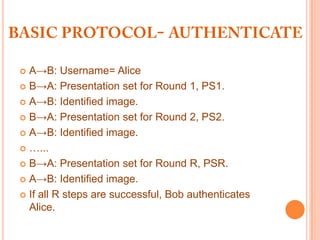
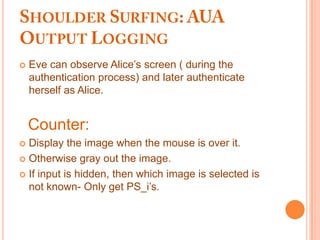
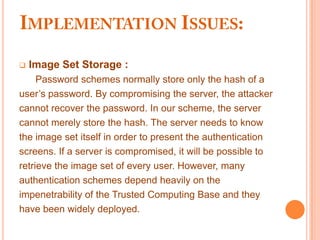
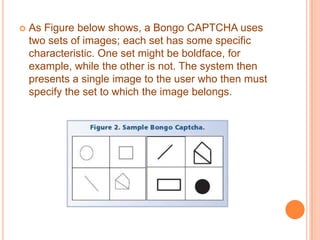
Image-based authentication (IBA) uses a set of user-selected images rather than a password for authentication. The IBA system displays an image set including key images mixed with other images. The user is authenticated by correctly identifying their key images. The document discusses IBA in detail, including potential vulnerabilities and methods to counter threats like observation attacks, brute force attacks, and frequency analysis attacks. It also covers the use of CAPTCHAs to distinguish humans and machines.