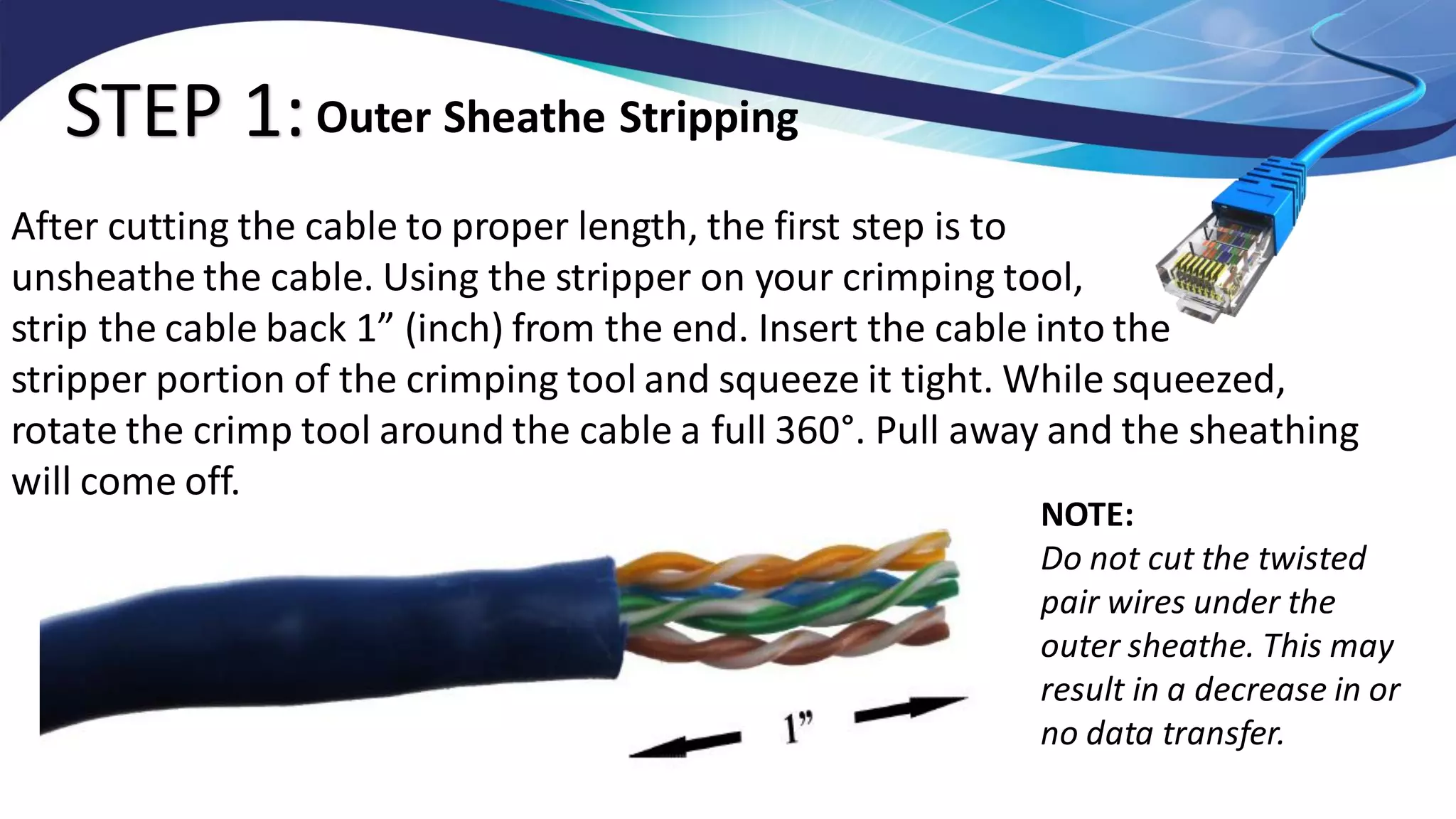
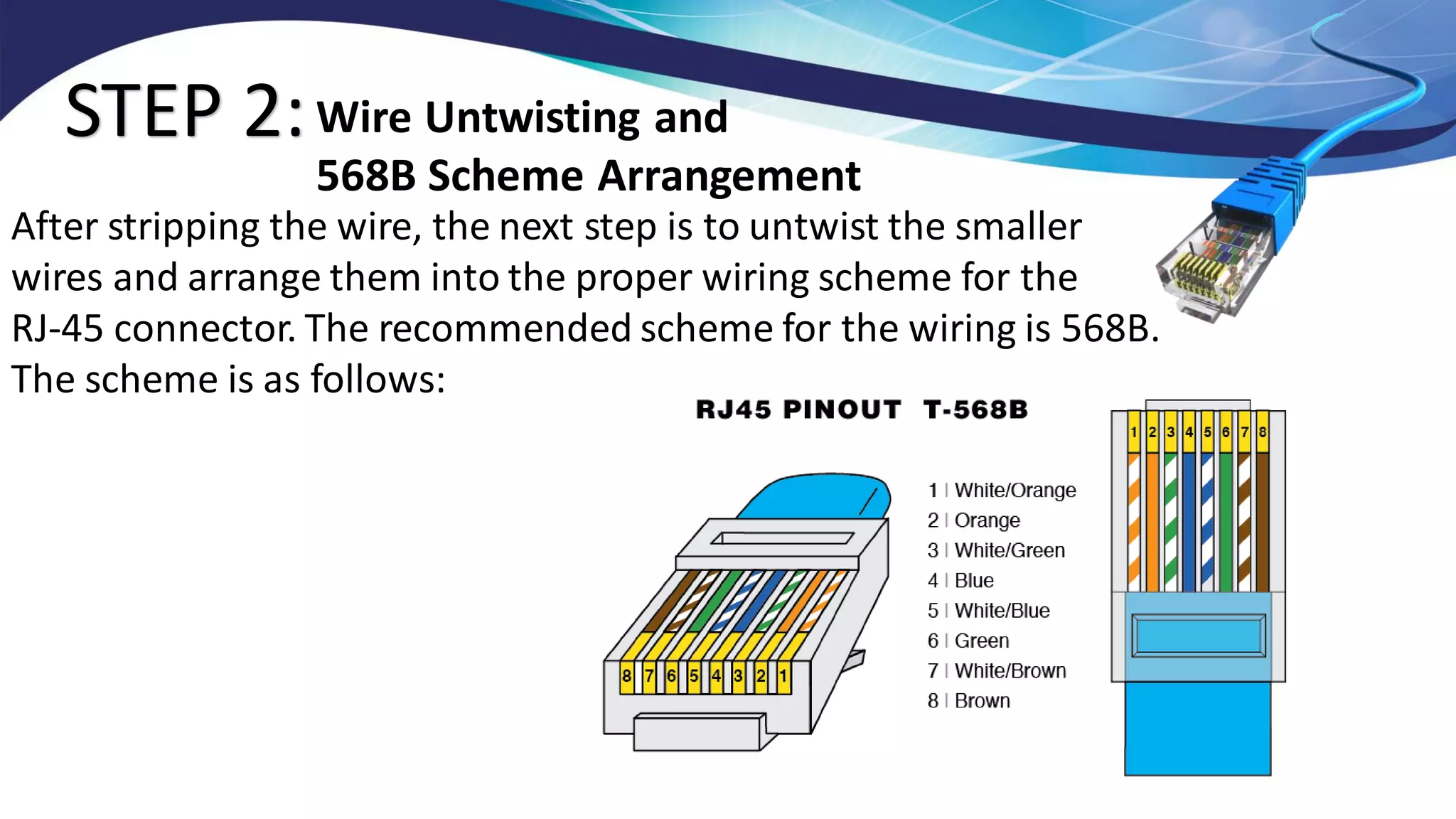
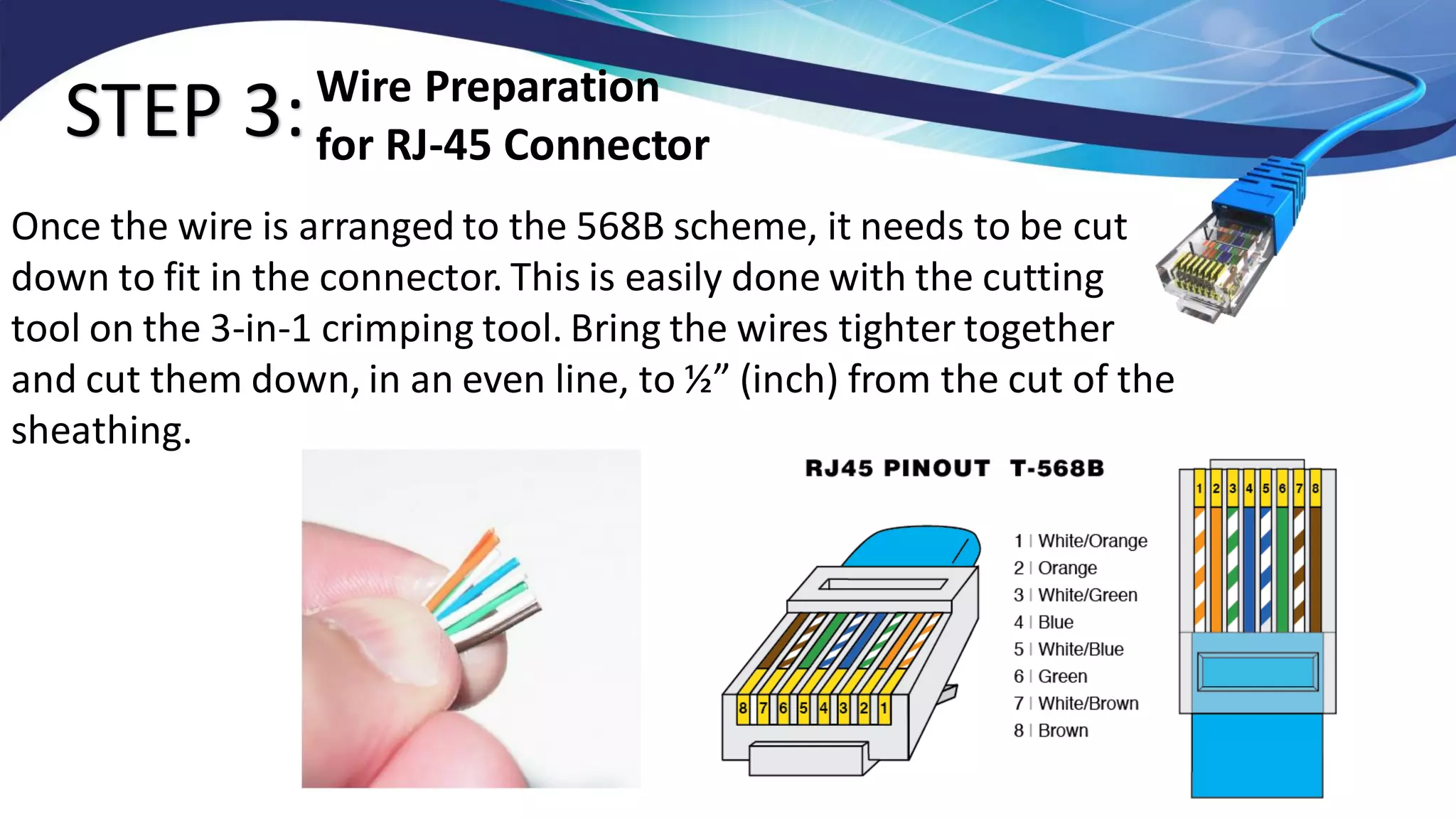
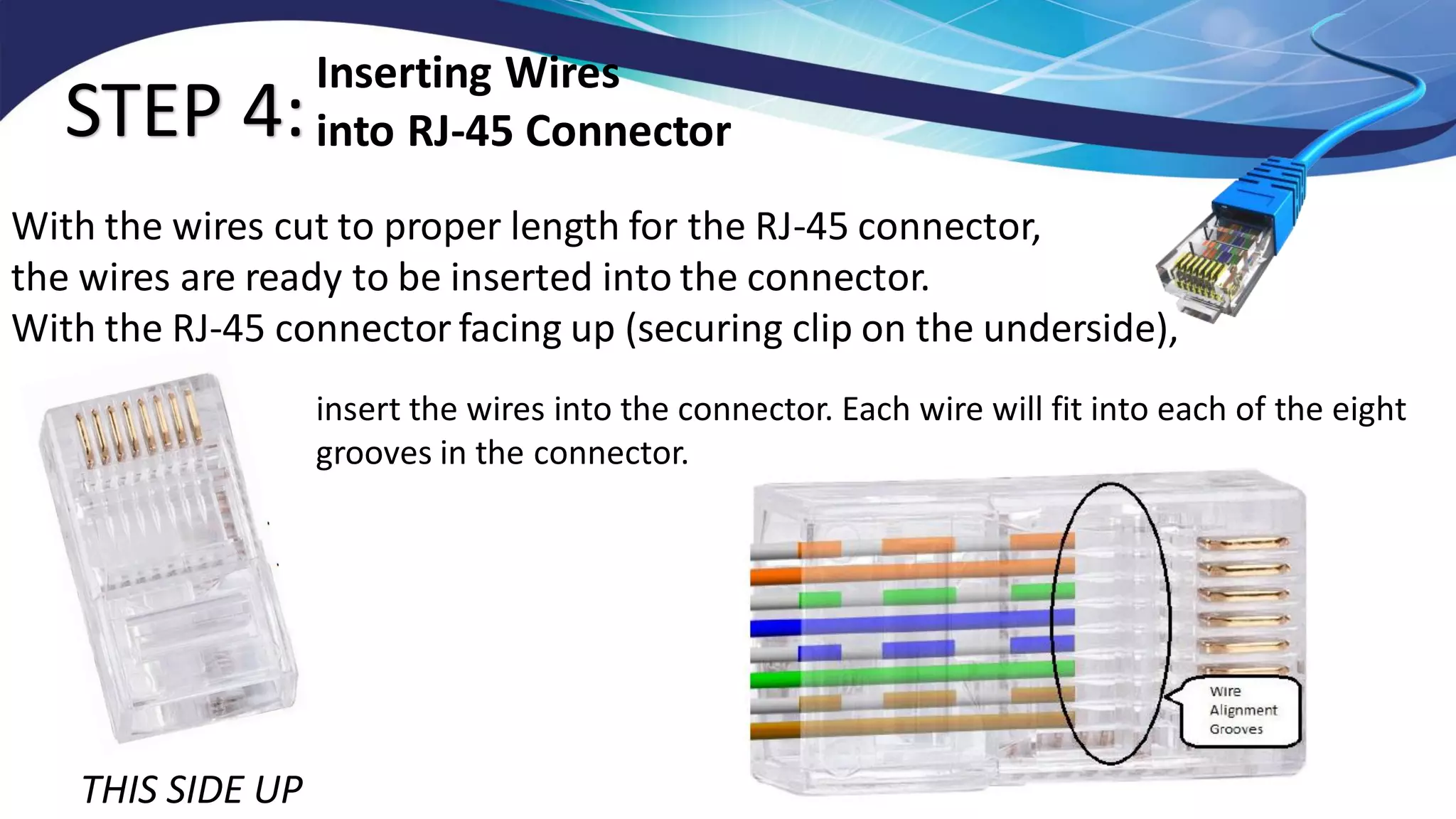
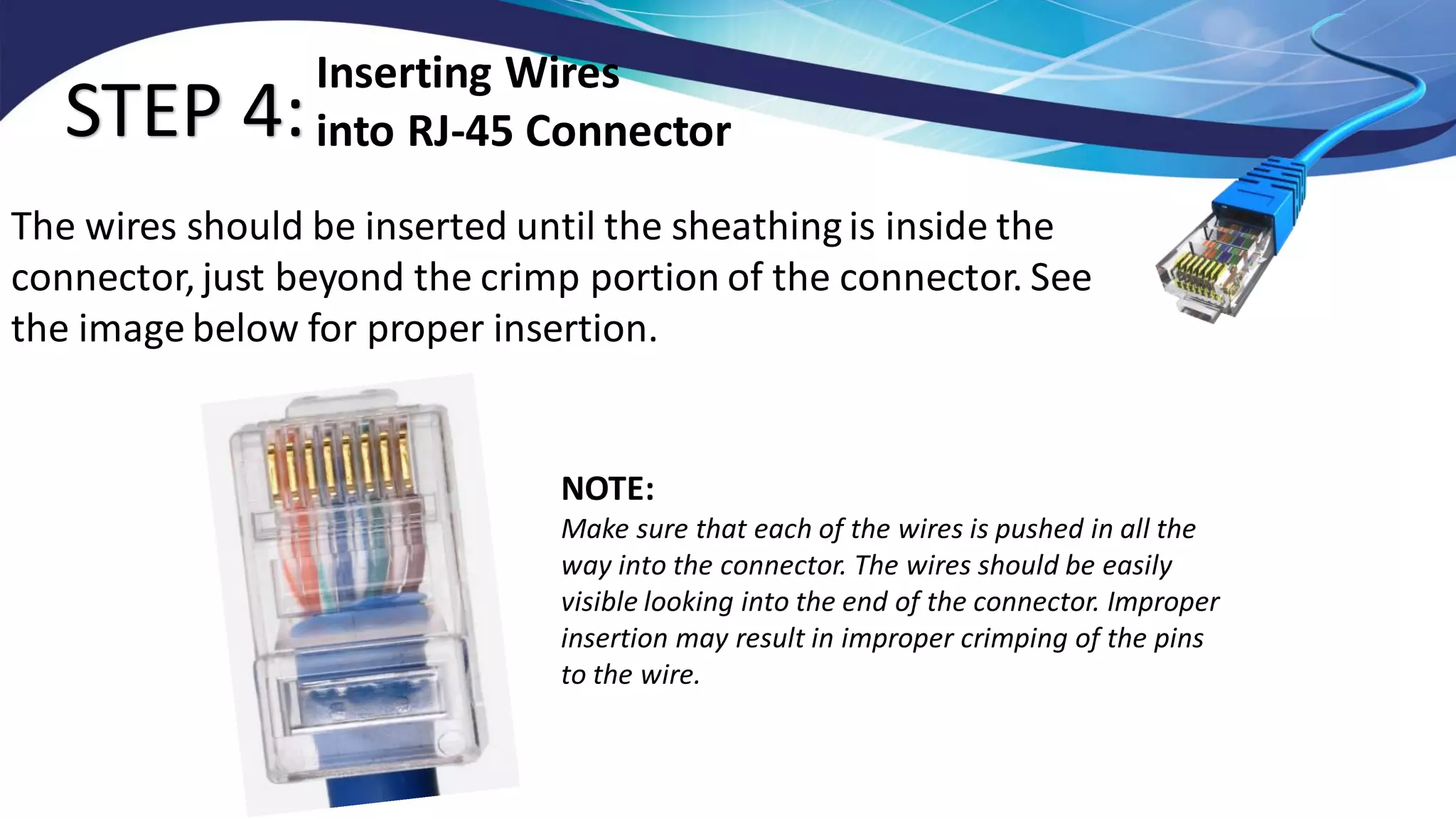
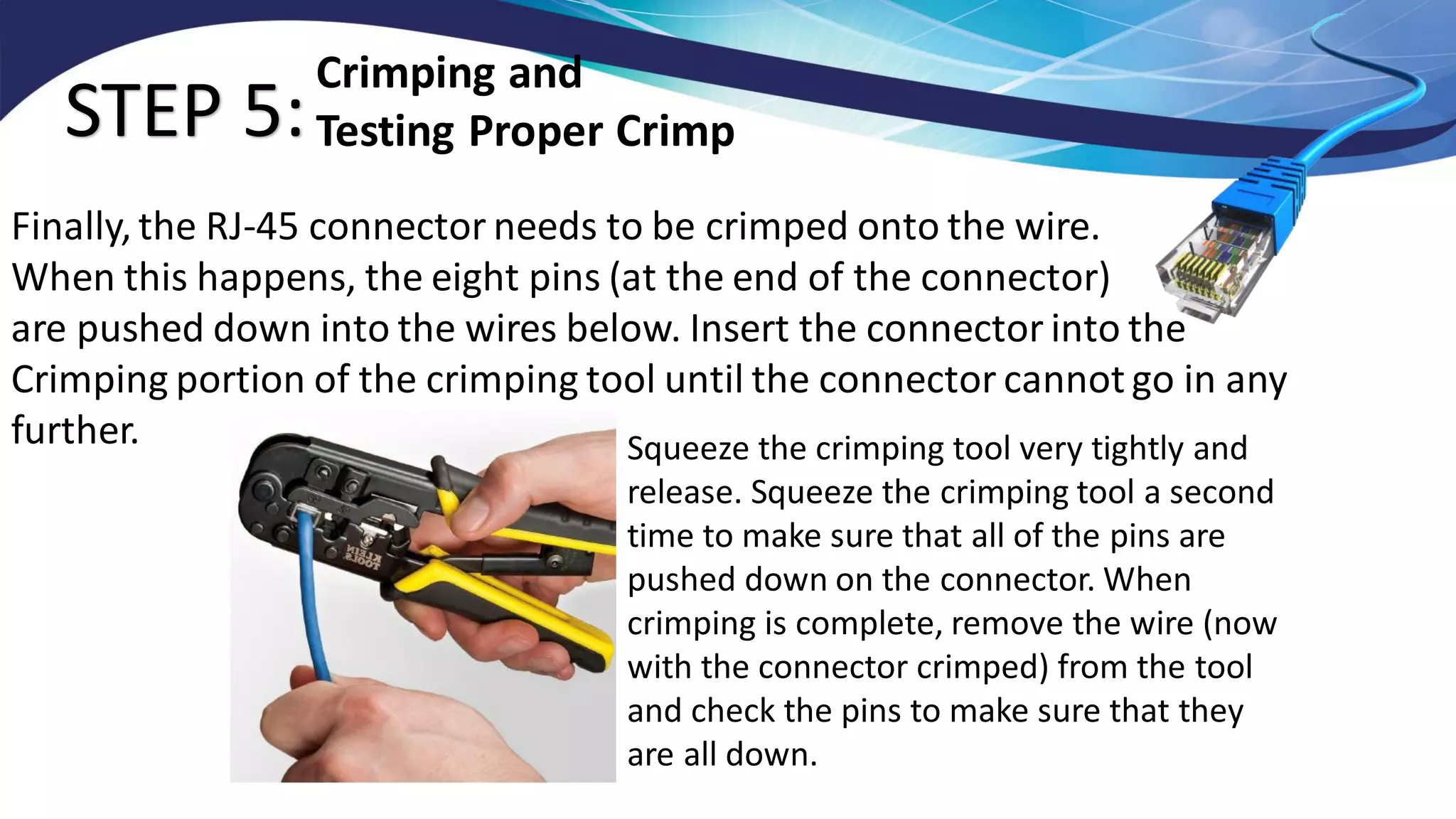
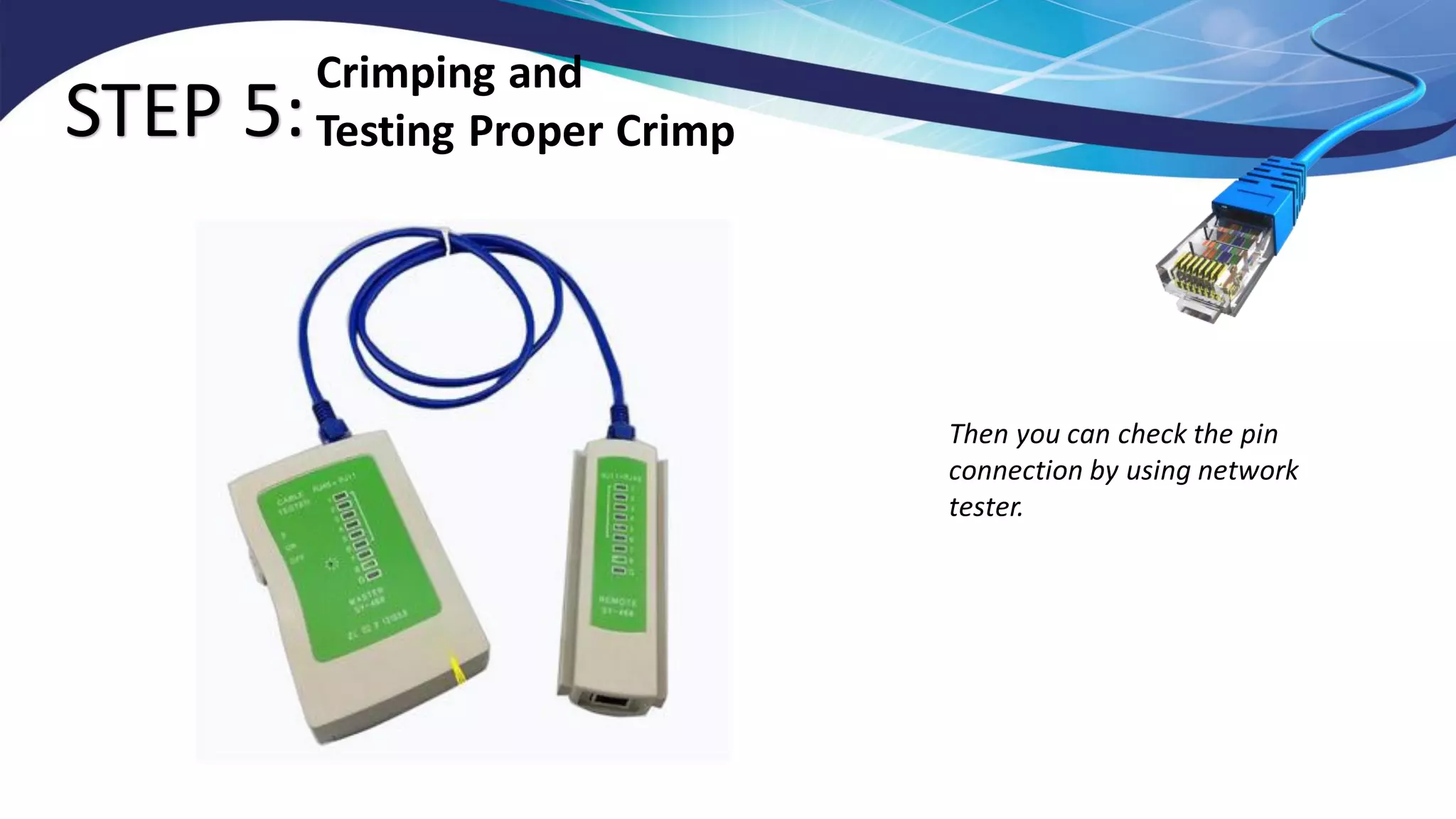
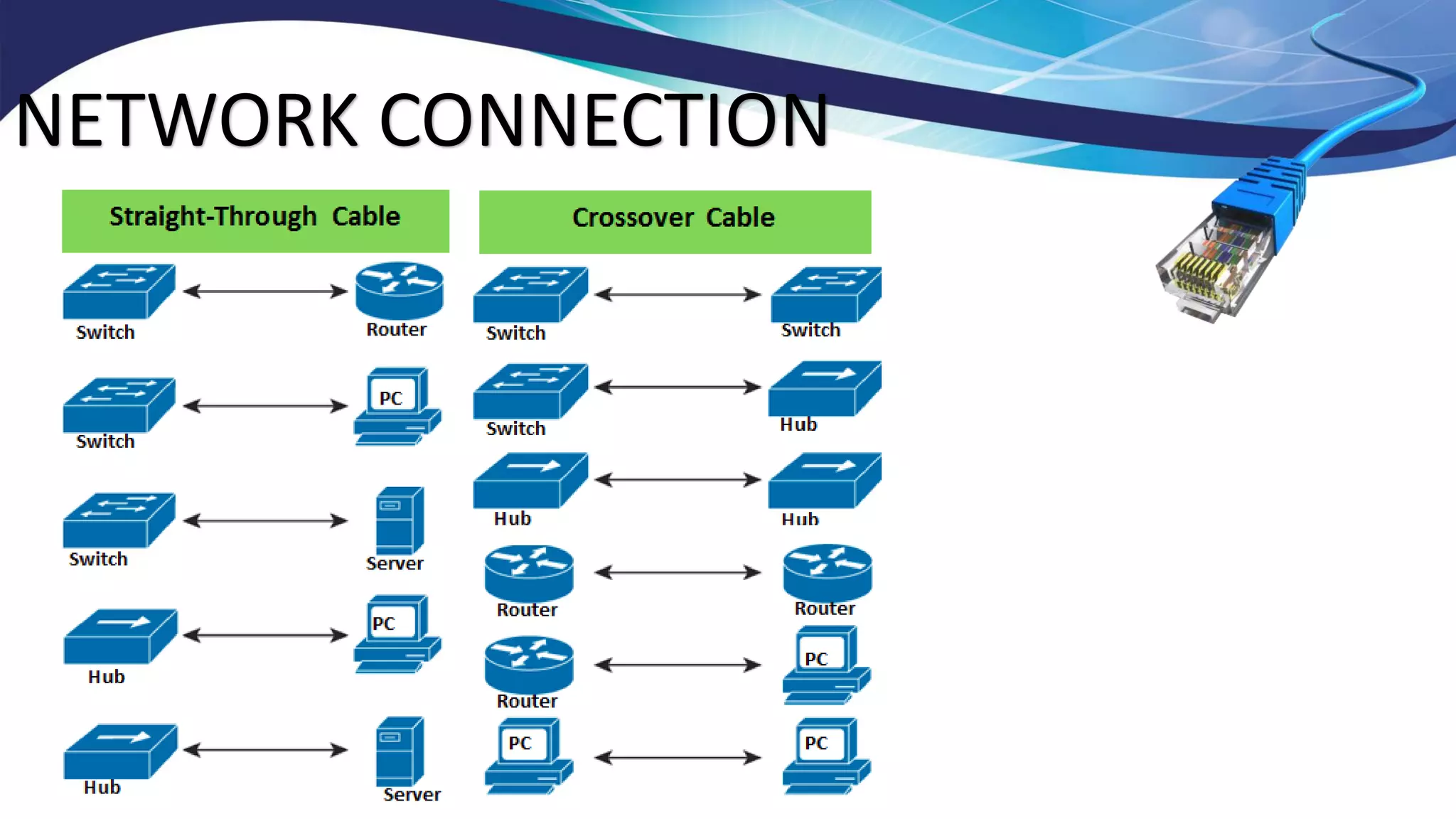
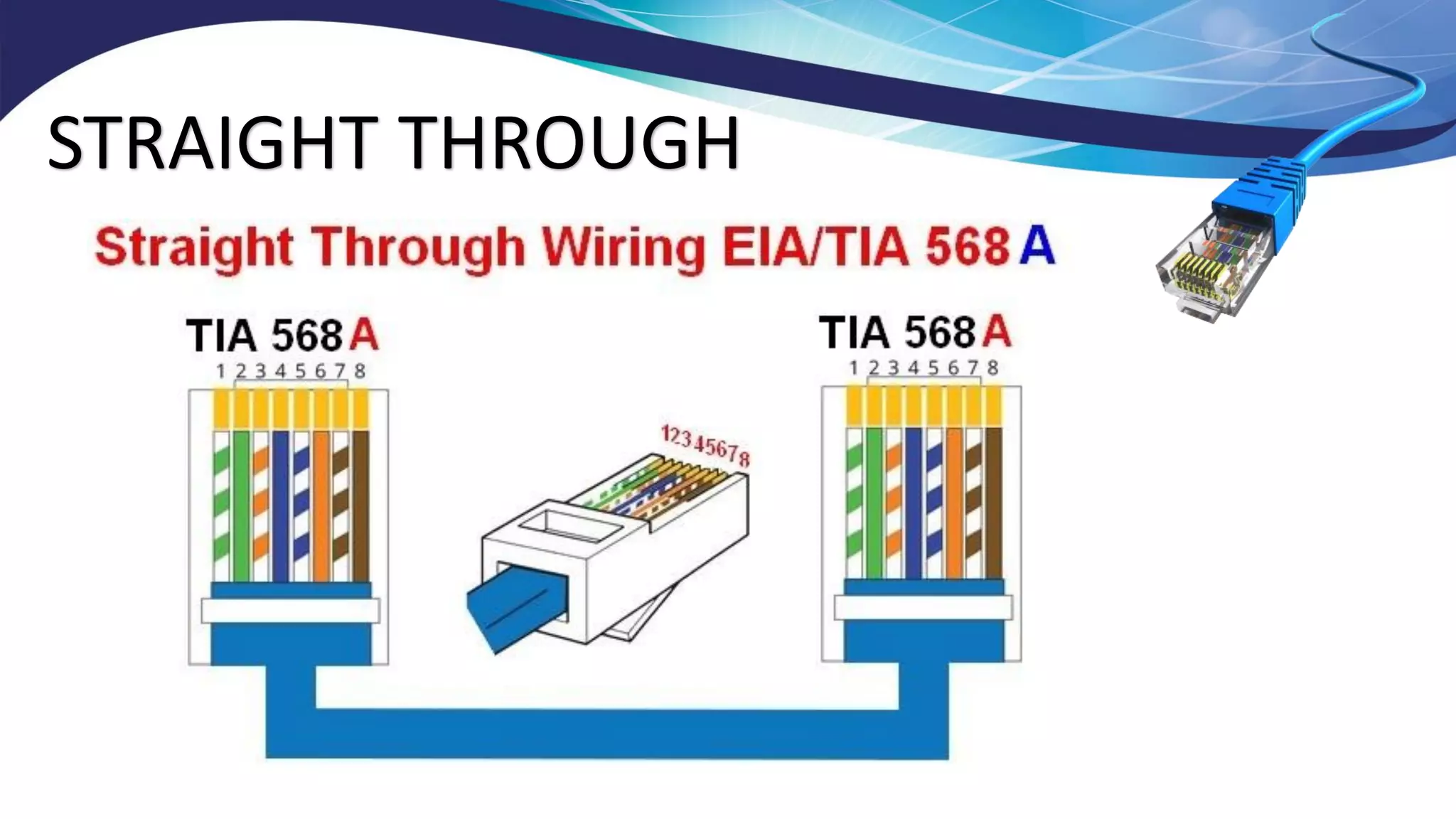
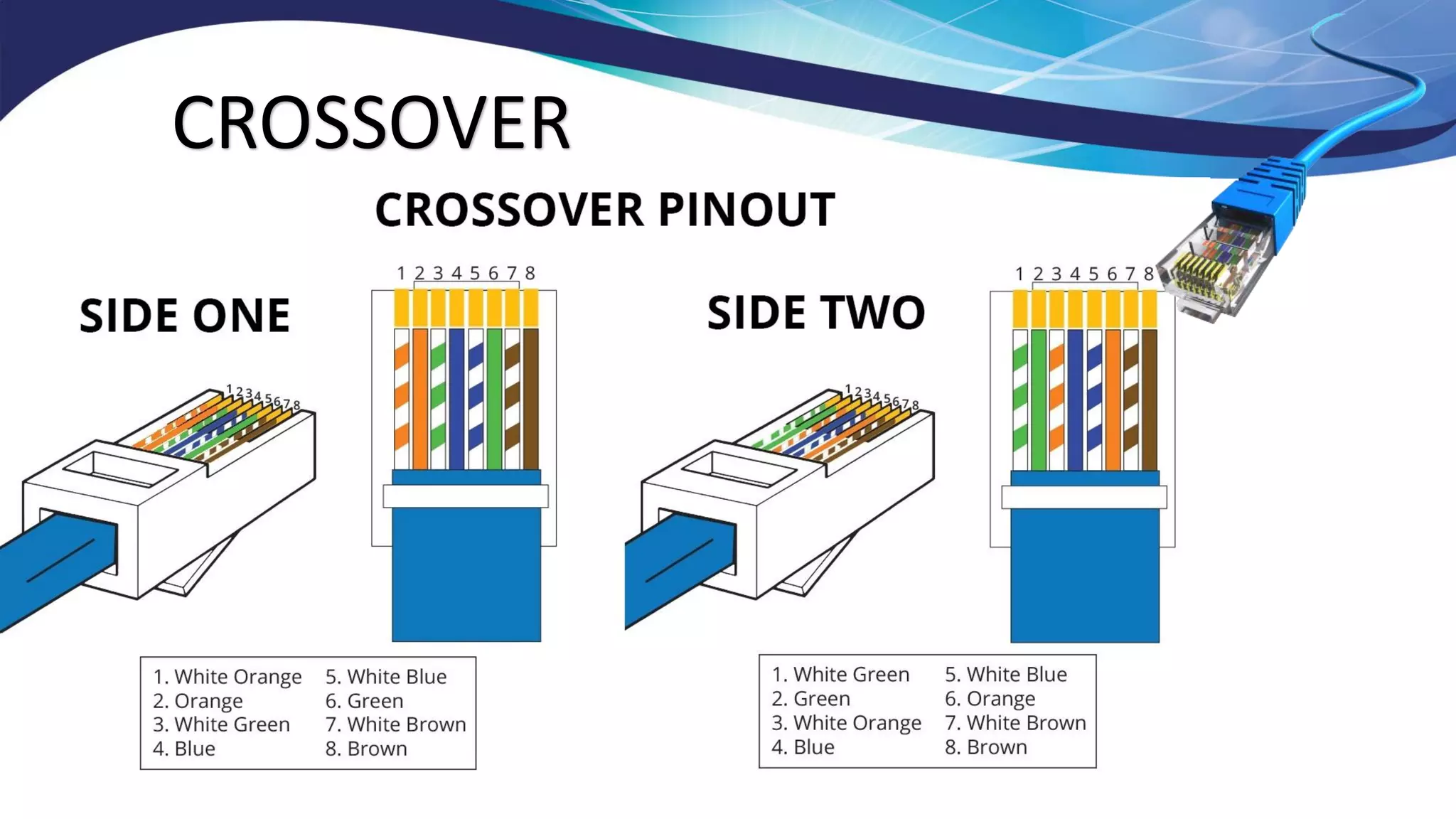
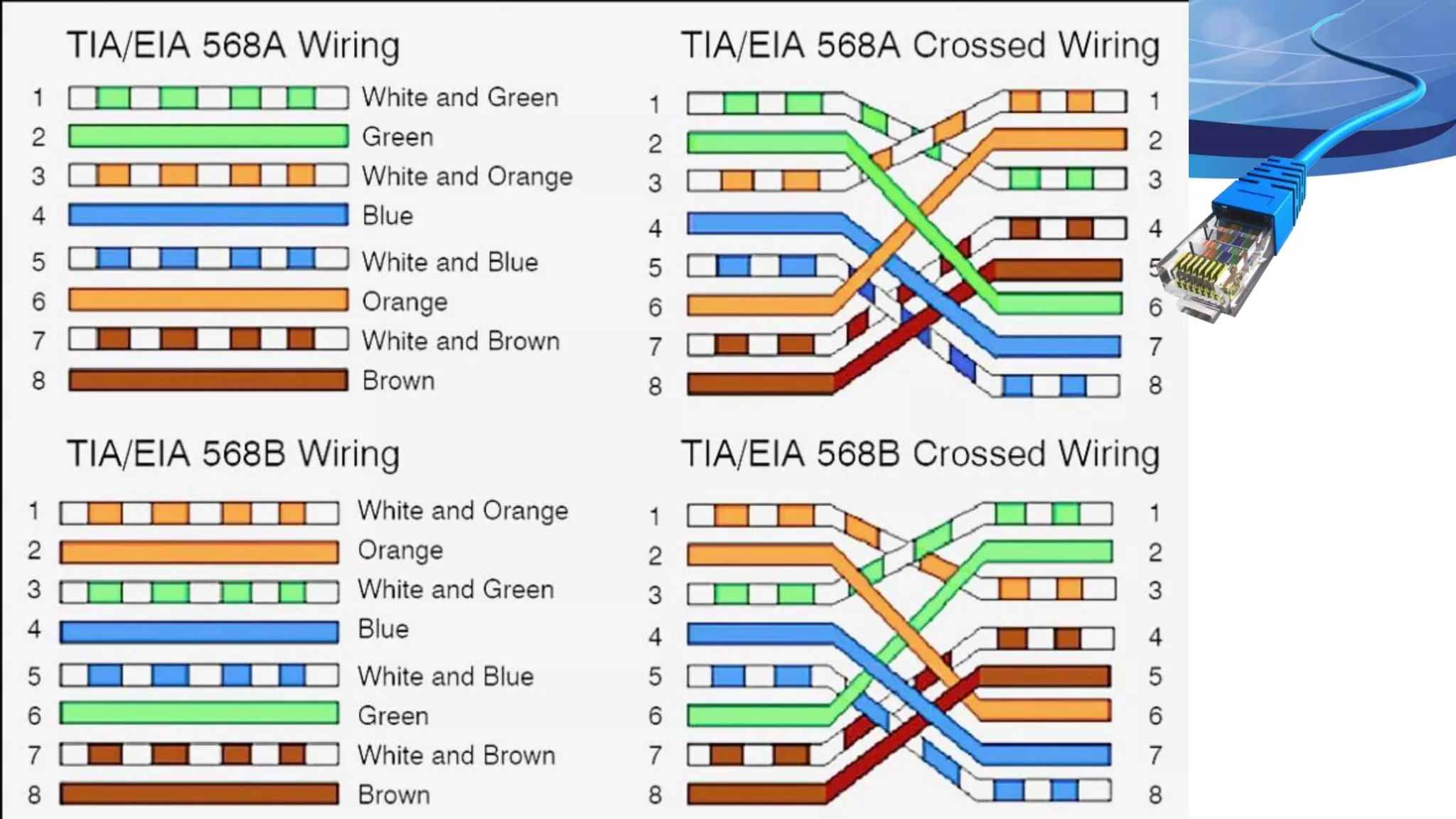
This document outlines the process of crimping RJ-45 connectors to Ethernet cables as part of a computer networking curriculum. It covers necessary tools, step-by-step instructions for preparing and crimping the cables, and explains the wiring schemes T568A and T568B. The completion of this module enables students to establish network connections using properly crimped cables.