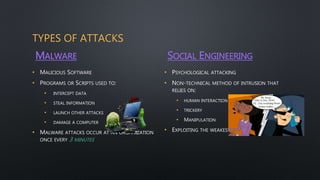
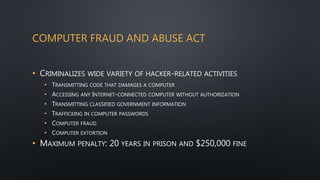
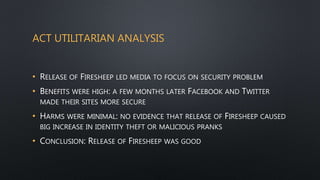
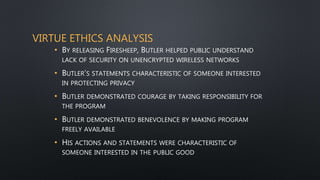
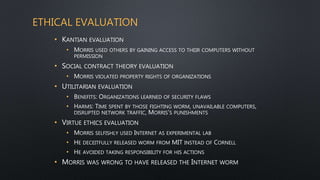
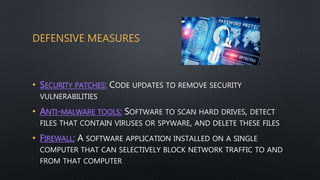
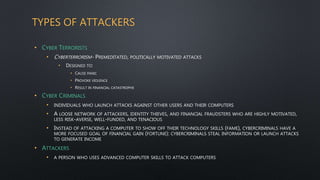
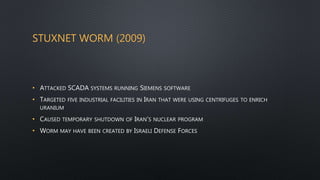
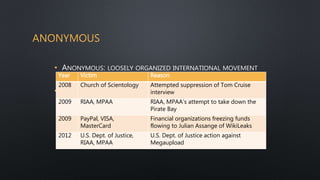
This document discusses computer and network security. It begins by noting that computers are becoming faster, less expensive, and more networked, increasing their importance and the need for security. It then discusses different types of attackers like hackers, malware, and social engineering. It provides examples of attacks like Stuxnet and cyber espionage attributed to China. It also discusses groups like Anonymous and defensive measures like antivirus software.