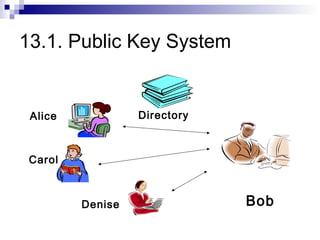
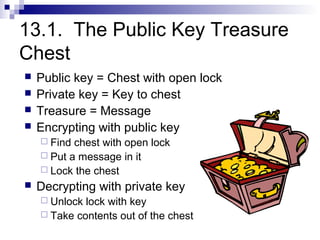
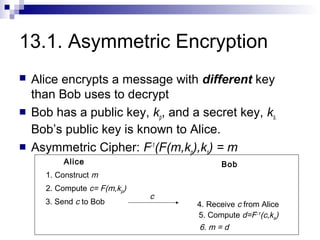
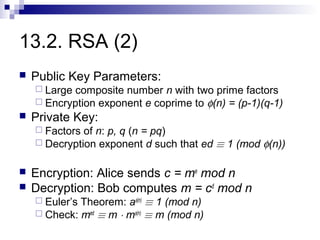
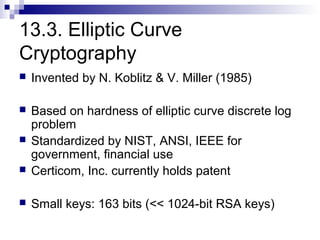
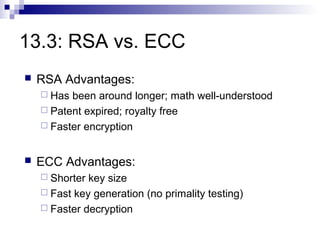
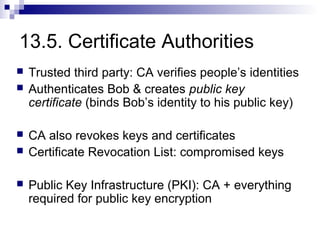
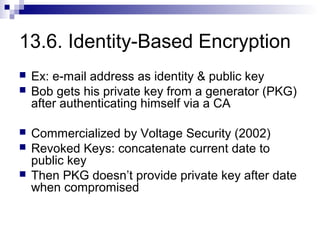
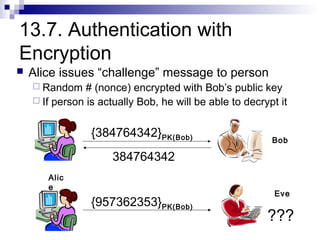
Asymmetric key cryptography uses two keys - a public key that can be shared publicly and a private key that is kept secret. This allows two parties who have never shared secrets before, like Alice and Bob, to communicate securely by encrypting messages with each other's public keys. Common asymmetric algorithms discussed are RSA, which uses prime number factorization, and ECC, which is based on elliptic curve discrete logarithms. A public key infrastructure (PKI) with certificate authorities (CAs) is required to authenticate users and manage public keys.