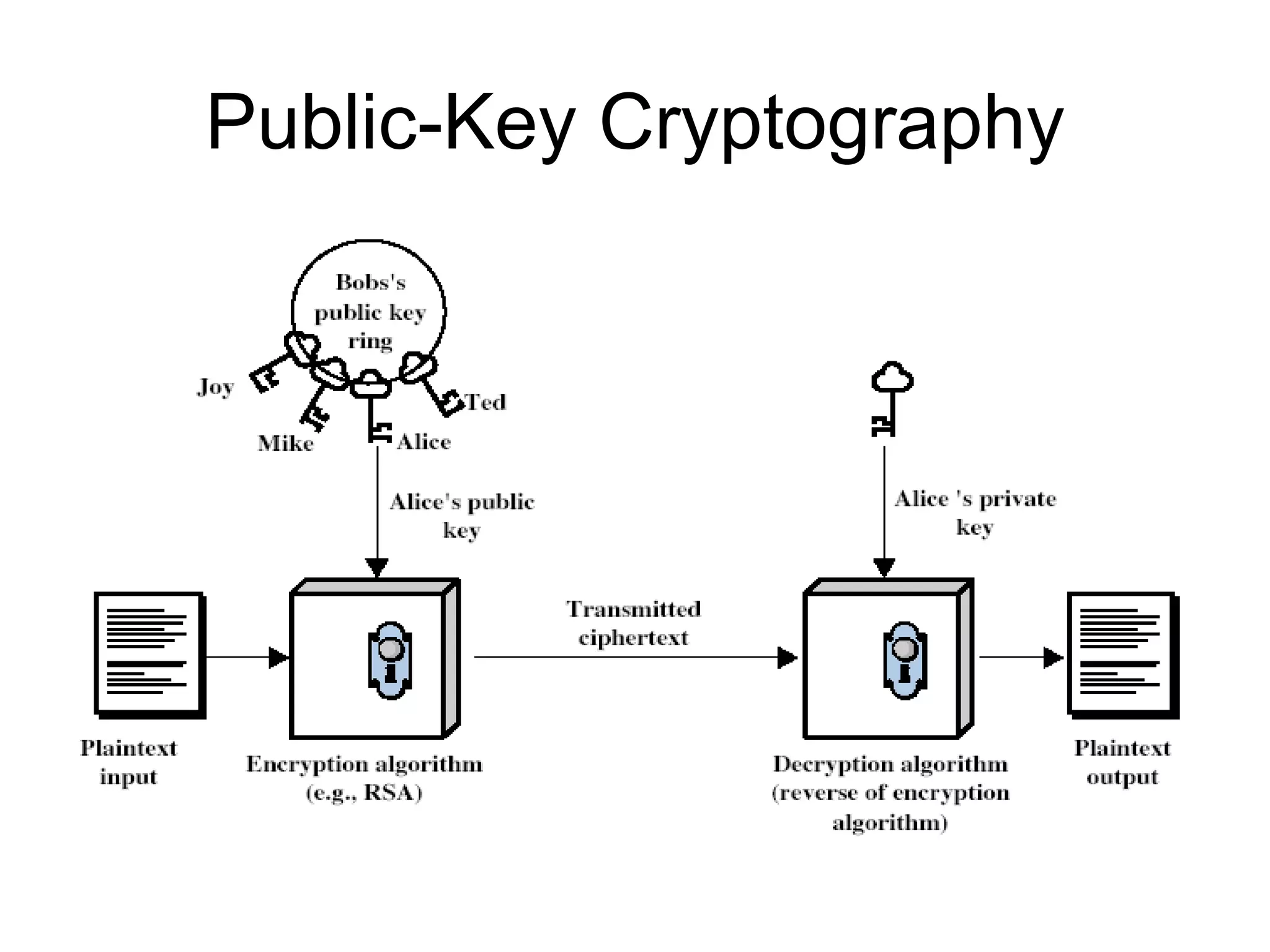
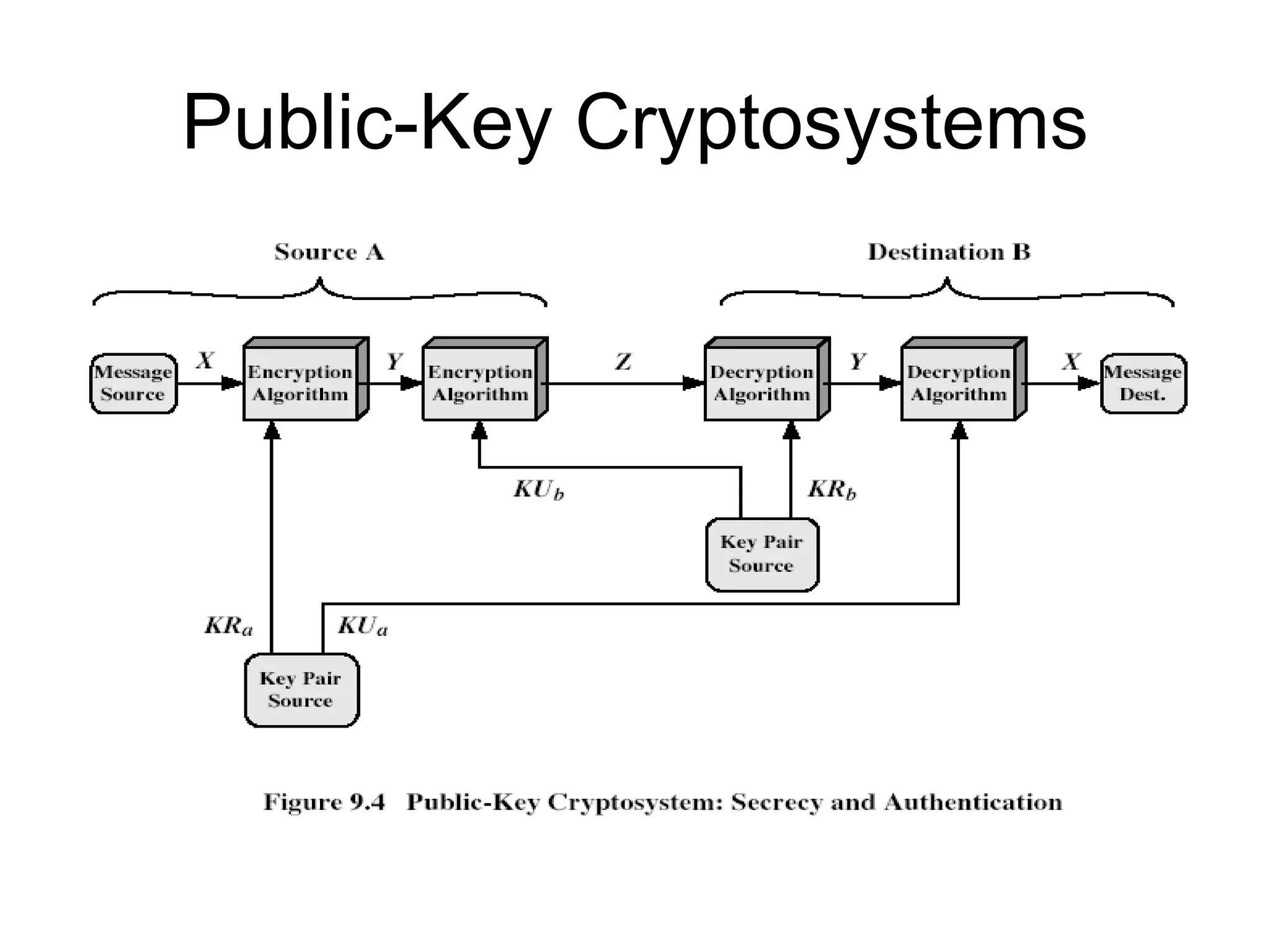
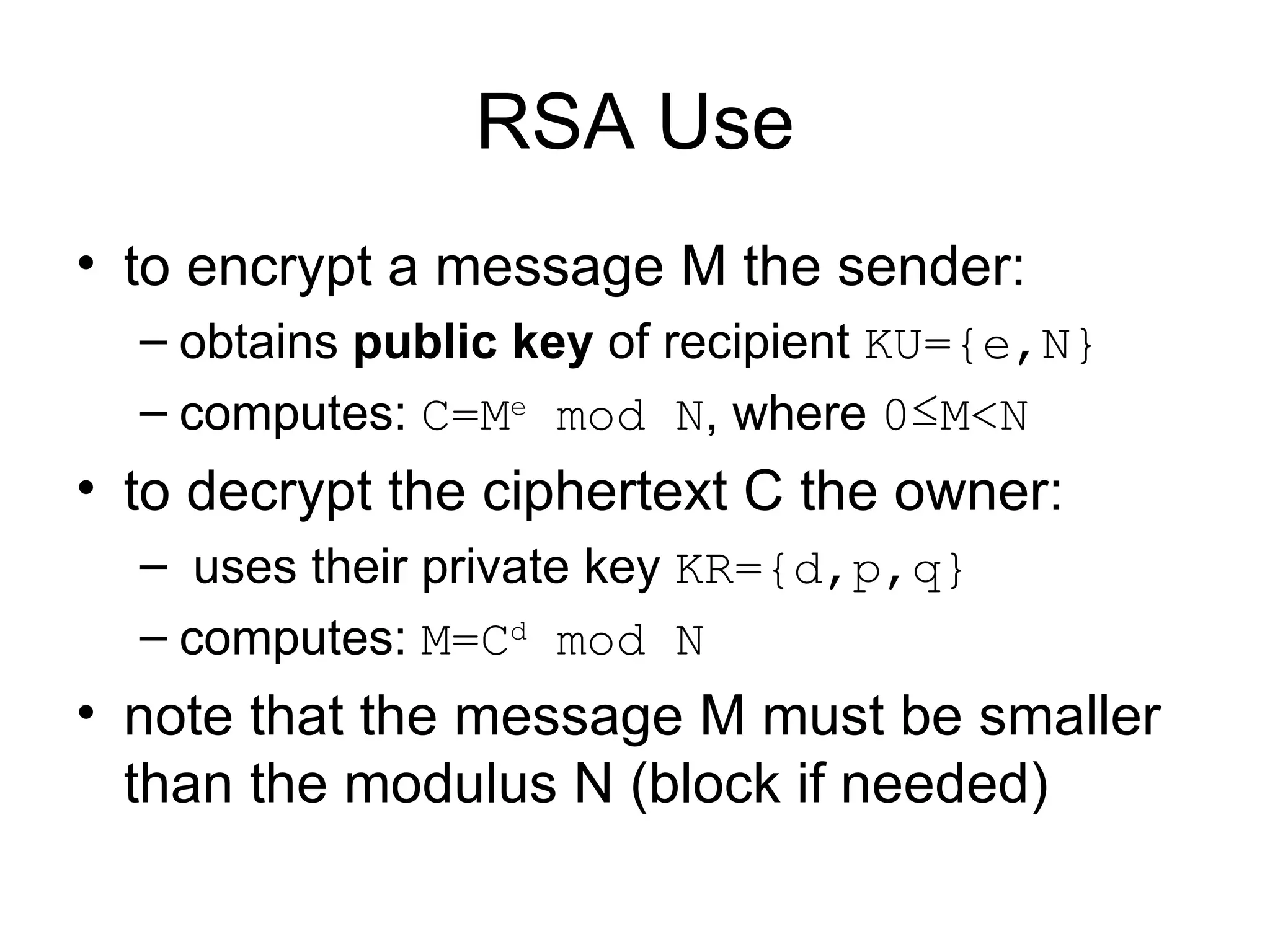
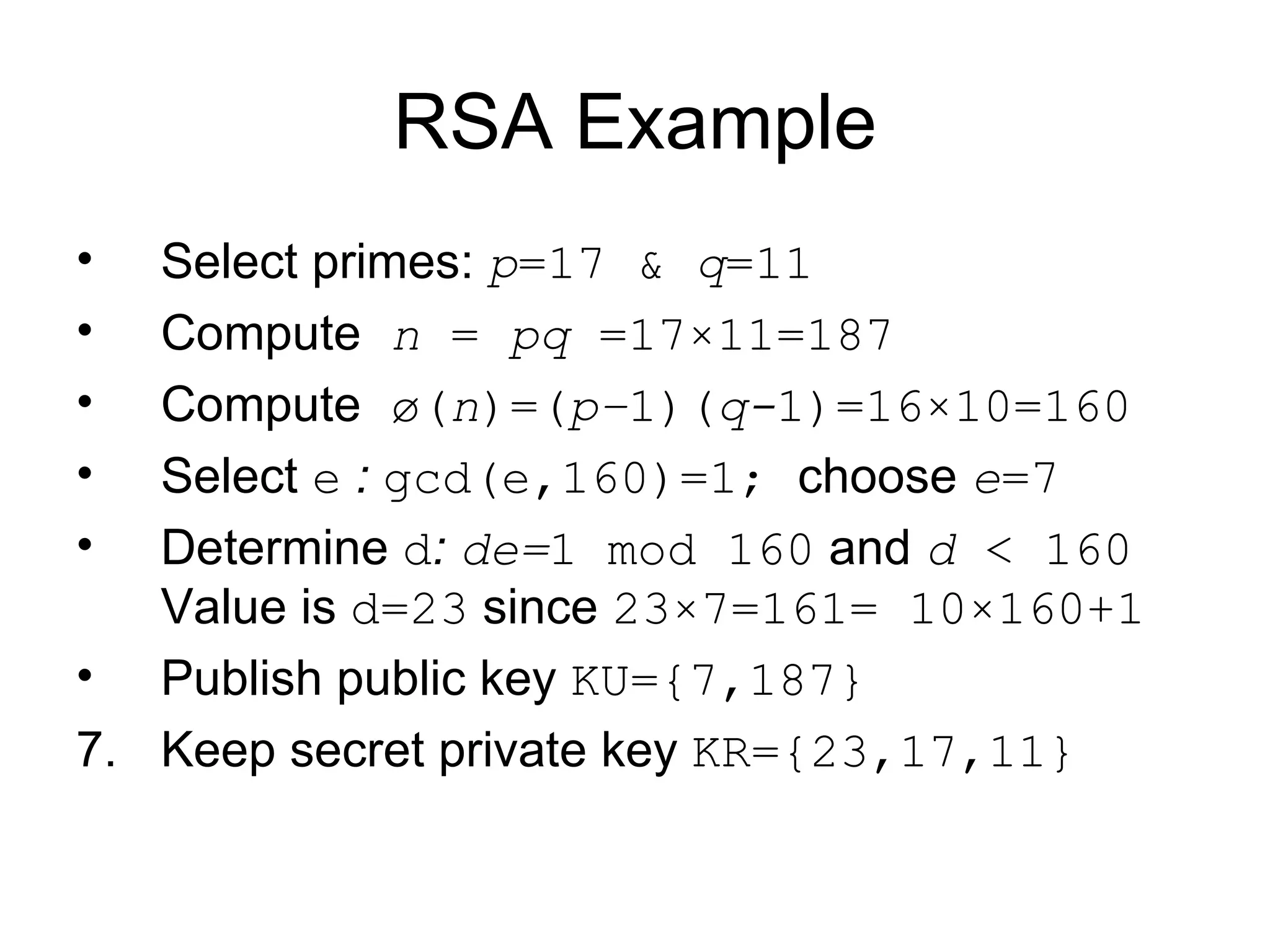
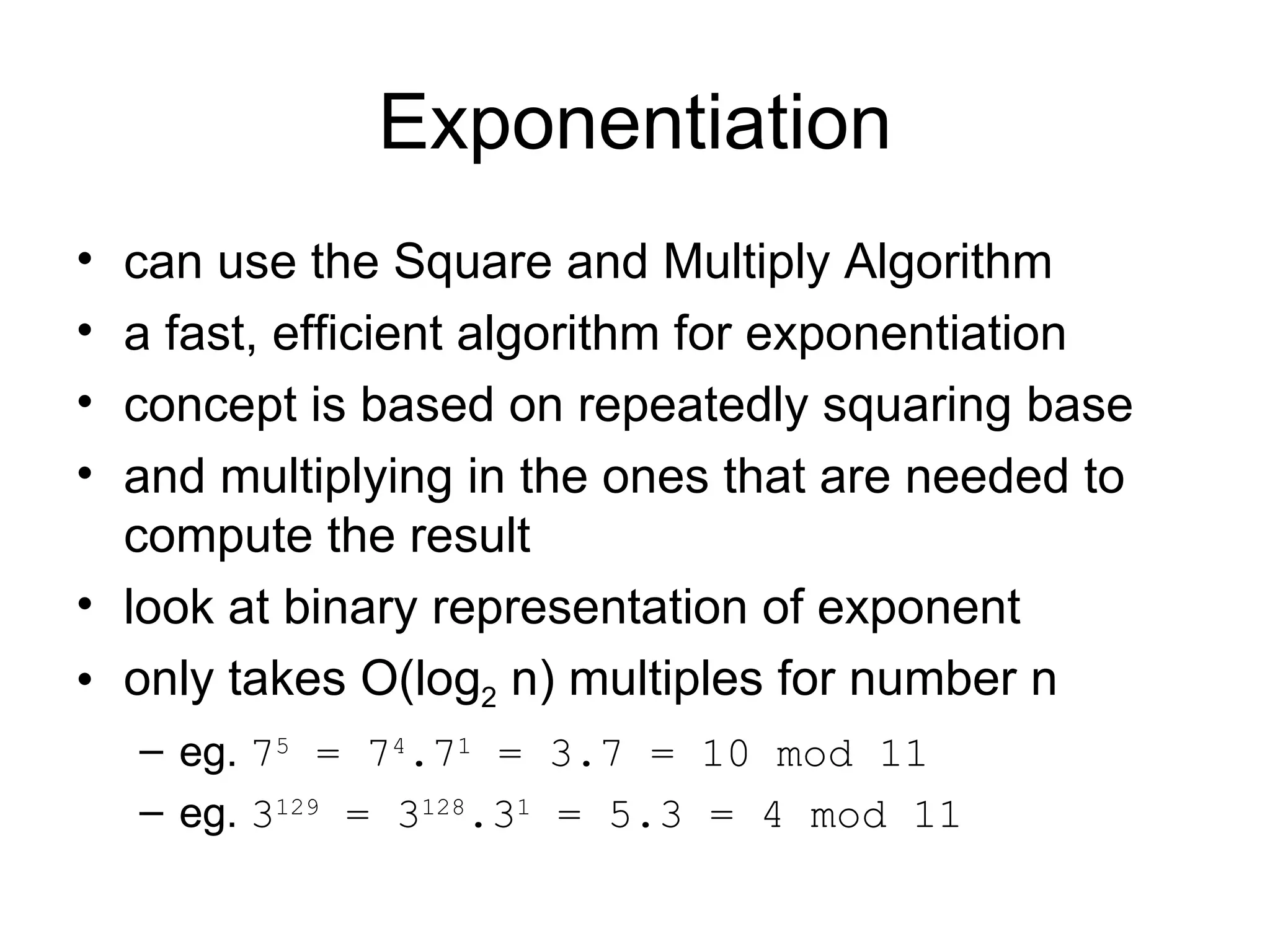
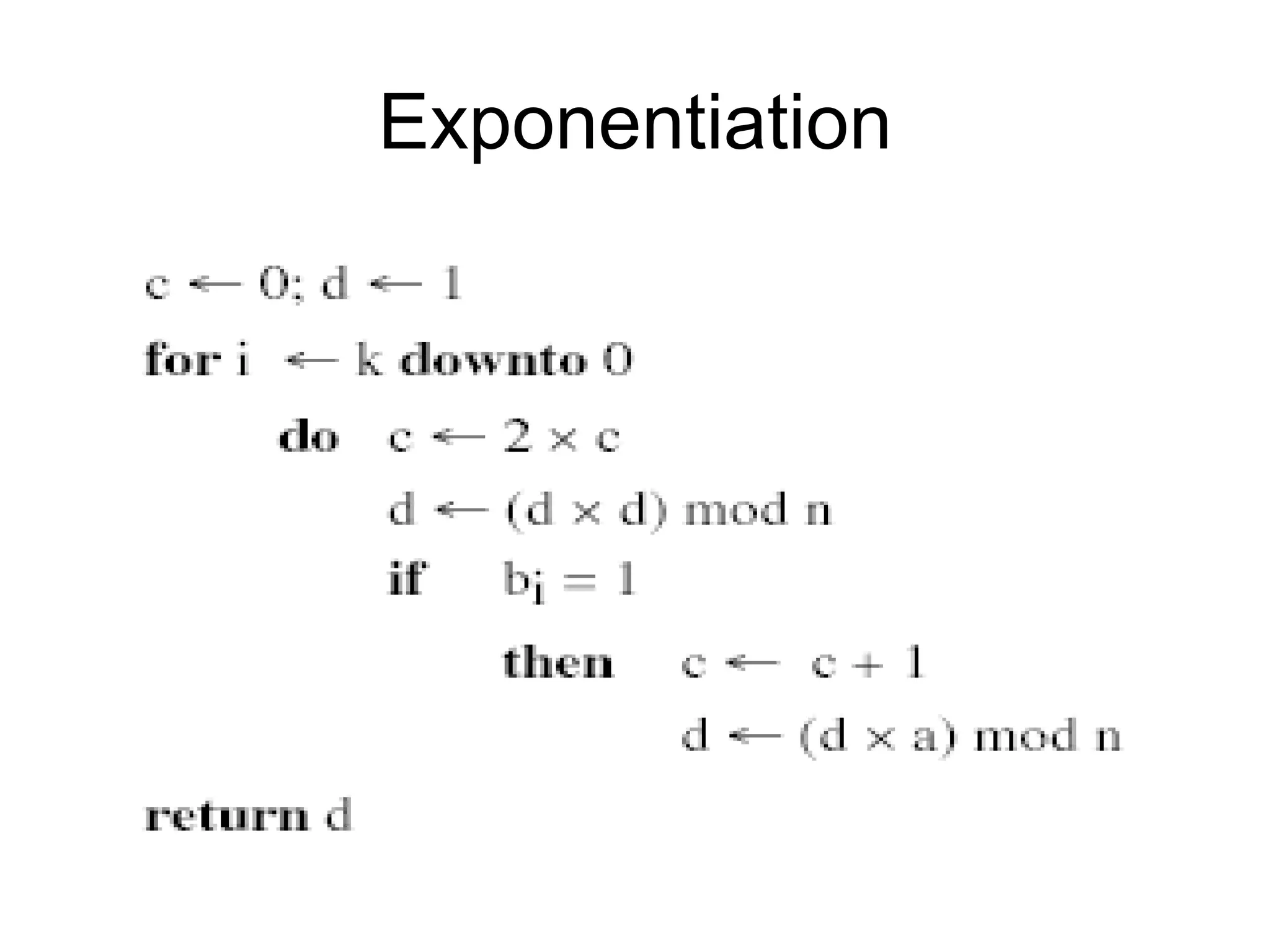
Public-key cryptography uses two keys: a public key that can encrypt messages and verify signatures, and a private key that can decrypt messages and create signatures. The RSA algorithm is widely used for public-key cryptography. It works by using large prime numbers to generate the public and private keys, such that it is easy to encrypt with the public key but computationally infeasible to derive the private key and decrypt without knowing the prime numbers. The security of RSA relies on the difficulty of factoring the product of the large prime numbers. Timing attacks aim to break RSA security by analyzing variations in computation times, but countermeasures can prevent leaks of private information.