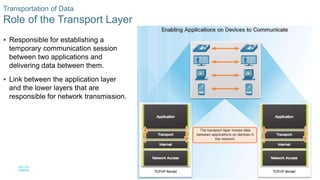
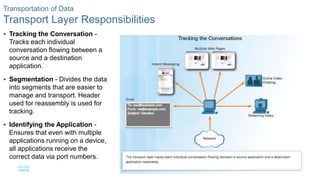
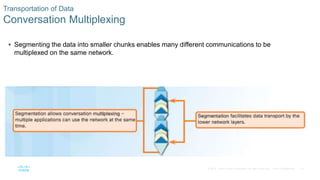
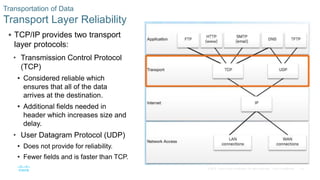
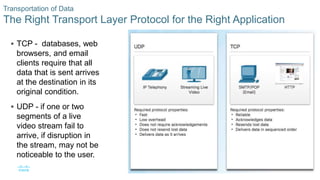
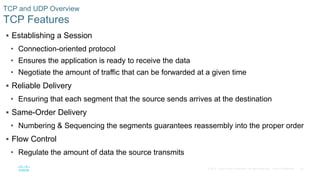
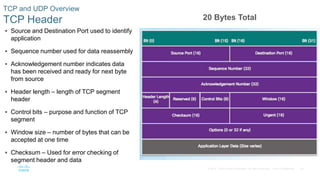
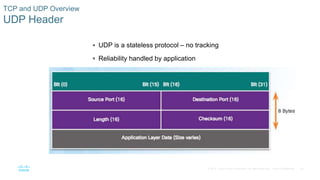
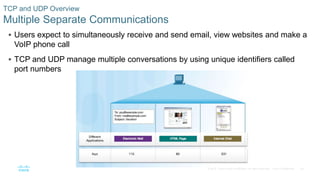
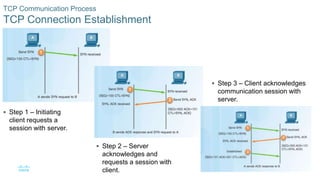
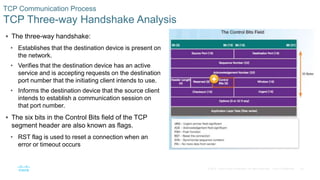
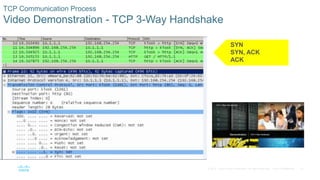
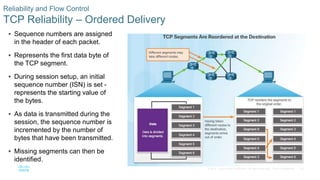
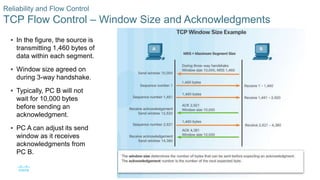
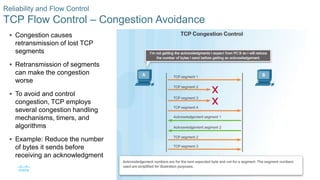
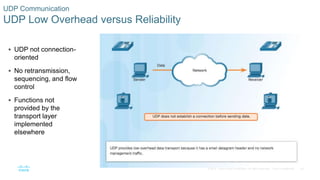
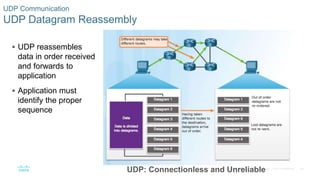
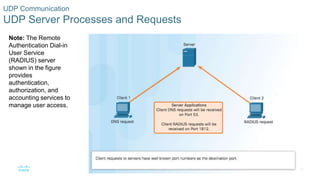
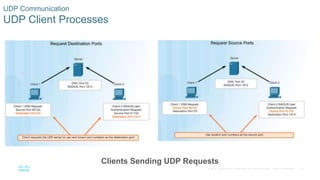
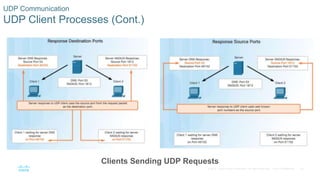
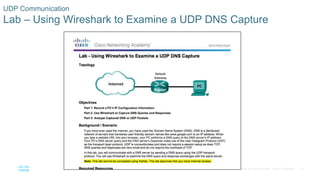
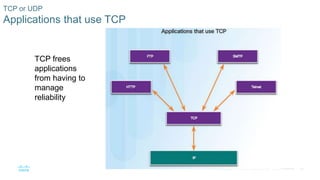
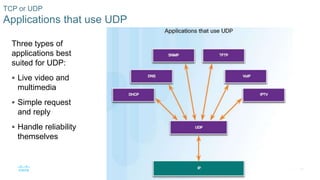
The document discusses the transport layer in computer networks. It describes how transport layer protocols like TCP and UDP support end-to-end communication by establishing connections between applications, segmenting data, and ensuring reliable or unreliable delivery. TCP provides reliable, in-order transmission using sequence numbers, acknowledgments and retransmissions if needed. UDP is connectionless and unreliable but has less overhead than TCP. The document compares TCP and UDP, and explains how applications use each protocol depending on their reliability needs.