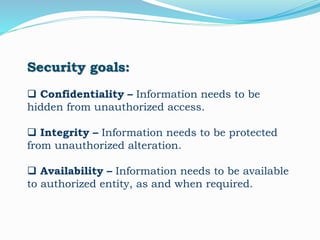
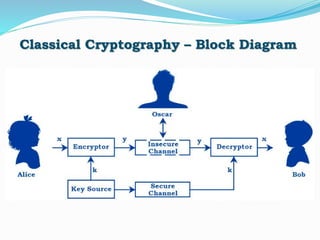
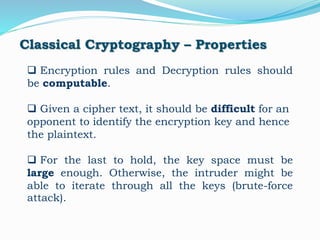
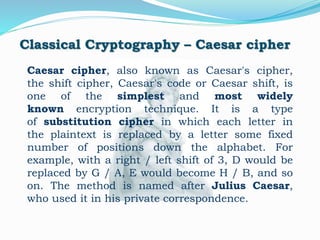
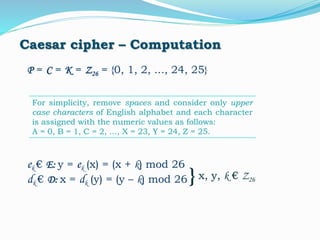
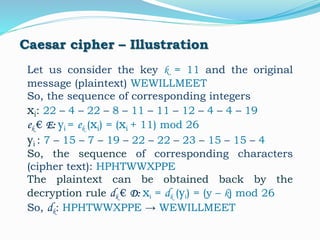
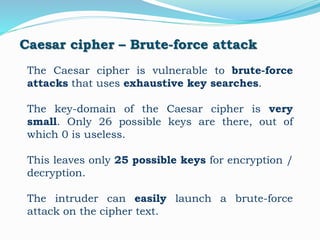
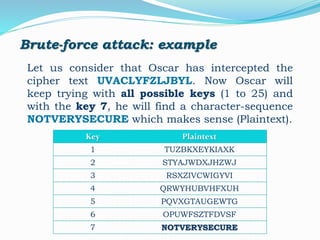
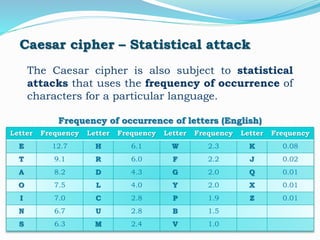
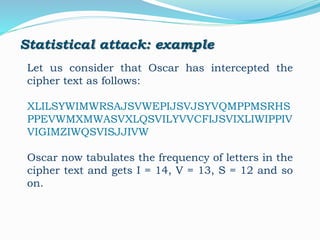
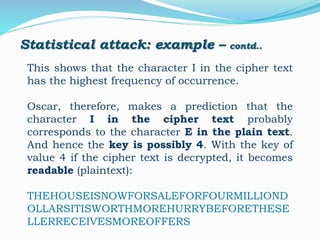
This document discusses cryptography and the Caesar cipher. It begins by defining cryptography as the encoding of messages to achieve secure communication and outlines its goals of confidentiality, integrity, and availability. The document then describes the Caesar cipher technique, in which each letter is shifted a fixed number of positions in the alphabet. It provides an example of encrypting a message with a shift of 11. The document explains that the Caesar cipher is vulnerable to brute force and statistical cryptanalysis due to its small key space and predictable letter frequencies. It concludes that more advanced algorithms are needed for secure encryption in the digital age.