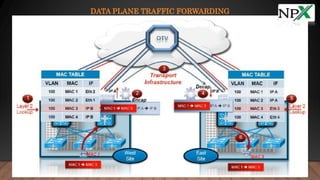
OTV is a technology that provides layer 2 extension capabilities between different data centers without using tunnels. It encapsulates layer 2 traffic with an IP header and transports it across an IP network. OTV devices called edge devices perform layer 2 learning and forwarding within a data center and encapsulation functions to extend layer 2 traffic across sites using IP addresses and multicast groups for control and data plane MAC address advertisement and traffic forwarding between sites.