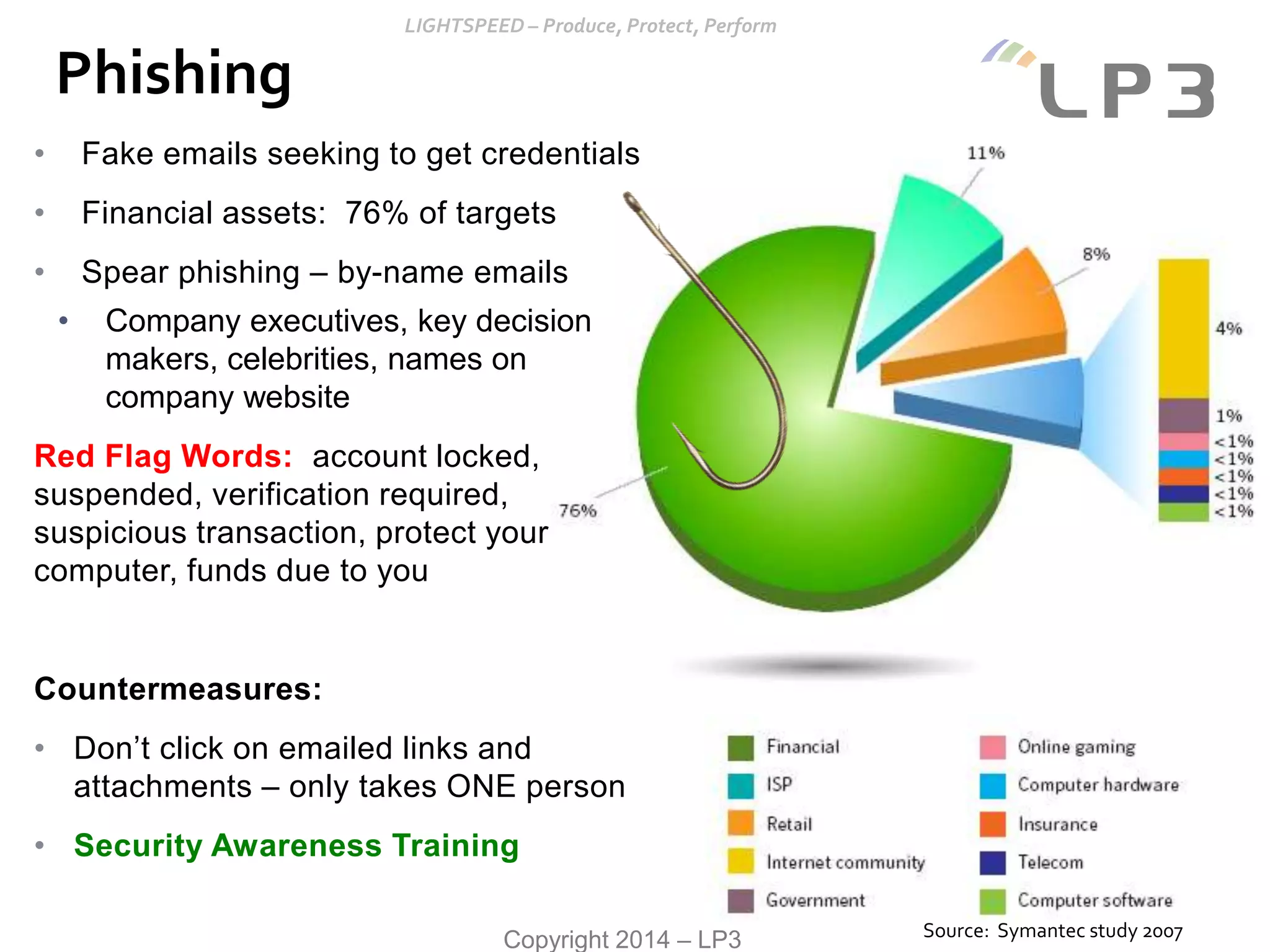
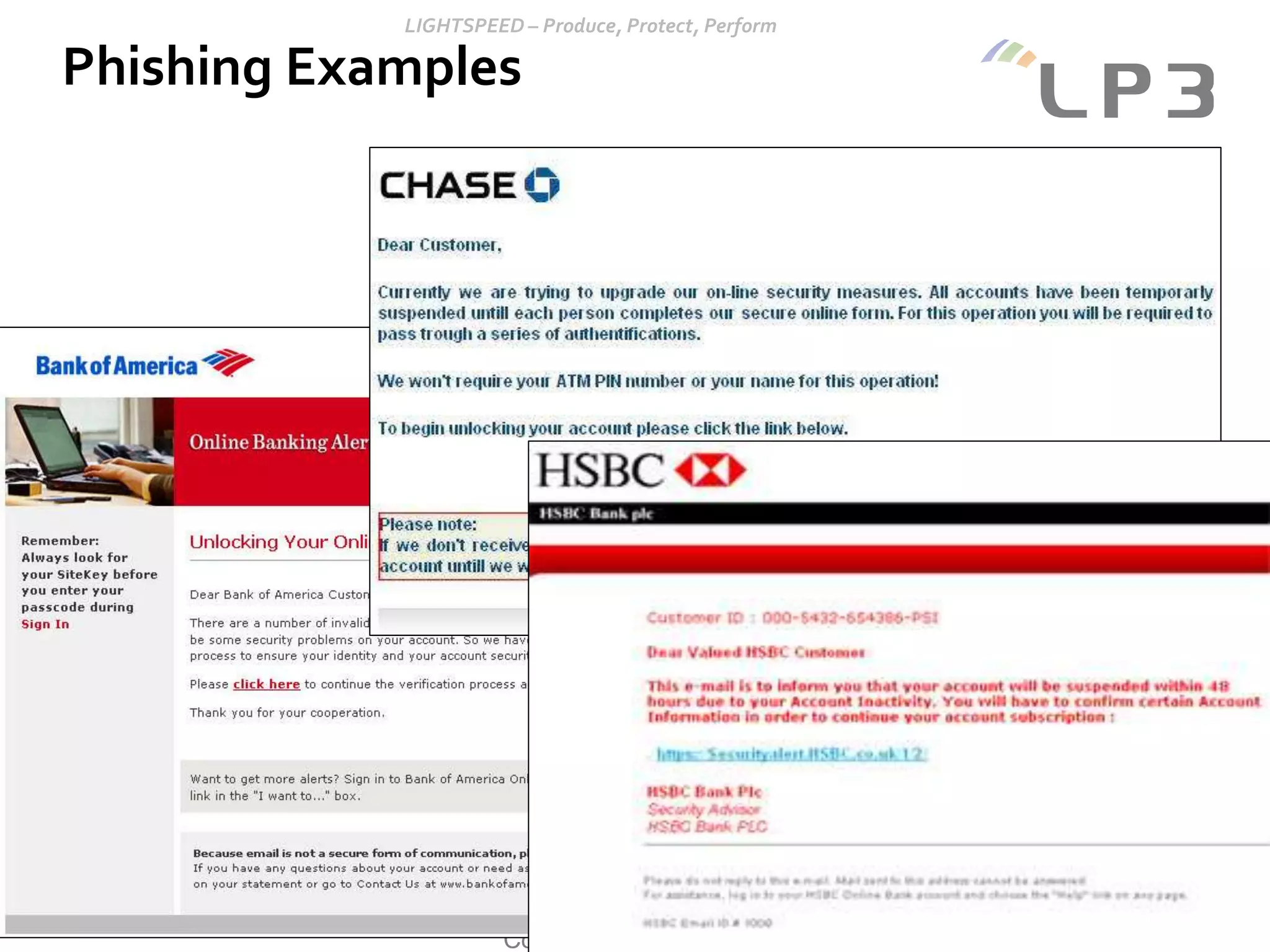
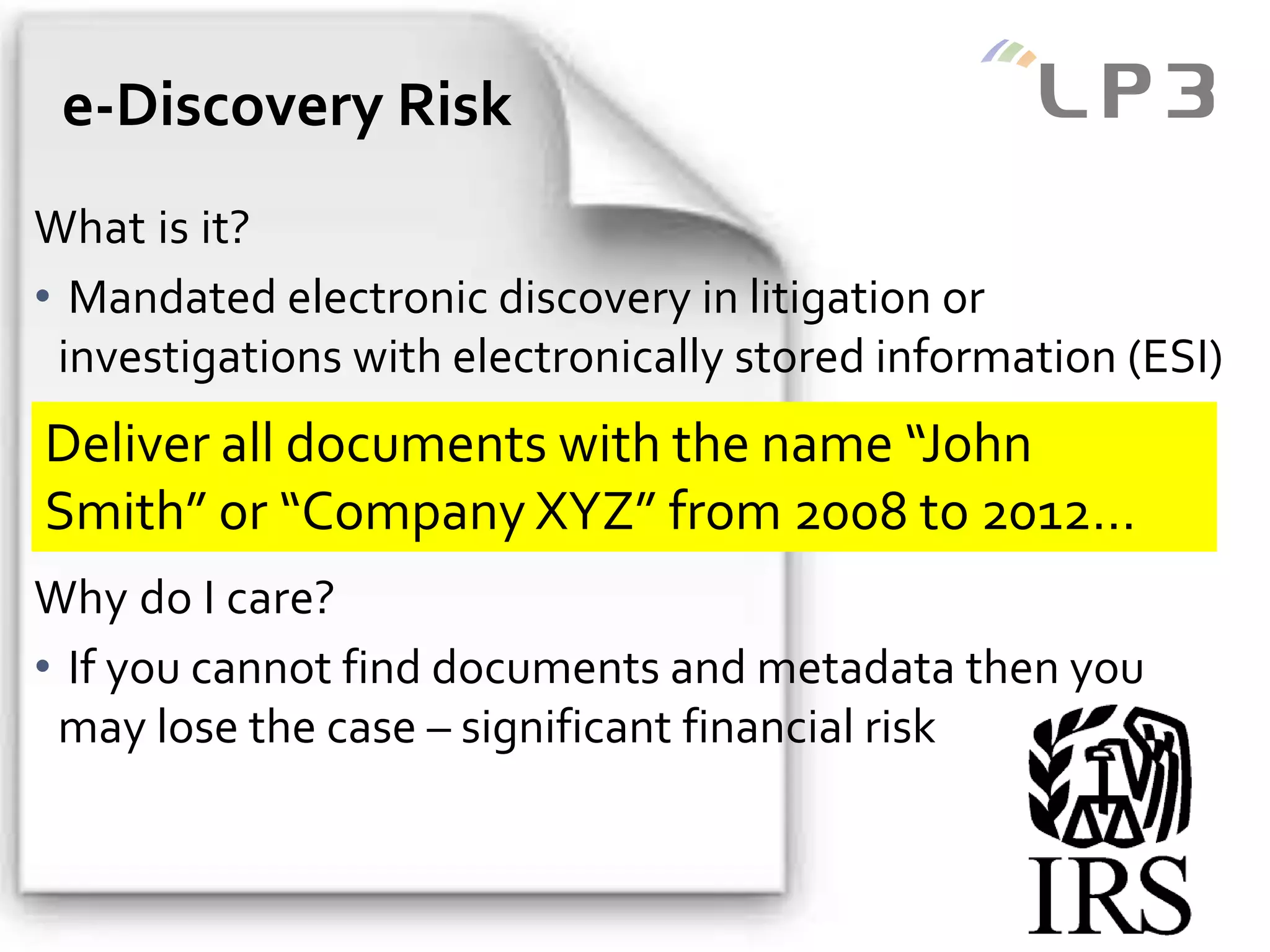
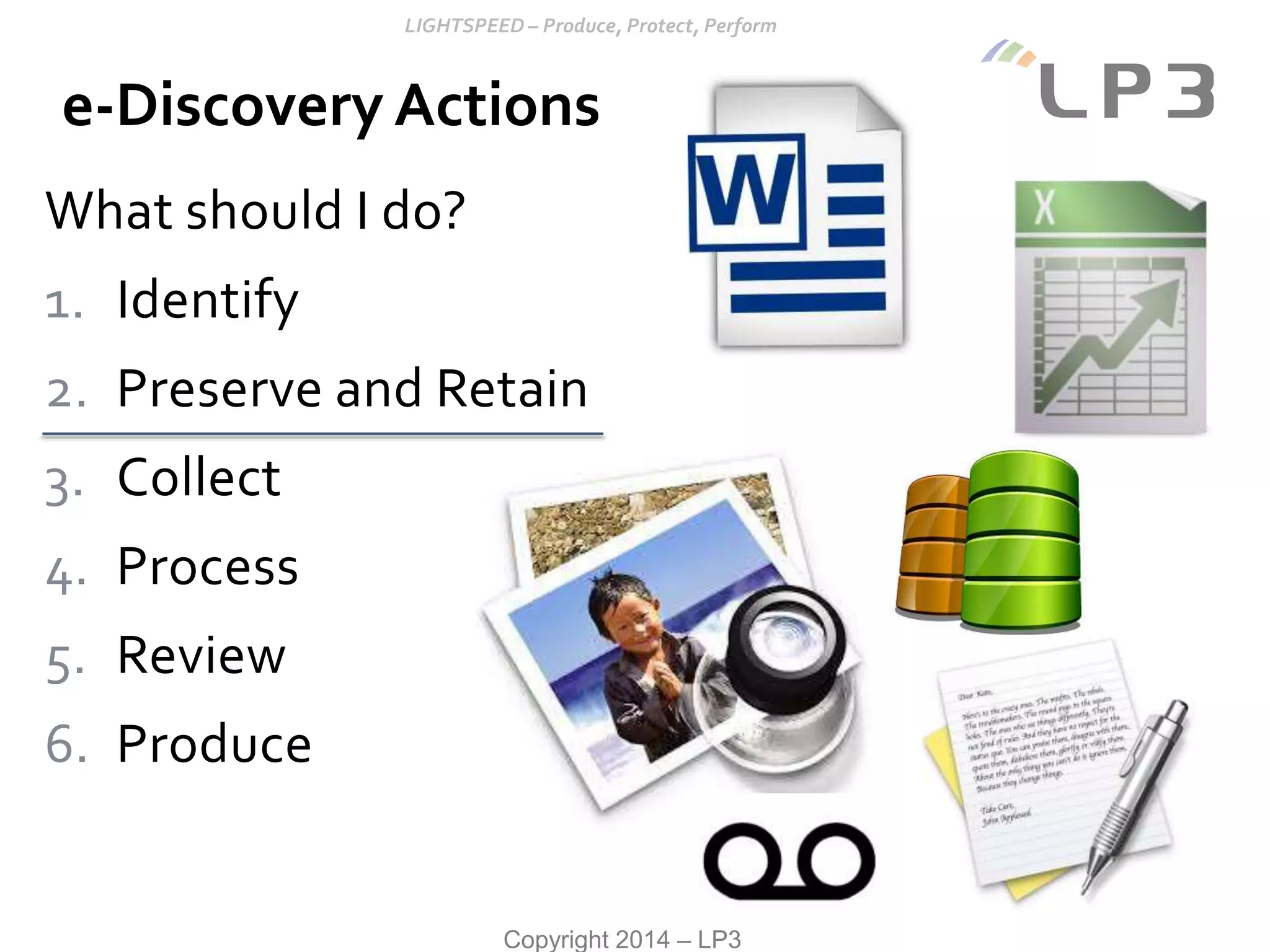
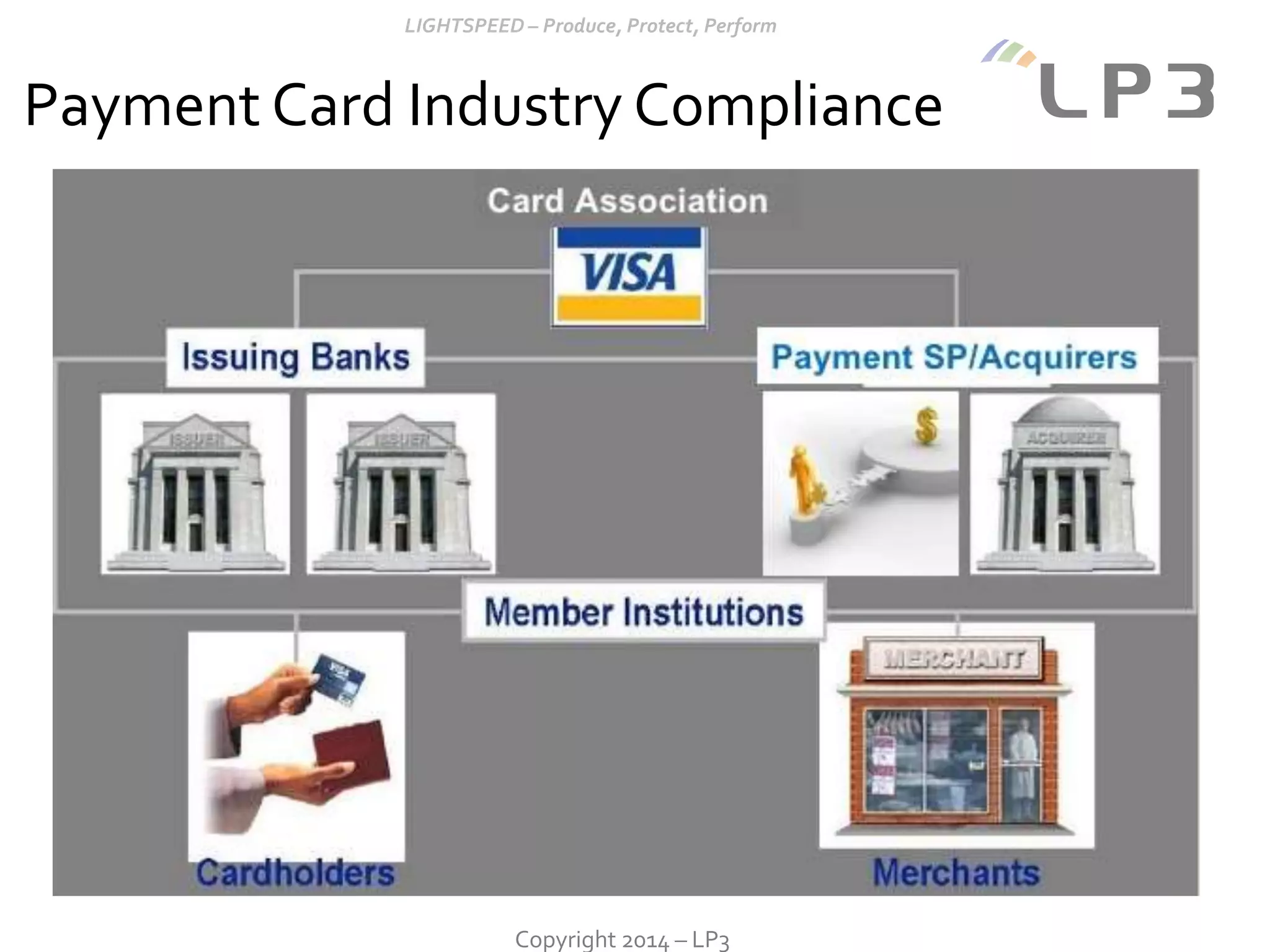
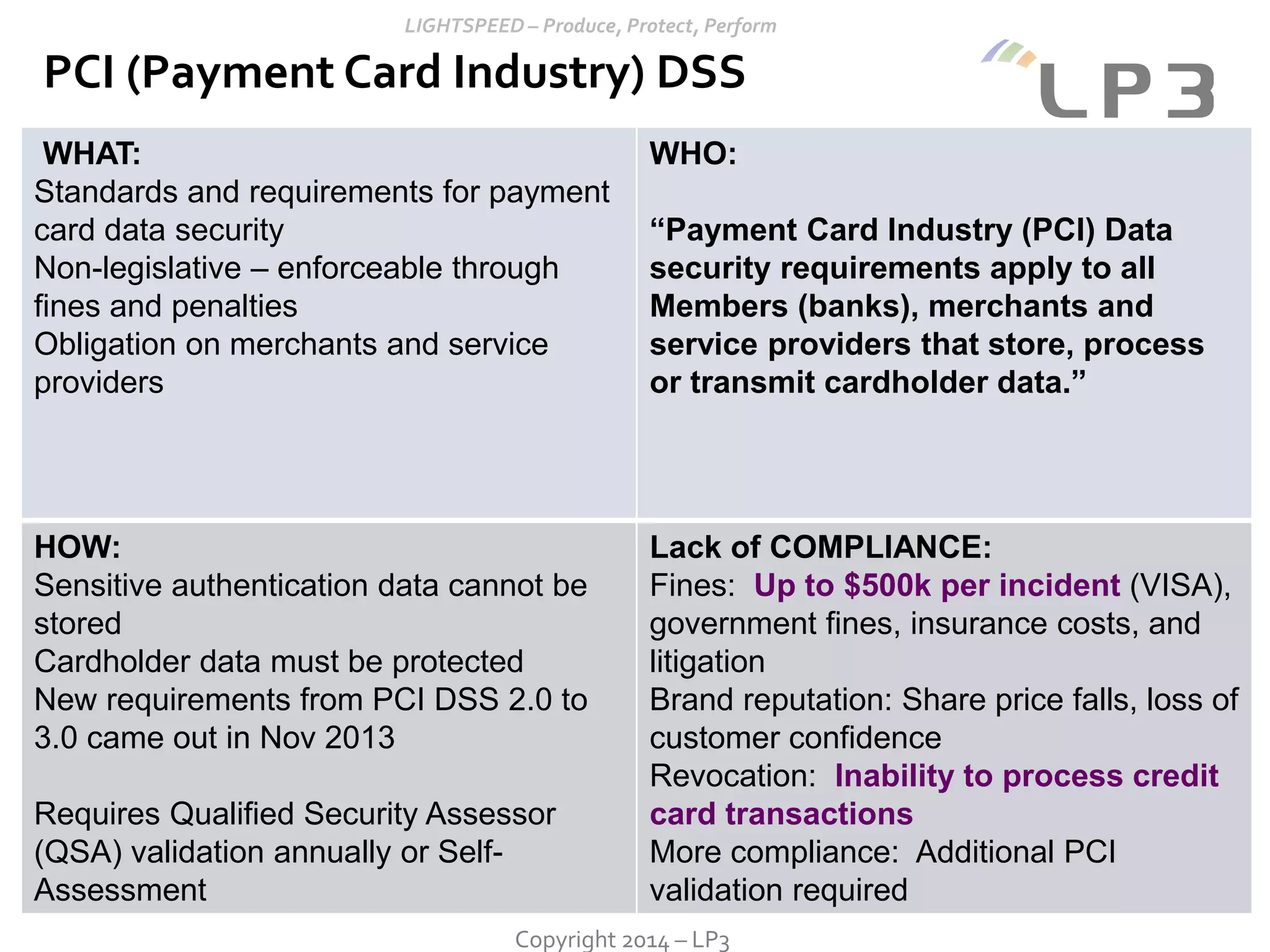
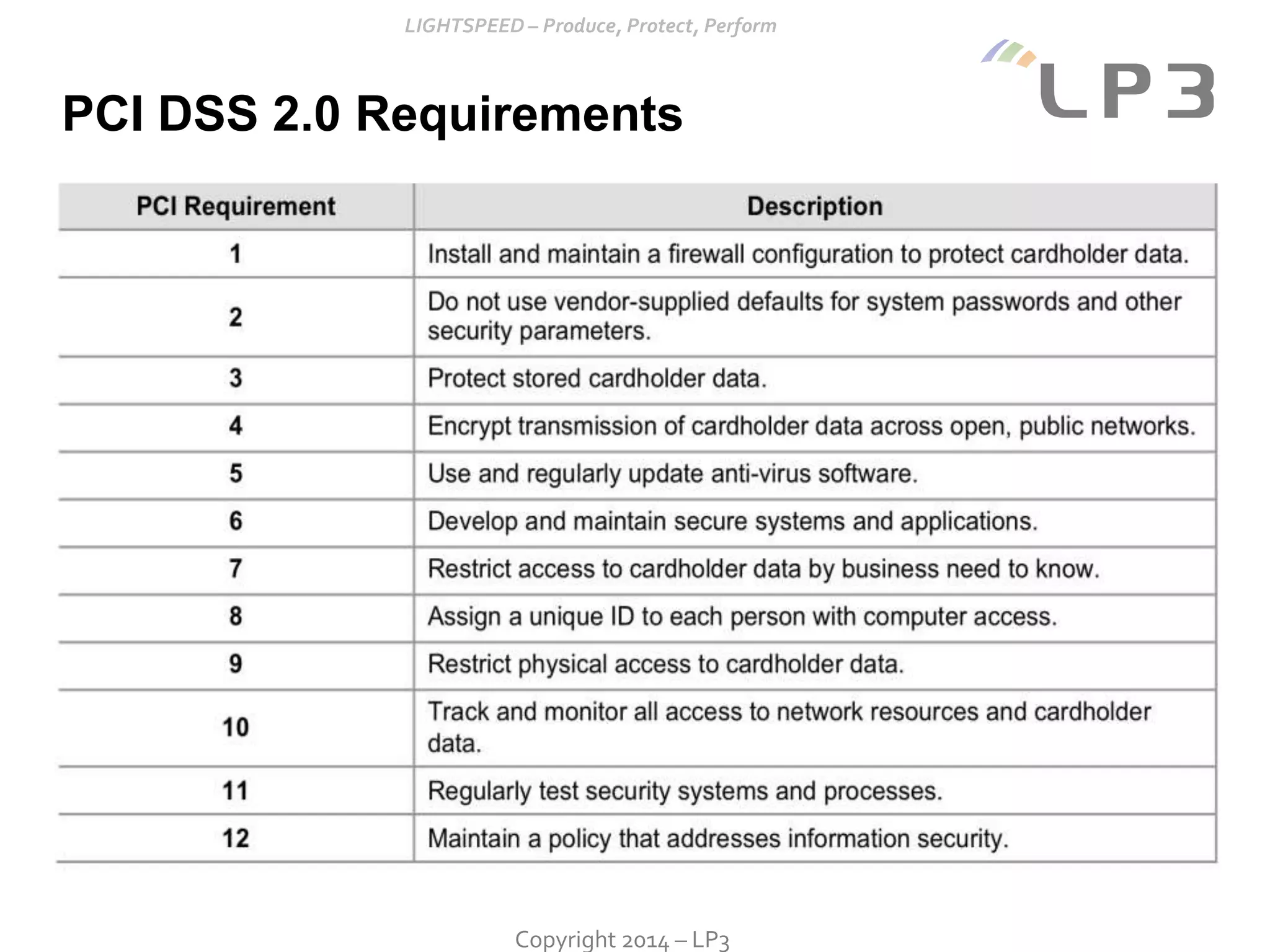
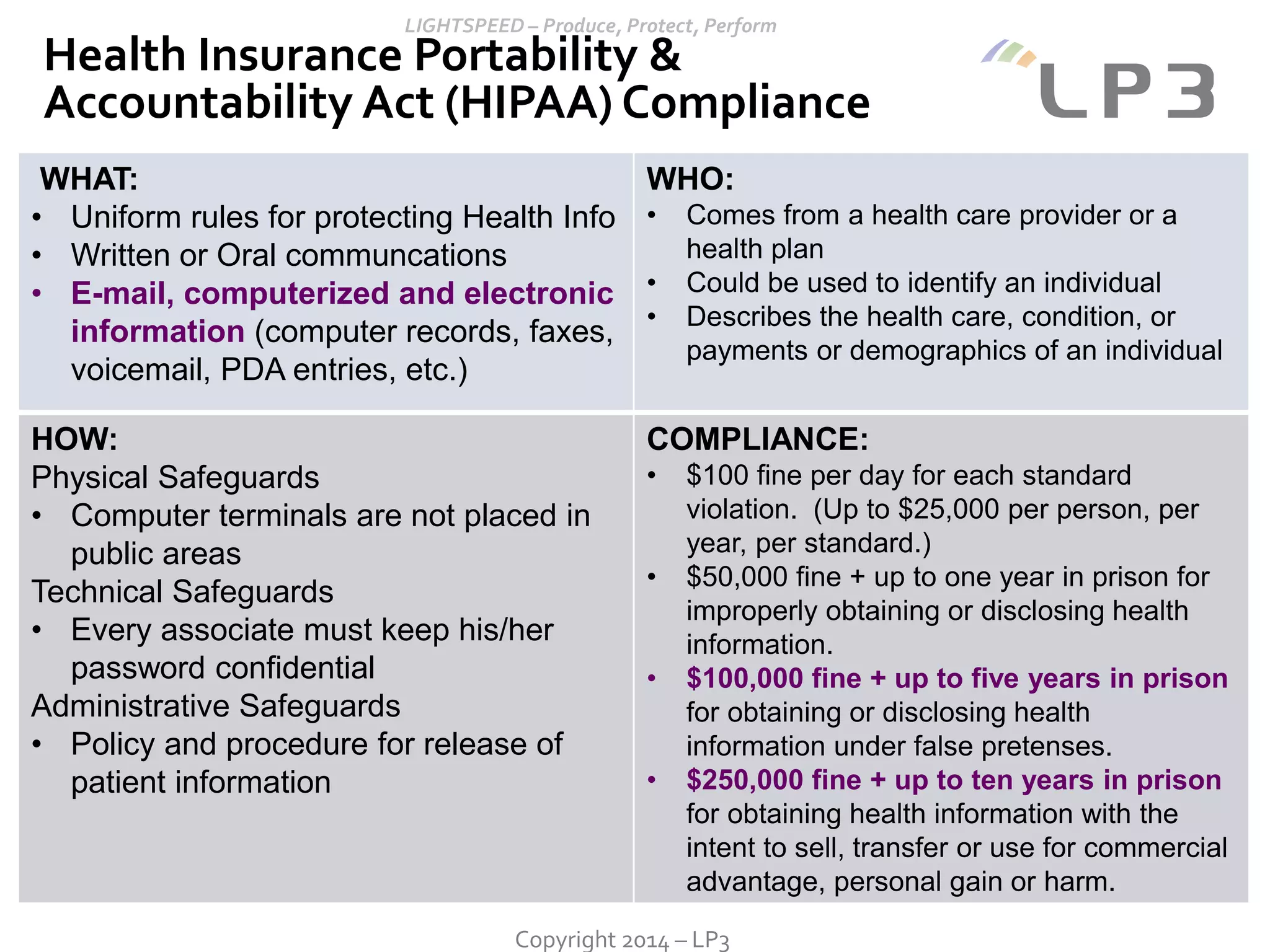
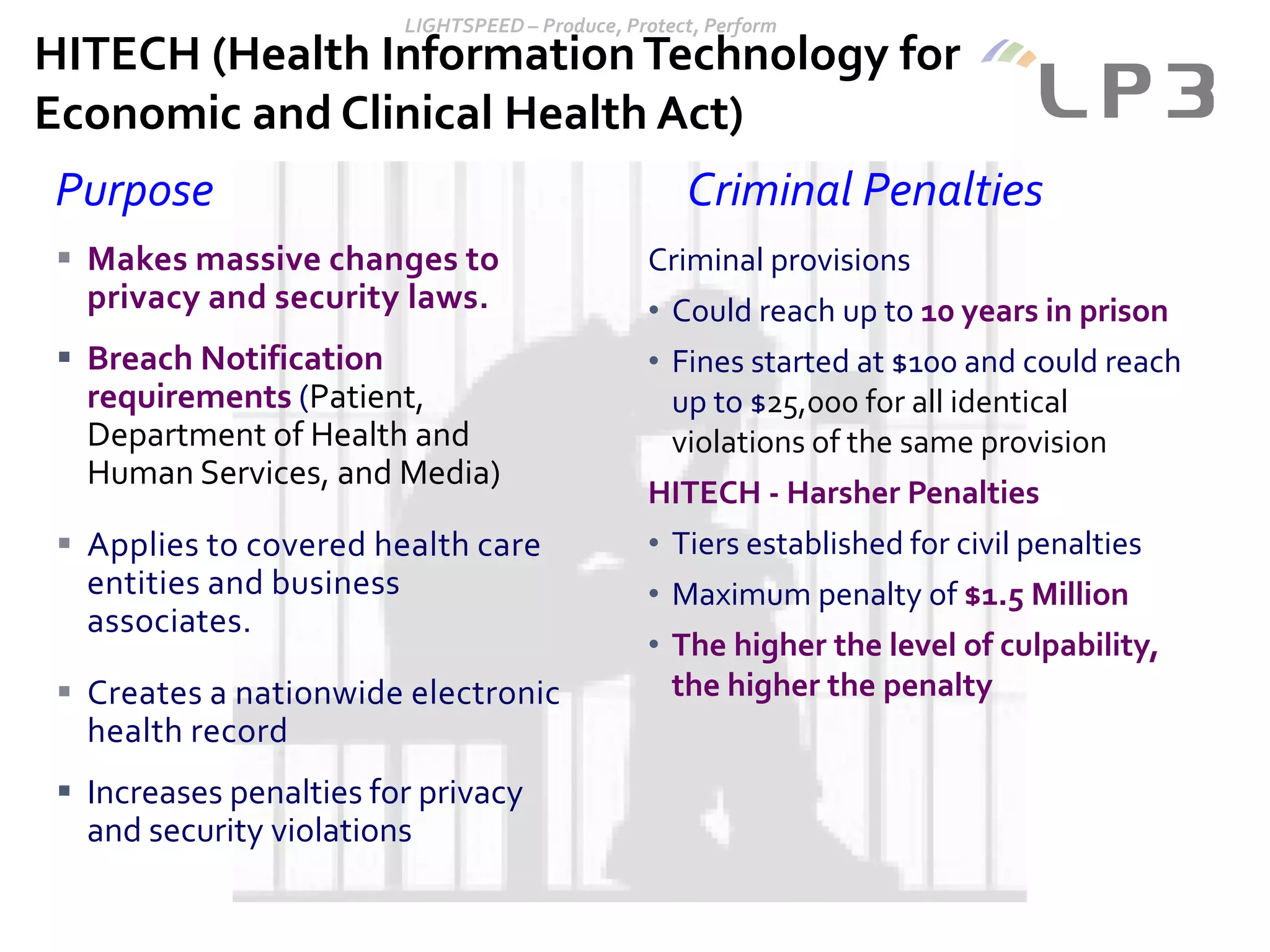
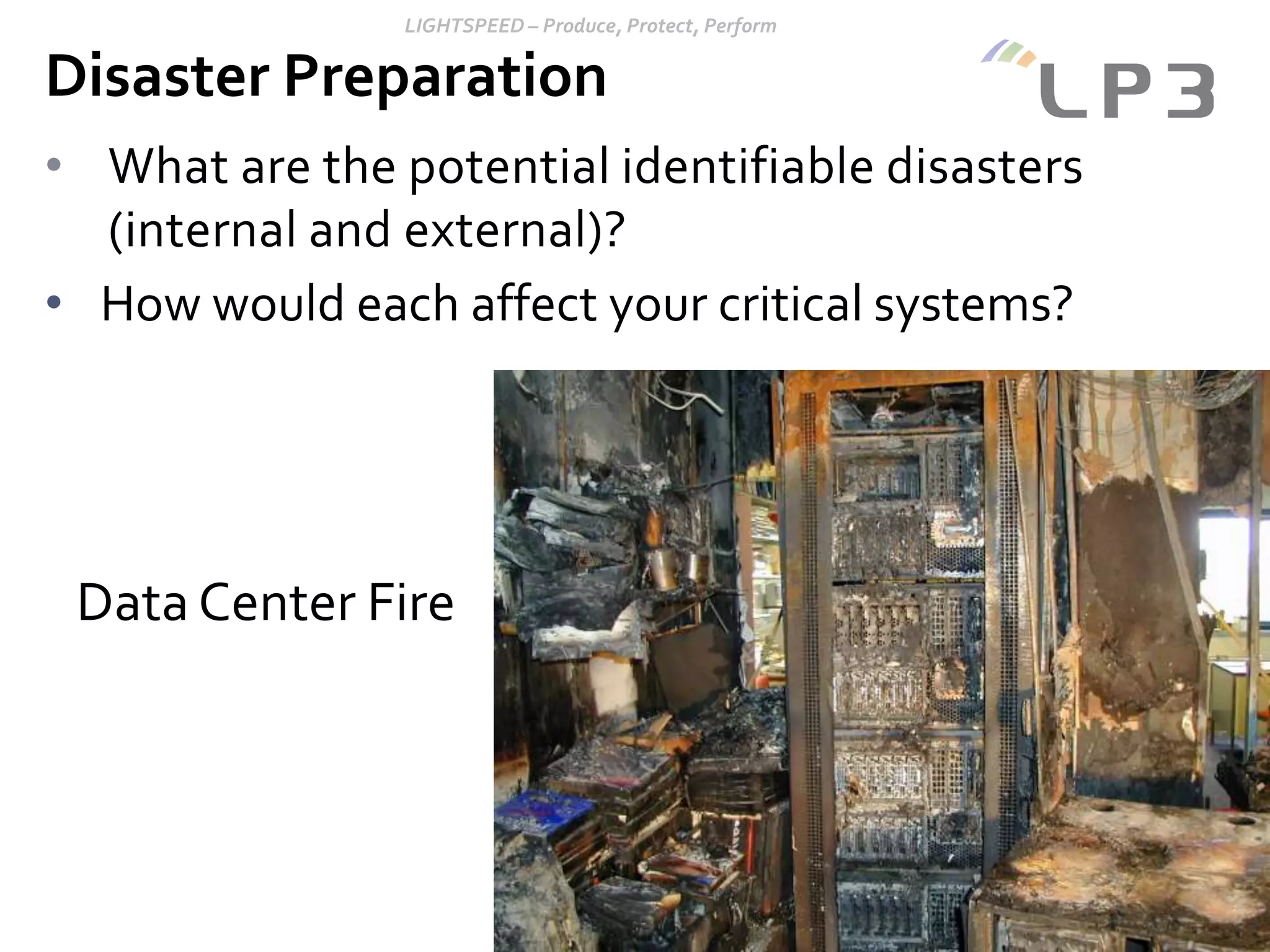
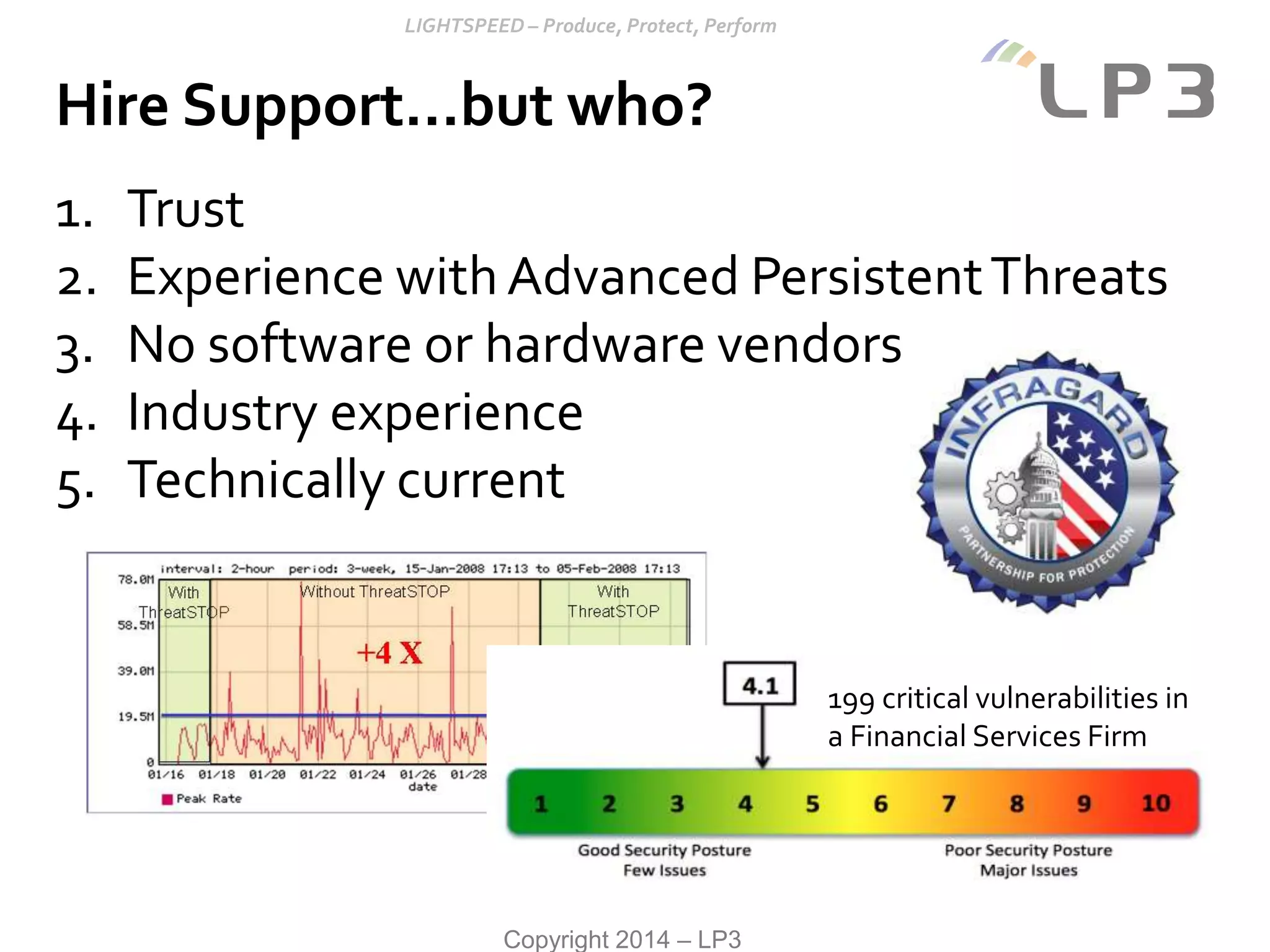
This document discusses various IT security, compliance, legal risk, and disaster preparedness topics. It begins by outlining the basics of an IT security lifecycle including inventorying assets, identifying risks, remediating risks, and monitoring alerts. It then discusses threats like cybercrime, phishing, and issues related to e-discovery, PCI compliance, and HIPAA compliance. The document provides recommendations for legal risk mitigation, disaster preparation, cyber incident handling, and options for addressing IT security needs either through do-it-yourself methods, outside help, or hiring a support organization.