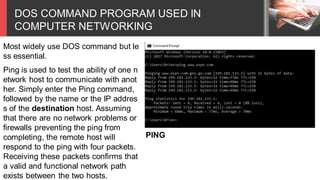
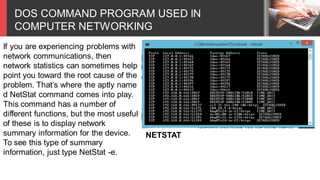
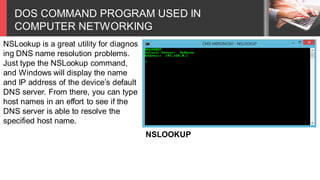
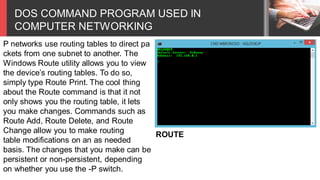
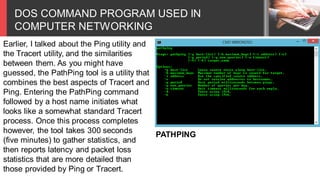
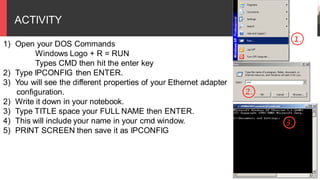
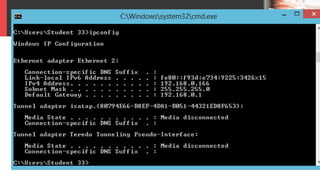
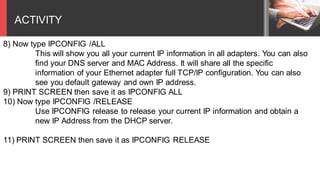
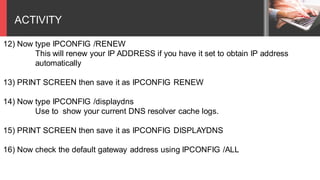
The document outlines a training module for computer networking focused on DOS commands, covering their applications and functionalities such as testing connectivity with ping, checking routes with tracert, and managing IP configurations with ipconfig. It provides detailed information on various commands like netstat, arp, hostname, nslookup, and route, emphasizing their roles in diagnosing and resolving network issues. The module includes activities for learners to practice using these commands to gather and analyze network information.