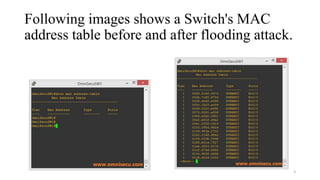
The document discusses the MAC address flooding attack, a method where an attacker floods a switch's MAC address table with fake addresses, causing it to fail-open and behave like a hub, allowing the attacker to capture sensitive data. It highlights prevention techniques using Cisco's port security feature, detailing its configuration and actions on violations, as well as other attacks such as DHCP starvation and ARP spoofing, alongside preventive measures like DHCP snooping and dynamic ARP inspection. The text serves as an instructional guide on network security practices to mitigate such vulnerabilities.