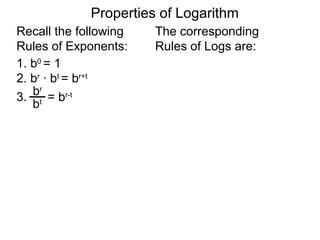
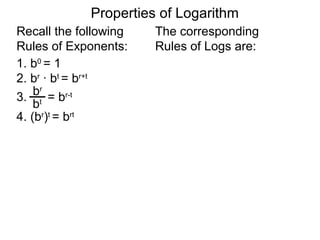
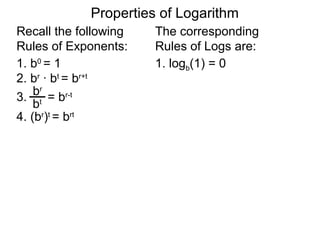
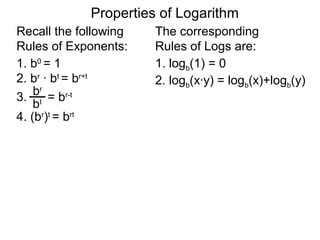
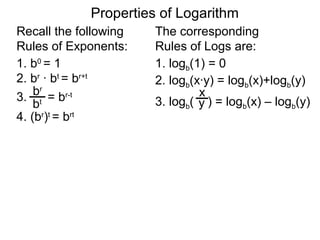
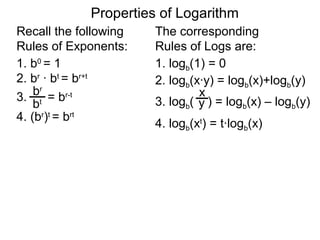
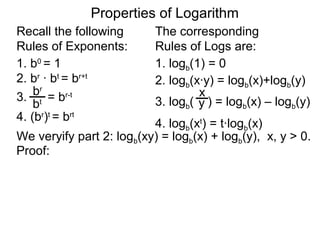
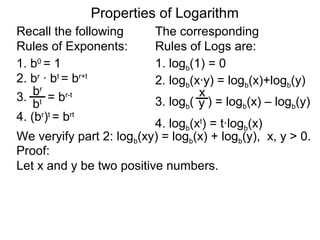
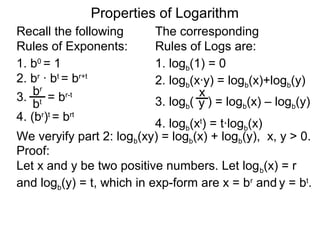
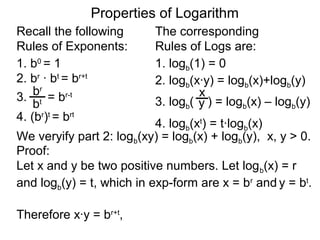
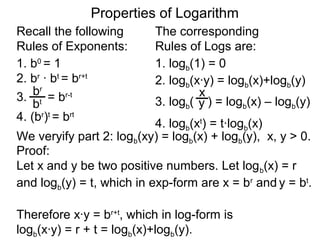
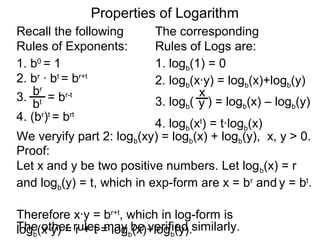
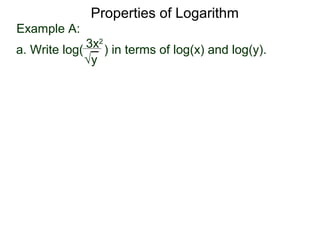
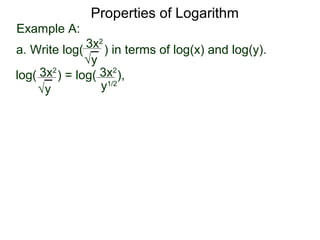
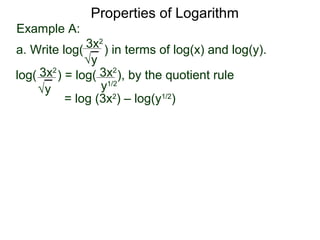
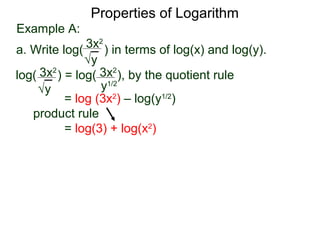
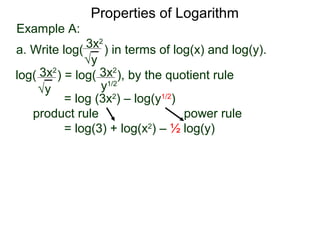
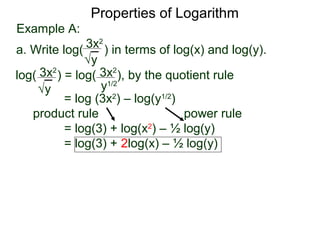
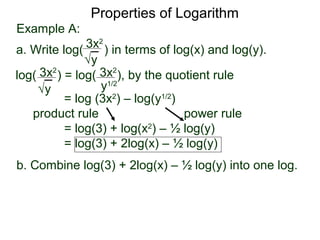
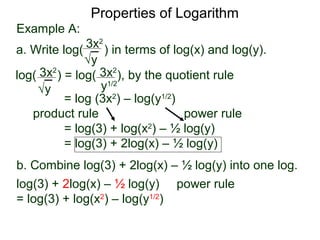
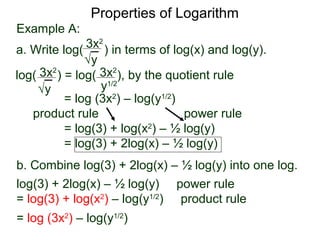
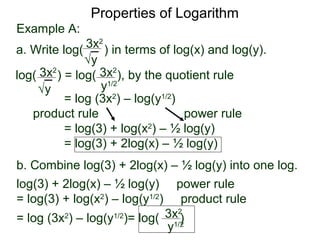
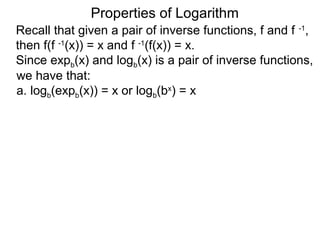
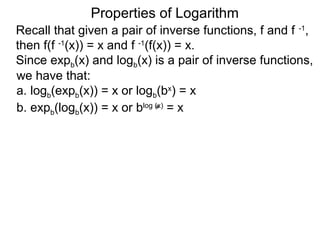
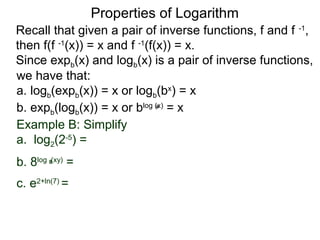
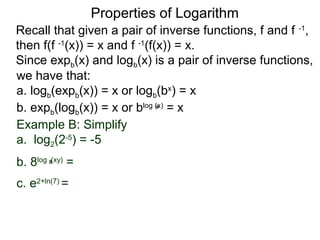
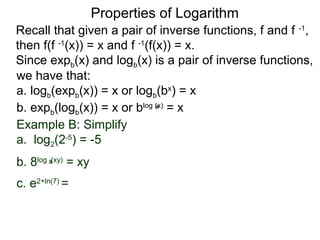
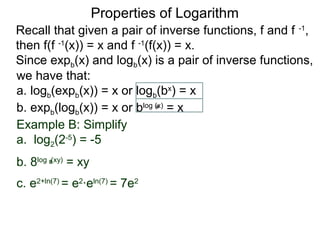
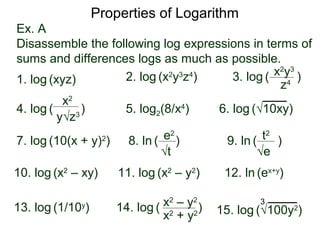
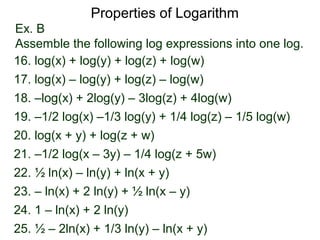
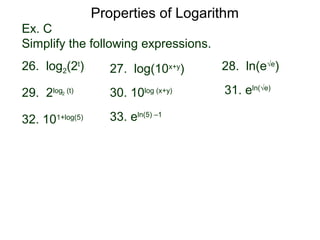
The document discusses properties of logarithms. It begins by recalling rules of exponents and their corresponding rules of logarithms. Four basic logarithm rules are presented: 1) logb(1) = 0, 2) logb(xy) = logb(x) + logb(y), 3) logb(x/y) = logb(x) - logb(y), 4) logb(xt) = tlogb(x). It then works through an example problem to demonstrate using these rules to write the logarithm of a expression in terms of logarithms of its variables. It concludes by noting that logarithms and exponentials are inverse functions, so logb(bx) =