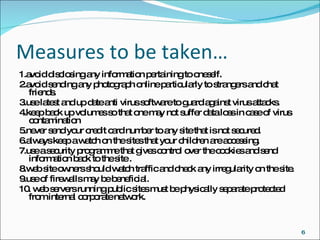
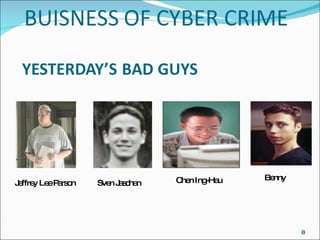
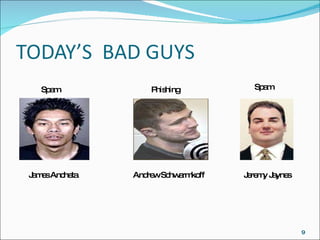
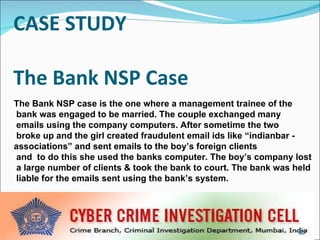
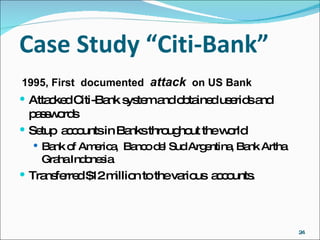
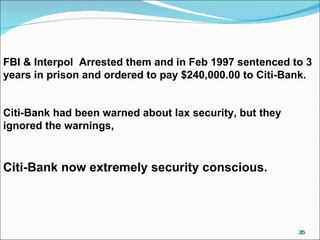
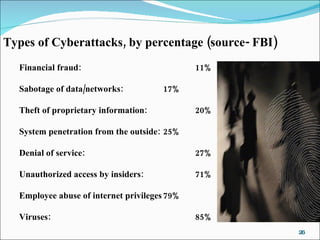
This document discusses high tech crimes and cybersecurity. It provides examples of different types of high tech crimes like data theft, hacking, identity theft, and cyberterrorism. It also discusses measures that can be taken to enhance cybersecurity, like using antivirus software, firewalls, strong passwords, and backing up data. Forensics procedures for investigating cybercrimes are also summarized.