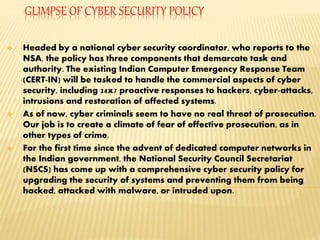
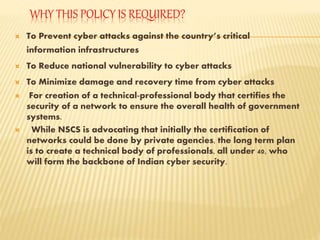
The document outlines India's new National Cyber Security Policy. It aims to secure computing environments and boost trust in electronic transactions. Key points:
- The policy establishes the Indian Computer Emergency Response Team (CERT-IN) to handle cyber security commercially, including responding to attacks.
- It seeks to create effective prosecution for cyber criminals, who currently face little threat.
- The policy upgrades security for government systems to prevent hacking and malware attacks, in response to growing sophisticated cyber threats facing the country.