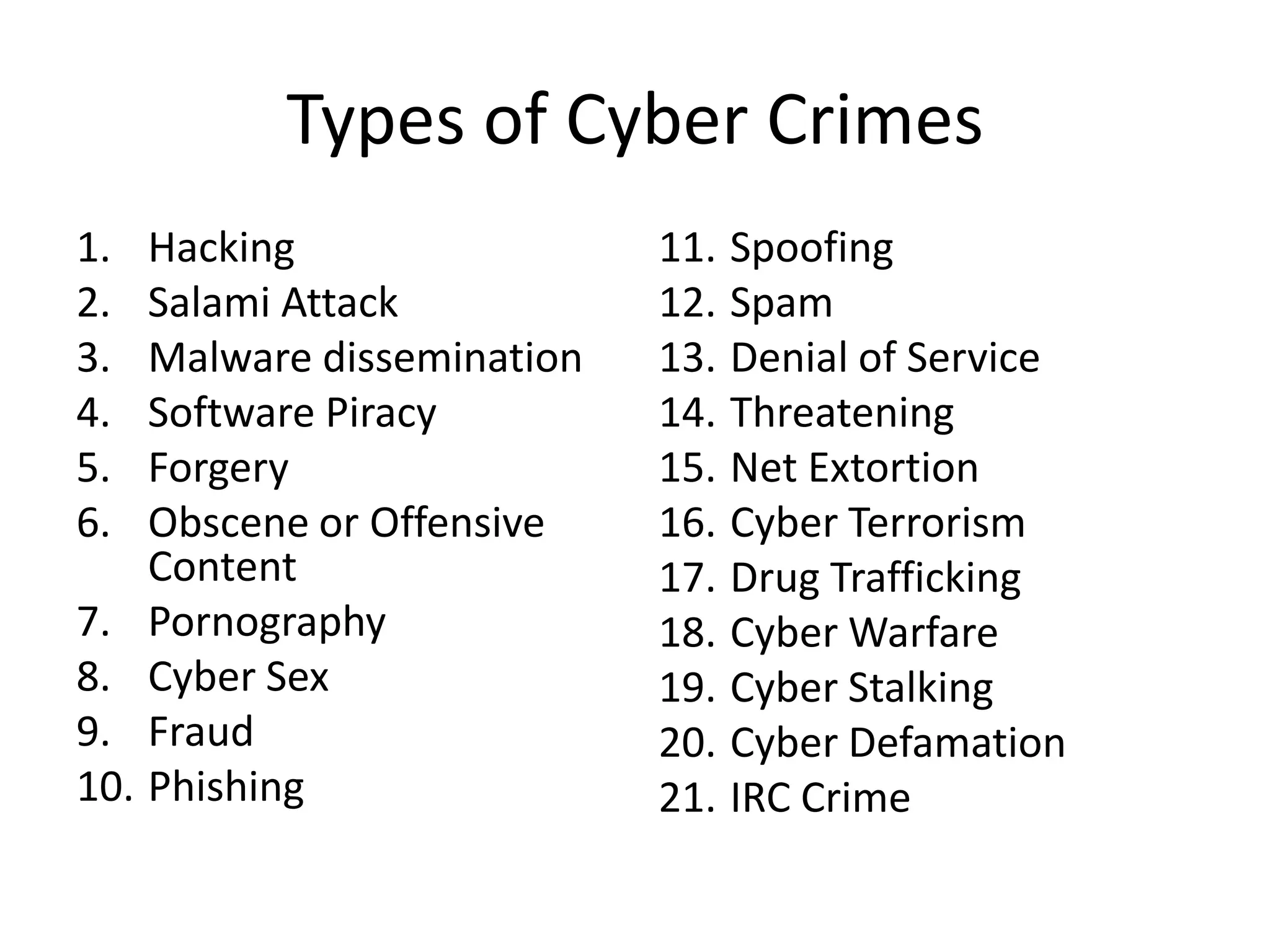
1. Cyber crimes involve any illegal activities that use computers and networks. Common cyber crimes include hacking, malware distribution, software piracy, cybersex, fraud, and identity theft.
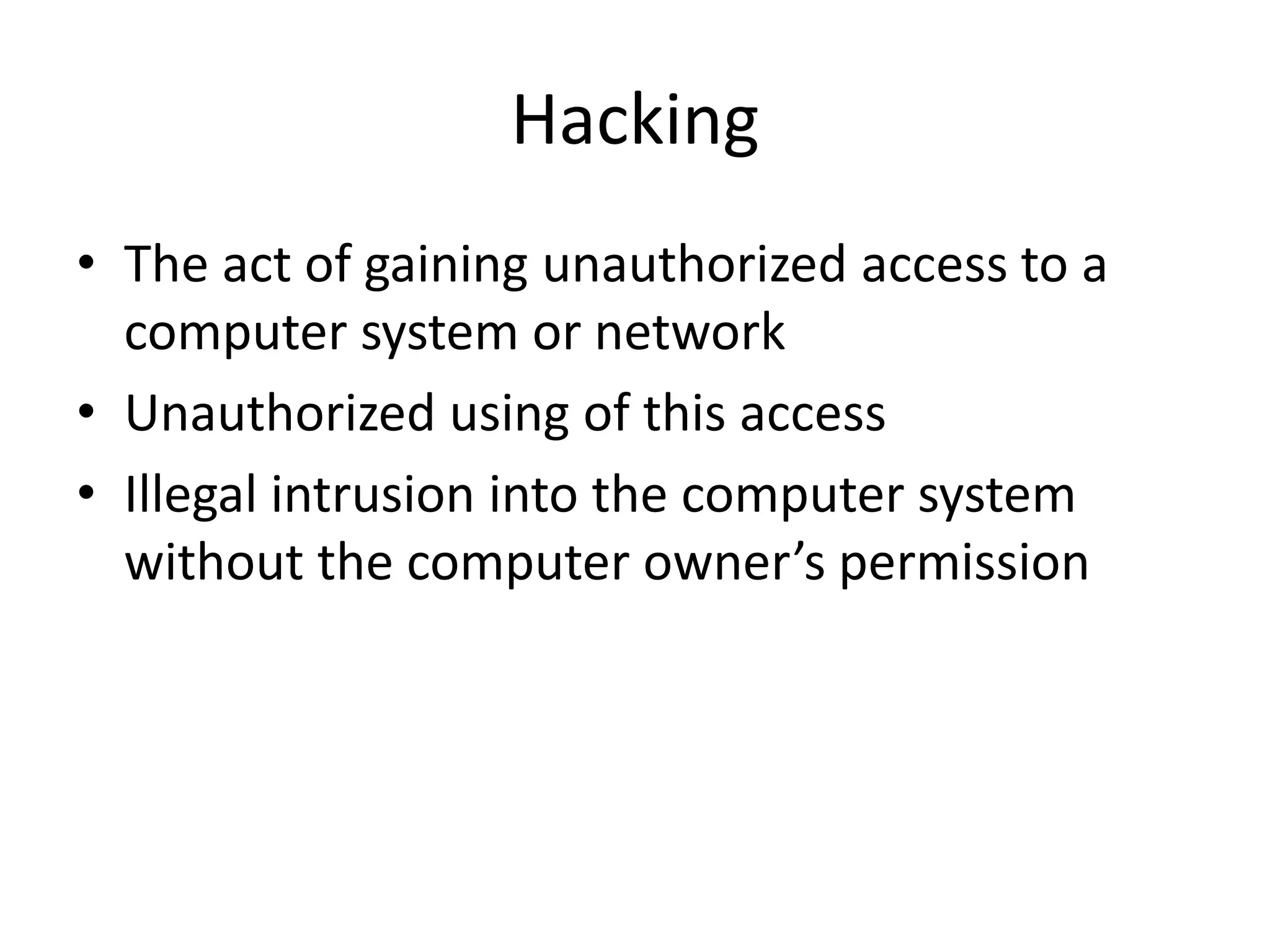
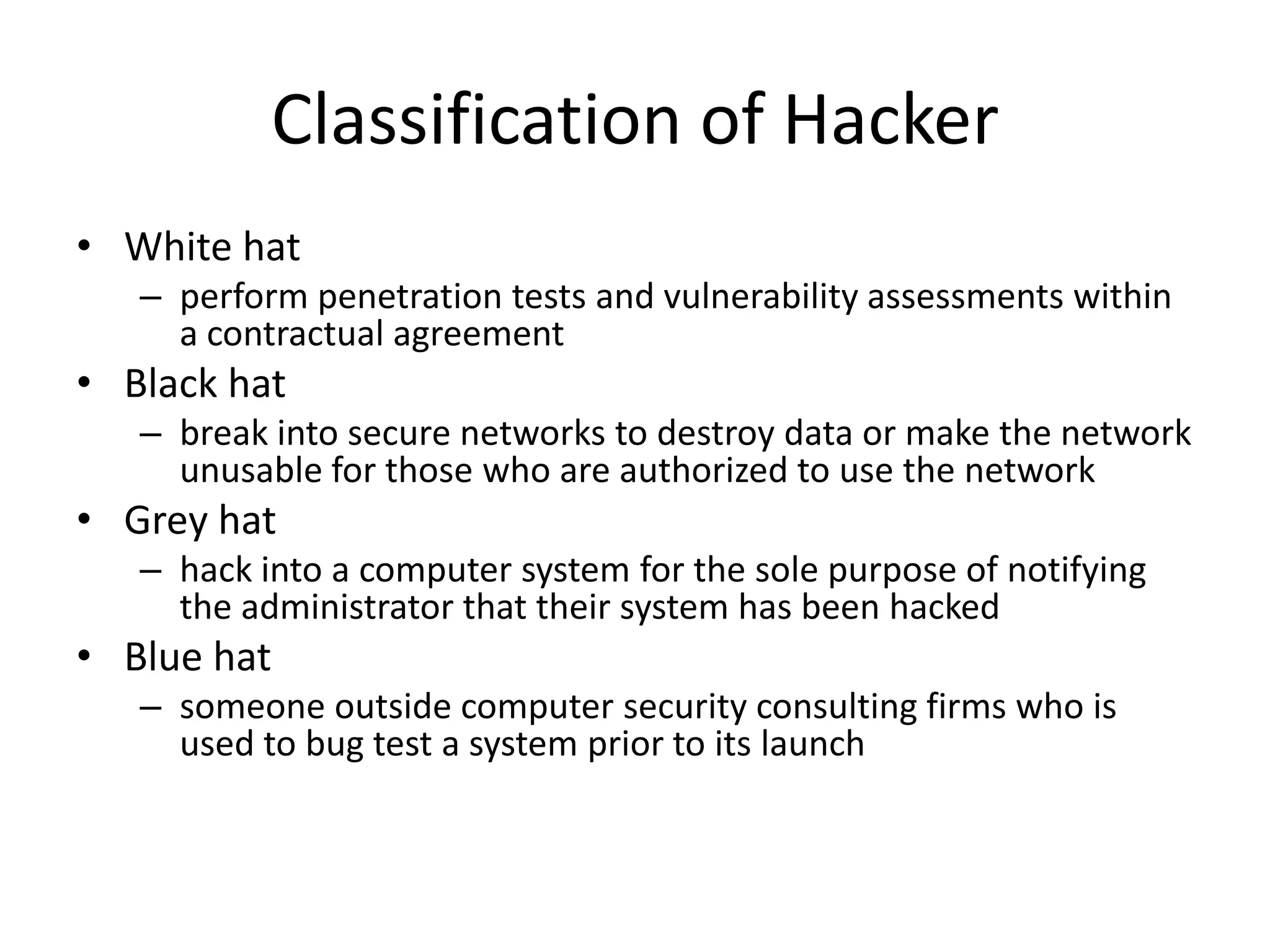
2. Hacking is the unauthorized access of computer systems or networks. Hackers may access systems to steal information, cause damage, or protest weaknesses. Malware like viruses and worms can be used to infect other computers.
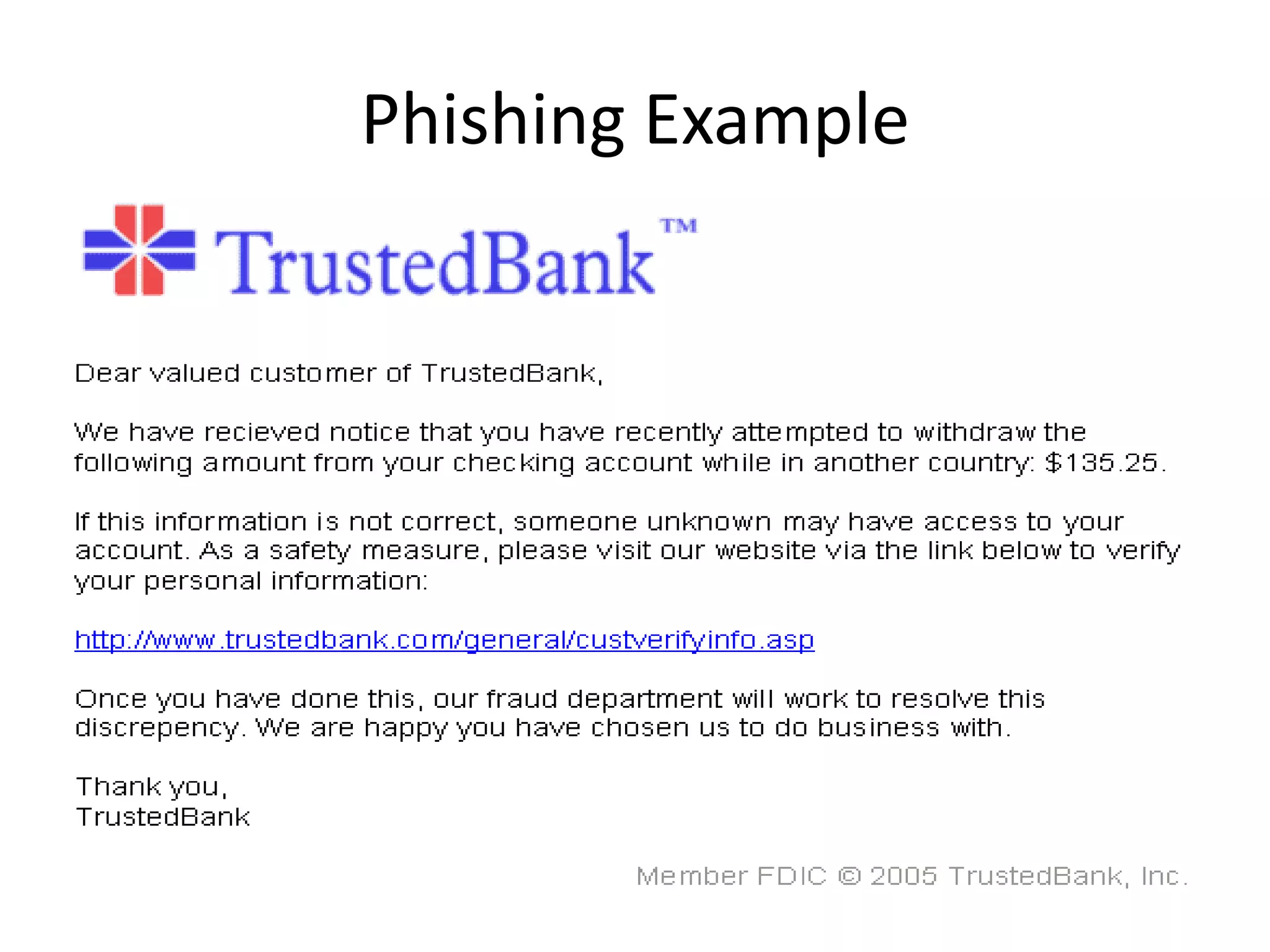
3. Software piracy is the illegal copying or distribution of copyrighted software. It reduces profits for developers and poses security risks. Other cyber crimes like cybersex, pornography, and fraud also use computers to enable or facilitate illegal activities.