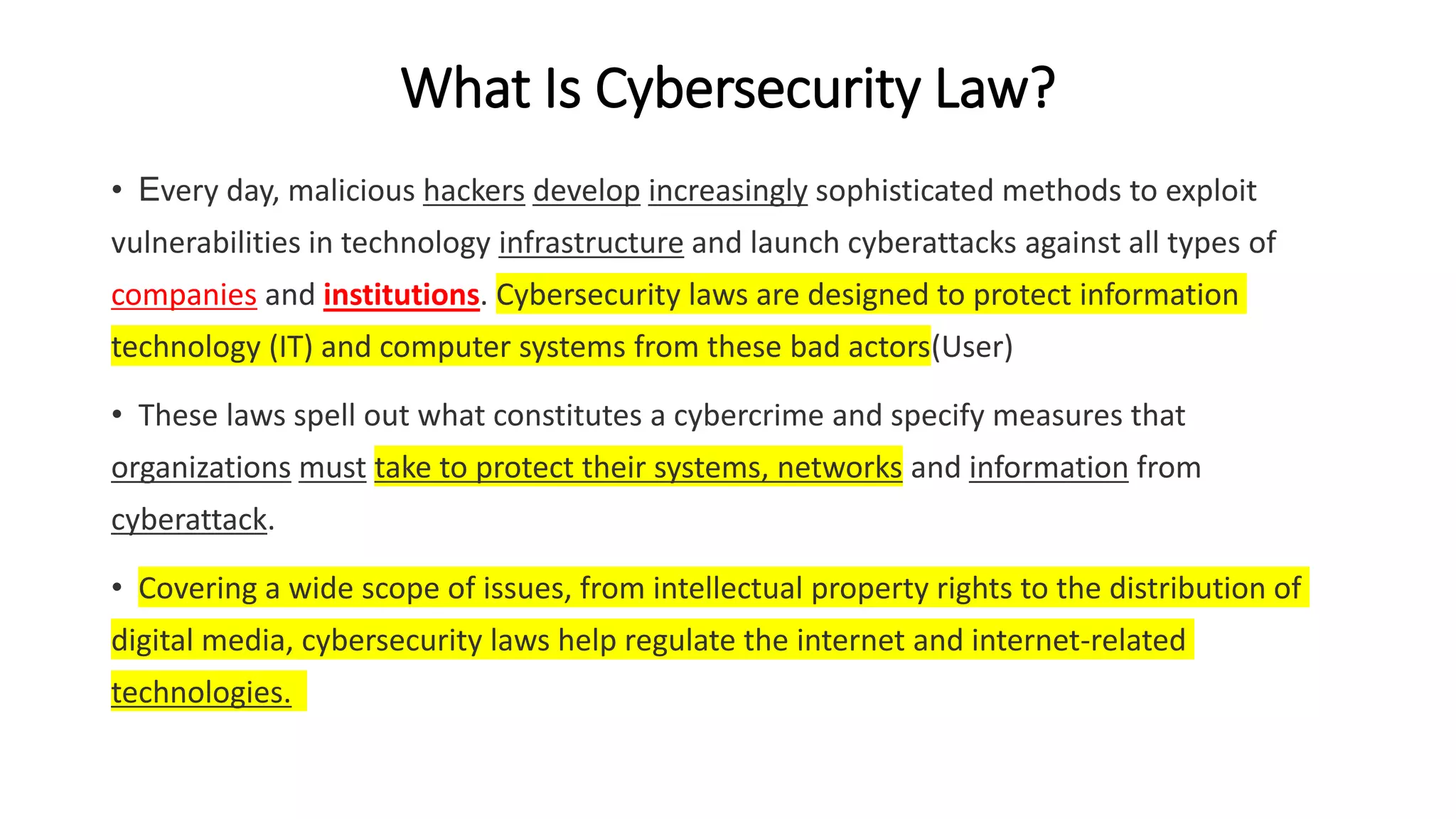
Cybersecurity laws are designed to protect digital systems and data from cybercrime. Major cybersecurity laws include the Computer Fraud and Abuse Act, Health Insurance Portability and Accountability Act (HIPAA), and Payment Card Industry Data Security Standard. These laws mandate cybersecurity practices, data privacy and security requirements, and set guidelines for sharing threat information. Federal agencies like the Department of Homeland Security, FBI, and FTC enforce these laws and work to safeguard critical infrastructure from cyberattacks.