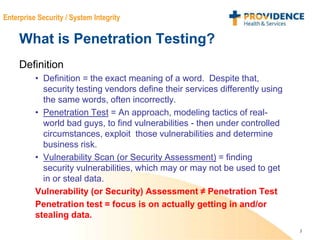
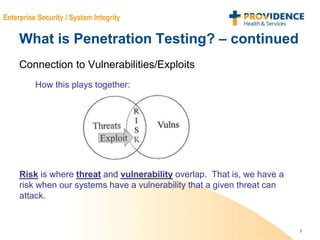
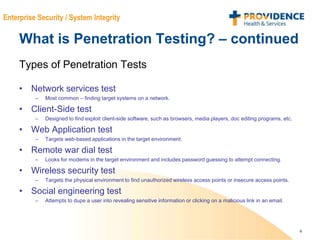
This document provides an overview of penetration testing, including its definition, purpose, types, methodology, tools, challenges, and takeaways. Penetration testing involves modeling real-world attacks to find vulnerabilities in a system and then attempting to exploit those vulnerabilities to determine security risks. It is important for identifying flaws that need remediation and assessing an organization's security posture and risk profile. The methodology generally involves planning, reconnaissance, scanning, exploitation, and reporting phases. Challenges include performing comprehensive testing within time and budget constraints and addressing business impact.