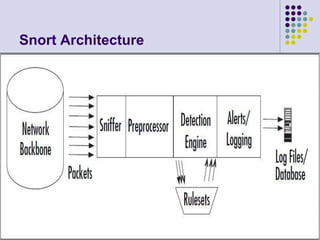
Snort is an open source network intrusion detection system (IDS) that can perform real-time traffic analysis and packet logging on IP networks. It works by using rules to compare network traffic patterns to known attacks and flag any matches. Snort has four main components - the packet sniffer, preprocessors, detection engine, and output. The sniffer reads packets, preprocessors check for certain behaviors, the detection engine matches rules, and output generates alerts that can be logged or sent to external systems. Snort rules can detect a variety of attacks and are useful for monitoring networks when vulnerabilities are known but patches are not yet available.