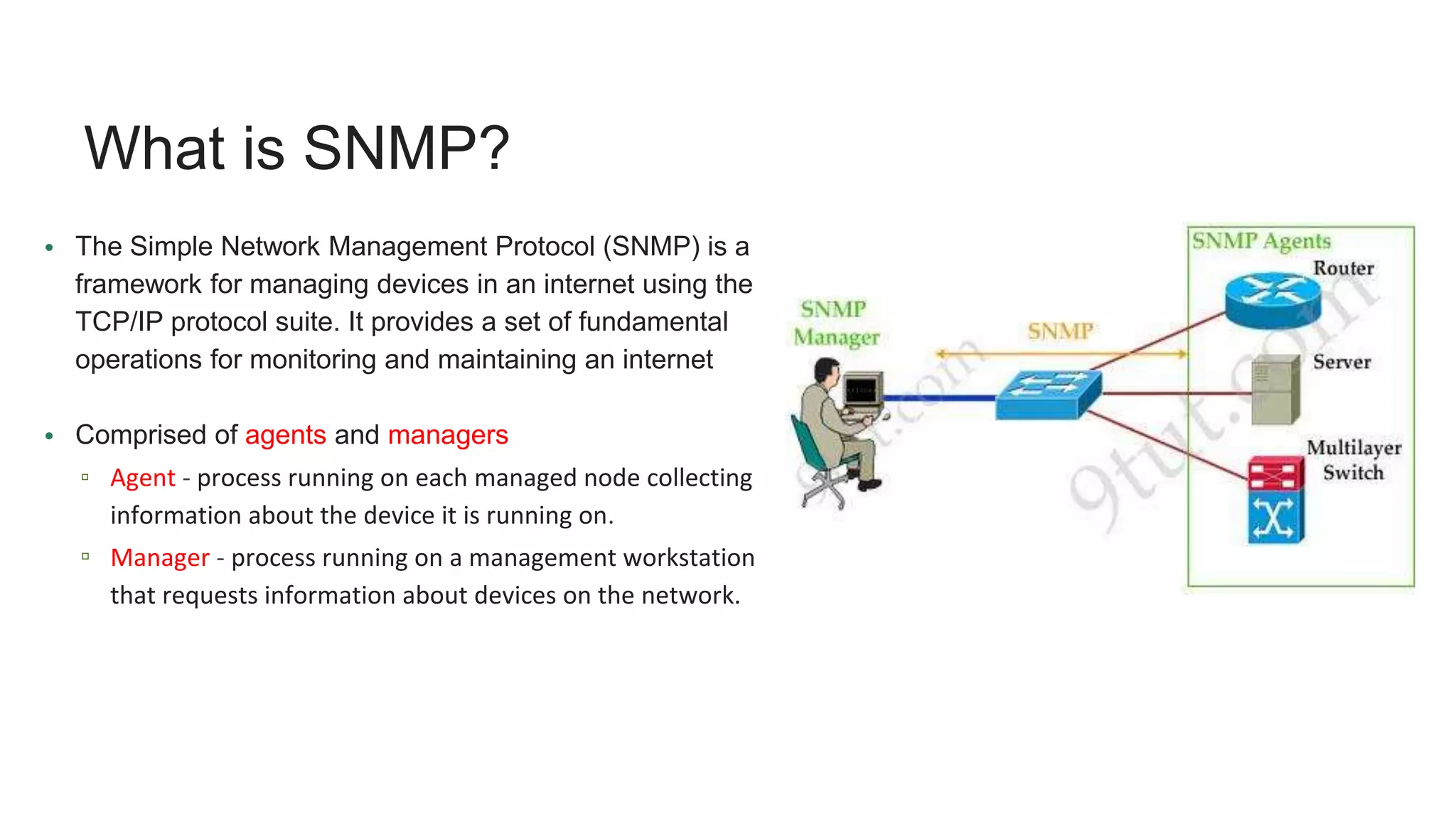
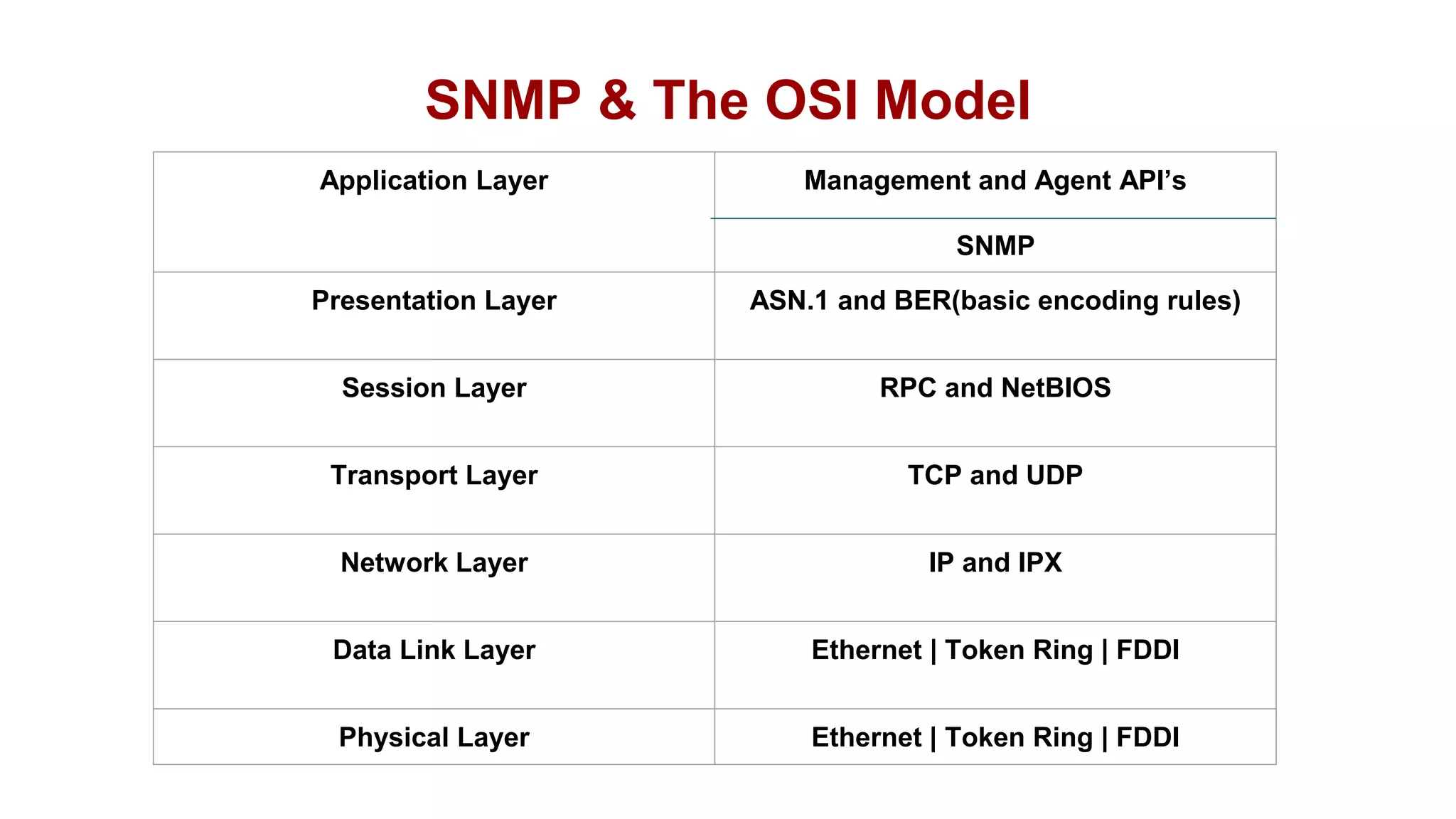
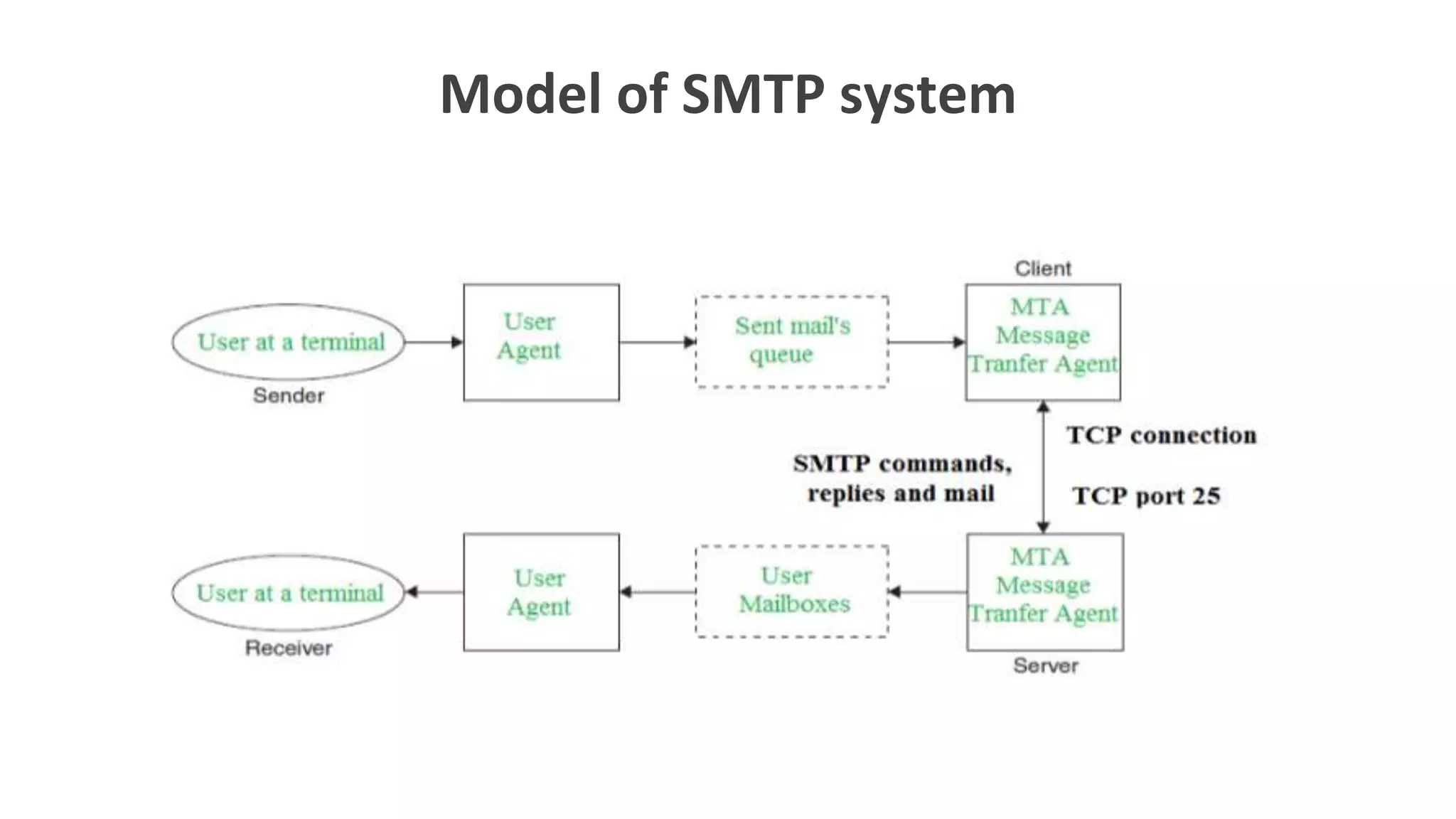
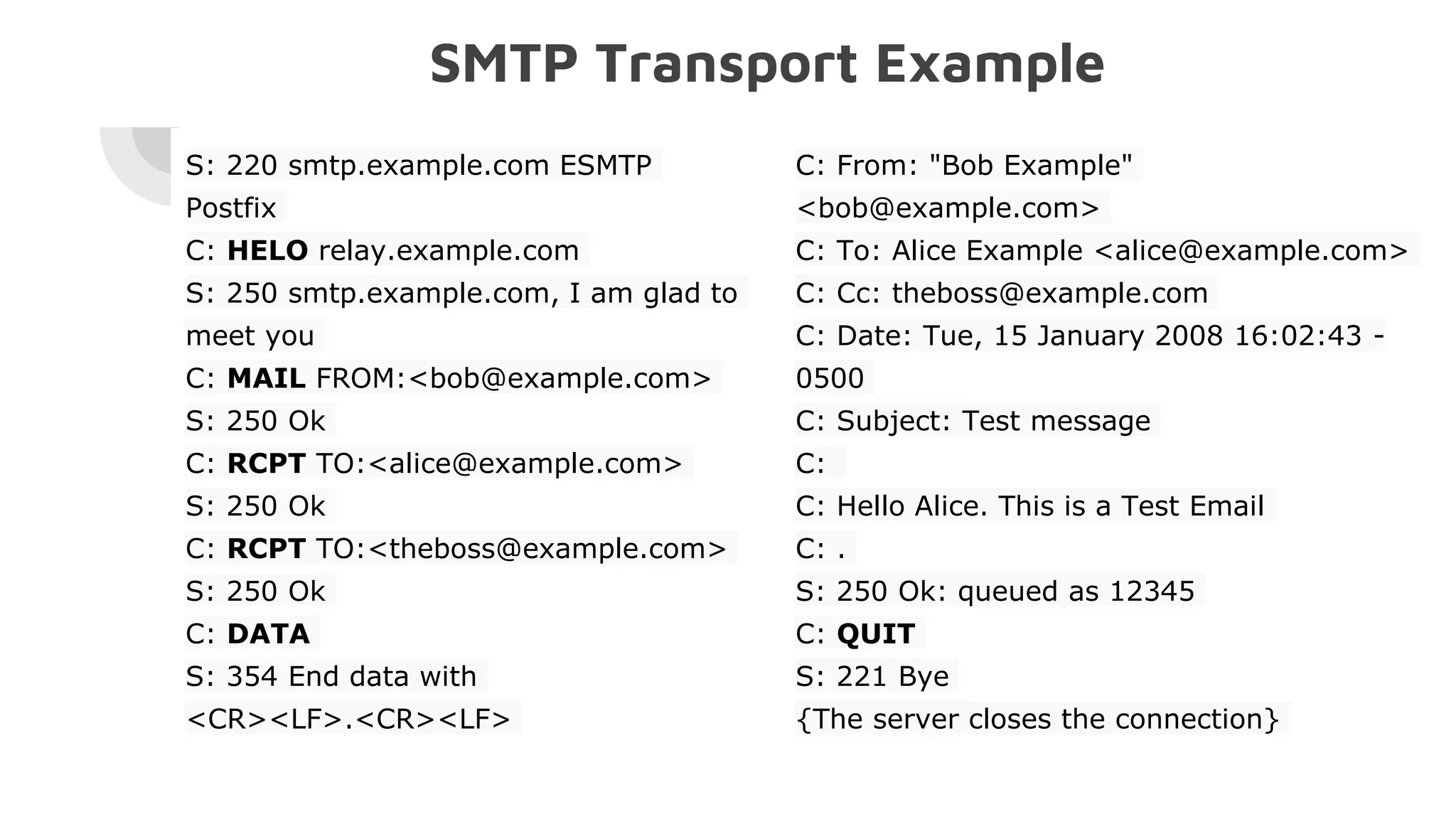
The document provides an overview of network management systems (NMS), focusing on the Simple Network Management Protocol (SNMP) and the Simple Mail Transfer Protocol (SMTP). It explains the functionalities of SNMP for monitoring network devices and details SMTP's role in email transmission, including its commands, limitations, and the use of Multipurpose Internet Mail Extensions (MIME) for handling various content types. Overall, it emphasizes the interrelation between SNMP and SMTP in managing and communicating across networks.