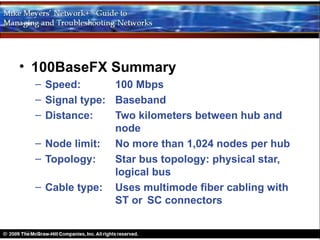
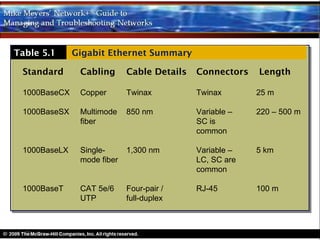
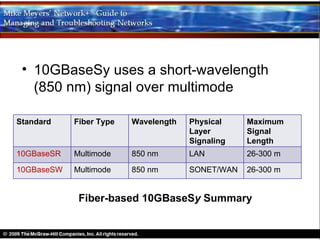
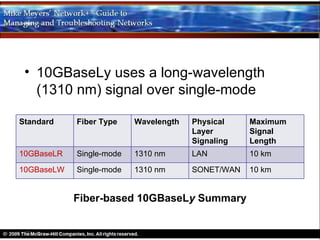
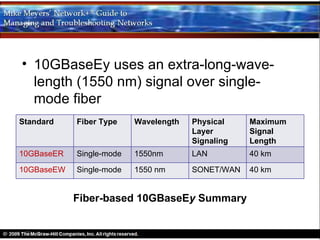
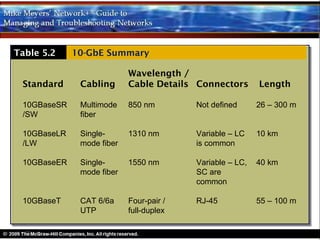
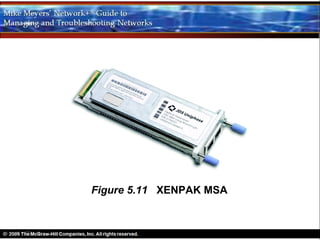
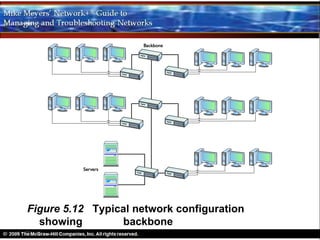
Modern Ethernet standards include 100-megabit Ethernet, Gigabit Ethernet, and 10-Gigabit Ethernet. 100-megabit Ethernet standards include 100BaseT and 100BaseFX. Gigabit Ethernet standards include 1000BaseT, 1000BaseCX, 1000BaseSX and 1000BaseLX. 10-Gigabit Ethernet standards include 10GBaseSR, 10GBaseLR and 10GBaseER which use different fiber types and wavelengths, and 10GBaseT which uses copper cabling. Higher speeds require fiber optic cabling and support longer transmission distances.