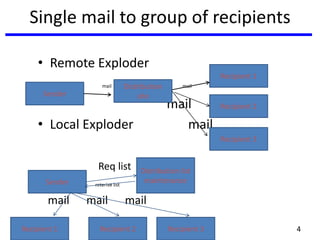
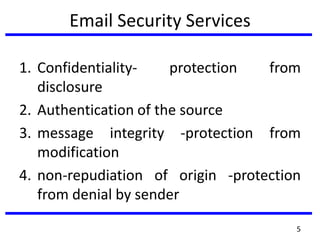
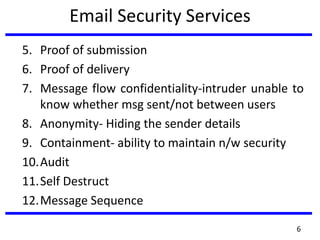
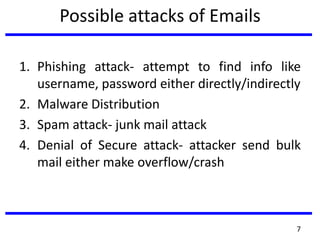
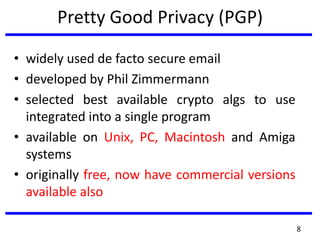
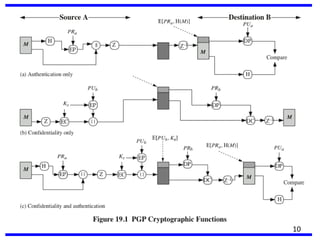
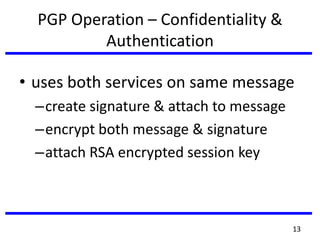
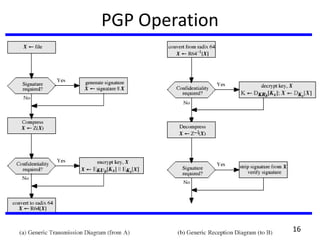
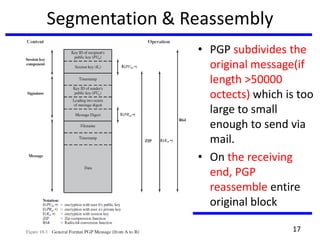
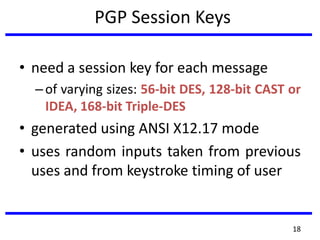
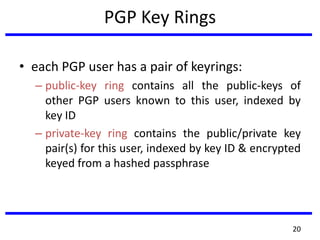
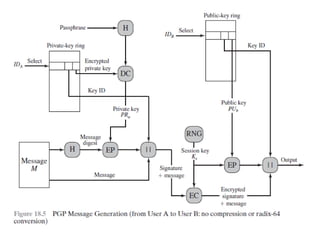
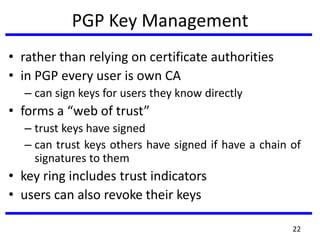
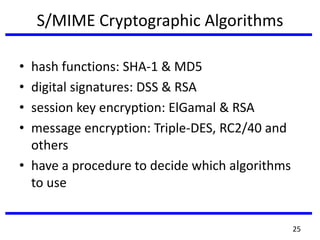
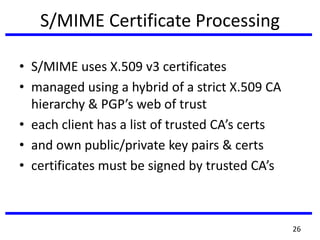
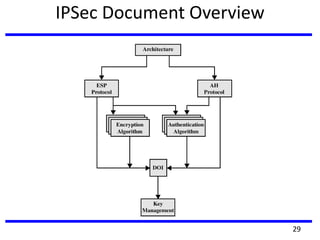
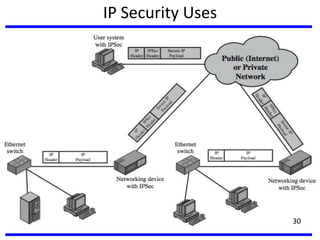
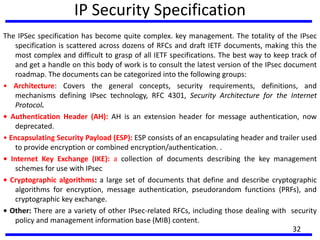
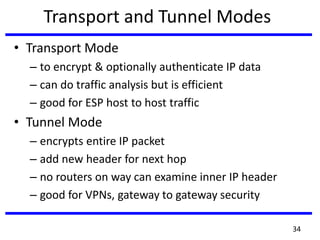
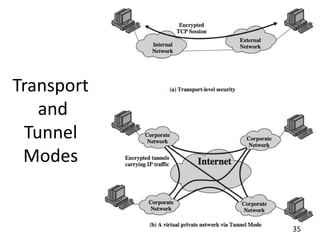
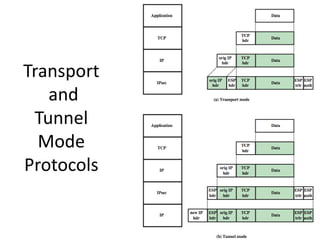
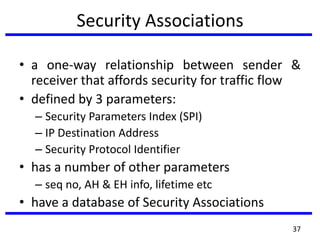
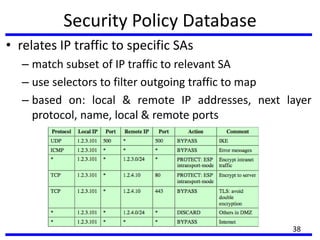
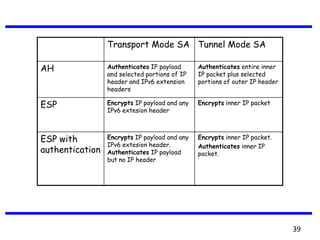
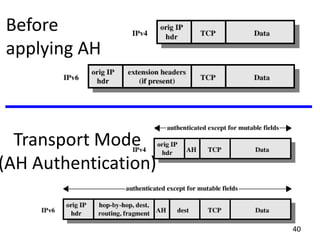
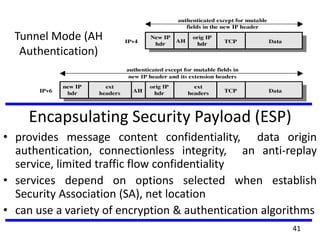
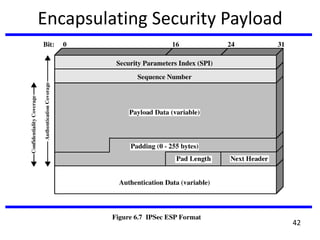
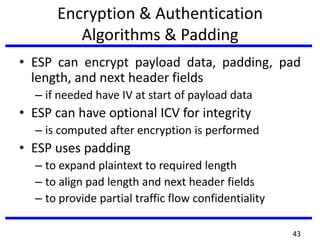
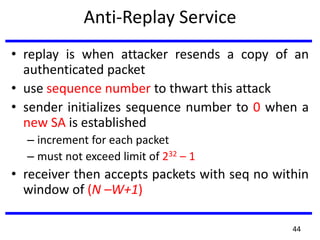
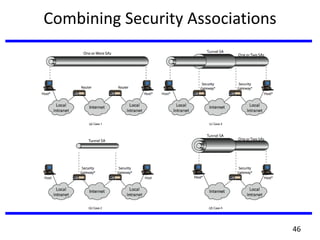
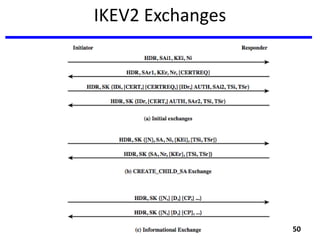
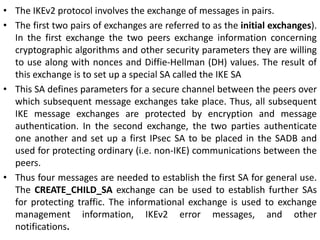
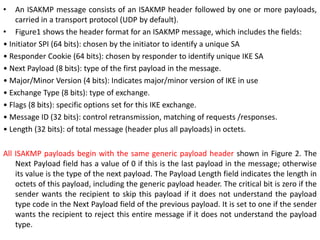
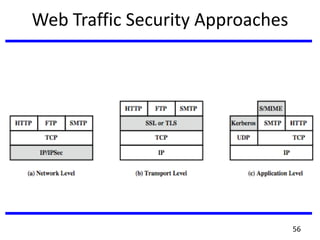
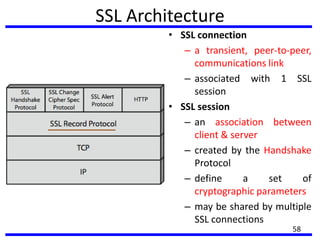
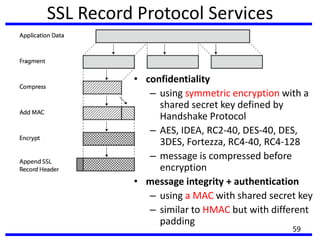
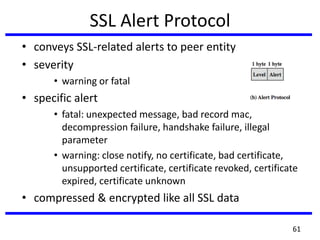
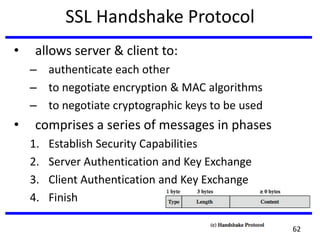
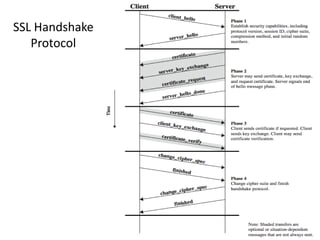
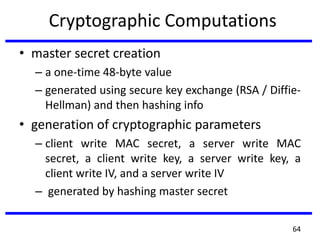
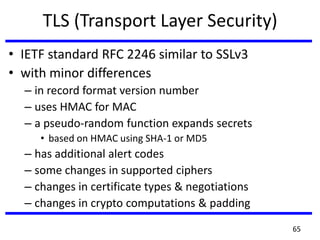
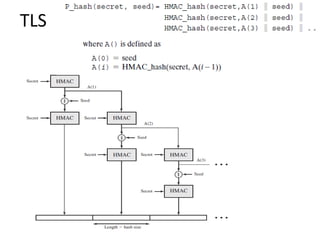
The document outlines the concepts and mechanisms of email, IP, and web security, focusing on email security services like confidentiality, authentication, and non-repudiation, as well as attacks like phishing. It discusses encryption methods and protocols such as PGP and S/MIME for secure communications, and details the complex framework of IP security (IPsec) covering its architecture, operations, and key management. Additionally, the document describes SSL/TLS for web security, emphasizing the importance of these security measures in protecting information across networks.