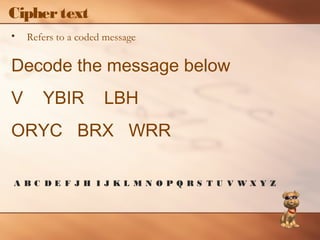
This document discusses various topics relating to computer ethics and privacy. It addresses issues like plagiarism, encryption, privacy in the workplace, protecting privacy online, computer crimes and viruses, cyberstalking, and information warfare. It emphasizes the importance of respecting oneself, others, and academic integrity when using computers and the internet.