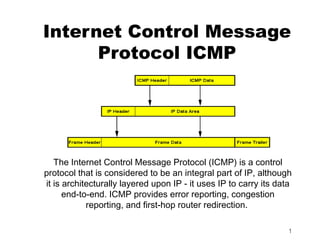
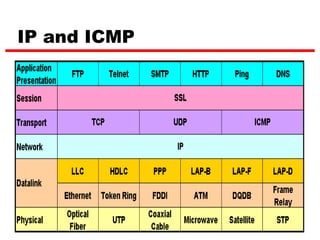
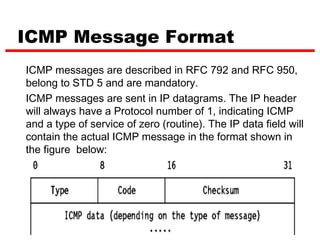
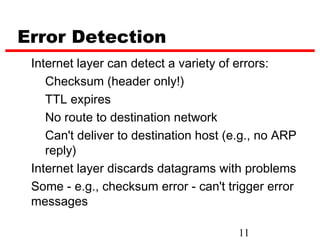
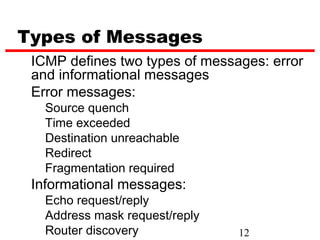
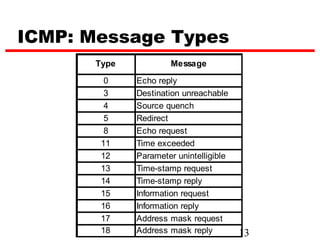
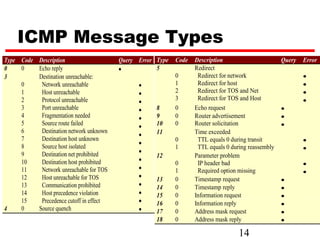
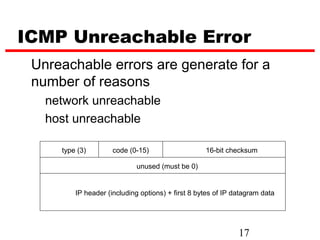
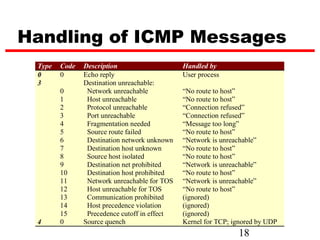
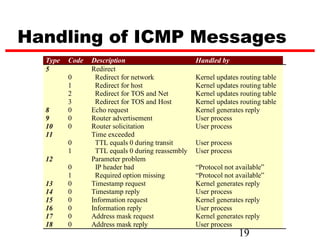
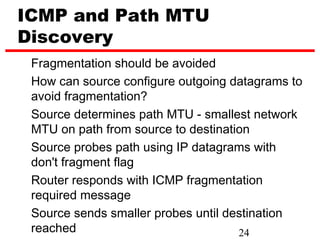
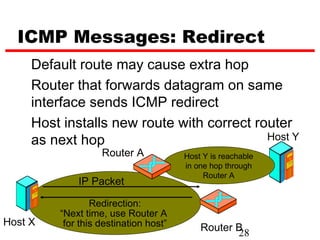
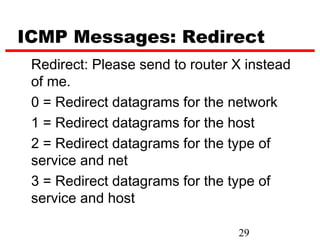
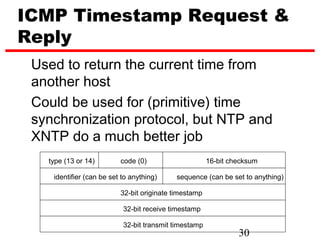
The document discusses the Internet Control Message Protocol (ICMP). ICMP provides error reporting, congestion reporting, and first-hop router redirection. It uses IP to carry its data end-to-end and is considered an integral part of IP. ICMP messages are encapsulated in IP datagrams and are used to report errors in IP datagrams, though some errors may still result in datagrams being dropped without a report. ICMP defines various message types including error messages like destination unreachable and informational messages like echo request and reply.