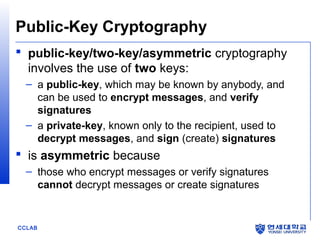
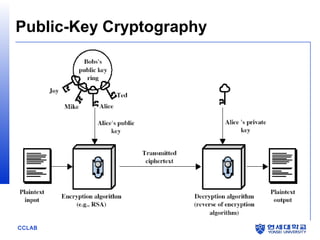
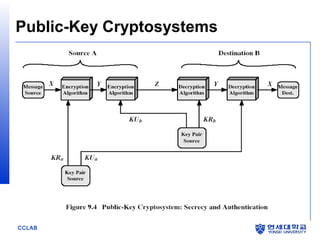
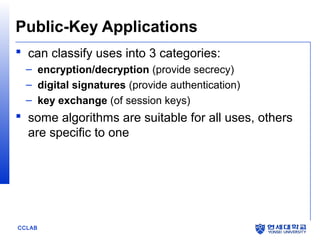
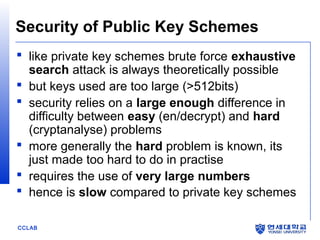
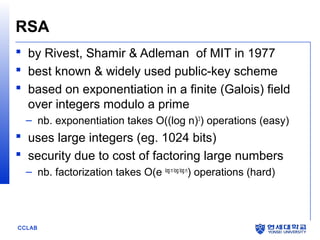
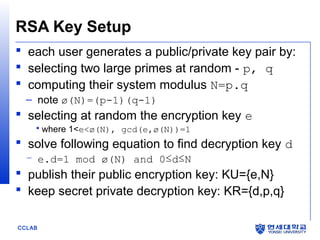
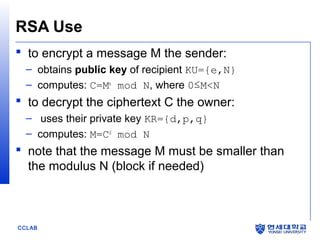
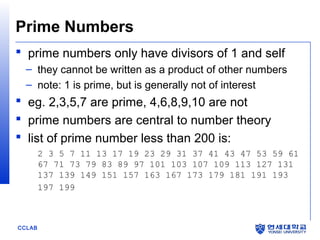
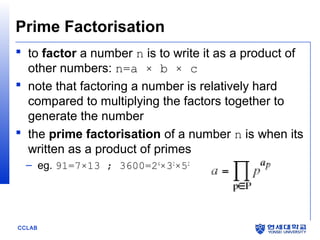
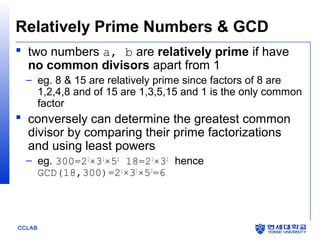
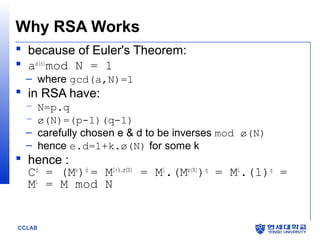
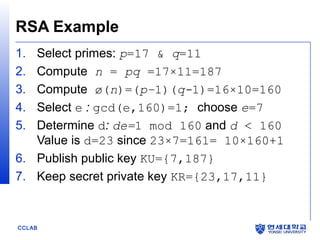
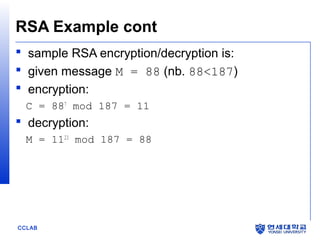
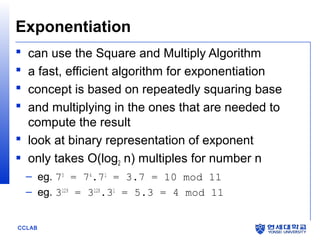
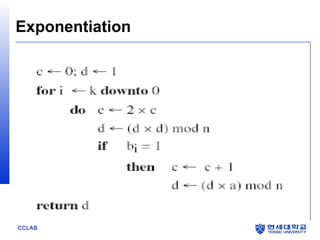
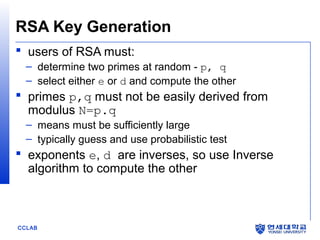
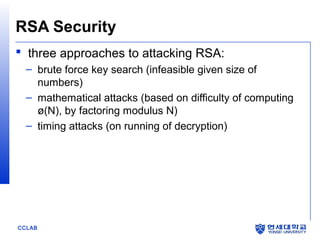
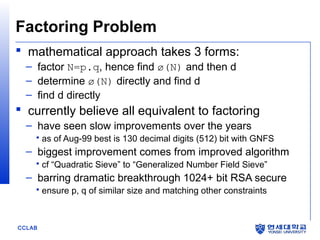
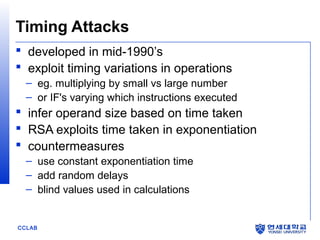
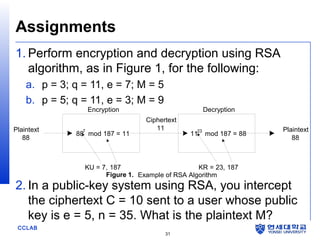
The document discusses the RSA algorithm for public-key cryptography. It explains that RSA uses a public key and private key pair, where the public key is used to encrypt messages and the private key is used to decrypt them. The security of RSA relies on the difficulty of factoring large prime numbers. It describes how the RSA algorithm works by choosing two prime numbers to generate keys, how encryption and decryption are performed using modular exponentiation, and factors that influence the security of RSA implementations.