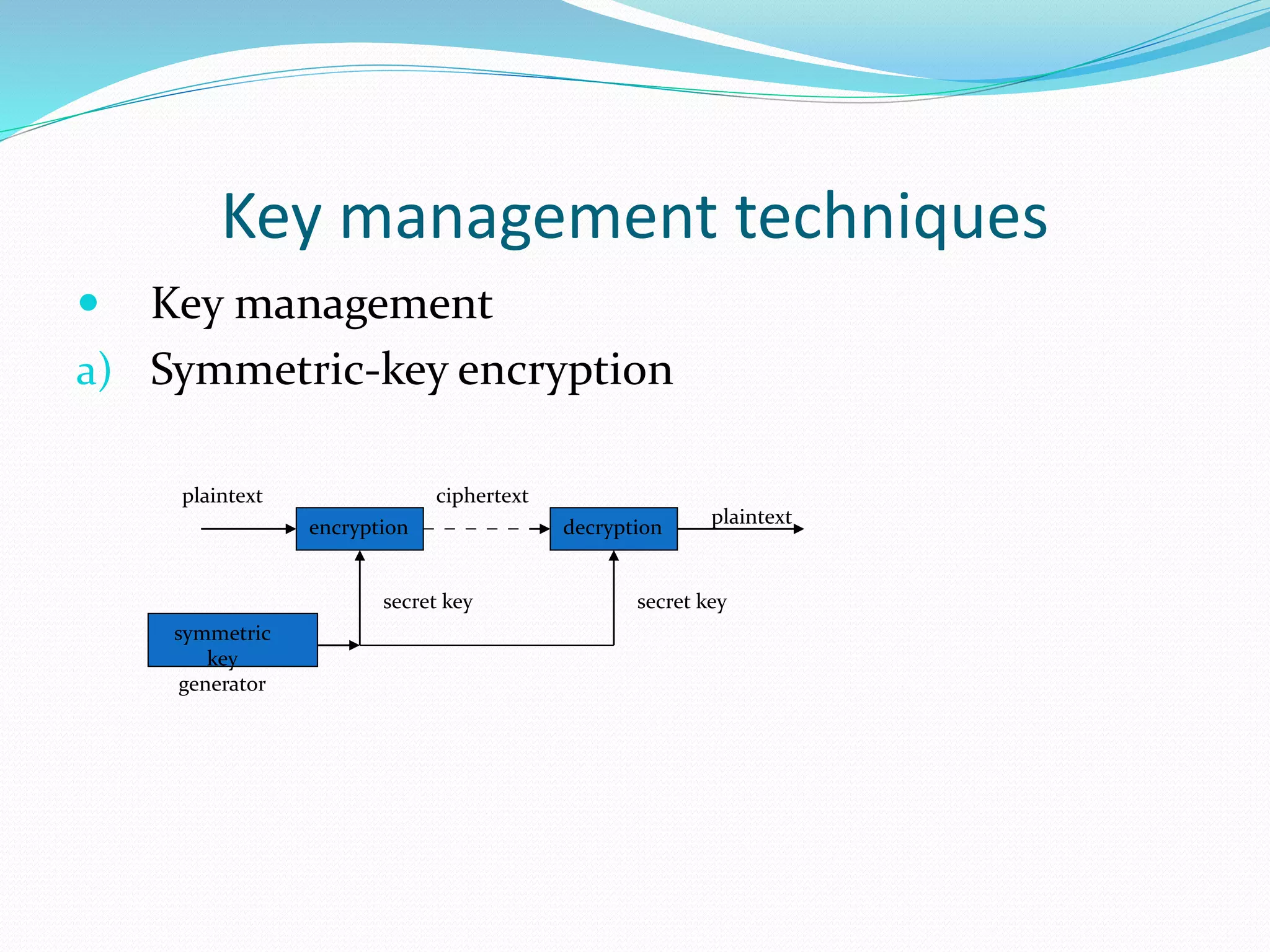
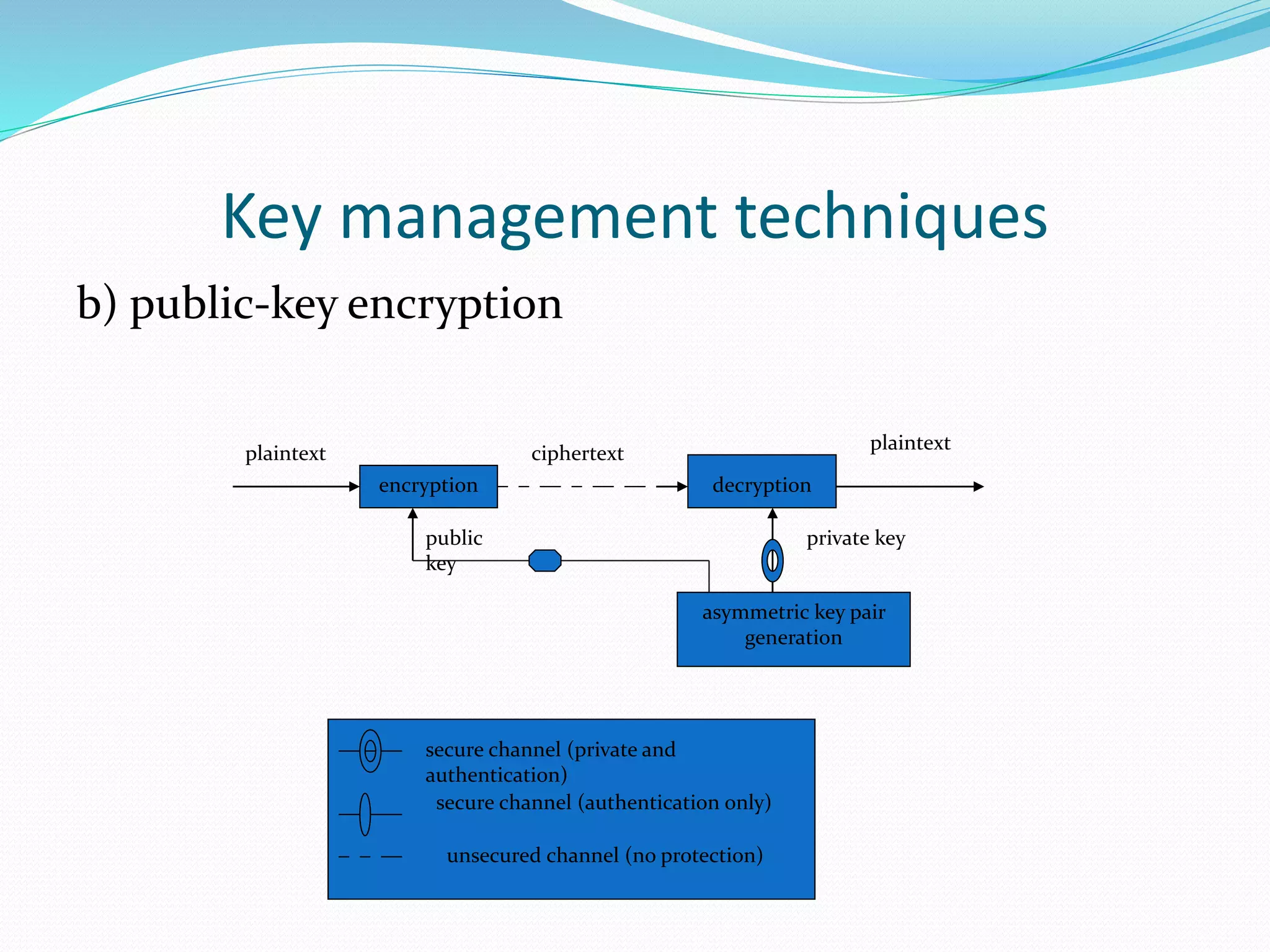
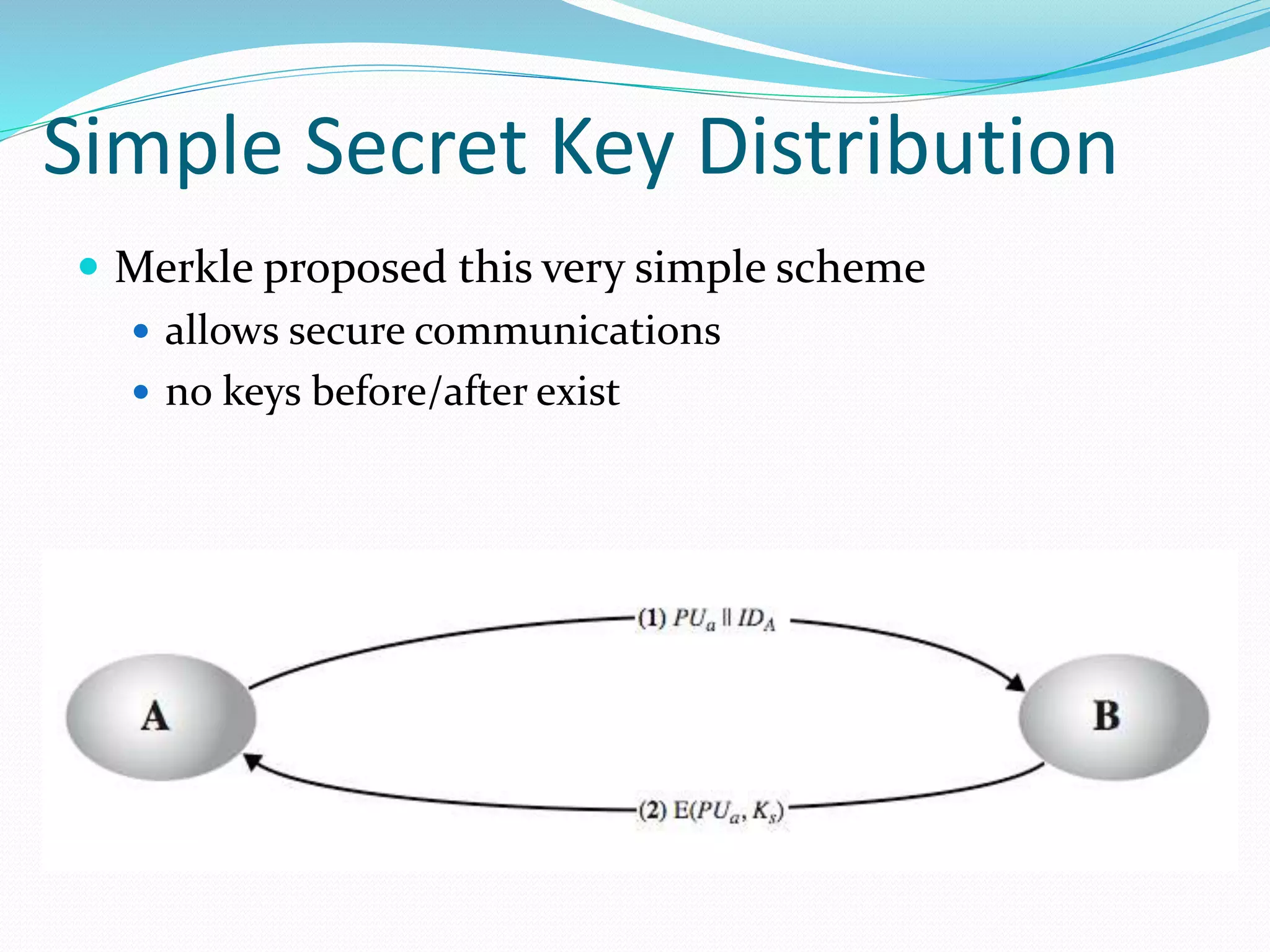
Key management is the set of techniques and procedures for establishing and maintaining secure key relationships between parties. It involves generating, distributing, storing, updating, and revoking cryptographic keys. The objectives of key management are to maintain secure keying material and relationships to counter relevant threats like key compromise, in accordance with a security policy. Techniques include symmetric and public-key encryption, key hierarchies, certificates, and life cycle processes around user registration and key installation, update, and destruction.