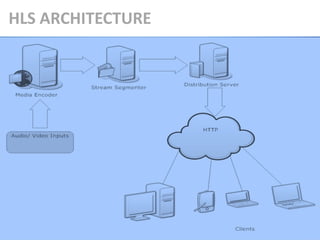
The document summarizes different techniques for streaming media, including HTTP Live Streaming (HLS) and Real Time Streaming Protocol (RTSP). It then describes the architecture and process of HLS in detail over 4 steps:
1) The media is encoded and segmented by the encoder.
2) The segmenter splits the encoded media into short chunks and encrypts the segments if needed.
3) The distribution system stores the segments and playlists on an HTTP server.
4) The client downloads playlists and segments through HTTP and plays the media.
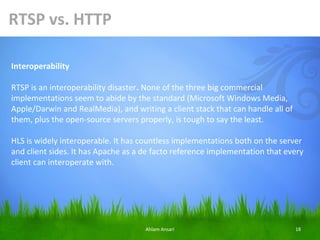
The document also compares RTSP and HLS, noting advantages of HLS like reliability, firewall traversal, and use on YouTube. It surveys different video-

![1. Media Encoder:
The Encoder encodes the video/audio. Videos are compressed into H.264/MPEG-4
format and the audio is encoded using advance audio coding. The video or audio
format is encapsulated in MPEG 2.
Transport Stream is specified in MPEG-2 Part 1, Systems (formally known as
ISO/IEC standard 13818-1 or ITU-T Rec. H.222.0) [3][4][5]. Transport stream
specifies a container format encapsulating packetized elementary streams, with
error correction and stream synchronization features for maintaining transmission
integrity when the signal is degraded.
Program stream is a container format for storage applications specified in MPEG-1
Systems and MPEG-2 Part 1. A program stream contains only one content channel
and is suited to authoring and storage not broadcasting. Contrast with transport
stream, which is designed to address the delivery of the content.
Ahlam Ansari 8](https://image.slidesharecdn.com/dospresentationbyahlamshakeel-121205033056-phpapp01/85/Dos-presentation-by-ahlam-shakeel-8-320.jpg)


![4. Client:
The client gets all the videos or audios through a HTTP connection. HTTP creates a session
between the client and the file at the DS. The session can be either a Live Stream Broadcast
session or a Video on Demand Session.
A) Live Stream Broadcast Session
LSD contains an index file that is dynamic in type and is continuously
updated and refreshed. It includes a moving window of segments.
B) Video on Demand Session
VoD contains an index file that is static in type and it contains all the
segments of the file. [2]
Ahlam Ansari 11](https://image.slidesharecdn.com/dospresentationbyahlamshakeel-121205033056-phpapp01/85/Dos-presentation-by-ahlam-shakeel-11-320.jpg)




![Step 4: Download video/audio at client side
How actually the video / audio is downloaded at client side [8]
1. Download the wowza URL (playlist)
2. Display the contents of the file
3. Download the first/second playlist url
4. Display the contents
5. wget the key URL
6. wget the ts file sequence
If the file is encrypted
7. Hexdump the key
8. Using calc get the HEXADECIMAL Value of "MEDIA-SEQUENCE", to get IV -> 95 =
5F using openssl decrypt the file
9. Now play the file "decr_tmp.ts" using "VLC media player"
Ahlam Ansari 17](https://image.slidesharecdn.com/dospresentationbyahlamshakeel-121205033056-phpapp01/85/Dos-presentation-by-ahlam-shakeel-17-320.jpg)



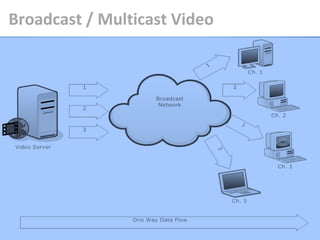
![•The multicast facility of modern communication networks [12] offers an efficient
means of one-to-many data transmission. The basic idea is to avoid retransmitting
the same packet more than once on each link of the network by having branch
routers duplicate and then send the packet over multiple downstream branches.
Multicast can significantly improve the VoD performance.
Passive receive with no control except selecting the channels. One channel is
needed per movie / programme.
Ahlam Ansari 30](https://image.slidesharecdn.com/dospresentationbyahlamshakeel-121205033056-phpapp01/85/Dos-presentation-by-ahlam-shakeel-30-320.jpg)

![•Near video on demand is a video delivery service that allows a customer to select
from a limited number of broadcast video channels when they are broadcast.
NVOD channels have pre-designated schedule times and are used for pay-per-view
services. Passive receive with limited controls. System response time inversely
proportional to number of required channels [12].
Ahlam Ansari 32](https://image.slidesharecdn.com/dospresentationbyahlamshakeel-121205033056-phpapp01/85/Dos-presentation-by-ahlam-shakeel-32-320.jpg)



![Conclusion
•YouTube uses HTTP/TCP to buffer video into the flash player on its main site. The
video is stored on Google Video's content distribution network. It's not streamed
as much as just sent as fast as possible to your computer. However, for 3g mobile
handsets, m.youtube.com uses RTSP to stream video. So, YouTube uses both
transfer methods [10]. Another thing to consider is that YouTube is popular
because "it just works". RTSP isn't always supported well through routers, which
would prevent that for use on the desktop. Also, m.youtube.com doesn't stream
the same video file as youtube.com. Most YouTube videos are not streamed, but
progressively download over HTTP. A small number of partner videos are securely
streamed, using RTMPE.
Ahlam Ansari 48](https://image.slidesharecdn.com/dospresentationbyahlamshakeel-121205033056-phpapp01/85/Dos-presentation-by-ahlam-shakeel-48-320.jpg)
![Reference
[1] Http://develpr.apple.com/library/ios/#documentation/NetworkingInternet/Conceptual/
StreamingMediaGuide/Introduction/Introduction.html
[2] http://www.slideshare.net/DSPIP/apples-live-http-streaming
[3] ITU-T (2006-05). "H.222.0 Summary". Retrieved 2010-06-03.
[4] ITU-T. "H.222.0 : Information technology - Generic coding of moving pictures and
associated audio information: Systems". Retrieved 2010-06-03.
[5] ISO/IEC 13818-1:2000 - Information technology -- Generic coding of moving pictures and
audio information: Systems, neuron2.net, 2000-12-01, retrieved
2010-06-03
[6] http://www.remlab.net/op/vod.shtml
Ahlam Ansari 50](https://image.slidesharecdn.com/dospresentationbyahlamshakeel-121205033056-phpapp01/85/Dos-presentation-by-ahlam-shakeel-50-320.jpg)
![[7]
http://developer.apple.com/library/ios/#documentation/NetworkingInternet/Conceptual/
StreamingMediaGuide/DeployingHTTPLiveStreaming/DeployingHTTPLiveStreaming.html
%23//apple_ref/doc/uid/TP40008332-CH2-DontLinkElementID_29
[8] http://www.wowza.com/forums/showthread.php?13363-Is-it-possible-to-deploy-Apple-
HTTP-Live-streaming-(HLS)-encryption-on-wowza-server/page2
[9] Carlos A S Cunha, “Application of a Self-Healing Video-Streaming Architecture to RTSP
Servers”, 2011 IEEE International Symposium on Network Computing and Applications.
[10] http://answers.yahoo.com/question/index?qid=20071126005233AA4h3Ox
[11] W.-F. Poon, K.-T. Lo and J. Feng, “Batching policy for video-on-demand in multicast
environment”, ELECTRONICS LETTERS 20th July 2000 Vol. 36 No. 15
[12] Huadong Ma and Kang G. Shin, ”Multicast Video-on-Demand Services”, ACM
SIGCOMM
Ahlam Ansari 51](https://image.slidesharecdn.com/dospresentationbyahlamshakeel-121205033056-phpapp01/85/Dos-presentation-by-ahlam-shakeel-51-320.jpg)