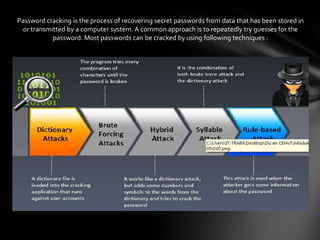
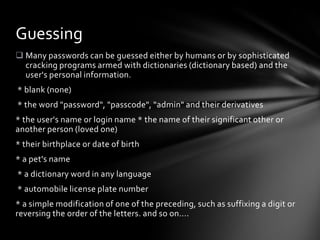
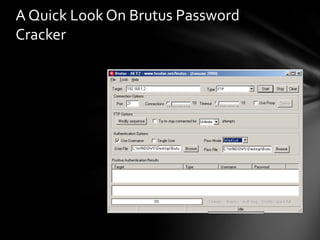
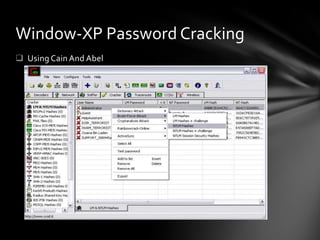
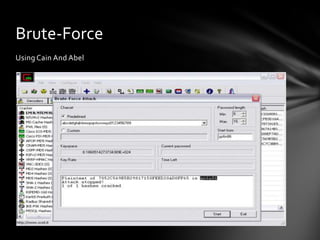
The document discusses various techniques for cracking passwords, including dictionary attacks, brute force attacks, and exploiting weaknesses in password hashing algorithms. Default passwords, social engineering through phishing emails, and the use of tools like Cain and Abel, John the Ripper, and THC Hydra are also covered as effective cracking methods. Common password mistakes that can enable cracking are also listed.