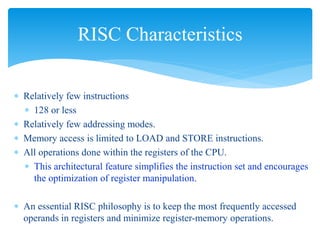
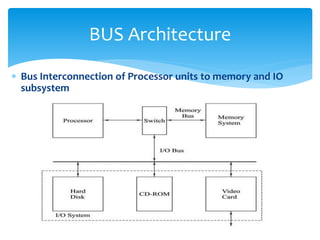
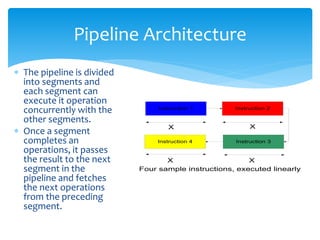
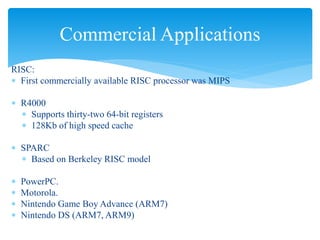
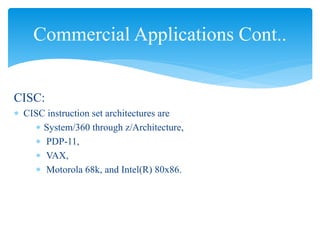
This document discusses the history and characteristics of CISC and RISC architectures. It describes how CISC architectures were developed in the 1950s-1970s to address hardware limitations at the time by allowing instructions to perform multiple operations. RISC architectures emerged in the late 1970s-1980s as hardware improved, focusing on simpler instructions that could be executed faster through pipelining. Common RISC and CISC processors used commercially are also outlined.