1. The document presents an overview of Markov chains and processes, with a focus on their applications in marketing.
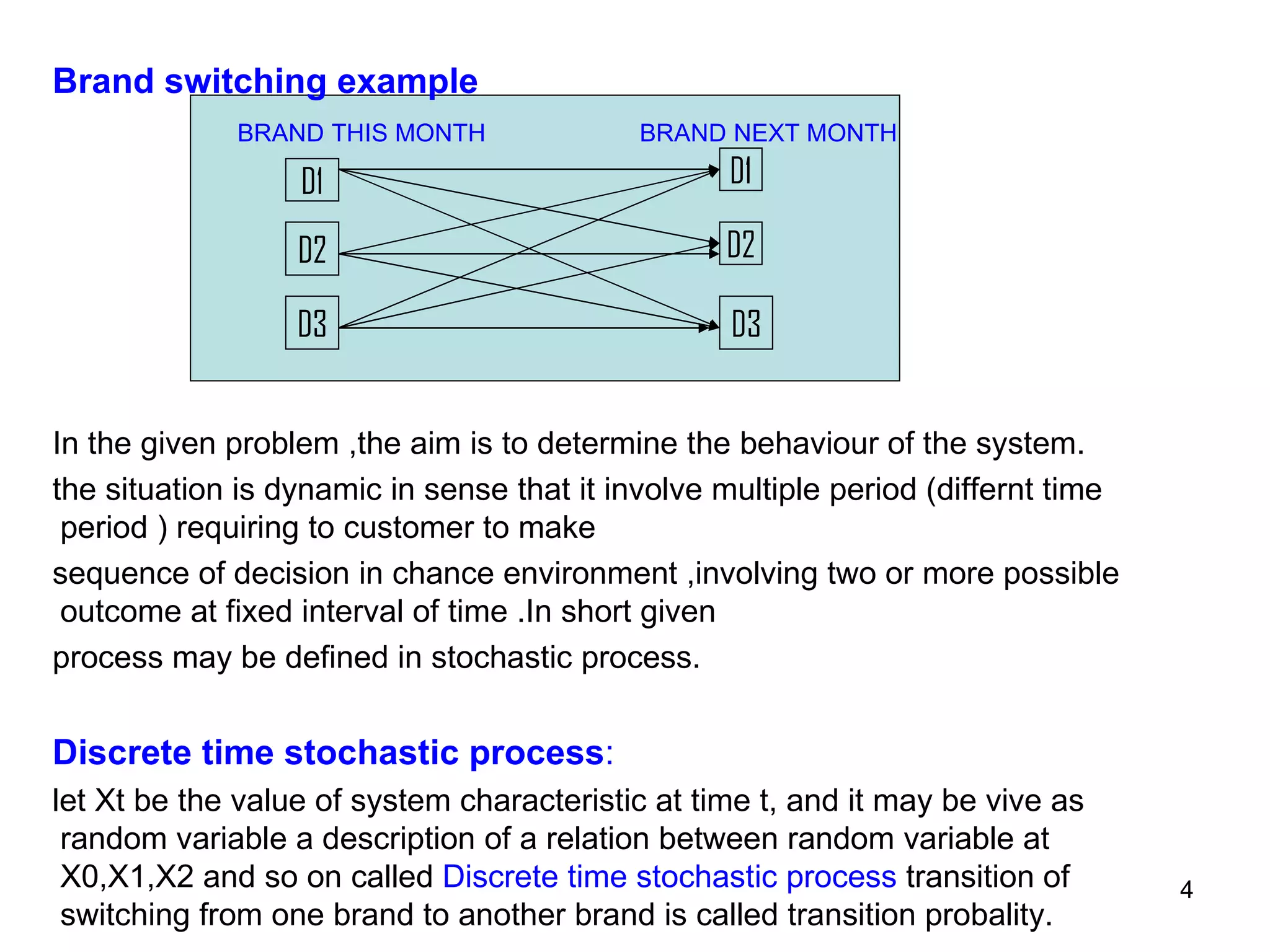
2. It provides an example of brand switching over time as a Markov process and outlines some key aspects of Markov processes including finite states, stationarity, and uniform time periods.
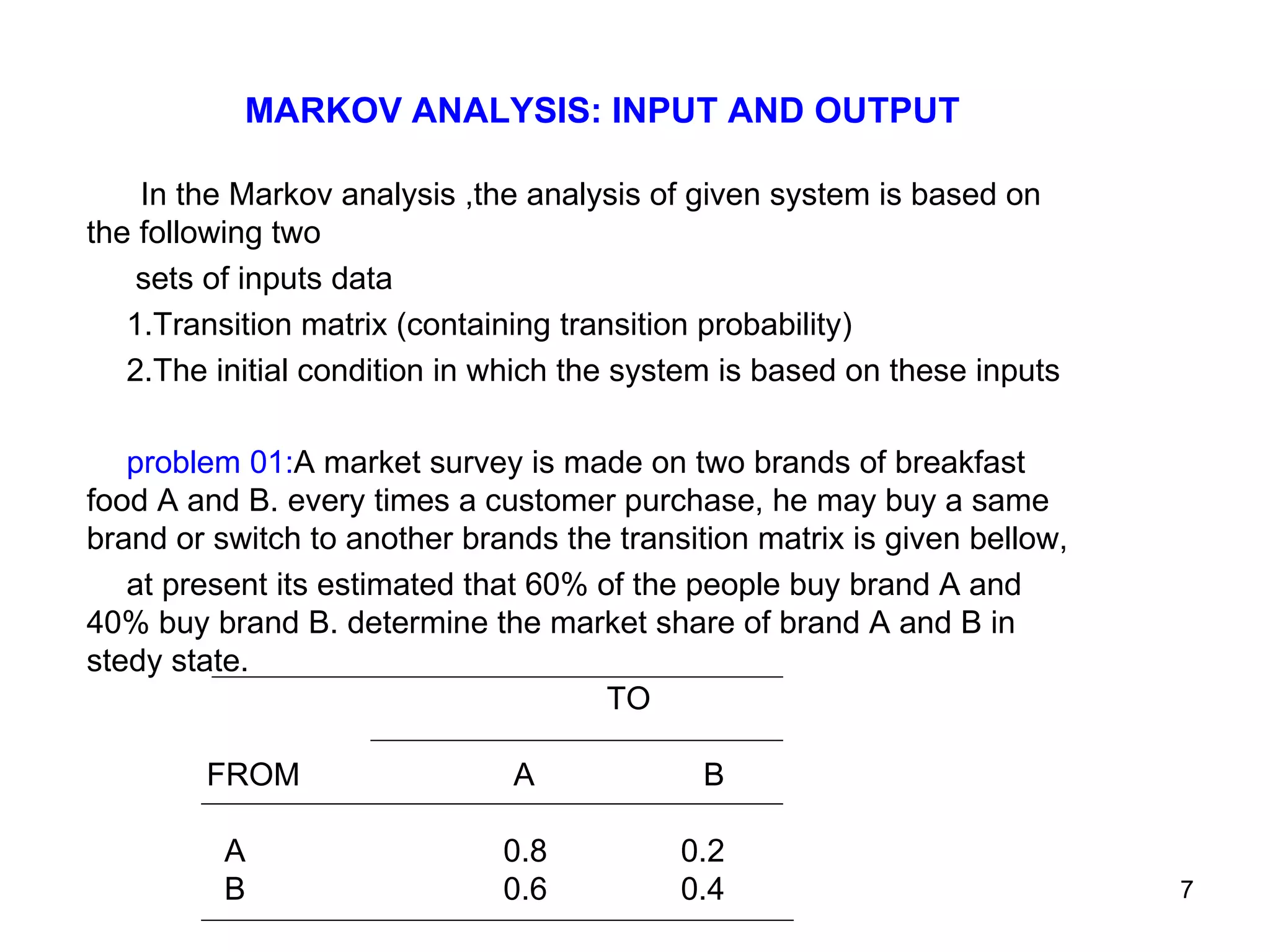
3. The document also gives an example problem using a transition matrix to determine the market share of two breakfast brands in a steady state based on customer purchase patterns.

![References [1] Business Statistics, G. C. Beri (TMH) [2] Quantitative Techniques in Management, N. D. Vohra (TMH) [3] Quantitative Methods For Business, Anderson ( Thomson Learning Books) [4] Statistical methods, S.P. Gupta ( S Chand) [5] Levin Richard & Rubin David - Statistics for Management (Prentice Hall of India)](https://image.slidesharecdn.com/markovchain-091116043814-phpapp02/75/M-A-R-K-O-V-C-H-A-I-N-10-2048.jpg)
