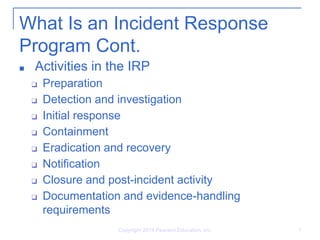
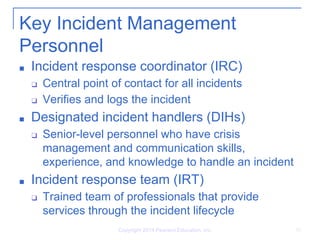
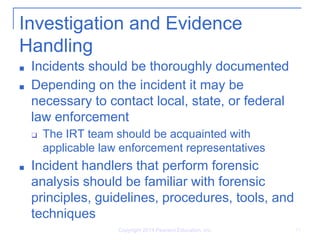
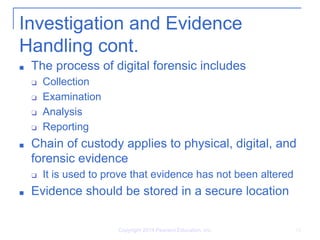
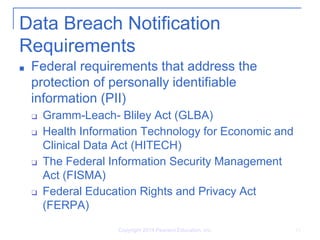
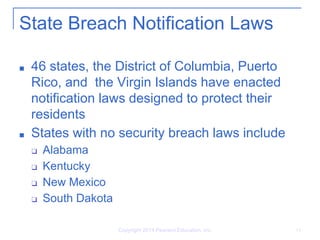
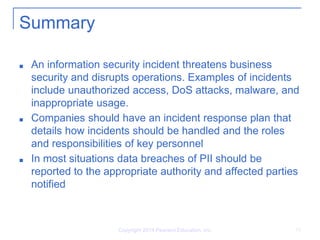
This document discusses information security incident management. It defines what constitutes an information security incident, such as unauthorized access or denial of service attacks. It also outlines the key aspects of an incident response program, including preparation, detection, response, and documentation. The document explains the roles of incident response coordinators, handlers, and teams. It also covers investigation practices, evidence handling, and federal and state data breach notification requirements.