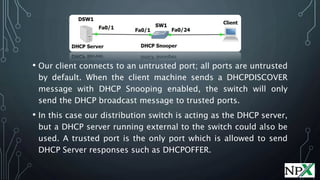
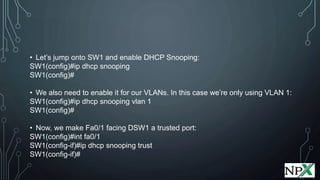
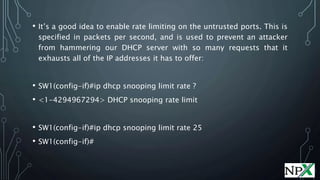
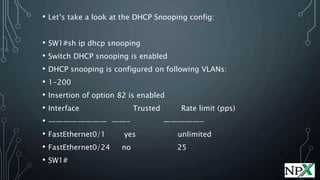
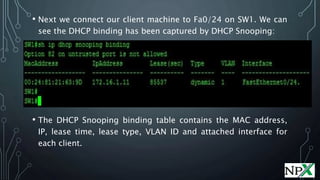
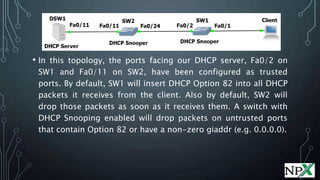
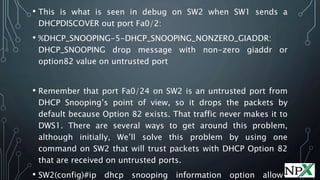
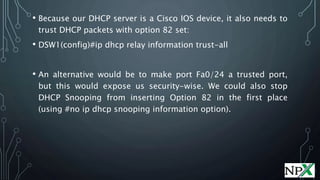
DHCP Snooping allows switches to prevent man-in-the-middle attacks by DHCP spoofing. It trusts only the port connected to the DHCP server, monitors traffic for IP and MAC bindings, and uses this information for other security features. When enabled, DHCP Snooping will only forward DHCP requests to trusted ports and maintain a table of client bindings.